
Policy-as-code transforms compliance for stablecoin transactions by automating sanctions screening through machine-readable rules. This approach ensures payments are blocked before execution, reducing risks like regulatory fines and frozen accounts. Here's the core idea:
What it does: Converts compliance rules into automated checks, applied in real-time.
How it works: Screens wallet addresses and transaction details against sanctions lists (e.g., OFAC SDN) before funds are transferred.
Why it matters: Stablecoins settle in seconds, making traditional manual reviews too slow.
Benefits:
Speed: Instant compliance checks.
Accuracy: Eliminates human error.
Auditability: Creates tamper-proof records for regulators.
Core Components of Policy-as-Code Sanctions Screening
Data and Inputs for Screening
For a policy-as-code system to effectively screen transactions, it relies on a variety of data inputs - wallet addresses, transaction details, identity metadata, and system parameters. Each of these plays a key role in ensuring compliance and identifying potential risks.
Wallet addresses are the starting point. Every screening begins by cross-checking sender and recipient addresses against blocklists and sanctions databases. These checks are performed in real time, with some systems updating data from OFAC's Specially Designated Nationals (SDN) list every 2 to 5 minutes to catch newly added entities. Transaction metadata, such as the dollar amount, asset type (e.g., USDC, USDT), and transfer direction (inbound or outbound), adds further context to the screening process. Identity metadata links wallets to real individuals or organizations through details like KYC (Know Your Customer) verification status, jurisdiction, risk level, and investor eligibility.
For cross-border transactions, additional Travel Rule data is required. This includes information about the originator and beneficiary, as mandated by FinCEN regulations. To simulate risk scenarios during testing, systems use "Magic Values." For instance, Circle’s testnet flags addresses ending in 9999 as hits for sanctions and 8889 for CSAM-related risks.
Once these inputs are in place, they serve as the foundation for creating actionable, codified rules.
Defining and Executing Codified Rules
Sanctions policies are translated into machine-readable JSON structures that define how they are enforced. These policies specify the scope (whether they apply to a project or a specific account), the operation (e.g., signEvmTransaction or transfer), and the criteria (e.g., ethValue <= 1 ETH or address not in OFAC list).
The actual enforcement happens via function hooks. For example, when a smart contract's transfer function is called, the system pauses to query a compliance oracle. This oracle returns a simple boolean flag (e.g., isSanctioned(address)); if the result is positive, the transaction is immediately blocked. In March 2024, the Plume Network became the first public blockchain to implement sequencer-level AML screening. During a millisecond-long simulation, transaction details are sent to the Forta Firewall API. If an address flagged by OFAC is detected, the Plume RPC drops the transaction before it even reaches the mempool.
"The code doesn't rely on someone to flag a breach later; it makes the breach impossible in the first place." – Natalia Latka, Head of Regulatory Affairs, ComPilot
For sanctions lists that are updated frequently, teams use signature gating. This lightweight compliance layer applies screening logic before a treasury's private keys approve a transaction, avoiding the need to redeploy smart contracts whenever a rule changes. These automated processes ensure that pre-transaction checks catch any issues before a payment is authorized.
Pre-Transaction Control Points in Stablecoin Payments
The most effective point to enforce controls is before signing. Once a transaction is signed and broadcast to the blockchain, it's too late to intervene. Pre-signing evaluations act as the final checkpoint, ensuring all policies - such as sanctions, spending limits, and counterparty risks - are adhered to before authorization.
Stablerail addresses this by operating above custody and before signing occurs. When a payment intent is created, the system runs mandatory checks, including sanctions screening, policy enforcement, and behavioral anomaly detection. A Risk Dossier is then generated, offering a verdict (PASS, FLAG, or BLOCK) along with plain-English explanations. The MPC wallet only signs the transaction after human approval, ensuring that no sanctioned payment is processed, even if the wallet software has been compromised.
Organizations managing their own infrastructure can implement custom RPC interception to enforce similar policy checks. Transactions pass through a security-focused RPC layer that screens them against dynamic blocklists before they are broadcast to the network. Testing these controls is straightforward: using eth_simulateTransaction, teams can simulate routing decisions (Allow, Block, or Flag) without incurring gas fees or risking failed on-chain transactions. These measures provide a secure and efficient way to ensure compliance while maintaining operational flexibility.
Designing a Policy-as-Code Architecture
Reference Architecture for Stablecoin Treasury Governance
A well-structured policy-as-code architecture for sanctions screening rests on three interconnected layers. At its foundation are self-custodial wallets, often using MPC (multi-party computation) technology, designed to securely manage funds across blockchains like Ethereum, Base, and Polygon. Above this lies an agentic control plane that evaluates policies in real time. Finally, a data integration layer links to live sanctions screening tools - such as Chainalysis or TRM Labs - to cross-check addresses against the OFAC SDN lists.
