
Managing treasury operations requires control, verification, and accountability - especially with irreversible digital transactions like stablecoin payments. Yet, many organizations still rely on outdated, manual processes that increase risks of fraud, errors, and compliance failures. Multi-step approvals solve these problems by introducing structured workflows with clear roles, tiered checks, and automated safeguards.
Key Takeaways:
Fraud Prevention: Dividing responsibilities (e.g., initiators, approvers, signers) reduces single points of failure. For example, Radiant Capital’s $53M loss in 2024 could have been avoided with stricter role segregation.
Error Reduction: Multiple reviews catch issues like duplicate payments or incorrect wallet addresses before funds are moved.
Policy Enforcement: Tiered approval hierarchies ensure low-risk payments move quickly, while high-risk transactions require senior sign-offs.
Automation: Machine-enforced rules and real-time notifications streamline processes and ensure compliance with regulations like SOX.
Transparency: Immutable audit trails link every transaction to its business purpose, simplifying audits and improving accountability.
By integrating multi-step approvals into treasury systems, organizations can safeguard funds, meet regulatory requirements, and maintain operational efficiency without compromising security.
Digitizing treasury workflows with TIP
How Multi-Step Approvals Strengthen Governance
Multi-Step Treasury Approval Workflow: From Initiation to Execution
Strong treasury governance isn't about bogging down processes with unnecessary red tape - it's about spreading responsibility to ensure no single person can execute high-risk transactions alone. Multi-step approvals create a system where different roles handle specific parts of the transaction process, ensuring every transaction is reviewed thoroughly before any funds are moved.
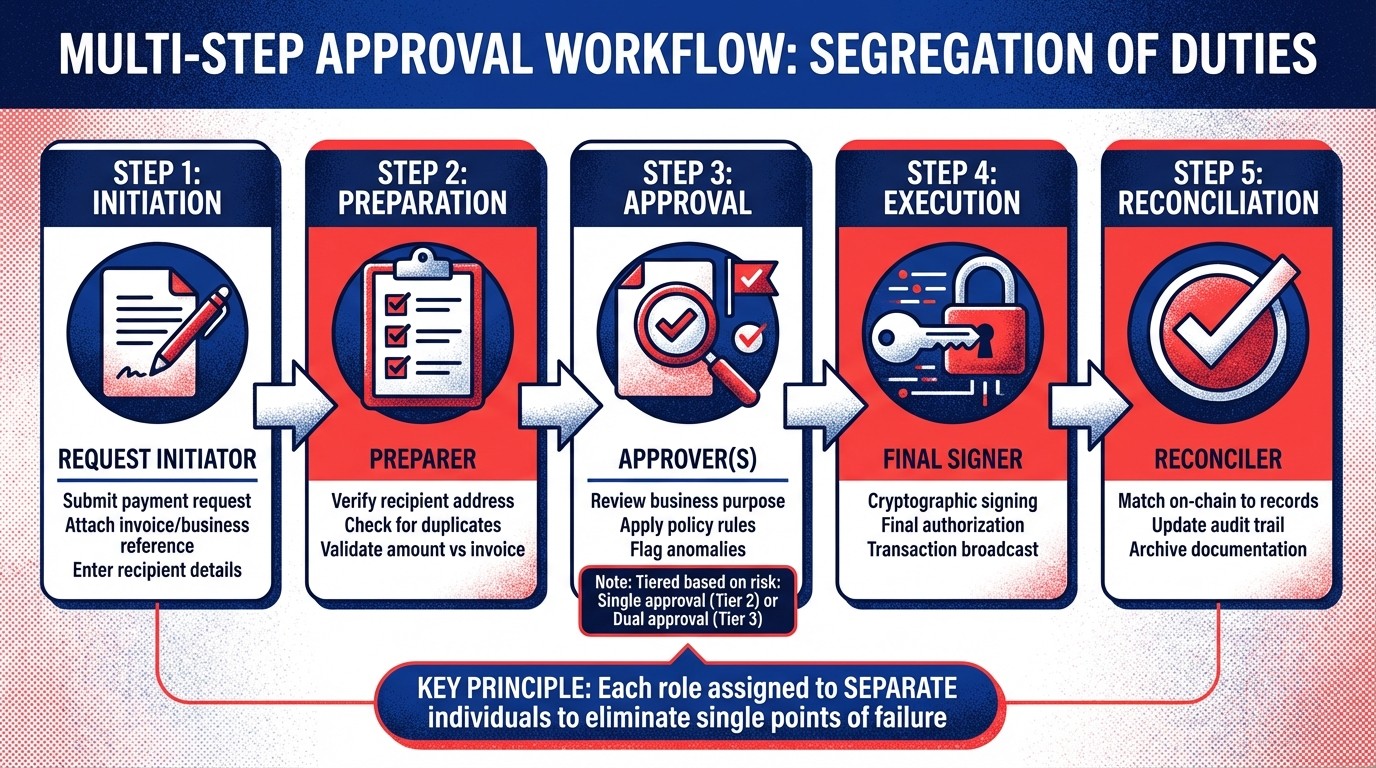
Segregation of Duties
One key principle in governance is dividing the transaction process into distinct roles: initiation, approval, and execution. Each of these roles - request initiator, approver, and final signer - should be assigned to separate individuals. This separation reduces the risk of a single point of failure, where one compromised account or individual could jeopardize the organization’s treasury.
