
Mistakes in stablecoin treasury operations can lead to irreversible financial losses. With blockchain transactions surpassing $27.6 trillion in 2024 and no option to reverse errors, finance teams must adopt strict controls. Key essential controls include:
Policy Controls: Enforce dual approvals, address whitelisting, and mandatory references for transactions.
Automated Safeguards: Use policy-as-code to automate checks like transaction limits, address validation, and time-based restrictions.
Access Controls: Limit permissions with role-based management and multi-factor authentication.
Separation of Duties: Divide roles (e.g., requester, approver, signer) to reduce fraud risks.
Pre-Transaction Verification: Simulate transactions, screen for sanctions, and flag anomalies before execution.
Monitoring and Reconciliation: Track transactions daily, verify records, and maintain a detailed audit trail.
These steps help prevent costly errors, improve accountability, and secure treasury operations.
Policy Controls Checklist
Policy controls are essential for enforcing business rules and minimizing errors. Without them, you’re left relying on human memory and discipline - an unreliable and costly approach. These controls lay the foundation for the automated pre-transaction checks discussed later.
Transaction Rules and Approval Requirements
Implement stablecoin treasury management best practices, including dual control for critical changes. No single individual should have the authority to add a new destination address or alter the signer set without a second approval. This prevents unauthorized changes from slipping through.
Require a mandatory business reference (like an invoice ID, payroll batch ID, or refund ticket number) for every transaction. This ensures smooth ledger reconciliation and reduces manual tracking errors.
Use address whitelisting with change locks by maintaining a "Golden Source" of approved payees. If a vendor’s address is updated, payments to that address should automatically freeze, triggering mandatory escalation.
For high-value transfers - those exceeding $100,000 - or transactions involving new beneficiaries, enforce a 4-hour cool-off period. This delay gives time to catch errors or fraudulent activity before funds leave your system.
Separation of duties is a must. No single person should oversee the entire payment cycle, reducing the risk of insider threats.
While these rules require human oversight, integrating policy-as-code shifts much of the burden to automated systems, ensuring consistent enforcement.
Policy-as-Code Implementation
Manual checklists can easily fail. Policy-as-code translates business rules into automated controls that run before every transaction. Even high-level executives, including the CEO, cannot bypass these programmed rules.
The Stablerail Policy Console enables finance teams to define rules in plain English, which are then converted into programmatic controls. These rules are enforced at the pre-flight stage - before any transaction is signed or processed - preventing errors rather than catching them after settlement.
Policy-as-code ensures deterministic outcomes by automating decisions. Instead of simple allow/deny responses, modern policy engines can return nuanced actions like Approve, Deny, Hold (pause for review), Route (choose the best chain or asset), or Step-up (require additional verification). This reduces operational bottlenecks while maintaining strong safeguards.
Treat your policies like software. Use version control to track changes, conduct automated testing for edge cases, and maintain rollback paths to quickly deploy updates when needed. This method allows you to address policy gaps in minutes rather than weeks, ensuring your rules stay effective and up-to-date.
Automated enforcement plays a key role in reducing insider errors, especially in stablecoin treasury operations.
Access Controls and Separation of Duties
Adding to automated policy enforcement, implementing strict access controls and dividing roles are key steps to reducing insider risks. The principle here is simple: no single person should be able to complete an entire transaction from start to finish. This separation of duties helps prevent both accidental errors and deliberate fraud. If one person can initiate, approve, and execute payments, it creates a single point of failure that could jeopardize your entire treasury.
Role-Based Access Management
The principle of least privilege is critical - grant people only the access they absolutely need. For instance, a junior accountant preparing payment batches shouldn’t have the ability to change the vendor whitelist or adjust approval thresholds.
Breaking the payment process into distinct roles adds another layer of security. Here's how it works:
The Requester initiates payments and provides necessary documentation, like invoices.
The Preparer builds the transaction and ensures it complies with company policies.
The Approver verifies the business purpose and legitimacy of the counterparty.
The Signer executes the transaction with a cryptographic signature.
The Reconciler checks that blockchain activity matches internal records.
The Stablerail Treasury Hub enforces these roles programmatically, setting limits based on factors like transaction amount, currency, counterparty, and time per user. Even executives must follow the approval workflow to expedite payments. This isn’t about mistrust - it’s about safeguarding everyone from mistakes made under pressure.
