
Stablecoins are transforming business payments by offering faster, cheaper alternatives to traditional methods. But their speed and irreversibility create risks, like accidental transfers to compromised wallets or sanctioned entities. Policy blocking addresses these challenges by enforcing rules before transactions are signed, ensuring compliance and reducing errors.
Here’s how it works:
Pre-Execution Controls: Transactions are evaluated against rules (e.g., spending limits, vendor whitelists) before approval.
Policy Engine: Automates checks like sanctions screening and anomaly detection.
Human Review: High-risk payments are flagged for manual approval.
Audit Trails: Every step is logged, creating tamper-proof records for compliance.
Platforms like Stablerail integrate these safeguards, making stablecoin payments secure and aligned with business policies while maintaining efficiency.
Stablecoins to Scale A Compliance Playbook After GENIUS
How Policy-Driven Transaction Blocking Works
Policy-Driven Stablecoin Payment Workflow: From Intent to Settlement
Policy-driven transaction blocking builds on pre-execution controls by introducing a dedicated decision layer that evaluates transactions before they’re signed. This layer operates between the payment request and the final signature, assessing each transaction against predefined rules. Instead of relying solely on authorized signers to decide, this system proactively blocks risky transactions, ensuring compliance and identifying unusual patterns before any funds are moved. It shifts the focus from reactive monitoring to stopping threats before they materialize.
What Policy Blocking Does
At its core, policy blocking enforces transaction rules and approval processes upfront. When a stablecoin payment is initiated, the system generates an intent that undergoes automated checks and, if required, human review. The intent is compared against the organization’s payment policies, resulting in one of several outcomes:
Approve: The transaction complies with all rules.
Deny: The transaction violates a critical rule.
Hold: Manual review is necessary.
Step-up: Additional authentication is required for higher-risk transactions.
Core Components of Policy Blocking Systems
Policy blocking relies on four essential components to enforce rules before transactions are signed:
Policy Engine
This component ensures compliance by enforcing rules like spending limits, roles, whitelists, and time restrictions. For instance, it can enforce policies such as "Transfers over $10,000 on weekends require dual approval" or "Only allow USDC transactions on Base and Ethereum mainnet."
Identity and Credential Layer
This layer verifies the identity and credentials of the initiator, including their KYC/KYB status and ownership proofs, ensuring that only authorized individuals or entities can initiate payments.
Enforcement Layer
It connects the policy decision to the transaction execution mechanism - whether through an MPC (multi-party computation) signing service or a smart contract gate - ensuring no transaction proceeds without meeting the required criteria.
Evidence and Audit Layer
This generates immutable, timestamped Proof-of-Control receipts for every step of the process. These receipts document who initiated the payment, who approved it, the risk assessment, and which policy rules were applied.
Before a transaction is executed, the system performs several automated checks. These include:
Sanctions Screening: Compares the recipient against OFAC and other watchlists.
Taint Analysis: Flags addresses linked to suspicious activity or those that could trigger freezes by stablecoin issuers.
Behavioral Anomaly Detection: Identifies unusual patterns, such as transactions at odd hours or amounts that deviate from typical activity.
Policy Rule Enforcement: Ensures compliance with spending limits, vendor whitelists, and approval hierarchies.
Platforms like Stablerail integrate these checks into a single Risk Dossier that accompanies each payment request. This dossier provides clear explanations in plain language, referencing specific policy clauses and timestamps.
How Human Approvals and Audit Trails Work
For higher-risk transactions, the system directs them to human reviewers after automated checks. Routine payments proceed automatically, but flagged transactions require additional scrutiny and multi-level approval. This ensures transparency and traceability at every step.
The system also incorporates automated delay mechanisms. For example, high-value transfers or payments to new recipients can trigger a time delay (e.g., a 4-hour hold), allowing manual intervention to address potential errors or prevent social engineering attacks. Every action in the process - from intent creation and automated checks to manual reviews, overrides, and final signatures - is documented in a detailed, timestamped audit trail. This ensures compliance with regulatory and audit requirements.