Take the case of Radiant Capital in October 2024, where a compromised multisig setup led to a $53 million loss. Attackers targeted individuals with signing authority, exploiting the lack of proper role segregation. If stricter role-based controls had been in place, the breach would have required compromising multiple independent parties across different stages of verification - a far more challenging task.
For organizations managing stablecoin payments, this separation of duties is even more vital. Unlike traditional banking, where fraudulent transactions might be reversed, blockchain transactions are permanent. Multiple layers of review - such as verifying recipient details and enforcing transaction policies and verifying crypto compliance - add critical safeguards. By dividing responsibilities, organizations can implement tiered approval processes that adapt based on the risk level of each transaction.
Policy Enforcement Through Approval Hierarchies
Building on the foundation of role segregation, tiered approval hierarchies further enhance governance and risk management. These hierarchies allow finance teams to tailor their oversight based on transaction specifics. For example, routine, low-value transactions might proceed automatically after basic checks, while high-value or unusual transactions require human review or even executive escalation. This approach ensures efficiency without sacrificing oversight - small payments to vendors might not need the CFO’s involvement, but a $50,000 transfer to a new wallet would trigger additional scrutiny.
Here’s a comparison of how tiered approvals stack up against single-signer controls:
Feature | Tiered Approval | Single-Signer Control |
|---|---|---|
Governance | Multi-layered roles, automated policy enforcement | Single-key or basic multisig setup |
Fraud Prevention | High (MPC, dual control, automated checks) | Low (prone to key compromise) |
Efficiency | Automated workflows, batch processing | Manual processes, time-intensive |
Auditability | Detailed, immutable audit trails | Limited, manual reconciliation |
Tiered systems also ensure consistency. Instead of relying on individual judgment, the system applies uniform rules to transactions. For instance, any payment over $5,000 to a new vendor would always require additional verification, while weekend transfers above a certain threshold might need senior-level approval. This standardized approach eliminates ambiguity and ensures that policies are enforced, even during times when key personnel are unavailable.
Risk Reduction Through Structured Approval Workflows
Structured approval workflows are a critical tool for reducing risks in treasury operations. By incorporating multiple checkpoints before executing any transaction, these workflows help deter fraud, prevent compliance violations, and minimize costly mistakes. This is especially important for companies managing stablecoin payments, where transactions are irreversible. Studies continue to highlight the prevalence of payment fraud and business email compromise (BEC) schemes, making these safeguards indispensable.
Fraud Prevention
Multi-step approvals act as a strong defense against fraudulent transactions. With 98% of companies still relying on some level of manual payment operations, the risks of human error and fraud remain significant. Structured workflows address this vulnerability by requiring multiple independent reviews and approvals before any transaction is finalized.
Imagine a scenario where an attacker gains access to an employee’s credentials through a phishing attack. In a single-signer system, this breach could result in immediate financial loss. However, in a structured approval process, the attacker would need to bypass multiple layers of authentication and verification, significantly increasing the chances of detection before any damage occurs.
Modern systems enhance these protections by using automated risk assessments during the pre-signing phase. These automated tools screen transactions for red flags such as sanctions violations, unusual behavior patterns, and counterparty risks. For instance, a payment to a new vendor address initiated at 2:00 AM on a Sunday could automatically be flagged for review, requiring explicit human approval and documented reasoning before proceeding. This layered approach not only reduces fraud but also supports adherence to regulatory requirements.
Regulatory Compliance
Structured workflows are a cornerstone for adhering to regulations like Sarbanes-Oxley (SOX) and new rules for digital assets. They enforce governance policies through machine-executable rules, ensuring that spending limits, whitelists, and approval hierarchies are followed without exception - even by top executives.
Every step in the workflow, from initial intent to the final cryptographic signature, is logged in a tamper-proof audit trail. This creates defensible evidence for regulators and auditors. For example, if a high-value transaction requires CFO approval, the system records the approval, along with the timestamp, previous risk assessments, and any documented exceptions. This level of transparency transforms compliance from a reactive process into an integrated feature of every transaction.
