
Stablecoin payment limits are critical for secure and efficient treasury operations. They help prevent fraud, meet compliance standards, and ensure financial oversight by automating controls directly into transaction workflows. With stablecoin transactions exceeding $6 billion monthly in 2025, organizations face rising risks like payment fraud (79% reported attempts in 2024). Payment limits address these challenges by:
Reducing fraud risks: Blocking unauthorized transfers, enforcing tiered approvals, and limiting transaction amounts.
Meeting regulatory standards: Automating anti-money laundering (AML) and sanctions compliance with policy-based rules.
Improving oversight: Streamlining approvals and maintaining real-time audit trails for transparency.
For example, systems like Stablerail enforce rules such as "Weekend transfers over $10,000 require CFO approval" before signing occurs. These safeguards protect funds while maintaining the speed of blockchain payments, offering a modern solution to treasury governance challenges.
Stablecoin Treasury, Built for Institutions
Why Payment Limits Matter in Treasury Governance
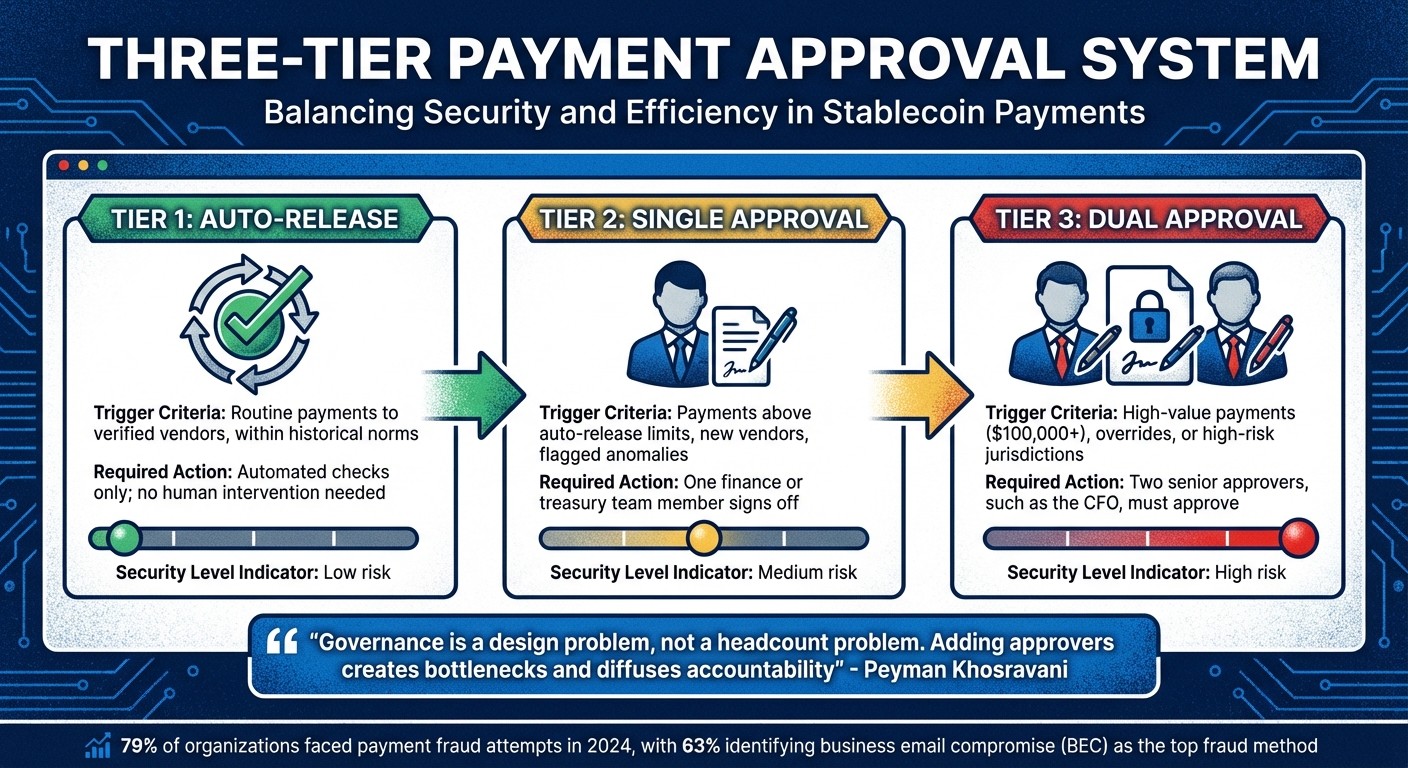
Three-Tier Stablecoin Payment Approval System: Security vs Efficiency
Payment limits turn high-level treasury policies into practical safeguards that kick in automatically before any transaction touches the blockchain. They establish thresholds that help prevent mistakes, ensure compliance, and mimic the trusted controls used in traditional banking.
