
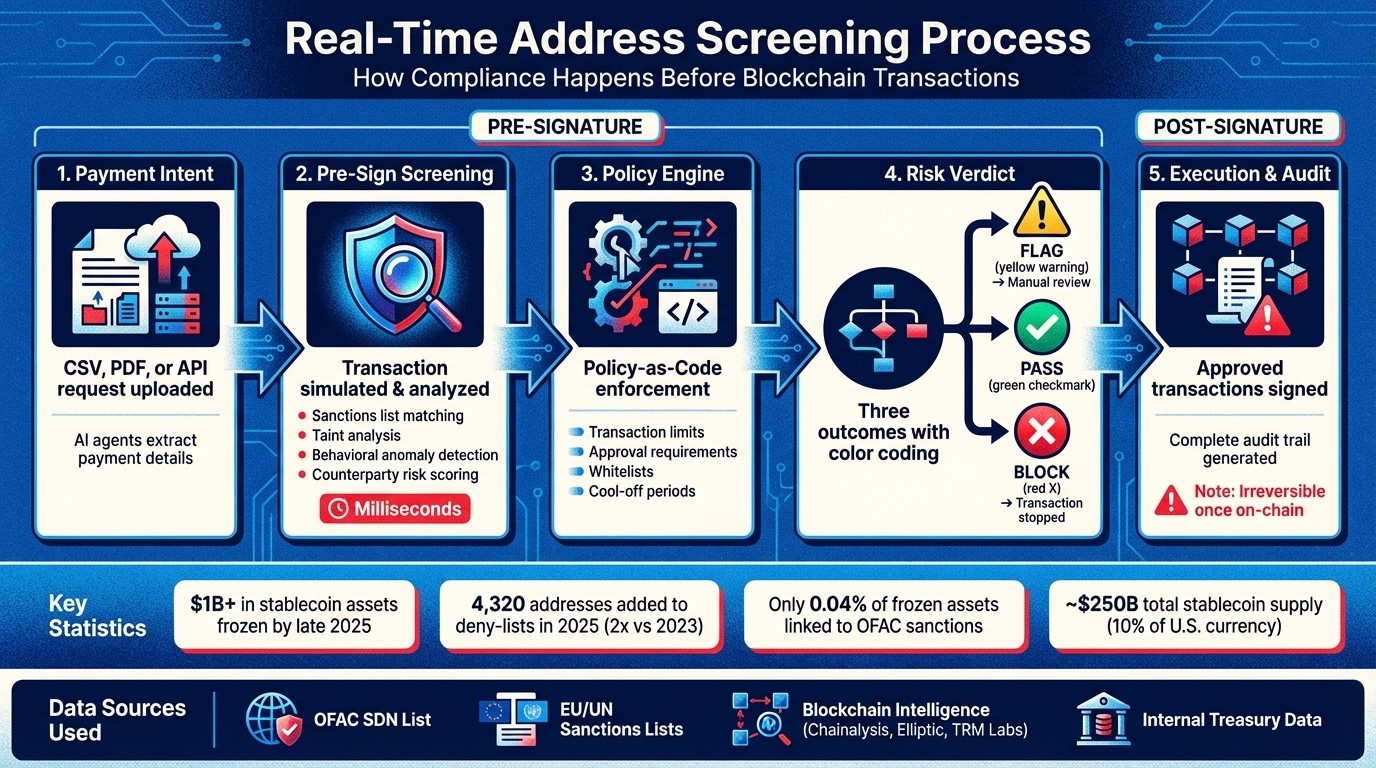
Real-time address screening is a fast, automated process that checks wallet addresses for compliance before stablecoin transactions are finalized. It prevents funds from being sent to high-risk or flagged addresses, ensuring regulatory requirements are met. This process occurs before transactions are signed or broadcast to the blockchain, making it the only effective stage for compliance enforcement since blockchain transactions are irreversible.
Key Takeaways:
Why It Matters: Stablecoins settle instantly, leaving no room for manual compliance checks. Mistakes can lead to frozen assets or regulatory penalties.