For organizations managing digital assets, embedding regulatory requirements directly into the treasury system ensures compliance in real time - before the funds are ever moved.
Error Reduction
Structured workflows also play a vital role in minimizing human errors that can lead to costly outcomes. Mistakes like entering the wrong wallet address or duplicating a transaction can result in permanent loss of funds on the blockchain. By introducing multiple layers of review, these workflows help catch such errors before they occur.
Assigning distinct roles - like Requester, Preparer, Approver, Signer, and Reconciler - to different individuals ensures that each transaction is examined from multiple perspectives. For instance, the preparer might notice a typo in the recipient address, the approver might flag a mismatch between the payment amount and the invoice, and the signer might catch a duplicate payment to the same vendor in a single batch.
Automated simulations further strengthen this process. Before requesting a signature, the system can run checks to detect duplicates, verify address changes, and confirm that transaction details align with business references. Requiring mandatory business references - such as tying transactions to specific invoice IDs, payroll batches, or contracts - ensures that every blockchain transaction is traceable to its business purpose. This eliminates ambiguity and provides a clear, audit-ready trail linking on-chain activity to internal records.
Technology's Role in Automating Approval Processes
Automation is reshaping how approval processes work, turning outdated manual methods into streamlined, efficient systems. These automated solutions consistently enforce rules, notify the right people in real time, and maintain a detailed record of every decision. This shift is especially important in treasury operations involving stablecoins, where transactions are irreversible, and monthly B2B payments in stablecoins surpassed $6 billion by mid-2025.
Consistency Through Automation
Manual processes often rely on individuals to remember and correctly follow procedures, leaving room for error. Automation eliminates this variability by embedding governance rules directly into transaction workflows. This ensures that every payment adheres to the required checks, no matter who initiates it or when it occurs. By integrating seamlessly with existing multi-step approval systems, automation not only improves consistency but also simplifies the entire process.
Machine-Enforceable Policies
Policy-as-code systems take treasury policies and translate them into machine-readable rules that are automatically enforced. Instead of relying on static documents like PDFs or wikis that employees might overlook, these policies are built directly into the payment infrastructure. For instance, a rule such as "New address payments over $5,000 require CFO approval and verification" becomes a non-negotiable constraint enforced by the system before any signature can be requested.
This approach ensures no one, not even executives, can bypass mandatory approval workflows. Every transaction, whether it's a $500 routine payment or a $50,000 transfer to a new vendor, undergoes the same rigorous checks. By embedding governance into the code, the process aligns perfectly with multi-layered approval strategies.
Speed and Real-Time Notifications
Automated systems speed up approvals by instantly notifying the right individuals when their input is needed. These real-time alerts direct approvers to a centralized dashboard where they can quickly access transaction details, risk assessments, and supporting documents, all in one place.
When a payment requires review, the system automatically routes it to the appropriate person based on predefined roles and thresholds. For example, if a high-value transaction needs the CFO's approval, they receive an instant notification complete with all the necessary context - invoice details, counterparty risk scores, and any flagged anomalies. This data helps teams evaluate stablecoin risks before finalizing high-value transfers. This allows for informed decisions in minutes rather than hours. Mobile co-signing adds even more flexibility, enabling approvals on the go while maintaining visibility through web-based dashboards.
Transparent Audit Trails
In addition to speeding up approvals, automated systems create detailed audit trails that ensure accountability. These systems maintain tamper-proof records that auditors and regulators can easily review. For every step in the process, the system logs user identities, timestamps, decision rationales, and supporting evidence.
The contrast between manual and automated systems is striking:
Feature | Manual/Simple Signer Systems | Automated/Role-Based Systems |
|---|---|---|
Approvals | Informal (Slack/Email/Chat) | Formal, system-enforced multi-step workflows |
Audit Trail | Manual reconciliation of spreadsheets | Automated, immutable, tamper-evident logs |
Transparency | "Blind signing" of technical data | Human-readable risk dossiers and dashboards |
Accountability | Difficult to attribute keys to individuals | Identity-based logs for every action and override |
Risk Detection | Post-event reconstruction | Real-time, pre-signature anomaly detection |
For any exceptions or policy overrides, the system enforces independent authorization and requires documented justification. This ensures that every deviation is accounted for, closing any potential gaps in governance.
Customizing Approval Workflows for Treasury Operations
Every organization has its own risk tolerance and governance structure, which means approval workflows need to be tailored to fit specific operational needs. For instance, one company might require dual CFO sign-offs for certain payments, while another might allow similar transactions to be auto-released. The key is to embed risk-conscious controls into existing automated systems.
