
Stablecoin payments are fast, efficient, and always available, but their speed comes with risks. Once a transaction is signed on-chain, it can't be undone. Pre-sign risk checks solve this by identifying issues like compliance violations, fraud, or errors before the transaction is finalized. This proactive approach ensures secure, accurate, and compliant payments while maintaining the benefits of stablecoins.
Key Points:
What are pre-sign risk checks? Automated reviews of payment intents before signing to catch risks such as sanctions exposure, policy breaches, or unusual activity.
Why are they important? Stablecoin transactions are irreversible, and mistakes like sending funds to the wrong address or violating regulations can lead to serious financial or legal consequences.
How do they work? Risk checks screen for sanctions, enforce policies (e.g., spending limits, whitelists), and detect anomalies in real time.
Benefits for businesses: Avoid costly errors, ensure compliance, and maintain an auditable, secure payment process.
By combining automated tools with human oversight, companies can streamline operations, reduce risks, and follow a stablecoin compliance checklist without sacrificing transaction speed.
Types of Pre-Sign Risk Checks
Pre-sign risk checks are a critical safeguard, designed to stop threats before a transaction is finalized. These checks are triggered automatically as soon as a payment intent is created - before any cryptographic signature is applied. Their purpose? To block errors, fraud, or compliance violations in real time. Here’s a closer look at the three primary types of pre-sign risk checks and how they help secure stablecoin transactions.
Sanctions and Taint Screening
Every wallet address carries a history. Sanctions and taint screening tools dig into that history, analyzing the "lineage" of funds. They check whether funds have passed through high-risk channels like mixers, flagged exchanges, or wallets tied to sanctioned entities. This process ensures compliance with regulations like OFAC, MiCA, and the Travel Rule, while minimizing exposure to regulatory risks.
Modern systems rely on policy-as-code, which automates the evaluation of each payment intent. These evaluations cover jurisdictional allowlists, KYC statuses, and taint thresholds. The outcome is a Policy Trace - a documented record showing which rules were applied and whether the transaction passed or failed. This creates a clear audit trail for regulators and boards, offering transparency and accountability.
Policy and Limit Enforcement
Policy enforcement turns complex financial and compliance rules into machine-enforceable safeguards. These safeguards automatically apply to every transaction, covering areas like spending limits (e.g., per transaction or daily caps), velocity checks (e.g., number of payments per hour), recipient whitelists (e.g., pre-approved wallet addresses), and network restrictions (e.g., only USDC on Base or Ethereum).
Did you know that 56% of accounts payable teams spend over 10 hours weekly handling manual invoices and supplier payments? Automating rules can drastically reduce this workload. For instance, policies like "New address payments over $5,000 require CFO approval" or "Weekend transfers exceeding $10,000 need additional approval" can be encoded directly into workflows.
To ensure integrity, systems use SHA-256 intent fingerprinting. This means if any transaction detail - like the recipient, amount, or asset - is altered after the policy check, the cryptographic signature will fail, and the transaction will be blocked. These enforcement layers operate with lightning-fast speeds (latency under 50ms), ensuring compliance without slowing down payments. Additionally, anomaly detection adds another layer of protection by identifying irregular patterns.
Behavioral Anomaly Detection
Anomaly detection focuses on identifying unusual transaction behaviors - timing, amounts, frequency - that deviate from established patterns. For example, it flags velocity spikes (too many payments in a short period), unauthorized amounts (exceeding transaction or daily limits), or unusual timing (like a large payment to an unfamiliar address on a weekend).
AI systems play a key role here, analyzing both transaction details and on-chain data to catch risks a human might miss. Imagine your company typically processes $50,000 in weekly vendor payments, but suddenly a $200,000 request to a new address appears late on a Saturday night. The system would flag this for human review. Beyond just blocking transactions, these systems provide plain-English explanations that highlight the evidence - such as policy clauses, timestamps, and historical baselines. This helps approvers understand exactly why a transaction was flagged, empowering them to make informed decisions.