How It Works: The system screens wallet addresses against global watchlists (e.g., OFAC SDN) and uses blockchain analytics to identify risks in milliseconds.
Regulatory Need: Compliance with regulations like OFAC, FATF's Travel Rule, and MiCA is mandatory. Real-time checks reduce legal and financial risks.
Core Features: Includes sanctions matching, taint analysis, behavioral anomaly detection, and counterparty risk scoring.
Tools Used: Combines official watchlists, blockchain intelligence (e.g., Chainalysis), and internal treasury data for precise risk assessments.
Finance teams can integrate this process into their workflows using platforms like Stablerail, which automates pre-signature compliance checks, enforces policy rules, and generates detailed audit trails for every transaction. This ensures transactions are secure, compliant, and traceable.
Real-Time Address Screening Process for Stablecoin Transactions
Core Components of Real-Time Address Screening Systems
Data Sources and Integration
Real-time screening systems rely on multiple data layers to ensure compliance before transactions are executed. At the core are official government watchlists, such as the OFAC Specially Designated Nationals (SDN) list, the EU Consolidated Financial Sanctions List, UN Security Council Sanctions Lists, and the UK Office of Financial Sanctions Implementation (OFSI) list.
In addition to these static lists, these systems incorporate blockchain-specific intelligence from providers like Chainalysis, Elliptic, TRM Labs, and Range Security. These tools offer insights such as wallet clustering, risk scores, and historical behavior patterns, which help identify connections between addresses. By late 2025, issuers had frozen over $1 billion in stablecoin assets across Ethereum, Solana, and Tron networks. That same year, 4,320 new addresses were added to on-chain deny-lists - more than twice the number recorded in 2023.
Advanced systems also integrate internal treasury data, including invoicing records and vendor whitelists (often referred to as "Golden Source" catalogs). By combining regulatory watchlists, blockchain analytics, and internal records, these systems can quickly differentiate between legitimate and suspicious transactions, often in milliseconds.
These diverse data inputs form the backbone of the real-time screening methods described below.
Screening Methods
Modern screening operates at the pre-sign or sequencer level, intercepting transactions before they are broadcast to the blockchain. The system simulates transactions to extract all wallet addresses involved, even those buried within complex smart contract calls.
Key techniques include:
Sanctions list matching: Checking addresses against official watchlists.
Taint analysis: Tracing funds linked to illicit sources.
Behavioral anomaly detection: Identifying unusual patterns, such as transfers occurring at odd hours.
Counterparty risk scoring: Evaluating transaction history and address associations.
These methods yield one of three outcomes: PASS, FLAG, or BLOCK.
Interestingly, only about 0.04% of frozen stablecoin value - roughly $419,320 - is linked to addresses officially sanctioned by OFAC. This suggests that most enforcement actions are proactive, driven by issuers rather than regulatory mandates. As Range Security explains:
Blacklisting is not driven by regulatory lists alone. Instead, issuers appear to rely on internal risk detection, incident reports, or ecosystem feedback.
To improve accuracy and minimize disruptions, additional measures are applied to reduce false positives.
Reducing False Positives
False positives can disrupt operations and delay legitimate transactions. To address this, screening systems use fuzzy matching algorithms like Levenshtein distance, which account for variations in spelling or typos (e.g., "Al-Qaeda" vs. "Al Qaida"). Risk-scoring engines also combine multiple data points to deliver more nuanced decisions.
Another key strategy is whitelisting. By maintaining a verified list of trusted counterparties, systems allow frequent, low-risk transactions to bypass certain checks without compromising security. For transactions that are flagged, clear escalation paths are in place. Instead of outright blocking, these payments are routed for manual review, ensuring compliance without disrupting workflows.
This layered approach ensures treasury teams can rely on precise, fast pre-sign compliance checks, seamlessly integrated into their broader governance processes.
Crash Course in US Crypto Regulations, Compliance, and Blockchain Analytics
How Real-Time Screening Fits into Treasury Governance
Real-time address screening isn’t just a standalone process - it plays a central role in a policy-driven workflow that connects payment intent to execution. Instead of treating compliance as an afterthought or a back-office task, modern treasury systems integrate screening directly into the decision-making process. This integration shifts screening from being a reactive audit step to a proactive control mechanism that enforces rules before any funds are moved. Essentially, this governance layer builds upon the pre-sign screening techniques discussed earlier.
