
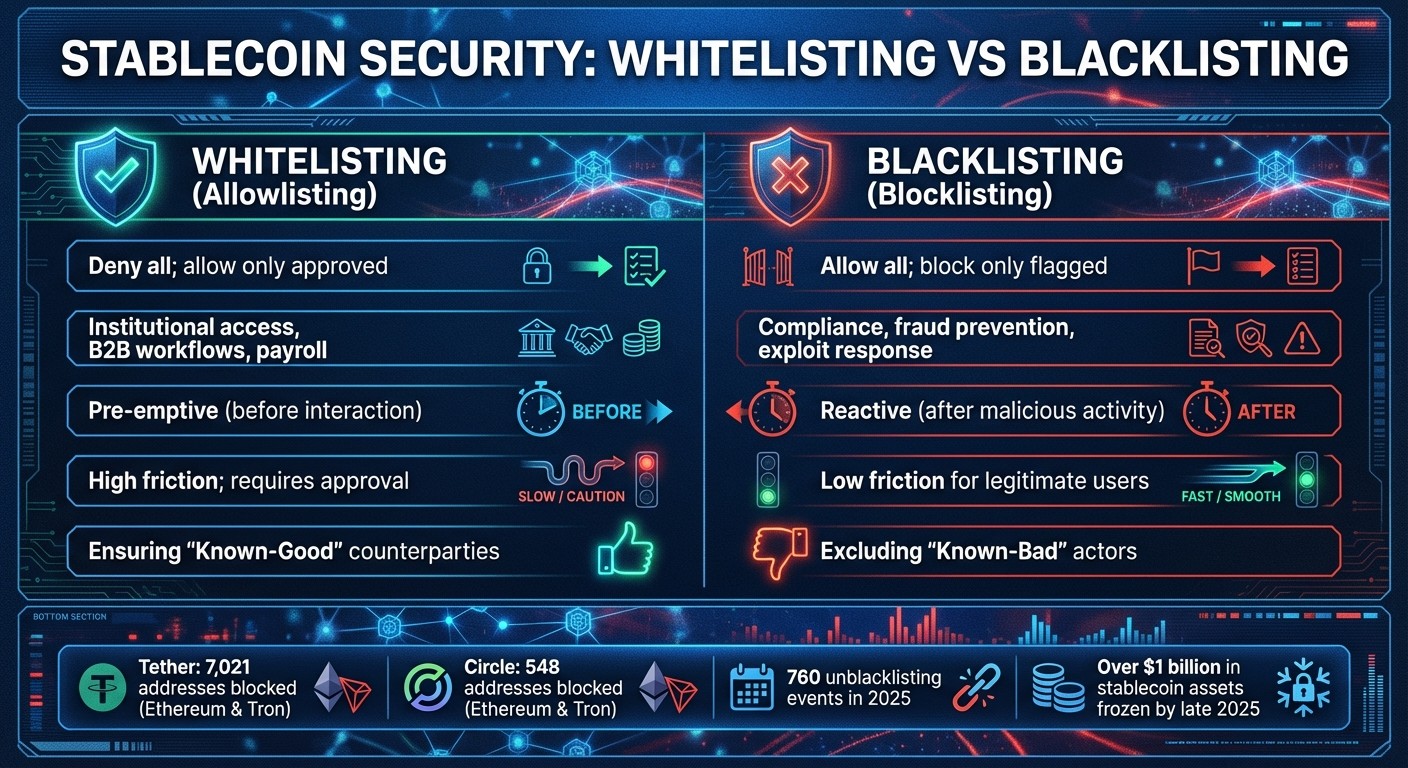
When managing stablecoins, ensuring security and compliance is non-negotiable. Whitelisting and blacklisting are two key tools to control transactions and protect assets. Whitelisting allows only pre-approved addresses to interact, minimizing errors and fraud. Blacklisting blocks flagged addresses, helping recover stolen funds and comply with regulations.
Key Takeaways:
Whitelisting: Pre-approves addresses for transactions, ideal for payroll, vendors, and high-value operations.