How to Build a Pre-Sign Risk Check Workflow
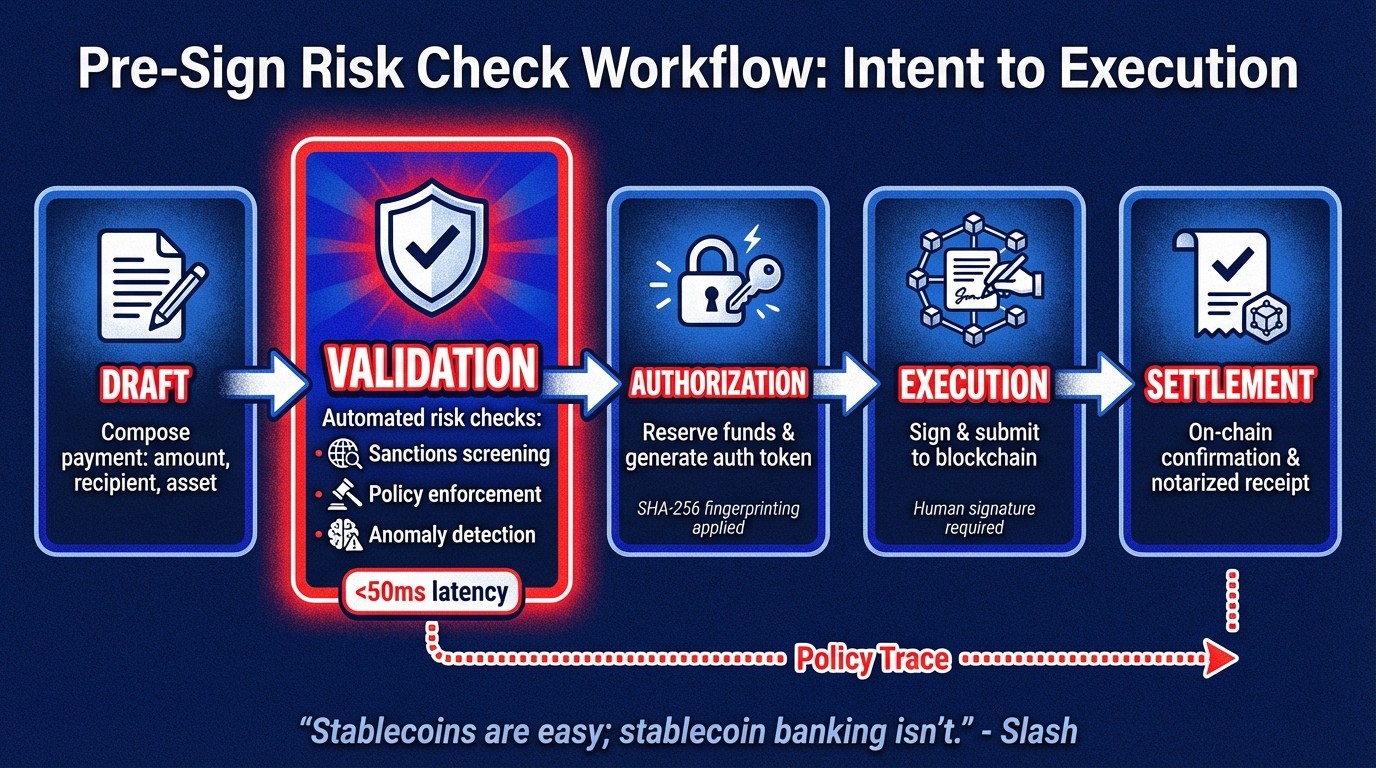
Pre-Sign Risk Check Workflow: From Intent to Execution
A pre-sign risk check workflow automates controls between payment intent and execution, helping you catch errors, fraud, and compliance violations before signing. The idea is to stop issues in their tracks without holding up legitimate payments. Here’s how you can set this up for your corporate treasury operations.
Setting Up Governance Rules and Policies
First, define the basics: who can move funds, how much, to whom, and through what channels. These rules form the backbone of your policy-as-code system. For example, you might require extra approval for high-value payments or transfers to new addresses. These aren’t just suggestions - they’re machine-enforceable rules that apply automatically to every transaction before signing.
Your policy setup should include:
Transaction limits: Set per-transaction caps, daily limits, and velocity thresholds.
Whitelists: Pre-approve wallet addresses and counterparties.
Network restrictions: Specify which blockchains and stablecoins are allowed.
Compliance screening: Conduct sanctions checks on individuals, entities, locations, and wallet addresses.
Manual processes can be a huge time drain. For instance, 56% of accounts payable teams spend over 10 hours weekly on manual invoice and supplier payment tasks. Automating these policies can save significant time and effort.
If your company deals with regulated stablecoin flows, you’ll need to account for reserve and redemption rules. For example, the GENIUS Act, signed on July 18, 2025, mandates that stablecoin reserves consist of cash or high-quality liquid assets with a maximum 93-day maturity. Full compliance is expected by early 2027, 18 months after the law’s enactment. Your policy layer should verify these requirements automatically before processing any transaction.