To further secure the process, use multi-factor authentication (MFA) for all signers. Combine single sign-on (SSO) with MFA and hardware keys to protect against credential-based attacks. For wallets holding reserve funds, consider requiring more signers than for operational wallets.
For high-value transactions - anything over $100,000 - or payments to new beneficiaries, enforce a 4-hour cooling-off period. This buffer allows time to catch errors or detect fraud before funds are transferred out.
While access controls are essential, separating duties across roles ensures an additional layer of protection against both mistakes and fraud.
Separation of Duties (SoD)
Allowing one person to control the entire payment cycle significantly increases risk. Errors can go unnoticed, and fraud becomes easier to execute. By separating duties, multiple individuals review each transaction, reducing the likelihood of mistakes or malicious actions slipping through.
Take the October 2024 Radiant Capital hack as a cautionary tale. Attackers exploited a weak 3-of-11 multisig setup to steal $53 million because the system lacked truly independent verification. As Trail of Bits aptly put it: “When your security domains overlap, multisig becomes single-sig with extra steps”.
To further reduce risks, segment funds into tiered wallet access:
Cold wallets (reserves) for long-term storage.
Warm wallets (operational) for regular transactions.
Hot wallets (automated) for frequent, lower-risk payments.
Each wallet type should have its own approval thresholds. This approach ensures that even if automated systems are compromised, no single person can override the payment process.
The goal isn’t to bog down legitimate operations but to create checkpoints that catch issues before they lead to irreversible losses. Even for high transaction volumes, a brief delay for high-value transfers is a small trade-off for protecting your treasury from catastrophic risks.
Pre-Transaction Verification Checklist
Before executing any stablecoin payment, it’s essential to run both automated and manual checks. These steps act as a safeguard against errors, fraud, and compliance issues. The goal? Spot potential problems before you sign, while there’s still a chance to fix them.
Automated Pre-Sign Checks
Automated checks should be the first line of defense, running quickly to catch issues before a transaction is finalized. A cornerstone of this process is transaction simulation, which previews the payment’s outcome on-chain. This step identifies first-time destinations, address changes, or duplicate transfers before you commit.
Sanctions and screening checks are equally critical. These automatically compare counterparties against prohibited address lists and exposure thresholds. If there’s a link to sanctioned entities or "tainted" funds, the system flags it. For example, after the July 2023 Multichain hack, stablecoin issuers froze $66 million of the $126 million stolen by acting swiftly with 24/7 incident response protocols.
Another automated safeguard involves detecting behavioral anomalies. If your team typically processes $50,000 in weekly payments but suddenly initiates a $200,000 transfer on a Saturday night, the system should flag it for review. Policy engine enforcement ensures rules like “payments over $5,000 to new addresses require CFO approval” or “weekend transfers over $10,000 need additional sign-off” are consistently applied, preventing circumvention.
Address hygiene checks are crucial to ensure payments only go to pre-approved counterparties listed in your "Golden Source" whitelist. If a vendor’s address changes, the system halts the payment and triggers an escalation. Additionally, network and asset compatibility checks verify that assets are sent on supported chains and routes, reducing the risk of irreversible losses.
If any automated check raises a concern, the flagged transaction moves to a human reviewer for further scrutiny before final approval.
Human Review and Approval
Even with robust automated systems, human oversight is essential for confirming flagged transactions. Whether it’s a first-time beneficiary, an unusually large payment, or a counterparty risk, a human reviewer provides the final decision.
Stablerail’s Risk Dossier equips approvers with a clear verdict: PASS, FLAG, or BLOCK. Instead of vague alerts, the dossier includes detailed, plain-English explanations supported by evidence - like policy clauses, timestamps, and specific risk indicators. This ensures CFOs and finance leaders can make informed decisions and defend their choices to auditors or boards later.
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money." - Stablerail
Approvers must document their reasons for any override, creating a clear audit trail and accountability. For high-value transfers exceeding $100,000 or payments to new beneficiaries, a 4-hour cooling-off period allows time to catch errors or identify potential social engineering attempts before funds are irreversibly moved.
The October 2024 Radiant Capital hack, which led to a $53 million theft, highlights the dangers of weak verification controls. As Trail of Bits observed:
"True 'What You See Is What You Sign' (WYSIWYS) remains impossible with current hardware wallet technology... leaving signers partially blind to what they're actually authorizing".