This setup operates on a deny-by-default approach, meaning transactions are automatically blocked unless they explicitly align with trusted criteria. The policy engine processes high-volume transactions against customizable JSON-based guardrails using expression languages like expr. This allows financial teams to fine-tune business logic without the need to redeploy code.
"Policies are defined as JSON documents and executed with the expr expression language so teams can ship granular business logic without redeploying code." – fystack/programmable-policy-engine
Integration methods vary. Some systems utilize custom RPC layers to intercept transactions before they interact with the blockchain. Others embed smart contract hooks to override functions like transfer and transferFrom, enabling on-chain oracles to immediately halt flagged transactions. More advanced models leverage sequencer-level screening to block illicit funds before they even reach the mempool. Together, these layers form the backbone for effective enforcement and auditing processes.
How Stablerail Enforces Policy-as-Code Governance
Stablerail builds upon this scalable architecture by ensuring every transaction passes through multiple layers of policy checks before being signed. These mandatory checks include sanctions screening, enforcement of transaction limits, detection of behavioral anomalies (like unusual transaction times or amounts), and counterparty risk assessments.
The system generates a detailed Risk Dossier for each transaction, providing a verdict - PASS, FLAG, or BLOCK - alongside plain-English explanations that cite specific policy clauses and include timestamps. For transactions flagged as medium risk, the engine can trigger additional safeguards like multi-factor authentication or require CFO approval before proceeding. Only after human authorization does Stablerail’s MPC wallet sign the transaction, embedding compliance directly into the approval process.
This evaluation framework operates hierarchically. Broad project-level policies, such as blocking payments to OFAC-flagged addresses, are assessed first. Then, more specific rules - like department-level transaction limits - are applied. The policy engine also enforces strict schema validation to catch metadata errors early, reducing false positives and improving accuracy.
Audit Trails and Reporting for Compliance
Strong audit trails are essential for maintaining compliance and accountability. Every transaction decision is accompanied by a cryptographic record that logs rule identifiers, inputs, and outcomes. Stablerail captures the complete lifecycle of each transaction - from initial intent and compliance checks to any flags raised, overrides applied, approvals granted, and final signing. Settlement proofs and policy traces link each transaction to its specific policy version and outcome, ensuring audit readiness.
The policy engine’s decision metadata includes critical details, such as whether the transaction was allowed or denied and the specific rule applied. This information is instrumental for creating automated reconciliation pipelines. Additionally, simulation endpoints allow teams to review detailed policy execution scenarios and potential outcomes before committing to live transactions. If a payment is blocked due to sanctions screening, the audit trail records the exact reasons, the policy rule applied, and the identities of those involved in the review. All events are timestamped and cryptographically signed, ensuring transparency and supporting continuous compliance improvements. These detailed records enhance accountability while enabling teams to refine their policies proactively.