Once your governance rules are in place, the next step is to map these policies into a workflow that ensures transaction integrity.
Mapping the Intent-to-Execution Process
After setting up your policies, you’ll need to structure the workflow to separate intent from execution. This distinction between business "Intent" (what and why) and technical "Execution" (on-chain submission) creates a clear audit trail and helps prevent tampering. Typically, the workflow involves five stages:
Draft: Composing the payment, including the amount and participants.
Pending/Validation: Running automated checks for sanctions, limits, and anomalies.
Authorization: Reserving funds and generating an authorization token.
Capture/Execution: Signing and submitting the transaction to the blockchain.
Settlement/Reconciliation: Issuing notarized receipts after on-chain confirmation.
To ensure security, apply SHA-256 fingerprinting to the transaction intent. This means any change - whether to the recipient, amount, or asset - invalidates the signature. High-performance policy layers can validate transactions against complex rules in under 50ms, maintaining compliance without slowing down payments.
"Stablecoins are easy; stablecoin banking isn't." - Slash
Configuring Approval Hierarchies and Human Review
Set up role-based access control to assign specific roles for your finance, treasury, and compliance teams. Use threshold-based escalation so that only high-risk or high-value transactions trigger human review. For instance, you might require review for payments over $10,000 or transfers to new addresses. For the most sensitive transactions, implement dual-control and quorum approvals, requiring multiple authorized signers. This prevents single points of failure and reduces insider risk.
Human oversight acts as the final safeguard. While AI can block, flag, and explain risks, only authorized individuals should approve transactions. Every decision should be recorded cryptographically. AI copilots can handle background checks - like sanctions screenings or anomaly detection - and provide clear risk explanations, but they cannot initiate transfers or hold keys. As an added layer of security, include an emergency kill switch that allows administrators to halt all automated transactions if a significant risk is detected.
"Nothing moves without a human signature. The AI can only block, flag, and explain - never spend." - Stablerail
Technical Requirements for Pre-Sign Risk Checks
Creating a reliable system for pre-sign risk checks requires a solid technical foundation. To operate effectively in production, three key layers are essential: secure custody, real-time compliance integrations, and tamper-evident audit systems. These layers must work seamlessly to enforce policies while keeping legitimate transactions smooth. Here's a breakdown of what it takes to build such a system.
Custody and Wallet Setup
Start by setting up MPC wallets to split private keys, ensuring no single entity has full signing authority. This approach allows a control plane to enforce policies before any signature request, keeping funds secure. For flexibility, ensure your MPC-based vaults support major blockchains like Ethereum, Base, and Polygon, as well as stablecoins such as USDC and USDT.
To manage signing operations, integrate HSMs (hardware security modules) or cloud-based key management services like AWS KMS or GCP Cloud KMS. Simplify operations further by using sponsored transfers or dedicated gas wallets. This eliminates the need for individual wallets to hold native tokens (e.g., ETH) for transaction fees.
Connecting Compliance and Screening Tools
Compliance is a critical step. Link your control plane to blockchain intelligence platforms like Chainalysis or TRM Labs via APIs to screen wallet addresses against OFAC lists and assess taint exposure. Use a policy-as-code engine to translate finance and compliance rules into machine-enforceable policies. This engine evaluates transactions based on factors like identity checks (e.g., sanctions, KYC), transaction patterns (e.g., thresholds, velocity), and business rules (e.g., network restrictions).
Speed is key. For instance, PolicyLayer reports that their compliance checks typically take less than 50ms, ensuring policies are enforced without slowing transactions. To secure data integrity, implement SHA-256 fingerprinting to flag any post-check modifications. Additionally, all communication between agents and the control plane should be protected using HTTP Message Signatures to block man-in-the-middle attacks.
Recording Audit Trails and Evidence
To meet financial regulations, maintain audit logs for the standard 7-year retention period. Use WORM (write-once-read-many) storage, such as AWS S3 Object Lock, to prevent tampering. Your audit system should document a full "Policy Trace", detailing why each transaction was approved or denied, including rule IDs, outcomes, and messages.
For tamper-evident records, compute a Merkle root of aggregated log data periodically and publish it to a public blockchain like Ethereum or Polygon. This ensures any changes to historical records are immediately detectable. Use structured formats like JSON or Protobuf for all state-changing actions - such as admin updates, parameter changes, and fund movements - to create a clear and complete audit trail. Tools like The Graph or Subsquid can help generate queryable APIs from raw blockchain data, simplifying the creation of daily transaction reports for regulators. To detect gaps or replay attacks in the audit sequence, include a unique, incrementing nonce in all event logs.
