
Stablecoin payments are irreversible, making compliance critical. Two approaches tackle this issue:
Real-Time Policy Enforcement: Screens transactions before execution. It blocks, flags, or approves payments based on pre-set rules, preventing errors or regulatory violations. Features include sanctions screening, anomaly detection, and risk scoring. This proactive method avoids issues like wallet freezes caused by high-risk transactions.
Post-Transaction Monitoring: Reviews payments after settlement. It identifies problems too late to reverse, leaving businesses exposed to risks like sanctioned payments. Delays in detection and manual processes make it less effective for fast blockchain transactions.
Key Takeaway: Real-time enforcement ensures compliance upfront, reducing risks and errors. Post-transaction monitoring identifies issues after the fact but lacks preventive measures.
Quick Comparison
Real-time enforcement is the better option for managing stablecoin treasuries, ensuring payments are secure and compliant before execution.
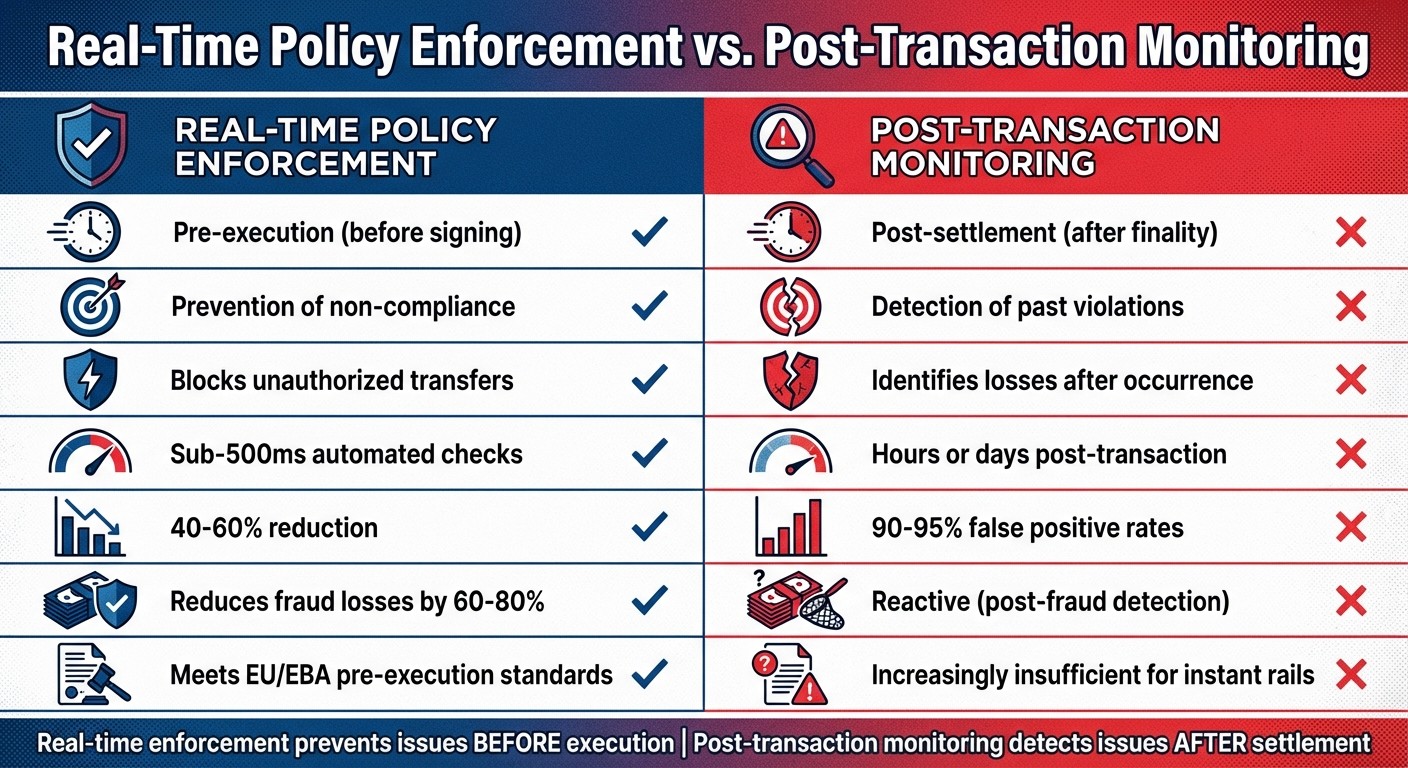
Real-Time Policy Enforcement vs Post-Transaction Monitoring Comparison
Managing Crypto Threats in 2026 | Compliance, Fraud & Investigation Strategies
How Real-Time Policy Enforcement Works
Real-time policy enforcement acts as a smart layer between the intention to make a payment and its execution on the blockchain. Instead of analyzing transactions after they’ve settled, this system evaluates payments before they’re signed. By running automated checks based on pre-set rules, it determines whether to approve, deny, hold, route, or escalate a transaction. This approach shifts compliance from being a reactive process to a proactive safeguard, catching issues before they hit the blockchain.
