
Stablecoin transactions move fast - often irreversible in seconds. That’s why pre-transaction controls, like whitelisting, are essential. Whitelisting restricts payments to pre-approved addresses, reducing risks like phishing, insider threats, and key compromises. But it’s not a complete solution. Modern systems combine whitelisting with real-time risk checks, policy enforcement, and audit trails for better security and compliance.
Key Takeaways:
Whitelisting Basics: Blocks payments to unapproved addresses, protecting funds from errors or fraud.
Limitations: Manual updates, slow onboarding, and lack of context for flagged transactions.
Integrated Systems: Tools like Stablerail add sanctions screening, anomaly detection, and automated governance for smarter, safer transactions.
For stablecoin treasuries managing $1M–$50M annually, integrated controls outweigh standalone whitelisting, offering stronger safeguards without sacrificing efficiency. These controls are central to stablecoin treasury management best practices for growing organizations.
1. Standalone Whitelisting
Standalone whitelisting involves creating a pre-approved list of destinations for fund transfers. Think of it as a security gate for your treasury - if a destination address isn’t on the list, the transaction gets blocked. While effective on its own, this approach is typically just one layer in a broader pre-transaction control framework.
Risk Coverage
This setup doesn’t just limit where funds can go - it also tackles some major security concerns. Here’s how it covers three key risks:
Phishing and social engineering attacks: Even if an employee mistakenly approves a fraudulent transaction, funds can only be sent to pre-approved addresses.
Insider threats: Rogue employees with signing authority can’t redirect funds to personal wallets.
Compromised keys: Even if an attacker gains access to your private keys, they can’t move assets to unauthorized destinations.
To make this system even more secure, you might want to enforce a 24–72 hour cooldown period for newly added addresses. This provides time for verification and reduces the risk of hasty errors. Pairing whitelisting with tools like address labeling and transaction memos can also help ensure funds are sent to the correct approved destination.
Governance and Policy Integration
Adding new addresses to the whitelist requires a structured, multi-step process with multi-signature approval. This reduces the risk of social engineering and ensures no single individual can make changes on their own. Ideally, the whitelist should be managed using a multi-signature wallet or governance module.
However, standalone systems have their downsides. Manual vetting and updating of the whitelist can slow things down, especially when onboarding new counterparties. Rules for who can approve changes, how long cooldown periods should last, and which addresses qualify for the list are often scattered across spreadsheets or custom tools. This fragmented approach can make consistent enforcement tricky and lead to operational delays.
Auditability and Compliance
Traceability is essential, and whitelisting helps by creating a clear audit trail. Every transaction is tied to a pre-approved counterparty, making it easier to explain approval decisions. But standalone systems aren’t perfect when it comes to auditability. Joan Alavedra from Openfort highlights one key issue:
The logic is brittle, distributed across multiple systems, and invisible to anyone trying to audit what a wallet can actually do.
Additionally, relying on manual address books stored in spreadsheets can create compliance headaches. Without version control or dual-approval mechanisms, it’s hard to prove who approved an address, when it was added, or whether proper screening was done. This lack of documentation can cause problems when auditors or regulators ask for evidence of your counterparty vetting process.
2. Integrated Pre-Transaction Controls (e.g., Stablerail)

Integrated systems like Stablerail take whitelisting a step further by evaluating the full transaction context - amount, timing, behavior, and counterparty risk - before any signing occurs. Let’s break down how these systems use risk analysis and time-based safeguards to strengthen pre-transaction security.
Risk Coverage
These systems analyze multiple risk factors at once. Before a transaction is executed, AI tools create a "Pre-Flight Risk Dossier", which evaluates aspects like sanctions compliance, tainted funds, and counterparty risk. Based on this analysis, the system assigns one of three outcomes: PASS, FLAG, or BLOCK.
Time-based safeguards add another layer of security. For example, transactions exceeding $100,000 might face a mandatory delay of four hours. This pause provides a crucial window for identifying fraudulent activity or spotting patterns that could threaten stablecoin stability.
Governance and Policy Integration
Beyond risk analysis, integrated systems improve governance by automating policy enforcement. Instead of relying on manual checklists, these platforms implement policy-as-code rules. For instance, a policy requiring "CFO approval for weekend transfers over $10,000" is enforced automatically, ensuring no one - even executives - can bypass it.