Reducing Operational and Fraud Risks
With stablecoin transactions being irreversible, having controls in place before the transaction is critical. Once a transfer is completed on-chain - usually within minutes - there’s no way to reverse it, no chargebacks, and no bank to intervene. Payment limits act as a proactive defense, blocking unauthorized transfers and capping financial risk before funds leave the wallet.
A survey conducted in 2025 showed that 79% of organizations faced payment fraud attempts in 2024, with 63% identifying business email compromise (BEC) as the top fraud method. In these cases, attackers often pose as a CFO or vendor to authorize fake payments. Payment limits help counter this risk by using a tiered approval system that routes transactions based on their amount and risk level. For instance, if a $150,000 wire is requested for a new vendor, dual approval is triggered automatically, ensuring a single compromised account can’t drain the treasury.
This three-tier system balances security and efficiency:
Approval Tier | Trigger Criteria | Required Action |
|---|---|---|
Tier 1: Auto-Release | Routine payments to verified vendors, within historical norms | Automated checks only; no human intervention needed |
Tier 2: Single Approval | Payments above auto-release limits, new vendors, flagged anomalies | One finance or treasury team member signs off |
Tier 3: Dual Approval | High-value payments ($100,000+), overrides, or high-risk jurisdictions | Two senior approvers, such as the CFO, must approve |
As Peyman Khosravani, an industry expert, explains:
"Governance is a design problem, not a headcount problem. Adding approvers creates bottlenecks and diffuses accountability".
This system ensures routine payments flow smoothly under Tier 1 while high-risk transactions receive the scrutiny they deserve under Tier 3. It also aligns with regulatory requirements, which we’ll explore next.
Meeting Regulatory Requirements
Payment limits are essential for meeting anti-money laundering (AML) and sanctions compliance standards. Under the 2025 GENIUS Act, stablecoin issuers must maintain 1:1 reserve backing and provide monthly attestations signed by CEOs and CFOs. For companies using stablecoins, this means implementing structured payment controls that can be audited and defended.
Compliance-as-Infrastructure replaces traditional manual reviews with automated, real-time policies that govern transactions. Payment limits are a key part of this, embedding compliance rules directly into the system. For example, a policy might block payments over $50,000 to jurisdictions flagged by OFAC sanctions, regardless of who initiates the transfer.
This rule-based transaction model ensures payments only proceed if specific compliance criteria - like jurisdiction checks or counterparty verification - are met. Compliance becomes part of the transaction process itself, not an afterthought. Beyond regulatory adherence, payment limits also provide a framework for better financial oversight.
Maintaining Financial Oversight and Control
Payment limits give CFOs and finance teams the tools to enforce policies efficiently while scaling their oversight capabilities. With B2B stablecoin payments exceeding $6 billion monthly and total transaction volumes surpassing $27.6 trillion - 7.68% higher than the combined volume of Visa and Mastercard - the need for streamlined oversight has never been more pressing.