At its core, this system uses policy-as-code governance, turning treasury rules into machine-enforced protocols. For example, finance teams can define policies like “Payments over $10,000 on weekends need additional approval” or “Transactions to new addresses exceeding $5,000 require CFO sign-off and verification.” These rules are applied automatically to every payment. As Milos Djukanovic puts it: "A policy engine is the decision authority between payment intent and transaction execution, returning outcomes like approve, deny, hold, route, or step-up".
One major issue this model addresses is the freeze risk associated with stablecoin payments. If funds are sent to flagged or sanctioned addresses, stablecoin issuers like Circle or Tether can freeze the wallet, potentially locking up critical operating funds. Real-time enforcement prevents this by flagging high-risk counterparties before any transaction occurs, avoiding the regulatory headaches that post-transaction monitoring might reveal too late. Let’s dive into the key features that make this system so effective.
Core Features of Real-Time Policy Enforcement
Real-time enforcement systems carry out pre-sign checks, including sanctions screening, policy compliance, anomaly detection, and risk scoring. Each check provides clear outcomes supported by detailed explanations. Here’s how these features work:
Sanctions and taint screening: Compares recipient addresses against global watchlists and examines blockchain activity for links to illicit behavior.
Policy and limit enforcement: Ensures transactions adhere to spending caps, role-based permissions, and approved counterparty lists.
Behavioral anomaly detection: Flags unusual patterns based on factors like transaction timing, amount deviations, or payout frequency.
Counterparty risk scoring: Evaluates the recipient’s on-chain history and reputation to assess potential risks.
What sets this system apart is its ability to generate plain-English explanations for flagged payments. Instead of cryptic error codes, the system provides clear reasons - such as policy violations, timestamps, or risk scores - allowing finance teams to make informed decisions. If a payment is flagged, they can either override the alert or escalate it for further review.
Another critical safeguard is the separation of duties. No single person can initiate, approve, and execute a payment, ensuring a transparent process with a detailed audit trail documenting every step. These layered checks create a secure and efficient workflow from payment intent to execution.
Workflow from Intent to Execution
This system streamlines the journey from initiating a payment to its secure completion through four key stages:
Intent Creation:
The process begins when a user initiates a payment - whether by uploading a CSV file, submitting an invoice, or using a payment interface. The system automatically extracts key details, such as vendor name, invoice number, and amount, and matches them to the relevant policies.
Automated Verification:
Next, the system performs automated checks, including sanctions screening, spending limit validation, counterparty risk assessment, and anomaly detection. A Risk Dossier is generated with a verdict of PASS, FLAG, or BLOCK, along with detailed reasons. For example, if a vendor’s wallet address has changed since the last payment, the system locks the transaction for manual review to prevent potential fraud.
Human-in-the-Loop Approval:
For flagged transactions, an authorized reviewer steps in to examine the Risk Dossier. If they decide to proceed, they must provide a clear reason for overriding the flag. Transactions that pass all checks can move forward with a single click, using MPC wallets for corporate treasury to ensure secure multi-party computation signing.
Execution and Audit Trail:
Once approved, the transaction is signed via MPC, and a Proof-of-Control receipt is generated. This receipt includes all key details - what was paid, who approved it, the risk verdict, and timestamps. The comprehensive audit trail offers CFO-level evidence for auditors, boards, or regulators, showing that robust controls were in place.
How Post-Transaction Monitoring Works
Post-transaction monitoring examines transactions after they’ve been settled on the blockchain, meaning any issues are flagged only after the funds have already moved. By the time a problem is identified, the transaction is final and irreversible.
This process typically involves reviewing transaction logs in batches on a set schedule - daily or weekly, for instance. During these reviews, compliance teams check for sanctions violations, unusual patterns, and other red flags. However, blockchain transactions settle almost instantly - Ethereum takes about 12 seconds, and Solana only 2 seconds - while monitoring systems often lag by hours or even days. This creates a delay that bad actors can exploit.
"Post-transaction 'monitoring only' approaches discover issues after settlement finality".