To counter this risk, implement redundant verification using three independent workstations for initiation, simulation, and offline verification. Signers should manually compare transaction hashes character-by-character across these systems before finalizing any payment. This layered approach ensures that even if one system is compromised, the others provide accurate transaction data.
Monitoring, Reconciliation, and Audit Trail
Clearing pre-sign checks and executing on-chain payments is just the beginning for stablecoin treasury operations. What sets a solid operation apart is the ongoing work - continuous monitoring, daily reconciliation, and maintaining a complete audit trail. These steps help catch errors, ensure compliance, and create a record to avoid future missteps.
Transaction Monitoring
Real-time transaction monitoring is a must for spotting potential errors or fraudulent activity. Pay close attention to high-risk triggers like new destination addresses, updates to vendor address books, changes in policy rules or signer sets, and unusual transaction patterns. Both transaction-level alerts and broader operational thresholds should be part of your system.
Key areas to monitor include:
Wallet balance breaches: For example, when hot wallets exceed their limits.
Sudden fee spikes: These could signal compromised automation or network problems.
Policy or signer changes: These might indicate unauthorized access.
The importance of monitoring is clear from past incidents. In March 2022, ineffective monitoring led to a $600 million loss. Meanwhile, during the July 2023 Multichain hack, swift monitoring and response protocols enabled stablecoin issuers to freeze $66 million of the $126 million stolen within hours.
Set up automatic halt rules to pause outbound transactions under critical conditions - like a stablecoin peg deviation over 0.5%, bridge outages, or network sequencer failures. These safeguards provide essential time to evaluate and address issues before they escalate.
Reconciliation Processes
After monitoring, reconciliation ensures every transaction is accurate and accounted for. This process confirms what happened, why it happened, who approved it, and how it was recorded. To start, gather data from four key sources:
On-chain records: Transaction hashes, timestamps, and fees.
Wallet or custody logs: Approval records and signer actions.
Business systems: Invoices, payroll batches, or other operational data.
General ledger: Financial records.
Standardize token amounts and map contract addresses across networks. Then, tie every on-chain transaction to a specific business reference ID - like an invoice number or refund ticket - to ensure each payment serves a defined purpose. Any mismatches should go through a formal exceptions process with clear ownership and deadlines, rather than being resolved informally.
"A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process."
Stablecoin Insider
Daily reconciliation is essential - not just a month-end task. By verifying wallet balances by stablecoin, network, and operational tier every day, you can avoid last-minute chaos and keep your records audit-ready. Once reconciled, lock the period to preserve the integrity of your audit trail.
Audit Trail and Incident Response
Reconciliation sets the stage for a robust audit trail, which is crucial for quick and effective incident response. Your audit trail should capture every action in detail, including:
Payment intent IDs
Contextual data (e.g., jurisdiction, counterparty risk tier)
Decision outcomes with reason codes
Policy versions applied
Execution references like transaction hashes and timestamps
Tools like Stablerail's Proof-of-Control receipts offer CFO-level documentation for every payment. These receipts include risk verdicts (PASS, FLAG, or BLOCK), explanations for overrides, and the identities of all approvers - making them defensible to boards, auditors, and banking partners.
Clear incident response procedures are equally important. Define escalation paths, determine who can override halts, and require written justifications for manual interventions. Regular tabletop exercises can prepare your team for situations like compromised signing keys, fraudulent payments, or network outages. As Trail of Bits aptly puts it:
"The strongest security control isn't any single technical measure, but the organizational muscle memory that translates 'that happened to them' into 'here's what we changed to prevent it from happening to us.'"
Trail of Bits
With custodial stablecoins surpassing $27.6 trillion in transaction volume in 2024 - outpacing Visa and Mastercard combined - the stakes are higher than ever. Maintaining detailed, reliable records is not just a best practice; it’s a responsibility that ensures your treasury meets the same standards as traditional banking systems.