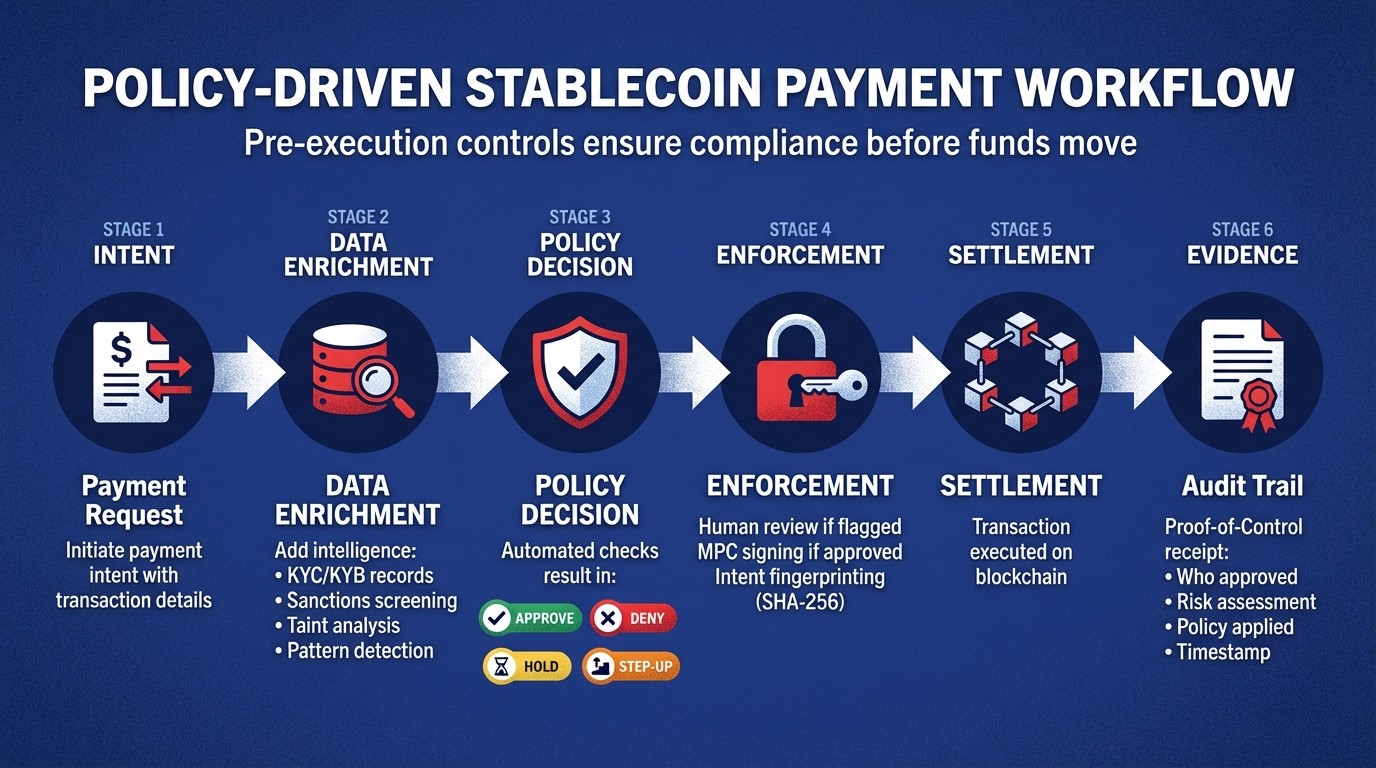
The workflow follows a structured sequence: the payment request (intent) is enriched with risk and identity data, the policy engine makes a decision, the enforcement mechanism either approves or blocks the transaction, the transfer is settled on-chain, and a comprehensive audit log is created. By embedding governance and compliance directly into the transaction process, policy blocking ensures that every stablecoin payment is both secure and aligned with business policies.
How to Design Payment Policies
Creating effective payment policies for stablecoin transactions requires a level of precision and reliability comparable to banking standards. These policies should be encoded as machine-readable logic, ensuring they prevent unauthorized payments, detect irregularities, and uphold compliance - all without hindering legitimate transactions. By replacing manual processes like spreadsheets and email chains with automated policy enforcement, every payment intent can be assessed before any signatures are applied.
Types of Payment Policies and When to Use Them
Payment policies can be categorized based on the specific risks they address. Here are some key types:
Amount threshold policies: These set transaction size limits. For instance, transfers exceeding $100,000 might require dual approvals, while payments over $10,000 on weekends could trigger additional reviews.