Despite this, 98% of companies still relied on manual processes for some payment operations as of 2025, creating inefficiencies. Payment limits streamline operations by automating routine decisions while reserving human judgment for higher-risk scenarios. A tiered system allows for the use of a "warm" wallet for smaller, routine payouts with lower limits, while a "cold" wallet with stricter approval requirements handles larger transfers.
Risk-based routing further enhances oversight by escalating approvals based on contextual risk factors, such as first-time vendor payments, address changes, or unusual transaction timings. For example, an address-change lock could automatically escalate any payment to a vendor with a recently updated address, regardless of the amount. This prevents attackers from exploiting impersonation schemes.
The philosophy behind these controls is straightforward:
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money".
Types of Payment Limits for Stablecoin Treasuries
Payment limits play a crucial role in reducing fraud and maintaining control over stablecoin treasuries. However, there's no universal approach - different types of limits serve distinct purposes, and many organizations use a combination of them for better protection. The main objective? To minimize risk exposure while ensuring legitimate transactions proceed without unnecessary friction. Here's a breakdown of the key categories and how they function.
Daily and Per-Transaction Limits
Per-transaction limits define the maximum amount allowed for a single payment, while daily limits (also called velocity limits) restrict the total amount that can be transferred in a 24-hour period. These two controls work together to block both large-scale theft and gradual schemes where smaller amounts are stolen over time.
For example, a treasury might enforce a $100,000 cap per transaction alongside a $250,000 daily limit. This setup ensures no single payment exceeds $100,000, and even multiple smaller payments can't collectively surpass $250,000 in any rolling 24-hour window. If an attacker gains access to a signing key, these limits act as safeguards, reducing potential losses until the breach is addressed.
Such limits are particularly effective against threats like business email compromise (BEC), where fraudsters impersonate executives to authorize fake transfers.
Time-Based Restrictions
Time-based restrictions add another layer of security by controlling when high-value transfers can occur. These controls are especially useful during weekends, holidays, or non-business hours - timeframes when legitimate payments are less likely. For instance, a $150,000 transfer initiated at 2 a.m. on a Saturday would automatically trigger additional scrutiny.
Organizations can implement these restrictions in two ways:
Hard block: Prevents payments above a certain amount from being processed outside designated business hours.
Cool-off delay: Pauses the transaction for a set period, such as four hours, to allow for verification.
For example, a policy might state: “Any transfer over $100,000 initiated outside 9 a.m.–5 p.m. EST, Monday–Friday, requires a four-hour delay and dual approval”. This approach is particularly effective against social engineering attacks, where fraudsters exploit off-hour urgency to bypass normal approval processes.
Counterparty and Address Approval Policies
Counterparty whitelisting ensures payments are only sent to pre-approved wallet addresses, reducing the risk of funds being misdirected. This involves maintaining a vetted list of vendor wallet addresses, verified during onboarding. Payments to any address not on the whitelist are either blocked or escalated for manual review.
For instance, a policy might require: “New address payments over $5,000 need CFO approval and verification”. These limits are enforced through policy-as-code, where programmatically applied rules ensure every transaction adheres to established policies before being signed. Even if a senior executive initiates a payment, the system won’t process it unless the recipient address is pre-approved or the required approvals are in place. This seamless integration with treasury governance frameworks ensures compliance at every step.
Limit Type | Function | Primary Risk Mitigated |
|---|---|---|
Per-Transaction | Caps the amount of a single transfer | Large-scale theft or single-event errors |
Daily/Velocity | Caps total volume over time | Gradual theft or high-frequency errors |
Time-Based | Restricts transfers to business hours or adds delays | Off-hour fraud and social engineering |
Address Whitelist | Limits recipients to pre-approved wallets | Misdirected funds and phishing attempts |
How Stablerail Enforces Payment Limits

Stablerail takes a proactive approach to payment security, stepping away from traditional methods by applying rules before any signing occurs. Acting as a governance layer above custody, the platform ensures full control of keys through MPC-secured vaults while enforcing strict pre-signature controls. This setup allows for contextual verification before any transaction is signed, creating a safer and more controlled environment. It all begins with well-defined, automated policies.