Because these systems act as advisory tools rather than preventive measures, they can only highlight mistakes after the fact. For example, if a stablecoin payment is sent to a sanctioned wallet, the transaction cannot be undone. In such cases, the treasury may face serious consequences, such as a freeze from the stablecoin issuer. This reactive model is a stark contrast to pre-execution controls, which aim to prevent such errors in the first place.
Common Techniques in Post-Transaction Monitoring
Post-transaction systems use several methods to detect issues after funds have moved:
Transaction tracing: Tracks fund flows across the blockchain to identify connections to flagged or suspicious wallets.
Suspicious activity reporting: Flags unusual behaviors, such as large withdrawals or payments to unknown entities, for further investigation.
Audit logs: Maintains detailed, timestamped records of all transactions, creating a compliance trail for regulators and internal reviews.
However, delays in these processes can cause significant problems. Rules-based systems often generate false positives - sometimes as high as 90–95% - which overwhelm compliance teams with alerts that require manual investigation. Meanwhile, criminals can exploit the time gap between when a transaction is settled and when it’s flagged.
"A customer can open an account online, transfer illicit funds through multiple layering transactions, and close the account within hours - far faster than end-of-day sorting can detect".
The risks of delayed detection are real. For example, in 2021, the Financial Conduct Authority fined HSBC £63.9 million for weaknesses in its transaction monitoring systems over an eight-year period. Similarly, when the UK launched real-time payments in 2008, online banking fraud spiked by 132% in a single year because traditional monitoring couldn’t keep up with faster payment speeds.
Despite the tools used, the inherent delays in post-transaction monitoring limit its ability to reduce risks effectively.
Limitations of Post-Transaction Monitoring
For stablecoin treasuries, the combination of delays and the irreversibility of blockchain transactions creates significant vulnerabilities. The biggest issue is that once a transaction is finalized, it cannot be undone. For instance, if $50,000 is mistakenly sent to a sanctioned address, the system might catch the error later, but by then, the funds are gone.
Batch reviews, often conducted on a 24-hour cycle, leave gaps in compliance. Blockchains settle transactions in seconds, while sanctions lists like OFAC’s are updated daily. A wallet address that appears legitimate at the time of transfer could be sanctioned shortly after, leaving the monitoring system to catch the issue only in its next review.
Manual intervention further slows the process. Each flagged transaction must be individually investigated, which is far too slow for today’s fast-paced payment systems. This creates a bottleneck, forcing finance teams to choose between speed and security. These delays make it clear that while post-transaction monitoring has its uses, it struggles to meet the demands of modern financial systems.
Real-Time Policy Enforcement vs. Post-Transaction Monitoring
Real-time policy enforcement works proactively, stepping in before a transaction is signed to ensure compliance, while post-transaction monitoring only detects problems after the transaction has been finalized and cannot be reversed.
With real-time systems, payment intent is validated before the signature stage. These systems can automatically block high-risk transfers, applying actions like denying the transaction, placing it on hold, or triggering additional authentication steps. In contrast, post-transaction monitoring is reactive - it identifies issues only after the funds have already moved, making it impossible to prevent the transfer.
The importance of real-time enforcement is highlighted by new EU guidelines (EBA/GL/2024/14 and 15), which will require financial and crypto-asset service providers to demonstrate that transactions are screened before execution starting December 30, 2025. As Trapets succinctly puts it:
"If screening takes place after the payment has been processed, it's already too late".
Tamas Kadar, CEO of SEON, reinforces this point:
"By identifying high-risk transactions instantaneously and blocking them before they are completed, organizations can prevent financial harm rather than merely reacting to it after the fact."
These regulatory shifts emphasize the growing need for pre-execution controls, particularly in stablecoin treasuries.
AI-powered real-time screening systems are a game-changer in this space. Operating in under 500 milliseconds, they reduce false positive alerts by 40–60%, enabling quick and accurate decision-making. Traditional systems, on the other hand, often generate false positive rates as high as 90–95%, creating a heavy workload for manual review teams.
Comparison Table
One standout example of real-time enforcement is Stablerail, which functions as an agentic control plane positioned above custody and before transaction signing. Stablerail demonstrates how embedding pre-sign controls can enhance governance for stablecoin transactions. It performs essential checks - such as sanctions screening, policy enforcement, behavioral anomaly detection, and counterparty risk scoring - while generating clear, plain-English risk reports. These reports explain why a transaction was flagged, ensuring that finance teams can maintain the same governance standards they expect for traditional bank wires, all while retaining the speed of on-chain settlement.