Stablerail acts as a gatekeeper between payment intent and the signing process, eliminating the risk of "blind signing." Transactions are only executed if they meet all predefined treasury rules.
This method also enforces separation of duties (SoD) programmatically. No single person can initiate, approve, and execute a transaction. As Stablerail explains:
Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money.
Additionally, funds remain under your control thanks to MPC-secured, non-custodial vaults. The system overlays governance protections without ever taking custody of the assets.
Auditability and Compliance
Integrated systems also excel in providing real-time, automated audit trails. Every transaction generates a "Proof-of-Control" receipt, which records critical details such as the payment amount, purpose, approver, and risk assessment. This eliminates the need for manual record-keeping and ensures a clear, automated trail for every action - intent creation, risk checks, flags, overrides, approvals, and final signing.
Advantages and Disadvantages
Standalone Whitelisting vs Integrated Pre-Transaction Controls Comparison
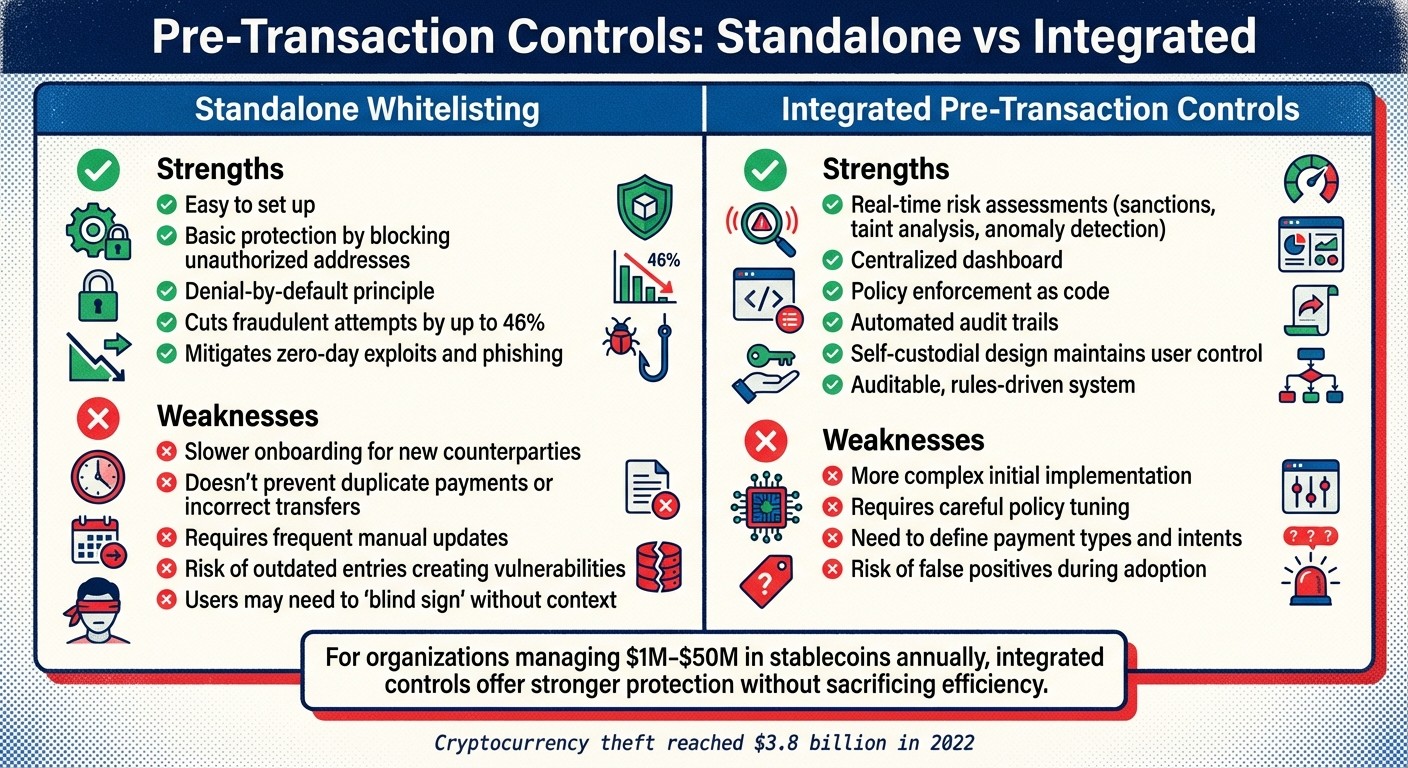
When it comes to pre-transaction controls for stablecoin payments, there are clear trade-offs between standalone whitelisting and integrated control systems. Here's a breakdown of their key differences:
One major drawback of standalone whitelisting is its reliance on constant manual updates. Outdated entries, such as defunct vendors or former employees, can create security gaps. In contrast, integrated controls operate as an auditable, rules-driven system, enforcing crypto compliance during the payment intent phase instead of relying solely on post-transaction monitoring.