Setting Up Automated Payment Policies
The Policy Console provides CFOs and finance leaders with the tools to establish machine-enforceable rules for every payment. Instead of relying on manual approvals, policies are encoded directly into the system as policy-as-code. This automated governance mirrors the controls used in traditional banking. For instance, a rule like "Payments over $5,000 to new addresses require CFO approval and verification" is automatically enforced - transactions won't proceed unless all conditions are met.
These policies are flexible and can adapt to specific risk levels. For example, a treasury handling $10 million annually might use a three-tiered approach: payments under $1,000 are auto-approved, those between $1,000 and $25,000 require single approval, and anything above $25,000 demands dual approval. Additional rules might restrict certain stablecoins to specific chains (e.g., "Only allow USDC on Base/Ethereum") or impose automatic cool-off periods when daily outflows exceed $100,000.
Pre-Sign Checks and Risk Dossiers
Before any payment is executed, Stablerail's system generates a detailed Risk Dossier that assigns a PASS, FLAG, or BLOCK verdict. This dossier performs multiple checks simultaneously, including sanctions screening, taint and exposure analysis, counterparty risk evaluation, and behavioral anomaly detection. Each finding is tied to specific policy clauses and timestamps, ensuring that approvers understand the reasoning behind any flagged issues.
"Every payment is simulated before execution. First-time destinations, address changes, and duplicates are caught before you sign." - Stablerail
Approval Workflows and Audit Trails
If a transaction is flagged, Stablerail routes it through a tailored, multi-step approval process. High-risk payments automatically trigger stricter verification measures. For example, a transfer exceeding $100,000 might require both the CFO's approval and a mandatory cool-off period to prevent social engineering attacks. Similarly, if a vendor's wallet address changes in the "Golden Source" system, the account is locked and escalated for review before any payment can proceed.
Each action is meticulously documented. Every payout generates a Proof-of-Control receipt that finance teams can use for audits, board reviews, or regulatory compliance. This replaces the fragmented records often scattered across emails and chat logs. Such audit-ready documentation is critical, especially considering that 79% of organizations faced payment fraud in 2024, with 63% affected by business email compromise.
Feature | Manual Wallet/Spreadsheet Process | Stablerail Policy-Enforced Process |
|---|---|---|
Approvals | Informal (Slack, Telegram, Email) | Formal, multi-step policy engine |
Risk Checks | Manual or after the fact | Real-time, AI-driven pre-signature checks |
Signing | "Blind signing" of technical data | Human-readable, contextual signing |
Audit Trail | Hidden in chat logs or manual records | Automated, tamper-evident logs |
Visibility | Requires manual reconciliation | Real-time treasury dashboard |
This structured approach not only tightens security but also streamlines compliance, setting the stage for further benefits discussed in the next section.
Benefits of Payment Limits in Stablecoin Treasury Operations
Payment limits bring a structured approach to managing stablecoin treasuries, shifting the focus from reactive problem-solving to proactive risk management. When implemented effectively, these controls safeguard funds, enforce company policies, and meet regulatory standards - all while maintaining smooth business operations.
Better Financial Security
Payment limits act as a protective barrier, reducing the risk of major losses. A tiered approval system ensures that the level of scrutiny matches the transaction size:
Routine, low-risk payments: Automatically processed after basic checks.
Mid-level transfers: Require a single approval.
High-value transactions (e.g., over $100,000): Trigger dual authorization and include mandatory cool-off periods.
These cool-off periods, often around four hours for large or first-time transactions, provide crucial time to identify and stop potential fraud, such as social engineering attacks. Velocity caps further minimize risks by limiting how quickly funds can be drained, even if credentials are compromised.
Another key feature is the enforcement of policies through code, which ensures that no individual - executives included - can override the rules. Additionally, separating duties ensures that the person initiating a payment cannot approve or finalize it, reducing the risk of insider threats.