Role-Based Access and Responsibility Assignment
Approval authority should align with expertise rather than hierarchy. For example, a controller reviewing vendor invoices might bring more operational insight than a CEO tasked with the same review. As Peyman Khosravani puts it:
Governance is a design problem, not a headcount problem: Adding approvers creates bottlenecks and diffuses accountability.
Modern systems reflect organizational roles in payment policies. For instance, routine vendor payments under $10,000 might only need the accounts payable manager’s approval, while any new vendor relationship - regardless of the amount - requires CFO sign-off. Override authority should be limited to specific senior roles, like the CFO or Controller, and every override must include mandatory documentation for accountability.
Approval Triggers and Thresholds
A dynamic 3-tier matrix can route payments based on risk factors rather than just dollar amounts:
Tier | Category | Triggers | Approval Requirement |
|---|---|---|---|
Tier 1 | Auto-Release | Routine, within historical norms, verified vendor | Automated checks |
Tier 2 | Single Approval | New/modified vendors, above routine ceiling | One finance/treasury member |
Tier 3 | Dual Approval | $100,000+, high-risk jurisdictions, off-hours | Two independent senior approvers |
This system emphasizes that transaction risk stems from context - like vendor history and timing - rather than just the payment amount.
Dual-Control for High-Risk Transactions
For high-risk payments, dual-control measures require two independent approvers who were not involved in initiating the transaction. This is essential for scenarios like payments over $100,000, transfers to high-risk jurisdictions, or transactions flagged by anomaly detection systems. The second approver acts as an additional safeguard. If a fraudulent request slips past one reviewer, the second layer of independent review greatly increases the chances of catching it before funds are released.
Benefits of Multi-Step Approvals for Treasury Management
Multi-step approvals bring a new level of efficiency to treasury operations, improving cash flow forecasting, liquidity management, and decision-making.
Improved Cash Flow Forecasting
Traditional systems often provide visibility only after transactions are completed, but multi-step workflows change that by revealing payment intents in advance. This allows CFOs to anticipate upcoming liabilities and refine cash runway predictions.
For instance, approval service-level agreements (SLAs) create predictable timelines for payments. If vendor payments under $10,000 typically clear two approval steps within four hours, and high-value transfers over $100,000 include a required four-hour cooling-off period, treasury teams can precisely calculate when funds will leave the account. This level of predictability eliminates guesswork and stabilizes short-term cash flow planning, which is often disrupted by manual coordination via Slack or email.
Additionally, batch payouts consolidate daily outflows into planned liquidity blocks. This approach helps maintain minimum balance requirements and ensures working capital is optimized across accounts.
These proactive measures offer better visibility and tie seamlessly into enhanced payment transparency.
Payment Transparency
Real-time data from automated workflows gives treasury teams a clear view of payment activity. By linking on-chain transactions directly to internal records, teams can avoid the surprises that often surface during end-of-month reconciliations.
Each payment comes with a complete audit trail, detailing who requested it, who approved it, which policies were verified, and when it was executed. This transforms reconciliation into a simple verification process rather than a time-consuming investigation.
With this level of clarity, treasury teams can maintain control over liquidity and risk in real time, enabling smarter, faster decisions.
Multi-Step Approvals in Digital Asset Treasuries
Blockchain treasuries, unlike traditional systems, operate in a world where transactions are irreversible, pseudonymous, and constantly active. These unique challenges demand additional safeguards that go beyond standard governance protocols. Multi-step approvals, designed specifically for this decentralized environment, provide the governance layer necessary to manage digital asset operations effectively.
Below, we’ll explore how machine-enforceable policies, automated risk assessments, and immutable audit trails address these challenges head-on.
Policy-as-Code for On-Chain Payments
Machine-enforceable policies act as automated guardrails, ensuring every transaction complies with pre-defined business rules before it even reaches the blockchain. Rather than relying on manual checks or sporadic approvals, treasury teams can set these rules to enforce consistency across all transactions.
Take this scenario: a policy could require CFO approval for payments over $5,000 to new wallet addresses or mandate additional checks for transfers exceeding $10,000 during weekends. These rules, when encoded, automatically assess every payment intent and block any transaction that violates policy - before it’s signed. This is critical, especially considering that 79% of organizations faced payment fraud in 2024, with business email compromise being a major threat. By removing subjective decision-making, policy-as-code ensures consistent enforcement.
Stablerail’s Policy Console exemplifies this approach. It allows finance teams to define role-based limits and approval workflows that apply across various blockchain networks and stablecoins. Using Multi-Party Computation (MPC), the platform distributes signing authority across multiple parties, preventing any single individual or compromised device from unilaterally moving funds.