Policy-Driven Screening and Approvals
Treasury governance uses real-time screening results to enforce machine-driven, rule-based policies. These policies are not vague suggestions - they are specific instructions coded directly into the system. For example, finance teams can establish rules requiring extra approvals for transactions that are high-value or occur outside of normal business hours. The system applies these rules automatically, ensuring no one, not even executives, can bypass them without triggering an escalation.
This approach, often referred to as Policy-as-Code, combines deterministic rules (like hard transaction limits, whitelists, and role-based permissions) with probabilistic risk signals (such as sanctions screening, taint analysis, and anomaly detection). The policy engine then acts as a gatekeeper, delivering outcomes like approve, deny, hold, or step-up. By managing these policies like software - complete with version control and automated testing - finance teams can adapt quickly while maintaining a clear audit trail of all active rules.
Pre-Signing Verification and Risk Dossiers
Before any payment is finalized, the system simulates the transaction to detect potential issues. This simulation prevents "blind approvals", where signers might authorize payments without fully understanding the associated risks. The process generates a concise Risk Dossier with outcomes such as PASS, FLAG, or BLOCK.
These dossiers provide clear explanations supported by evidence, such as policy clauses, timestamps, and risk scores, enabling approvers to make well-informed decisions. For example, if a vendor’s address changes unexpectedly, the system can automatically halt the payment and initiate an escalation to address potential social engineering attempts. As Stablerail explains:
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money."
This pre-sign verification integrates seamlessly into broader treasury workflows, enhancing decision-making at every step.
Audit Trails and Regulatory Documentation
From the initial intent to the final settlement, every action is recorded in a comprehensive audit trail. These logs capture critical details like the policy version applied, inputs used, risk verdicts, and any manual overrides, complete with the reasons behind them. This level of detail ensures that treasury teams can defend their decisions to auditors, boards, and regulators.
Advanced systems take this a step further by using append-only, Merkle-addressable transcripts and cryptographic receipts to make logs tamper-evident and verifiable. By linking on-chain transaction hashes with off-chain business details - such as invoice IDs or payroll batch references - these audit trails provide a complete picture. This ensures on-chain activity aligns with off-chain financial records, making it easier to close the books at month-end or undergo external audits.
Multi-Layered Screening Approaches
Expanding on the concept of pre-sign screening, a multi-layered strategy strengthens risk detection by combining various analytical techniques. Relying on just one method can leave vulnerabilities that skilled threat actors might exploit. By integrating tools like blockchain forensics, behavioral analysis, and counterparty assessments, this approach uncovers risks that static lists might overlook. Each layer focuses on a unique aspect - such as the origin of funds, transaction patterns, or the reputation of involved entities - working together to create a more complete picture before a payment is approved.
Blockchain Analytics and Forensics
Blockchain analytics track the movement of funds across different intermediaries and networks, exposing cross-network transactions. This is especially important because bad actors often rotate wallets or use bridges to move assets between networks in an attempt to avoid detection. For example, in 2025, the DPRK-affiliated group "TraderTraitor" laundered $30 million in stolen Ether by funneling it through 350 newly created addresses before converting it to Bitcoin.
Forensic tools also pinpoint "tainted" counterparties - wallets linked to phishing schemes, botnets, or laundering activities - that haven’t yet been flagged on official sanctions lists. Consider this: only 36.4% of OFAC-sanctioned stablecoin wallets are blacklisted on-chain, and a mere 0.04% of over $1 billion in frozen stablecoin assets is tied to official sanctions. In mid-2025, Tether made headlines by blacklisting over 800 addresses on the Tron network in a single day, targeting clusters tied to phishing and botnets.
Forensic analysis creates detailed cross-chain risk profiles by dissecting internal transaction components before execution. Since malicious actors often fragment their transactions through bridges to bypass enforcement systems, cross-chain tracing is critical.