Blacklisting: Blocks malicious addresses or performs sanctions screening, often used in response to hacks or fraud.
Combined Use: Many institutions use both methods for layered security.
Real-Time Monitoring: Static lists are insufficient; real-time tools like Chainalysis or TRM Labs enhance effectiveness.
Compliance: Adhering to AML/CFT regulations and creating audit trails is critical.
By late 2025, over $1 billion in stablecoin assets were frozen, highlighting the importance of proactive controls. Using tools like policy-as-code and automated checks can help prevent non-compliant transactions before they occur.
[SCOPE] All-in-One Platform for Stablecoin Business
What Are Whitelisting and Blacklisting in Stablecoin Operations?
Whitelisting vs Blacklisting: Key Differences in Stablecoin Security
Address control systems rely on two contrasting methods: whitelisting (only allowing approved addresses to interact) and blacklisting (blocking specific addresses while permitting all others). These approaches are essential for securing stablecoin treasuries, and many institutional operations combine both strategies to enhance security.
What Is Whitelisting?
Whitelisting, sometimes called allowlisting, restricts transactions to a list of pre-approved addresses. Think of it as an exclusive guest list: if an address isn’t on the list, it’s barred from participating. This method is widely used in institutional payment systems, private networks, and business-to-business (B2B) settlements.
For example, a corporate treasury might maintain a whitelist that includes verified vendor wallets, employee payroll accounts, and partner exchanges. Any attempt to send funds to an unapproved address is automatically blocked. This reduces the risk of accidental transfers or fraud. However, whitelisting does introduce some friction - new addresses must go through a formal approval process, and high-value transfers often require a waiting period for added security.
While whitelisting is proactive, it’s often complemented by reactive measures like blacklisting.
What Is Blacklisting?
Blacklisting, also referred to as denylisting or blocklisting, operates in the opposite way. By default, all addresses are allowed unless they’ve been flagged as malicious, fraudulent, or sanctioned. This method is a key tool for stablecoin issuers when responding to hacks, phishing schemes, or regulatory directives.
For instance, Tether has blocked 7,021 addresses on Ethereum and Tron, while Circle has restricted 548 addresses on the same networks. A notable example occurred in mid-2025 when Tether blacklisted over 800 addresses on the Tron network in a single day to counter spam and phishing attacks. Once an address is blacklisted at the protocol level, the issuer’s smart contract prevents any transactions involving that wallet, effectively freezing the funds. These blacklisting actions work alongside whitelisting to strengthen overall treasury security.
Why Address Control Systems Matter
Address control systems play a critical role in both regulatory compliance - such as adhering to AML/CFT and OFAC sanctions - and operational safety. Whitelisting minimizes errors, like sending funds to a mistyped address or the wrong network. Blacklisting, on the other hand, allows issuers to freeze stolen assets before they’re laundered through mixers or cross-chain platforms.
Take the Multichain hack in July 2023 as an example. Stablecoin issuers managed to freeze $66 million of the $126 million stolen within hours by blacklisting the attacker’s addresses. Interestingly, data shows that only 0.04% of frozen funds (about $419,320) are tied to OFAC-sanctioned addresses, suggesting that most blacklisting is driven by internal risk assessments rather than government mandates.
How to Implement Blacklisting
Using Sanctions Lists and Taint Analysis
Creating an effective blacklist goes beyond simply importing OFAC's Specially Designated Nationals (SDN) list into your system. Static sanctions lists, which cover just 36.4% of OFAC-sanctioned addresses, fall short when compared to the speed and precision of real-time taint analysis from blockchain intelligence tools. Bad actors frequently rotate wallets and fragment funds at a pace that outstrips the monthly updates of traditional lists.
A robust blacklist combines official sanctions lists with real-time taint analysis. Start by incorporating data from OFAC and other regulatory bodies, then enhance it with blockchain intelligence from providers like TRM Labs, Chainalysis, and Elliptic. These tools trace the entire lifecycle of funds, flagging assets linked to mixers, darknet markets, or exploit addresses. For instance, the T3 Financial Crime Unit - a collaboration between TRON, Tether, and TRM Labs formed in September 2024 - has frozen over $200 million in illicit assets by merging regulatory data with active threat intelligence.