"An audit trail is a chronological, immutable log of all significant events and state changes within a system." - ChainScore Labs
Conclusion
Key Takeaways
Pre-sign risk checks transform high-risk stablecoin transactions into structured, policy-driven workflows. By screening payments before they’re signed, finance teams can avoid compliance missteps and meet regulatory requirements like OFAC sanctions, MiCA rules, and the FATF Travel Rule - all without disrupting legitimate transactions. These checks also reduce "key-person" risk by distributing signing authority through MPC-secured vaults and enforcing detailed policies automatically.
Consider this: 55% of companies lose between 4% to 5% of their monthly revenue due to inefficiencies in payment processes. Pre-sign checks tackle this by automating critical tasks like sanctions screening, taint analysis, and anomaly detection in real time. This system creates tamper-proof audit trails, replacing messy and fragmented approval records, while meeting the 7-year retention standards regulators demand.
"Approvals are buried in Telegram, Slack, or email threads. There's no clean story for auditors, boards, or regulators." – Stablerail
Next Steps for Implementation
To build a pre-sign risk check framework, start by defining your policies. This includes setting fund permissions, transaction limits, approved counterparties, and allowed networks. Establish these guardrails before integrating any technical tools. Then, consolidate custody by moving from scattered solutions like hardware wallets and spreadsheets to MPC-secured vaults, which distribute private keys and allow configurable signing thresholds.
Once custody is centralized, implement policy-as-code to automate manual finance rules. Link compliance tools like Chainalysis or TRM Labs to your payment workflows to enable real-time risk assessments and sanctions checks for every transaction. For example, rules such as "Payments over $5,000 to new addresses require CFO approval" or "Weekend transfers above $10,000 need additional verification" can be enforced automatically before any transaction is signed.
Finally, integrate human oversight with immutable audit trails. Design your system so that automated tools can flag or block risky transactions, but a human signature is always required for final execution. Platforms like Stablerail take this "copilot, not autopilot" approach by running mandatory pre-sign checks - covering sanctions, policies, and anomalies - and generating a Risk Dossier with clear PASS/FLAG/BLOCK outcomes and explanations. This eliminates the reliance on ad-hoc processes like spreadsheets and Slack approvals, ensuring on-chain speed while maintaining strong governance standards.
FAQs
How do pre-sign risk checks improve the security of stablecoin payments?
Pre-sign risk checks enhance the safety of stablecoin payments by thoroughly reviewing each transaction before it gets approved. These checks cover areas like sanctions screening, policy enforcement, and behavioral anomaly detection, helping to spot and block unauthorized or risky transfers.
What’s more, they offer clear, easy-to-understand explanations for any flagged actions. This gives finance teams the context they need to make well-informed decisions. By catching potential issues early, these checks introduce an additional layer of control and accountability to the payment process.
How does AI help detect unusual activity in stablecoin payments?
AI helps identify unusual activity in stablecoin payments by analyzing transaction patterns and assessing risks. It looks at factors like the time of day, payment amounts, and frequency to spot anything out of the ordinary. When deviations occur, the system flags transactions that might involve fraud, mistakes, or policy violations.
In Stablerail, AI plays a key role in the pre-sign verification process. It acts as a smart assistant, reviewing each payment request and delivering detailed risk assessments. The system highlights potential issues, explains them clearly with references to policy rules and timestamps, and ensures transactions are both secure and compliant. This approach also cuts down on the need for manual checks, making life easier for finance teams.
How can businesses use pre-sign risk checks to ensure secure and compliant stablecoin payments?
Businesses can safeguard stablecoin payments while maintaining compliance by implementing pre-sign risk checks. These checks thoroughly analyze transactions before they’re approved, focusing on areas like sanctions screening, policy enforcement, and anomaly detection. Factors such as transaction timing, amounts, counterparty risks, and unusual patterns are evaluated. By automating these processes, businesses can reduce human errors and improve adherence to regulations.
Another key measure is defining policy-as-code, which allows companies to create enforceable rules. These might include setting transaction limits, specifying approved asset types, or requiring additional approvals for certain scenarios. These policies are automatically applied to every payment, ensuring all transactions comply with both internal guidelines and external regulations.
For added security, businesses can integrate human-in-the-loop approvals. This step enables finance teams to review flagged transactions, make informed decisions, and document their actions. By combining automation with human oversight, organizations can establish a scalable, secure, and transparent system for managing stablecoin payments.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