Behavioral and Geolocation Analysis
Behavioral analysis establishes what's "normal" for an account - typical transaction sizes, frequencies, and counterparties - and flags unusual activity that might signal account takeovers or social engineering attacks. This includes checks for rapid wallet creation, unusual transaction speeds, or irregular fee patterns.
Geolocation analysis examines where transactions originate and where they are headed, identifying connections to high-risk areas or sanctioned regions. It also uses technical details like device data and IP addresses to verify the source of a transaction. These insights feed into policy engines that provide clear outcomes such as "Approve", "Deny", "Hold," or "Step-up" (requiring extra verification). With stablecoin transactions occurring around the clock, fast compliance systems are essential.
By combining behavioral data with geolocation insights, organizations gain a more rounded view of potential risks.
Counterparty Risk Assessment
Counterparty risk assessment adds another layer by evaluating the history and exposure of involved entities to ensure they aren’t tied to high-risk activities. Stablecoin issuers like Circle and Tether can freeze assets if they detect interactions with flagged addresses, so real-time screening is crucial to identify these risks before a transaction is finalized. Advanced threat actors often use intermediary wallets or mixers to bypass sanctions lists, making it even more important to combine counterparty assessments with blockchain forensics to trace funds tied to sanctioned sources.
A well-rounded risk model incorporates hard rules (like sanctions lists), dynamic risk signals (such as anomalies), and governance controls (like whitelists) to deliver a clear verdict: "PASS", "FLAG," or "BLOCK". This approach also reduces false positives by using behavioral context and fuzzy matching for entity names, helping differentiate between high-risk actors and legitimate users, such as decentralized exchange aggregators or multisig wallets. For regulated stablecoin transfers, counterparty assessments ensure that originator and beneficiary information is verified and shared with the transaction to meet Travel Rule requirements.
How Stablerail Enables Real-Time Address Screening

Stablerail acts as a bridge between your treasury operations and the blockchain, ensuring that all transfers are verified before they’re signed. This timing is crucial because it allows for address screening before any funds are moved, rather than after. Operating as a non-custodial system, Stablerail ensures your funds remain under your control in MPC-based wallets. It never has unilateral signing authority. Instead, Stablerail functions as a "copilot", conducting essential pre-signature checks like sanctions screening, taint and exposure analysis, policy enforcement, behavioral anomaly detection, and freeze-risk warnings. These features integrate compliance and governance into every transaction seamlessly.
Stablerail's Agentic Control Plane
The agentic control plane automates pre-signature checks as soon as a finance team uploads a payment request. Whether the request comes in as a CSV file, an invoice PDF, or through an API call, AI agents extract the necessary details and compare them against your organization’s policies. They flag potential issues like first-time payment destinations, address changes, or duplicate payments before any transaction is finalized.
For every payment, the system generates a Pre-Flight Risk Dossier with a clear verdict: PASS, FLAG, or BLOCK. Each decision is accompanied by detailed, policy-linked explanations. For instance, if a vendor’s address has been updated, the system automatically locks the transaction for review. Additionally, "smart cool-off periods" delay high-value payments (over $100,000) or payments to new beneficiaries for a set period, such as four hours, to reduce the risk of social engineering attacks.
Policy-as-Code for Finance Teams
Stablerail's policy engine allows finance teams to define and enforce business rules for every transaction automatically. For example, you can require CFO approval for payments over $5,000 to new addresses or mandate extra scrutiny for weekend transfers. These rules accommodate role-based access, multi-step approvals, and transaction thresholds based on factors like amount, currency, or counterparty type.
This system transforms compliance from a manual, after-the-fact process into a real-time enforcement layer. In the regulatory environment of 2026, this approach - referred to as "Compliance-as-Infrastructure" - is increasingly critical for organizations managing stablecoin payments. By combining fixed rules with dynamic risk assessments, the policy engine delivers actionable outcomes like Approve, Deny, Hold, or Step-Up (requiring additional verification). Policies are version-controlled, allowing auditors to see exactly which rules were applied to any given decision, making compliance both scalable and transparent.