"Blacklisting is not driven by regulatory lists alone. Instead, issuers appear to rely on internal risk detection, incident reports, or ecosystem feedback." - Range Research
Real-time screenings are crucial for effective enforcement. Static lists updated monthly can't keep up with attackers who move funds across chains or through intermediaries. For example, after the Bybit hack in September 2025, security team zeroShadow tracked $30 million in stolen Ether across more than 350 new addresses. By coordinating with issuers, they froze the assets before they reached over-the-counter desks. This kind of integrated approach allows for swift and actionable enforcement, as demonstrated in real-world scenarios.
Examples of Blacklisting in Practice
In mid-2025, Tether executed the largest single-day blacklisting event on record, freezing over 800 Tron addresses to combat phishing and spam attacks. This large-scale enforcement highlights the operational demands of blacklisting and underscores the need for a formal appeals process, especially as unblacklisting events are observed.
Circle, on the other hand, employs a more selective strategy. On Solana, where enforcement is less common, Circle reversed four blacklisting decisions between 2024 and 2025, making it the only network with confirmed rollback activity during that time. This underscores an essential point: blacklisting systems must include a structured appeals process. Across all networks, 760 unblacklisting events were recorded in 2025, often triggered by law enforcement requests, operational errors, or abandoned cases.
The lag between detection and enforcement remains a significant issue. In 2025, over 6,000 blacklisted addresses had no balance at the time of enforcement because the funds had already been moved. In one case, TRM Labs helped a major financial institution recover more than $25 million stolen from a bank customer. Their success hinged on real-time collaboration with Virtual Asset Service Providers to freeze assets before they were cashed out. These examples highlight the need for a dynamic, continuously updated blacklist.
Operating and Maintaining Blacklists
Blacklisting isn’t a one-and-done task - it requires ongoing monitoring and systematic updates. The most effective systems have shifted from reactive responses to proactive measures, integrating automated screening into transaction workflows rather than relying on periodic checks.
To prevent errors or abuse, enforce dual-approval maker-checker controls, ensuring no single operator can alter the blacklist. Use test-specific magic value suffixes (like 9999 for sanctions) to validate screening rules before deployment.
Malicious actors often move funds from a blacklisted address on one blockchain to an active address on another, necessitating cross-network monitoring. To address this, modern treasury operations are adopting policy-as-code governance. This approach automatically triggers actions like "REVIEW" or "FREEZE_WALLET" based on predefined rules, creating an auditable trail for every decision. Integrating blacklist updates into treasury workflows strengthens governance and meets stablecoin compliance requirements, a critical aspect of securing stablecoin transactions.
For finance teams managing large-scale stablecoin payments, platforms like Stablerail streamline the process by integrating sanctions and taint screening directly into pre-transaction checks. Before any payment is approved, the system runs automated screenings against current blacklists and provides clear, plain-English explanations of any flags. These include policy details and timestamps, ensuring compliance with audit standards.
How to Implement Whitelisting
Building a Whitelist Framework
Creating a whitelist involves developing an address book that categorizes approved counterparties by name, network, and purpose. Unlike blacklisting, which reacts to threats, whitelisting operates on a default-closed model - no transactions are allowed unless explicitly approved through a structured process.
Each address added to the whitelist should undergo thorough Know Your Customer (KYC) checks, sanctions screening, and documentation of its business purpose. For example, a whitelisted address might correspond to a vendor invoice ID, a payroll batch, or a recurring service agreement. Every address must serve a clear, documented purpose.
To prevent internal errors or fraud, adopt a maker-checker model with a cooling-off period of 24–48 hours before activating a new address. One team member submits the request with required documentation, and another approves it.