Choosing the right approach depends largely on your transaction volume and risk appetite. For organizations managing between $1 million and $50 million in stablecoins annually, the operational burden of manual whitelisting often outweighs its simplicity. And with cryptocurrency theft hitting $3.8 billion in 2022 alone, pre-transaction screening has become an essential layer of protection. These distinctions highlight the importance of aligning your control method with your organization's specific needs.
Conclusion
Whitelisting is most effective when it functions as part of a layered pre-transaction control system rather than being used on its own. While it acts as a firewall to block unauthorized addresses and protect your treasury, it does have limitations. It cannot guard against insider threats, compromised signing keys, or social engineering attacks.
The move toward compliance-as-infrastructure changes the game by automating governance and enforcing rules in real time. Instead of relying on manual processes like back-office checks or spreadsheet tracking, these systems embed governance rules directly into code. This creates a machine-enforced layer that catches errors before they occur. As Stablecoin Insider aptly stated:
A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process.
For organizations managing between $1 million and $50 million in stablecoins annually, manual whitelisting simply isn’t practical. Integrated pre-transaction controls offer a better solution, combining whitelisting with sanctions screening, taint analysis, and anomaly detection. These controls maintain self-custodial security while generating immutable audit trails for every payment decision as part of a stablecoin compliance checklist. This highlights the need for a more streamlined and integrated system.
To optimize your approach, consider implementing a tiered wallet structure with strict multi-signature controls for your largest balances. Enhance your whitelist with transaction simulation tools and conduct quarterly reviews to remove inactive addresses and rotate signer keys. Most importantly, avoid managing a whitelist through a single externally owned account. Instead, rely on multi-signature wallets or governance modules to maintain control.
When whitelisting is combined with policy-as-code engines, dynamic risk management, and clear transaction context, it becomes more than just a security measure - it evolves into a system that secures the business decisions behind stablecoin payments. This is the difference between basic protection and fully operational control.
Stablerail demonstrates this integrated approach by operating above custody and before signing. It merges robust whitelisting with real-time policy enforcement, safeguarding not only the keys but also the critical business decisions tied to stablecoin transactions.
FAQs
When is whitelisting enough for stablecoin payments?
Whitelisting plays a key role in stabilizing stablecoin payments, especially when integrated into a broader pre-transaction control system. By limiting transactions to pre-approved wallet addresses, it provides a basic layer of security. However, for transactions involving greater risk, relying solely on whitelisting isn't enough. Pairing it with tools like sanctions screening, behavioral anomaly detection, and multi-layer approval processes creates a more robust framework. This multi-faceted system not only strengthens compliance and security but also ensures better oversight of transactions in an ever-changing risk environment.
How do cooldown periods reduce whitelist risk?
Cooldown periods help reduce the risks associated with whitelists by adding a delay before transactions are executed. This extra time is crucial for carrying out verification steps like sanctions screening, detecting anomalies, and ensuring compliance with policies. By introducing this pause, cooldown periods act as a safeguard, preventing unauthorized or potentially risky transfers from being finalized.
What’s the difference between whitelisting and policy-as-code controls?
Whitelisting involves approving specific addresses or entities, ensuring transactions occur only with pre-approved wallets. It’s a straightforward, list-based method for controlling access. However, it’s rigid and doesn’t accommodate more intricate or evolving policies.
On the other hand, policy-as-code integrates governance rules directly into automated systems. This approach allows for dynamic enforcement based on various conditions, such as transaction size, timing, or associated risk levels. It’s a more comprehensive solution, supporting advanced features like multi-step approvals and behavioral checks, making it suitable for complex scenarios.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