Stronger Policy Adherence and Decision-Making
By encoding payment limits directly into systems, organizations eliminate the guesswork and inconsistencies of manual processes. For instance, if a vendor’s wallet address changes, the system automatically locks the account and escalates for review. This ensures funds can’t be redirected to fraudulent accounts without multiple layers of oversight.
This structured approach doesn’t just prevent fraud; it also improves overall decision-making. Every payment decision is documented in real-time, creating a transparent and accountable process. Teams spend less time dealing with exceptions and more time focusing on strategic goals. This integration of compliance into daily operations turns what was once a back-office task into an active framework that governs payment approvals and routing.
Compliance and Audit Readiness
Payment limits also simplify compliance by automating documentation. Every transaction generates a clear record, including payment details, approval chains, and risk assessments - exactly what auditors and boards require. This is especially critical given that, as of 2025, 98% of companies still rely on some manual payment processes, leaving gaps in audit trails.
For high-risk events, such as policy overrides, automated tracking ensures that exceptions are flagged for independent review and require detailed business justifications. For example, if a $150,000 payment is approved on a weekend, the system logs all relevant details - timestamps, policy references, and approval chains - in a tamper-proof format. With B2B stablecoin transactions surpassing $6 billion per month by mid-2025, this level of rigor is critical for protecting treasury assets and maintaining trust with regulators and stakeholders.
Conclusion
Payment limits play a key role in protecting assets, enforcing policies, and meeting regulatory requirements. With the rise in fraud and increasing transaction volumes, the need for real-time, effective controls has never been greater.
Today's governance tools operate seamlessly in real time, embedding compliance into every transaction. By integrating payment limits directly into workflows, businesses can prevent unauthorized transfers, enforce tiered approval processes, and automatically generate audit-ready records.
A great example of this is Stablerail, which represents a new standard in treasury governance. Positioned between custody and transaction signing, it provides finance teams with the same level of control they expect from traditional banking, all while maintaining the speed of blockchain settlements. With features like policy-as-code enforcement, pre-signature risk checks, and detailed audit trails, organizations can implement rules such as "Weekend transfers over $10,000 require additional approval" and trust that every transaction complies automatically - no manual oversight needed.
For companies handling annual transactions between $1 million and $50 million, Stablerail's non-custodial framework ensures funds are secure while enforcing critical business rules. Each payment generates a comprehensive record, including timestamps, approval chains, policy references, and risk evaluations - exactly what auditors and boards require.
Chiara Munaretto, Co-founder and Managing Partner at Stablecoin Insider, captures the potential of this approach:
"With stablecoins' market cap surging toward ~$300 billion... it's clear the real drag on global commerce was intermediaries. Let's let stablecoins do their job."
FAQs
What payment limits should a stablecoin treasury set first?
To begin, establish payment limits that focus on high-risk transactions and ensure compliance. For example, you could require CFO approval for payments over $5,000 or mandate extra authorization for weekend transfers above $10,000. Implement policy-as-code governance to automate these rules, guaranteeing that every transaction is reviewed before approval. Start with thresholds that match your risk tolerance and regulatory requirements, and fine-tune them over time as your treasury processes evolve to uphold both security and compliance.
How do payment limits reduce BEC and wallet-drain fraud risk?
Payment limits play a key role in minimizing the risk of Business Email Compromise (BEC) and wallet-drain fraud. By implementing strict policies, automating pre-sign checks, and requiring multiple layers of approval, these measures help prevent unauthorized or suspicious transactions from slipping through the cracks. This approach ensures tighter control over financial operations and enhances overall security.
How does Stablerail enforce limits before signing a transaction?
Stablerail uses automated pre-sign checks and policy-as-code governance to enforce strict transaction limits. Before any signing occurs, it runs a series of verifications, including sanctions screening, exposure analysis, anomaly detection, and counterparty risk scoring.
Organizations can set enforceable rules, such as transaction limits or specific approval workflows, which are automatically applied to every transaction intent. This approach ensures adherence to compliance standards and helps block unauthorized or high-risk transactions, effectively minimizing both operational and regulatory risks.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