Presentation: Beyond the Hype: Sanctions Compliance in Crypto
Implementing Policy-as-Code for Finance Teams
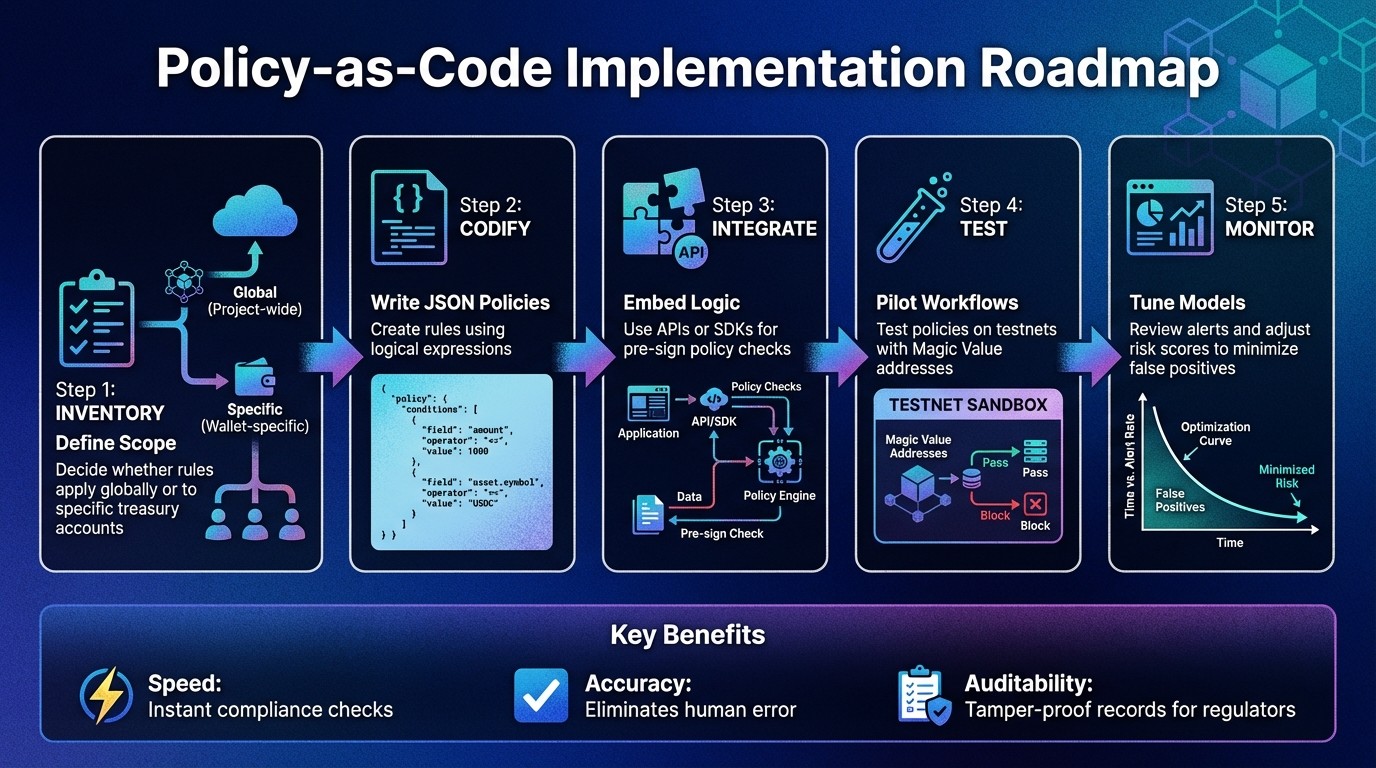
Policy-as-Code Sanctions Screening: 5-Step Implementation Roadmap for Finance Teams
Implementation Roadmap for Policy-as-Code Screening
To implement policy-as-code, start by cataloging your existing compliance rules and converting them into machine-readable formats like JSON. Begin by determining whether the policies should apply globally across all treasury accounts or only to specific wallets. For instance, you might set project-wide rules for OFAC blocks while establishing wallet-specific limits, such as a $50,000 daily cap for vendor payments.
Once the scope is defined, translate these rules into JSON policies using logical expressions. For example, a rule like amount <= 1000 && asset.symbol == "USDC" can restrict small USDC transfers. Tools like Stablerail's Policy Console allow finance teams to codify these rules without needing to write code. This means business logic, such as "Payments to new addresses over $5,000 require CFO approval and verification", can be transformed into automated, enforceable policies that activate before any transaction is signed.
Before deploying these policies, test them in controlled environments like testnets. Use test parameters and Magic Value addresses to simulate sanctions hits. Once the screening workflow is validated, integrate the policy engine into your systems via APIs or SDKs.
After codifying and testing policies, focus on refining their accuracy and maintaining effective governance.
Reducing False Positives and Improving Accuracy
Once your policies are in place, fine-tuning risk parameters becomes critical. Adjust fuzzy matching logic to cut down on false positives while maintaining precision. Instead of applying broad, generic blocks, use specific transaction parameters like ethValue, asset.symbol, operation type (e.g., signEvmTransaction), and destination address to create more precise rules.
Strict schema validation is another key step. Stablerail enforces rigorous schema definitions to catch metadata errors early, which helps reduce both false positives and negatives.
For data that changes frequently, a hybrid policy architecture can provide better results. Instead of embedding sanctions lists in immutable smart contracts, use external compliance oracles that refresh every 2 to 5 minutes with the latest OFAC updates. To ensure security, adopt a DENY-overrides-ALLOW model, where the default setting is "DENY" for high-risk scenarios, and specific "ALLOW" rules are added for trusted wallets or verified entities.
Continuous Testing and Governance Updates
Policy-as-code requires ongoing testing and updates to stay effective. Use simulation-first workflows to test new policies before they go live. These "dry-run" methods let you see how updated rules interact with real transaction data without executing actual transfers. This helps avoid unexpected disruptions to legitimate payments when refining your screening logic.
Real-time alerting through webhooks ensures compliance teams can act quickly if a transaction is flagged or blocked. Tagging each policy with metadata - such as ticket IDs, severity levels, or rule owners - streamlines investigations during audits.