Counterparty restriction policies: These limit who can receive funds by using a verified whitelist of approved vendor addresses. Additionally, address-change locks can escalate payments if counterparty details are altered, guarding against substitution fraud.
Time-based policies: These impose temporal restrictions, such as requiring extra approvals for transactions outside business hours or delaying high-value transfers to new beneficiaries.
Chain and stablecoin policies: These specify which networks and tokens are allowed. For example, you might permit only USDC transactions on Base and Ethereum while blocking other chains.
Operation-specific policies: These differentiate between transaction types, such as allowing message signing but restricting asset transfers or permitting staking only when lock-up periods exceed 24 hours.
Here’s a quick reference table summarizing these policies:
Policy Type | Practical Example | Primary Use Case |
|---|---|---|
Amount Threshold | Transfers over $100,000 require dual approval | Prevent unauthorized large payments |
Counterparty Restriction | Only allow payments to pre-approved vendor addresses | Protect against address substitution fraud |
Time-Based | Weekend transfers over $10,000 need CFO review | Detect unusual timing patterns |
Chain/Stablecoin Limit | Restrict to USDC on Base and Ethereum only | Maintain operational consistency |
Operation-Specific | Block asset transfers but allow message signing | Separate signing authority by action type |
These policies work together to strike a balance between security and efficiency.
How to Balance Security and Speed
Designing payment policies isn’t about creating rigid "allow" or "deny" rules. Instead, it’s about implementing flexible systems that adapt to the risk level of each transaction. For example, routine payments can be automated, minor anomalies might require single approval, and high-risk transactions could demand dual approval. Introducing automatic cool-off periods - like delaying high-value transfers or payments to new beneficiaries for four hours - adds a safety net, giving teams time to identify social engineering attempts or correct errors before funds are released.
This tiered approach ensures that standard transactions proceed quickly, while higher-risk scenarios introduce intentional friction where it’s most needed.
“Governance is a design problem, not a headcount problem: Adding approvers creates bottlenecks and diffuses accountability.”
By focusing on smart design rather than increasing complexity, organizations can enhance both security and efficiency.
How to Integrate Policies into Existing Workflows
To integrate these policies seamlessly, start by categorizing payment intents - such as payroll, vendor payments, or treasury sweeps - and tailor rules to fit each category. A one-size-fits-all approach often creates unnecessary obstacles for routine tasks while overlooking risks in specialized workflows.
Begin by mapping your current approval and payment processes, then translate these governance steps into automated, machine-enforceable rules. Tools like Stablerail simplify this process by providing policy consoles where finance teams can define rules in plain language. For example, a rule like "New address payments over $5,000 require CFO approval + verification" can be turned into an automated check that the system enforces before any signature is requested.
Maintaining a golden source whitelist of verified vendors and implementing address-change locks ensures that any alteration to counterparty details triggers automatic escalation. This mirrors the manual verification steps finance teams already perform but embeds them directly into the workflow, creating an audit trail that documents the rationale behind every payment decision.
How to Implement Pre-Execution Checks
Pre-execution checks take policy-driven transaction blocking to the next level, securing stablecoin payments by addressing risk and compliance before funds are transferred. These checks transform stablecoin transactions into structured, auditable workflows that can identify fraud, policy breaches, or compliance issues before any cryptographic signature is applied. This is critical because once a stablecoin transaction is recorded on-chain, there’s no going back.
The Payment Workflow: From Intent to Execution
The modern payment process unfolds in a clear sequence: Intent → Data Enrichment → Policy Decision → Enforcement → Settlement → Evidence. It all begins when someone initiates a payment intent. This could mean uploading a file of vendor payouts, submitting an invoice for approval, or triggering a request via API. The system captures the necessary payment details and checks them against predefined policies.
Next is data enrichment, where the system adds critical intelligence. This involves pulling identity data (like KYC/KYB records), running sanctions and taint checks to flag risky parties, and analyzing historical transaction patterns to detect anomalies. For instance, if a vendor typically receives $5,000 monthly but suddenly requests $50,000, the system flags this as unusual. All of this happens automatically and in milliseconds.