Audit and Evidence Generation
Every transaction processed through Stablerail is meticulously documented, tying back to the treasury governance system. Each payment generates a Proof-of-Control Receipt, which records essential details like the amount, rationale, approver, and verdict. From intent creation and risk checks to policy overrides and the final signature, every step is logged in a tamper-resistant audit trail.
This detailed documentation is invaluable, especially in light of the more than $1 billion in stablecoin assets frozen on-chain by issuers as of late 2025. Proof of due diligence can mean the difference between a routine audit and a regulatory inquiry. Stablerail ensures finance teams can demonstrate they enforce governance controls similar to those used for traditional bank wires while still enjoying the efficiency of blockchain transactions.
Key Takeaways
The Importance of Real-Time Screening
Real-time address screening plays a critical role in ensuring compliance before blockchain transactions are finalized. Unlike traditional financial systems, where payments can sometimes be reversed, stablecoin transfers settle almost instantly and cannot be undone. This gives finance teams just one chance to identify risky counterparties, policy breaches, or patterns that might lead to frozen assets before the funds are permanently moved. With stablecoins now accounting for the majority of illicit on-chain activity and their supply nearing $250 billion - about 10% of the U.S. currency in circulation - regulators like FinCEN and the EU's MiCA framework are pushing for compliance standards akin to those in banking. Real-time screening not only ensures operational transparency but also provides a clear audit trail, offering precise explanations for why transactions are either approved or blocked.
How Stablerail Simplifies Compliance
Stablerail eliminates the need for outdated manual processes by enforcing compliance before transactions occur. Its pre-sign risk dossiers catch new, modified, or duplicate addresses before any blockchain transaction is initiated. The platform’s policy-as-code engine automates rules such as “Payments over $5,000 to new addresses require CFO approval,” removing the need for manual reviews. Additionally, every transaction generates a Proof-of-Control receipt, linking it to specific policy rules and timestamps. These built-in controls enable finance teams to adapt their workflows as regulatory requirements continue to change.
Next Steps for Finance Teams
With real-time screening in place, finance teams should focus on addressing operational control gaps. If your team is still managing stablecoin payments with outdated tools like legacy wallets and spreadsheets, it might be time to reassess whether your current system can handle growing regulatory demands. Start by conducting a shadow audit of your treasury operations to pinpoint weaknesses, particularly in areas like address verification, separation of duties, and maintaining a robust audit trail.
To strengthen operations, consider creating a "golden source" for verified vendor addresses and introducing smart cool-off periods for high-value transactions or new payees. These measures, combined with real-time screening, can help protect your organization from asset freezes and regulatory challenges. Stablerail typically works with companies managing $1 million to $50 million in stablecoins annually, offering tailored onboarding and policy design support to help finance teams shift from passive oversight to active control.
FAQs
What happens when a payment is flagged but not blocked?
When a payment is flagged but not stopped outright, it calls for additional review and verification. This step ensures that human judgment is applied to confirm the transaction aligns with established policies before moving forward. Keeping thorough records of the review process is key to ensuring both compliance and transparency.
How do you screen addresses inside smart contract calls before signing?
Address screening before signing smart contract calls involves a series of essential pre-sign checks designed to prioritize both compliance and security. These checks typically include sanctions screening, exposure analysis, counterparty risk scoring, and anomaly detection. The result of this process is a detailed risk dossier that compiles all findings for thorough review. If necessary, human approvers have the ability to override decisions, adding an extra layer of scrutiny.
This approach enables real-time address validation, helping to block unauthorized transactions effectively. Additionally, it maintains a complete audit trail, ensuring transparency and accountability throughout the process.
How can a finance team set risk thresholds without causing false positives?
Finance teams can cut down on false positives by adopting a policy-as-code approach. This method uses customized rules alongside layered risk assessments to enforce security measures automatically. For instance, rules might include limits on transaction sizes, evaluating counterparty risk scores, or tracking behavioral patterns - all applied before any transaction is finalized.
Adding another layer, behavioral anomaly detection - such as spotting unusual timing or deviations in payouts - provides extra context. Over time, incorporating human-in-the-loop approvals helps fine-tune these thresholds, balancing security with efficiency and reducing unnecessary alerts.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