Network-specific rules are also critical. For instance, an Ethereum address on the mainnet may not function properly on other blockchains like Solana or Tron. Your framework should specify which networks each address is approved for and tag entries with metadata such as "Lifetime Volume", "Last KYC Date", or "Risk Tier" to support dynamic policy enforcement.
For larger operations, platforms like Stablerail can automate and audit whitelist enforcement. Rules can be set up, such as requiring CFO approval for payments exceeding $5,000 or restricting certain transactions to specific tokens like USDC on Base/Ethereum. Transactions that don't meet these criteria are blocked automatically, and every change to the whitelist generates an immutable audit trail with timestamps and approver details.
While whitelisting enhances security, it does come with trade-offs, particularly in terms of operational speed.
Security vs. Flexibility Trade-offs
Whitelisting offers unparalleled security by blocking unauthorized transactions before they occur, but it can slow down operations. In this model, every new counterparty must go through a formal approval process before funds can be transferred, which may delay urgent payments or complicate participation in decentralized finance (DeFi) protocols.
"The whitelist model delivers the highest level of AML/CFT control, enabling proactive prevention instead of reactive remediation."
– SlowMist Security Team
To strike a balance between security and efficiency, consider a tiered wallet system. Apply strict whitelisting to "Cold/Reserve" wallets, which hold the majority of funds and require multi-signature approval for transactions. For "Warm/Operations" wallets, which handle routine payments like payroll or vendor invoices, use more flexible controls. In some cases, strict whitelisting can essentially turn stablecoins into a closed ledger, limiting their use as a freely circulating currency. Because of this, many issuers use a hybrid approach - employing blacklists for general circulation while reserving whitelisting for critical tasks like minting, large redemptions, or handling newly minted tokens.
Operational friction can also be minimized by pre-approving known entities such as major exchanges, trusted liquidity providers, or frequent vendors. This allows compliance teams to focus on genuinely suspicious activity rather than reviewing every routine transaction. In fact, using an intelligent whitelisting system can reduce false-positive alerts by up to 93%.
These trade-offs are further shaped by evolving regulatory requirements.
Regulatory Requirements for Whitelisting
Regulators around the world are increasingly mandating or encouraging whitelisting as part of anti-money laundering (AML) and countering the financing of terrorism (CFT) compliance. For instance, the FATF Travel Rule requires both originator and beneficiary data for transactions, which a robust whitelist can help ensure. Maintaining a verified whitelist with full KYC documentation ensures that all payments include the necessary details.
In September 2025, Singapore's Monetary Authority (MAS) introduced rules requiring stablecoin issuers to return the par value of regulated stablecoins within five business days of a redemption request. To comply, issuers like StraitsX, which launched the XSGD stablecoin on Coinbase in October 2025, maintain reserves at financial institutions such as DBS and Standard Chartered. Their framework includes strict address controls and mandatory disclosures.
Similarly, Hong Kong's HKMA is introducing enhanced token standards that require administrative functions like whitelisting and freezing capabilities to be built into smart contracts. In such jurisdictions, whitelisting becomes a regulatory necessity, enforced through programmable policy engines.
"Compliance is still treated as a matter of paperwork, not of live, verifiable enforcement."
– Newton Protocol Litepaper
Beyond geographic regulations, certain activities - like handling securities-like instruments, cross-border payments to high-risk regions, or integrating with traditional banking systems - trigger stricter compliance standards. Regulators now expect continuous assurance, not just periodic audits. This means your whitelisting system must produce cryptographic receipts and tamper-proof logs for every transaction as real-time evidence of compliance.
Ongoing screening is also crucial. Even after an address passes initial verification, circumstances can change. Continuously check whitelisted addresses against updated sanctions lists, politically exposed person (PEP) databases, and risk categories like terrorist financing or gambling. Every change should generate on-chain event logs to create an immutable audit trail.
For high-security roles, consider generating keys in air-gapped environments and storing them in Hardware Security Modules (HSMs). Such precautions are vital in an industry where global compliance spending exceeds $274 billion.