Benefits of Real-Time Policy Enforcement for Stablecoin Treasuries
Operational and Compliance Benefits
Real-time policy enforcement is reshaping how stablecoin treasuries manage their operations by embedding governance directly into the transaction process. Instead of relying on outdated tools like spreadsheets or Slack approvals, Stablerail's Policy Console allows finance teams to set machine-enforceable rules. For instance, rules like "Payments over $5,000 to new addresses require CFO approval and verification" or "Transfers exceeding $10,000 on weekends need extra approval" are automatically applied to payment intents before they can move forward.
This "policy-as-code" model significantly reduces human error and ensures proper separation of duties. No single individual can request, approve, and execute a payment, while every transaction generates a Proof-of-Control receipt. This receipt provides key details, such as why the payment was approved, which policy applied, and who authorized it, creating an audit-ready trail. This approach not only meets SOX compliance standards but also provides CFO-grade evidence for auditors, boards, and regulators.
The Stablerail Treasury Hub simplifies operations even further by consolidating balances, entities, and chains into one platform. Meanwhile, the Policy Console ensures that defined roles and limits are enforced programmatically. This automation eliminates the need for manual processes, enabling instant settlement 24/7, bypassing the delays often associated with traditional banking hours. Together, these tools enhance operational efficiency while strengthening risk management for stablecoin transactions.
Risk Reduction in Stablecoin Transactions
Beyond improving operations, real-time policy enforcement addresses risks at the source, preventing costly and irreversible blockchain errors. Pre-sign checks - covering areas like sanctions screening, spending limits, and behavioral anomaly detection - identify potential issues before a transaction is executed.
One major risk is counterparty freeze-risk, where sending funds to a flagged address could result in stablecoin issuers like Circle or Tether freezing the entire treasury wallet. Stablerail mitigates this by screening for tainted counterparties and suspicious patterns, blocking transactions that could lead to freezes.
The platform also adds extra layers of protection with smart cool-off periods. For example, high-value transfers (over $100,000) or payments to new beneficiaries are automatically delayed, reducing the risk of social engineering attacks. If a vendor's address changes, the system’s "Golden Source" whitelist locks the payment and escalates it for mandatory review, safeguarding against invoice fraud.
Conclusion
Real-time policy enforcement is reshaping stablecoin treasury management by assessing payment intent before transactions are executed, effectively avoiding irreversible blockchain errors. This approach stands in stark contrast to post-transaction monitoring, which only identifies issues after final settlement. By catching potential problems upfront, real-time enforcement ensures a higher level of security and accuracy.
Stablerail serves as a prime example of this proactive model. Its self-custodial, pre-sign governance workflow ensures compliance while keeping the final signing authority in human hands. As Stablerail explains:
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money".
This setup separates decision-making from execution, eliminating blind signing by simulating payments ahead of time. It helps detect potential issues like address changes, duplicate payments, or interactions with flagged counterparties before any funds are moved.
The move from reactive monitoring to real-time enforcement highlights a growing shift toward machine-enforced compliance systems that take the place of manual back-office processes. Stablerail's policy-as-code engine automates enforcement of roles, limits, whitelists, and time constraints, ensuring that even top executives can’t override treasury safeguards.
FAQs
What is “pre-sign” screening in stablecoin payments?
Pre-sign screening in stablecoin payments refers to conducting essential checks before a transaction is signed. These checks include:
Sanctions screening: Ensures transactions comply with international and local regulations.
Policy enforcement: Confirms that the transaction aligns with organizational policies.
Behavioral anomaly detection: Identifies unusual patterns that could indicate fraudulent activity.
Counterparty risk scoring: Assesses the potential risk associated with the other party involved in the transaction.
By performing these checks, pre-sign screening helps maintain compliance and reduce risks. It also provides clear, evidence-based explanations for any flagged issues, ensuring potential problems are addressed before the transaction is executed.
How does real-time enforcement reduce wallet freeze risk?
Real-time enforcement helps reduce the risk of wallet freezes by implementing policy checks and validations before transactions are signed. This proactive approach ensures that issues like exceeding transaction limits, sanctions violations, or unusual activity are flagged early, stopping unauthorized or high-risk transfers in their tracks.
By identifying potential violations before execution, this method protects treasury operations, maintains compliance, and minimizes the likelihood of improper fund movements that could trigger wallet freezes or security breaches.
What policies should a stablecoin treasury enforce first?
A stablecoin treasury should prioritize implementing key policies to ensure secure and compliant operations. Start with transaction limits, approval workflows, and counterparty vetting. For instance, mandate CFO approval for significant payments or transactions involving unfamiliar addresses.
Additionally, incorporate safeguards like sanctions screening, exposure checks, and behavioral anomaly detection before approving any transaction. These steps help minimize risks, maintain compliance, and build a reliable framework for managing treasury activities effectively.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