Finally, the process moves to enforcement and settlement. If the transaction passes all checks, it proceeds to signing via MPC (multi-party computation) wallets. Here, key shares are assembled only after policy approval. If the transaction is flagged, it’s held for human review. Once signed, the system creates a Proof-of-Control receipt, which serves as an audit-ready record detailing the transaction: what was paid, why, who approved it, and which policy was applied. This workflow seamlessly combines automated policy enforcement with robust controls, paving the way for detailed risk reporting.
How Risk Dossiers and Policy Enforcement Work
Before any cryptographic signature is requested, the system produces a Pre-Flight Risk Dossier. This document summarizes all the check results in plain language, offering clear outcomes: PASS, FLAG, or BLOCK, each backed by evidence.
Each outcome includes detailed explanations. For example, a flagged transaction might note: "First-time destination address; vendor onboarded 3 days ago; payment amount 400% above baseline." This level of transparency enables approvers to quickly make informed decisions without needing to dig through additional data. The dossier also creates a reliable audit trail that can withstand regulatory scrutiny.
To ensure integrity, intent fingerprinting is used. By applying SHA-256 hashing, any changes made after the dossier’s approval will invalidate the transaction. This "two-gate architecture" ensures both the policy logic and the cryptographic integrity are verified before funds are moved. The risk dossier directly informs the human review and MPC signing process, ensuring compliance and security at every step.
How Human Approval and MPC Signing Work
Once the policy engine issues its decision and the risk dossier is ready, the process combines human oversight with cryptographic safeguards. Transactions with a "PASS" verdict proceed automatically, while flagged payments require human review. Approvers must examine the dossier, provide a clear override reason if approving, or reject the transaction outright. This rationale is permanently logged as part of the audit trail.
For approved transactions, the process moves to multi-party computation (MPC) signing. Cryptographic key shares are distributed across multiple parties, ensuring no single individual has full control of the treasury. Platforms like Stablerail integrate this into a streamlined "Approve & Sign" process. Once the key shares are assembled and the signature is executed, the system logs every detail: who signed, when, under which policy, and the risk verdict. This creates an immutable record that satisfies auditors, regulators, and boards while maintaining the speed and efficiency of blockchain settlement.
How to Maintain Compliance and Audit Readiness
Policy blocking transforms stablecoin payments into structured, auditable workflows, embedding compliance directly into the payment process. This approach shifts from manual, after-the-fact monitoring to real-time, machine-enforced policy layers. It's a model often referred to as "compliance-as-infrastructure", where regulatory requirements are baked into every transaction.
Regulatory Requirements for Stablecoin Payments
Stablecoin transactions come with a host of compliance requirements, and automated systems step in to meet these obligations seamlessly. For example, AML screening ensures real-time checks against sanctions lists from OFAC, the EU, and the UN before a transaction is approved. Similarly, the Travel Rule mandates that originator and beneficiary details be captured and shared for transfers over $3,000. By embedding this data directly into transaction workflows, these requirements are met without manual intervention.
A real-world example of this is MoneyGram's adoption of USDC on the Stellar Network in early 2026. This system, which serves 50 million people globally, was integrated with existing AML processes in just over two months. Since its launch, it has maintained zero compliance incidents. The GENIUS Act in the U.S. has further clarified the regulatory landscape, with Treasury Secretary Counselor Tyler Williams calling it "a roadmap for what we want to accomplish", offering clear guidance for stablecoin issuers and payment processors.
Platforms like Stablerail automate these checks, ensuring no transaction moves forward unless it complies with all regulatory requirements. This preemptive approach eliminates the risk of violations before they occur.
How to Prepare for Audits and Regulatory Reviews
A solid audit trail is crucial for compliance. Capturing metadata at every stage of a payment provides a clear, defensible record. This includes details like payment intent (who initiated it, the amount, and its purpose), contextual data (jurisdiction and risk tier), the policy version applied, and the final decision with human-readable reason codes. If a transaction is blocked, the system logs the specific policy clause that caused the denial, creating a "deterministic audit path" that auditors can easily follow.
Proof-of-Control receipts further strengthen compliance by documenting each payout's specifics - amount, approvers, risk assessment, and applied policies. These receipts link directly to the on-chain transaction hash, timestamp, and status, proving enforcement rather than mere documentation. Auditors can even replay historical decisions using the same inputs and policy versions to confirm consistent compliance.