Adding Address Controls to Treasury Workflows
Integrating whitelisting and blacklisting directly into payment workflows ensures that documented rules are followed and provides a clear, auditable reconciliation process. Finance teams should manage their stablecoin treasuries as if they were an operating system - complete with enforceable rules, permissions, and a transparent reconciliation process - rather than treating them as simple wallets holding funds. The key is to apply these controls during the pre-sign phase.
Pre-Transaction Checks and Address Verification
The pre-sign phase is critical. This is the moment between creating a transaction and broadcasting it to the blockchain - an ideal time to enforce address controls. Automated screenings can check addresses against sanctions lists, evaluate risk scores, and analyze behavioral patterns.
Before signing, it’s essential to conduct real-time AML (Anti-Money Laundering) and KYT (Know Your Transaction) checks. These checks can flag issues like sanctions exposure, illicit activity, or tainted funds. For high-risk cases, a small test transfer - such as $1 - can verify receipt before proceeding. If an address is flagged with a "severe sanctions risk", the system should automatically place the transaction on hold, requiring manual review. This "verify-before-send" approach helps avoid irreversible mistakes. Once a transaction is broadcast to the blockchain, there’s no undoing it.
To minimize internal fraud or errors, adopt a maker–checker model. This divides responsibilities among team members for initiating, preparing, approving, signing, and reconciling transactions. Adding a 24–48 hour cooling-off period for whitelist changes further enhances security.
Policy-as-Code Governance
Manual compliance methods are unsustainable as transaction volumes grow. Finance teams need machine-readable policies that can be automatically enforced during execution - before a transaction is signed or gas fees are spent on transfers that might ultimately be blocked.
Policy-as-code translates business rules into automated logic, ensuring non-compliant transactions are stopped before they’re executed. If a transaction violates any rules, it’s blocked, and the requester receives a clear explanation of the issue.
Platforms like Stablerail allow finance teams to set these rules through a Policy Console, where thresholds, approval requirements, and network restrictions can be defined. For instance:
Payments to new addresses over $5,000 may require CFO approval and verification.
Transactions involving addresses flagged for sanctions exposure can be automatically blocked.
Transfers exceeding $1,000 may require travel-rule metadata.
These policies are enforced in real time before signing, creating pre-execution controls that prevent non-compliant transactions from reaching the blockchain. This shift from post-trade paperwork to proactive enforcement is critical, especially given that global compliance spending surpassed $274 billion in 2023.
"Compliance must shift from retrospective paperwork to pre-trade and in-flight controls."
– Newton Protocol
Policy-as-code also enables continuous assurance. Instead of relying on annual audits or periodic reviews, every transaction is evaluated against the latest rules. This generates cryptographic proof of compliance, creating a tamper-proof record that auditors and regulators can independently verify.
With automated policies in place, it’s crucial to document every step to demonstrate compliance.
Creating an Audit Trail
Even the most advanced address controls are incomplete without a robust audit trail. A comprehensive record is essential to address disputes, investigations, or regulatory reviews. Every stablecoin transaction should produce a CFO-grade evidence package that ties on-chain data to business references.
Each transaction must include its hash, timestamp, asset details, business reference, approval log, and reconciliation entry. This transforms raw blockchain data into "finance-ready" records that auditors can easily interpret.
Platforms like Stablerail automatically generate these audit trails. From the moment a payment intent is created, the system logs the requester, business justification, and initial risk screening results. As the transaction moves through approvals, each action - policy checks, flags, overrides, and signatures - is timestamped and cryptographically signed. The final output is a CFO-grade evidence package, ready for auditors, boards, or regulators without requiring manual reconstruction.
"If your system cannot generate an evidence bundle for each payout, you will struggle under audit, disputes, or investigations."
– Stablecoin Insider
Audit trails also play a vital role in unblacklisting. By late 2025, there had been 760 unblacklisting events across major chains - 381 on Tron, 375 on Ethereum, and 4 on Solana - underscoring the importance of documented appeals and reversal procedures. When an address is removed from a blacklist, the audit trail should include the rationale, supporting evidence, and the identity of the approver to ensure the decision is defensible.