"The future of compliance won't just watch what happens on-chain. It will decide what's allowed to happen in the first place." – Natalia Latka, Head of Regulatory Affairs, ComPilot
Regular reviews are essential to keep your policies aligned with changing regulations. Sanctions lists are updated frequently, so your screening engine should pull data from sources that refresh every few minutes. A layered evaluation approach works well here: start with broad compliance rules at the project level, then add account-specific overrides for trusted exceptions. Combining regular simulations with real-time alerts ensures your pre-transaction controls remain strong, completing the cycle from defining policies to enforcing them effectively.
Conclusion: The Future of Policy-as-Code in Sanctions Screening
Key Takeaways
Policy-as-code integrates compliance checks directly into transaction workflows, preventing prohibited transfers before they can even occur. This approach ensures real-time enforcement, perfectly aligned with the rapid pace of digital asset markets, where transactions settle in mere seconds instead of days. By automating these processes, finance teams can streamline operations, minimize human error, and reduce the need for extensive training. Additionally, it consolidates wallet management and compliance tasks into a single, efficient interface.
Instead of relying on traditional narrative reports, treasury teams now have the capability to provide regulators with cryptographic proof that specific compliance obligations were met at the exact moment of execution. Platforms like Stablerail are leading the way by maintaining comprehensive audit trails for every action, from initial intent and risk assessments to final approvals and signatures. These advancements are paving the way for treasury operations to adapt seamlessly to evolving regulatory landscapes.
Preparing for Future Treasury Operations
To thrive in an increasingly complex regulatory environment, treasury operations need to embrace stablecoin treasury management best practices. Automated and dynamic compliance frameworks are being woven into blockchain protocols, signaling that policy-as-code is quickly becoming a standard requirement for stablecoin treasuries.
"The future of compliance won't just watch what happens on-chain. It will decide what's allowed to happen in the first place." – Natalia Latka, Head of Regulatory Affairs, ComPilot
To stay ahead of the curve, treasury teams should consider adopting hybrid architectures. These combine immutable smart contract rules with dynamic policy oracles, allowing updates to sanctions lists and thresholds off-chain without the need to redeploy contracts. This flexibility ensures that compliance logic can keep pace with daily regulatory changes. By implementing signature gating - a lightweight enforcement layer that applies compliance rules before transactions are signed - treasuries can adapt to new requirements without disrupting existing protocols. As machine-readable regulations gain traction and embedded supervision initiatives expand globally, policy-as-code is set to transition from being a competitive edge to becoming a fundamental expectation for institutional stablecoin operations.
FAQs
How does policy-as-code enhance sanctions screening for stablecoin payments?
Policy-as-code enables finance teams to set up and automatically enforce sanctions screening rules for every stablecoin transaction. These rules operate as pre-sign checks, ensuring compliance in real time while minimizing the chances of human error.
With automated enforcement, policy-as-code ensures consistent outcomes and generates a comprehensive audit trail for every decision. This not only simplifies regulatory compliance but also preserves the speed and efficiency of on-chain payments.
What are the essential components for implementing a policy-as-code system for sanctions screening?
To set up a policy-as-code system for sanctions screening, you'll need two main components working together.
First, a machine-readable policy framework is the backbone of the system. This framework lays out the rules, including scope (like which accounts or projects are covered), conditions (such as "block transfers to sanctioned addresses"), actions (e.g., approve or reject), and operations (like signing or sending transactions). These rules are evaluated by a policy engine, which automatically processes them for every payment intent, ensuring consistent compliance.
Second, you'll need tools that integrate these policies into your treasury workflow. A policy management interface enables finance teams to create and modify rules. For example, you might set a rule like, "Payments exceeding $5,000 on weekends require CFO approval." Before any transaction is signed, pre-sign checks - such as sanctions screening, limit enforcement, and anomaly detection - are conducted. A risk dossier is then generated, providing a verdict (PASS, FLAG, or BLOCK). To maintain compliance, an audit trail records every step, and a human-in-the-loop approval process ensures that flagged transactions are reviewed and approved before they're finalized.
Together, these components form a streamlined, enforceable policy-as-code system, perfectly suited for managing stablecoin treasury operations.
How does policy-as-code ensure compliance during stablecoin payments?
Policy-as-code works by embedding rules - like sanctions screening, transaction thresholds, and approval protocols - into machine-readable policies. These policies are applied automatically to every payment intent in real time, before any transaction is finalized.
With this setup, the system can immediately approve, flag, or block transactions based on the established criteria. This ensures that stablecoin payments comply with both regulatory requirements and internal policies at the exact moment they are processed.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