To ensure records remain tamper-proof, decision logs are stored in systems separate from the blockchain. This hybrid approach - off-chain policy enforcement for speed and on-chain constraints for transparency - provides both flexibility and strong auditability as regulations evolve.
How to Handle Cross-Border Payments and Global Compliance
Cross-border payments add another layer of complexity due to varying regulations across jurisdictions. For example, the UK's Bank of England caps individual holdings at £20,000 and business holdings at £10 million, while Brazil enforces enhanced reporting for payments over $100,000. Meanwhile, the EU's MiCA framework, fully implemented in 2025, allows companies to "passport" their authorization across member states, although reserve and redemption rules differ by region.
To navigate these complexities, jurisdiction-aware routing ensures each payment complies with local rules. The policy engine screens transactions for regional restrictions and selects the appropriate blockchain or stablecoin asset based on the sender's and receiver's locations. Instead of simple yes-or-no decisions, many systems use tiered outcomes - like placing a "hold" or requiring additional verification for medium-risk transactions. For instance, high-value payments (over $100,000) or those to new beneficiaries might face smart cool-off periods, delaying execution for manual review and reducing risks like social engineering.
Clear separation of duties further enhances compliance and accountability. Payment requesters, approvers, and signers each have distinct roles, and any overrides must include documented justifications. These justifications become part of the permanent audit trail, addressing insider risks while meeting regulators' expectations for detailed exception handling.
Conclusion
Policy-driven transaction blocking transforms stablecoin payments from quick yet risky transfers into structured, auditable workflows that align with corporate governance requirements. By enforcing checks before transactions are signed, finance teams can avoid the irreversible mistakes often associated with on-chain transactions. This proactive approach shifts compliance from post-transaction monitoring to real-time enforcement, ensuring decisions are compliant before any funds are moved.
A key benefit of this system is its layered defense strategy, where immutable, machine-enforced policies guide every transaction. Tools like Stablerail provide Proof-of-Control receipts, which document critical details such as who approved the transaction, the policy version applied, and the reasoning behind the payment's approval. This creates a clear audit trail that regulators and boards can easily verify.
Operational risks are further mitigated through pre-execution checks, which simulate payments before they are broadcast. These checks can identify tainted counterparties that may lead to stablecoin issuer freezes. For companies experimenting with autonomous AI agents to handle treasury operations, these safeguards are especially crucial.
The system succeeds by separating policy creation from execution. Finance teams can define rules like spending limits, allowlists, and jurisdictional restrictions in simple terms, which are then converted into machine-enforceable policies. While low-risk transactions proceed automatically for efficiency, higher-risk payments can trigger delays or require additional approvals.
This approach goes beyond being a security measure - it lays the groundwork for secure and efficient treasury operations on the blockchain. By integrating these controls, corporate finance teams can harness the speed and transparency of blockchain settlements without compromising on governance standards.
FAQs
What’s the difference between policy blocking and post-transaction monitoring?
Policy blocking is all about stopping issues before they even happen. It works by applying enforceable rules - like predefined limits, required approvals, or compliance checks - before a transaction is signed. This ensures that only transactions meeting the necessary criteria are allowed to move forward.
On the other hand, post-transaction monitoring kicks in after the transaction is completed. It helps identify suspicious behavior or irregularities through tools like anomaly detection or risk scoring. While monitoring is useful for oversight, policy blocking takes a proactive approach by preventing non-compliant transactions right at the decision-making stage.
How do pre-execution checks stop payments to sanctioned or tainted wallets?
Pre-execution checks act as a safeguard by blocking payments to wallets that are flagged as sanctioned or associated with illicit activity. These checks enforce mandatory compliance reviews before any transaction is signed. This process includes steps like sanctions screening, exposure analysis, and policy verification. By identifying and flagging high-risk wallets in advance, these measures ensure that such transactions are halted before they can move forward.
What happens when a stablecoin payment is flagged or held for review?
When a stablecoin payment is flagged or put on hold for review, the system performs several pre-execution checks. These include steps like enforcing policies, screening for sanctions, and analyzing behavioral patterns. Every action is logged in a detailed audit trail, allowing human reviewers to step in and either approve, override, or block the transaction. This process ensures that decisions are made with documented evidence, promoting both compliance and transparency.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