To comply with the FATF Travel Rule, modern audit trails must also incorporate encrypted metadata. This metadata should include originator and beneficiary identifiers for cross-border transfers. For transactions above the threshold (usually $1,000), this ensures regulatory requirements are met without exposing sensitive information on-chain.
Conclusion
To effectively manage and calculate risks and ensure compliance in stablecoin operations, it's essential to combine whitelisting and blacklisting with real-time risk management, automated policies, and audit trails. By late 2025, over $1 billion in stablecoin assets had been frozen on-chain, and more than 6,000 blacklisted addresses had no balance at the time of enforcement due to delays in the detection-to-action process. This lag highlights the limitations of reactive controls.
Adopting a compliance-as-code approach embeds machine-readable policies into pre-sign workflows, stopping non-compliant transactions before they occur. This proactive method is crucial, especially since only 36.4% of OFAC-sanctioned stablecoin addresses have been successfully blacklisted on-chain. Together, whitelisting, blacklisting, and policy-as-code create a more robust control framework.
Implementing separation of duties is another critical step - ensuring that no single person can request, approve, and execute payments reduces the risk of internal fraud and errors. These practices establish a solid foundation for internal controls, which are increasingly necessary as cross-chain risks grow.
Cross-chain visibility also remains a significant challenge. Malicious actors often exploit gaps between networks, transferring funds from Ethereum to Solana or Tron to bypass single-chain blacklists. Addressing this requires real-time monitoring and tracking across ecosystems to maintain effective controls across all networks where an organization operates.
FAQs
How do whitelisting and blacklisting improve stablecoin security?
Whitelisting and blacklisting work hand in hand to establish a secure framework for stablecoin transactions. A whitelist includes approved addresses, ensuring funds are only sent to verified recipients like trusted vendors or established partners. Meanwhile, a blacklist flags prohibited addresses, such as those tied to fraud, sanctions, or compromised wallets, automatically blocking any transactions involving them.
When used together, these measures allow organizations to implement strict payment rules while minimizing exposure to risky activities. Platforms like Stablerail leverage this dual-list strategy, letting finance teams set policies that mandate whitelist approvals and blacklist screenings before processing payments. This creates an automated, real-time system that pairs the speed of blockchain technology with strong compliance protocols.
How can I monitor whitelisted and blacklisted addresses in real time?
Real-time tracking of approved (whitelisted) and restricted (blacklisted) addresses is possible with a compliance engine that evaluates every on-chain transaction as it happens. These tools automatically compare transactions and destination addresses against established rules, flagging or blocking any that don't align with your policies - often within seconds.
Integrating these tools into your payment processes means every transaction - whether it's triggered by an invoice, a CSV payout, or an API - gets screened before being signed. This approach not only ensures adherence to your policies but also preserves the speed and efficiency of on-chain settlements. Plus, it creates a transparent audit trail for every decision made along the way.
Why is AML/CFT compliance essential for stablecoin operations?
Compliance with anti-money-laundering (AML) and counter-terrorist financing (CFT) regulations is critical for stablecoin operations. These digital assets are frequently used for high-value, cross-border payments, which means they must adhere to the same strict regulatory standards as traditional financial transactions. Falling short of these requirements can have serious repercussions, including sanctions, frozen assets, legal fines, and a loss of trust from both users and business partners.
To meet these standards, stablecoin issuers and operators use on-chain controls like blacklisting wallets associated with sanctioned entities. These measures are designed to deter illegal activities, safeguard the financial system, and uphold market integrity. In the U.S., regulations such as the GENIUS Act require stablecoin operators to implement robust compliance programs, making AML/CFT compliance not just a best practice but a legal obligation.
Platforms like Stablerail offer built-in solutions for compliance by incorporating pre-sign checks - such as sanctions screening, risk assessments, and policy enforcement - directly into transactions. This approach ensures regulatory adherence without compromising the speed and efficiency that on-chain payments are known for.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