Implementation Workflow Checklist
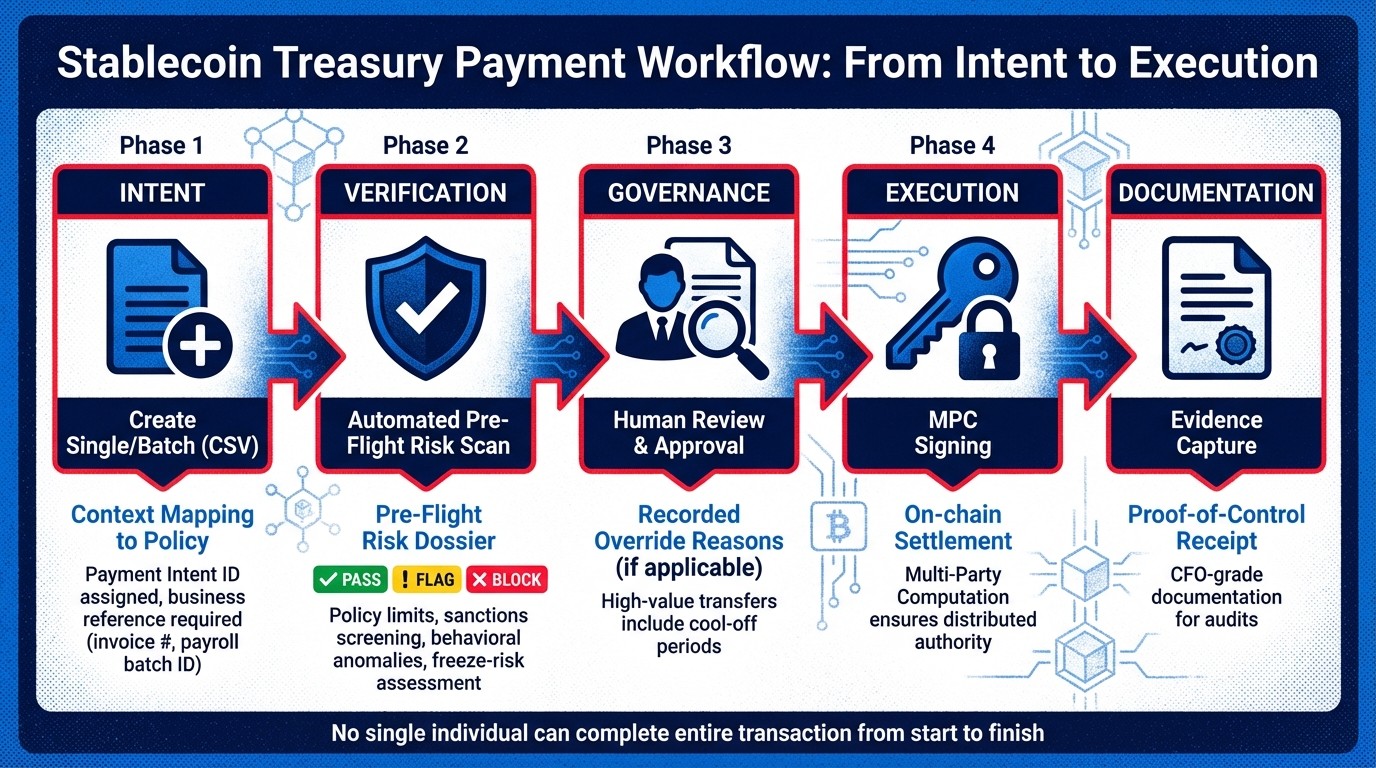
Stablecoin Treasury Payment Workflow: From Intent to Execution
From Intent to Execution
A well-structured workflow is key to reducing insider errors by fully documenting every payment, from the initial intent to its on-chain settlement.
Start by creating a payment intent - whether it's for a single transaction or a batch via CSV upload. This step automatically pulls in essential details like the recipient, amount, and business purpose, aligning them with stablecoin compliance policies. Each payment intent is assigned a unique Payment Intent ID and requires a business reference, such as an invoice number or payroll batch ID, to ensure traceability.
The system then performs pre-flight checks to verify the intent. These checks include validating policy limits, scanning for sanctions, identifying behavioral anomalies, and assessing freeze-risk. The result is a Risk Dossier with a verdict of PASS, FLAG, or BLOCK. As Stablerail aptly explains:
"Every payment is simulated before execution. First-time destinations, address changes, and duplicates are caught before you sign."