Pre-Transaction Verification and Risk Management
Before any payment is executed on-chain, automated systems perform pre-sign risk checks to assess potential issues. These verifications are crucial for catching risks that manual reviews, especially under time constraints, might overlook.
Stablerail’s automated controls conduct thorough checks, including sanctions screening, taint and exposure analysis, behavioral anomaly detection, and counterparty risk scoring. The system evaluates whether the payment amount deviates from normal patterns, whether the recipient’s wallet address has been flagged for risk, and whether the timing aligns with standard business hours. Based on these assessments, transactions are categorized as PASS, FLAG, or BLOCK.
This tiered framework automates routine approvals while escalating anomalies for human intervention. By automating low-risk decisions and focusing human attention on flagged transactions, this approach strikes a balance between speed and control.
Immutable Audit Trails for Blockchain Operations
Every treasury action, from initiating a payment to final execution, is logged in an immutable record. This audit trail provides a transparent and verifiable account of who initiated a payment, which policies were applied, what risks were flagged, and who approved or overrode decisions.
These structured records tie on-chain transactions directly to internal governance processes. For example, if a regulator questions why a flagged payment was approved, treasury teams can easily produce a detailed decision chain with timestamps and justifications.
Stablerail enhances this process by maintaining a comprehensive audit trail for every transaction. Its "golden source" whitelists, protected by change-locks, prevent errors like address substitutions, which could lead to funds being sent to the wrong recipient. This is especially important for companies handling between $1 million and $50 million annually in stablecoin transactions, where both transaction volume and regulatory scrutiny demand precise record-keeping.
These measures demonstrate how multi-step approvals can reinforce governance, providing the structure and security needed for both traditional and digital asset treasuries.
Conclusion
Multi-step approvals bring a structured approach to governance, striking a balance between efficiency and control. By distributing responsibilities across different roles, these workflows help reduce fraud, errors, and compliance issues. This separation ensures that no single individual has full control over the payment process - a critical safeguard, whether you're dealing with traditional bank transfers or stablecoin transactions.
Expanding on this concept, programmable governance offers a forward-thinking solution. Instead of relying on spreadsheets or messaging apps to manage approvals, organizations can now integrate approval hierarchies directly into their payment systems. This not only removes manual inefficiencies but also upholds the level of oversight that CFOs and auditors require.
For digital asset operations, where transactions are irreversible and function around the clock, structured workflows are indispensable. Features like policy-as-code enforcement, automated risk assessments before transactions, and immutable audit trails create the governance framework needed to navigate decentralized systems with confidence. This infrastructure is particularly valuable for organizations managing $1 million to $50 million in annual stablecoin volume, where transaction complexity and regulatory demands are higher.
The impact of these controls goes beyond compliance. Treasury teams using role-based systems gain improvements in cash flow forecasting, payment visibility, and audit readiness. These tools enable secure, scalable operations while providing the transparency and accuracy needed for sound financial management.
As treasury practices continue to evolve, structured approvals transform governance into a strategic advantage rather than a limitation.
FAQs
What’s the difference between multi-step approvals and multisig?
Multi-step approvals are all about maintaining governance and operational control. They involve transactions going through carefully structured stages, such as verification checks, policy enforcement, and human approvals. This process helps ensure compliance, minimizes risks, and provides a detailed audit trail for accountability.
On the other hand, while multisig wallets improve security by requiring multiple private keys, they don't offer the same depth of control. They lack the layered reviews, automated policy checks, and human oversight that are crucial for governance-focused treasury operations.
Which payments should be auto-released vs escalated for dual approval?
High-value or high-risk payments - think transactions over $100,000 or transfers to new or unverified addresses - should go through a dual approval process. This extra layer of oversight helps minimize risks like fraud or costly errors. On the other hand, routine, low-value payments that fall within policy limits, such as transfers to trusted recipients, can be automatically processed. This tiered system strikes a balance: it keeps everyday operations efficient while ensuring sensitive transactions get the careful review they need.
How do policy-as-code checks prevent bad stablecoin payments before signing?
Policy-as-code checks help safeguard stablecoin payments by automating pre-transaction verifications to ensure compliance, security, and adherence to policy rules. These automated checks cover areas like sanctions screening, exposure analysis, anomaly detection, counterparty risk scoring, and policy enforcement. By integrating these rules directly into the approval process, every payment intent is evaluated against established policies before it reaches human review. This reduces risks such as errors, fraud, or compliance breaches, while also maintaining a comprehensive audit trail.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