Once automated checks are complete, the process moves to human review. This phase ensures final approval through manual oversight. If the checks pass, the transaction proceeds to execution. If flagged, the payment remains locked until an override is provided, with the reason carefully recorded. The Risk Dossier guides reviewers during this step. For high-value transfers, cool-off periods offer additional time for review, reducing the risk of social engineering attempts.
Next, initiate secure MPC (Multi-Party Computation) signing to distribute authority, ensuring no single individual can unilaterally transfer funds. After this, the transaction is securely executed and logged. Each payment generates a CFO-grade Proof-of-Control receipt, which includes all payment details, approvals, the risk verdict, and the transaction hash. This documentation simplifies month-end reconciliations and provides defensible records for auditors, boards, and banking partners.
Conclusion
Insider errors often stem not just from malicious intent but from weak structures and informal processes. When too many people hold unchecked authority and approval workflows lack rigor, mistakes are bound to happen. The solution lies in four key areas: clear policies, strong access controls, pre-sign verification, and continuous monitoring. Together, these create a solid framework to protect your treasury from costly errors.
Policy-as-code transforms organizational guidelines into automated, machine-enforced rules that no one - executives included - can override. Separation of duties ensures that no single individual can take a payment from initiation to execution alone. Pre-sign verification acts as a safeguard by simulating payments to detect issues like altered addresses, duplicate requests, or flagged counterparties before any signatures are applied. Finally, continuous monitoring and reconciliation translate blockchain activity into actionable, audit-ready data, ensuring every transaction aligns with business objectives.
This proactive approach doesn’t just minimize errors - it improves treasury operations. For finance teams managing the staggering $27.6 trillion in stablecoin transactions recorded in 2024, transitioning from passive oversight to active control is no longer optional.
Stablerail exemplifies these principles through an integrated solution that functions as a control layer between custody and transaction execution. By performing mandatory pre-sign checks - such as sanctions screening, policy enforcement, anomaly detection, and counterparty risk analysis - Stablerail ensures transactions are secure before they’re signed. As they put it:
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money".
Each transaction generates a CFO-grade Proof-of-Control receipt, simplifying audits and board reviews. These measures reinforce the idea that structured governance is the cornerstone of reducing insider errors, ensuring stablecoin treasury operations remain secure and efficient.
FAQs
What are the top controls to prevent irreversible stablecoin payment mistakes?
To avoid permanent mistakes in stablecoin payments, it's crucial to have strong systems for governance, verification, and audits. Some essential measures include:
Policy-as-code governance: This enforces rules automatically, such as requiring CFO approval for high-value transactions or blocking transfers on specific networks.
Mandatory pre-sign checks: These checks can include sanctions screening and detecting anomalies before transactions are finalized.
Human-in-the-loop approvals: Adding a layer of manual oversight ensures critical transactions get reviewed by the right people.
Additionally, keeping a detailed audit trail is vital. It promotes transparency, holds parties accountable, and minimizes the likelihood of errors or risks during the transaction process.
How does policy-as-code prevent errors before signing a transaction?
Policy-as-code helps eliminate mistakes by enforcing predefined rules, policies, and limits automatically during the verification process. If a transaction doesn't meet these policies, it's stopped before reaching the signing stage. This approach ensures everything stays compliant while minimizing potential risks.
What should daily monitoring and reconciliation include for stablecoin treasury?
Daily monitoring and reconciliation for a stablecoin treasury play a crucial role in ensuring transaction accuracy, compliance, and overall integrity. This process involves several key steps:
Transaction Verification: Confirm that all transactions align with established policies, approval protocols, and set limits. This helps maintain control and prevents any deviations from the rules.
Sanctions and Anomaly Screening: Regularly screen for any sanctions violations or unusual activity. Identifying anomalies early can help mitigate potential risks.
Audit Trails: Maintain detailed records at every stage of a transaction. These audit trails are essential for accountability and transparency.
Reconciliation focuses on ensuring that all balances and records are accurate. This includes:
Balance Confirmation Across Chains: Cross-check balances across different blockchain networks to ensure consistency.
Record Matching: Align internal records with on-chain activity to verify that everything matches up.
Risk Assessments: Conduct periodic risk evaluations to identify and address errors or unauthorized transactions before they escalate.
Together, these practices help safeguard the treasury and uphold the reliability of a stablecoin system.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


