
Stablecoin transactions face millions in potential fraud risks every year. In 2025 alone, blockchain thefts hit $3.4 billion, with stablecoins accounting for 84% of verified crypto fraud. Once a fraudulent transaction is signed, recovery is nearly impossible. Pre-signature detection offers a way to stop these threats before they happen.
Here’s what you need to know:
Key Risks: Compromised keys, phishing, and logic exploits.
Detection Methods:
Rule-based systems (fast but rigid, high false positives).
Machine learning (better accuracy, but slower and reactive).
Pre-signature systems (like Stablerail, which intercept risks before signing).
Why It Matters: Stablecoin volumes reached $27.6 trillion in 2024, surpassing Visa and Mastercard combined.
Stablerail stands out by combining policy enforcement, behavioral analysis, and audit trails to block suspicious transactions before they’re signed. It reduces false positives, ensures compliance, and provides clear risk reports for finance teams.
For businesses managing millions in stablecoin transactions, pre-signature detection is a critical safeguard against fraud.
The End of SWIFT? How AI and Stablecoins Will Change Cross-Border Payments
1. Stablerail

Stablerail goes beyond just managing transactions - it incorporates thorough pre-signature checks to verify every stablecoin transaction before it’s signed. With its self-custodial architecture, funds are kept secure in MPC wallets for corporate treasury operations. This setup ensures that Stablerail never has unilateral signing authority, leaving finance teams fully in control of their keys while benefiting from enhanced governance.
Here’s a closer look at how Stablerail’s architecture strengthens pre-signature risk controls through detection accuracy, governance policies, and audit capabilities.
Anomaly Detection Accuracy
Stablerail’s detection system is built on domain-specific feature engineering tailored to stablecoin workflows. Before signing a transaction, specialized agents analyze factors like time-of-day anomalies, deviations from typical transaction patterns, and unusual payout behaviors. Additionally, these agents monitor stablecoin-specific risks, such as smart contract freezes or interactions with blacklisted addresses.
For every transaction, the platform generates a Risk Dossier that delivers a clear verdict: PASS, FLAG, or BLOCK. Each dossier includes straightforward explanations, citing relevant policy rules and timestamps, making it easier for finance teams to grasp why certain transactions are flagged.
Governance and Policy Integration
The platform employs policy-as-code governance, enabling finance teams to define enforceable rules like "Payments to new addresses exceeding $5,000 need CFO approval and verification" or "Weekend transfers over $10,000 require additional layers of approval." These rules are automatically applied to all payment intents before they can be signed, ensuring compliance is checked upfront.
This method enforces what’s known as policy-compliant signatures - valid signatures are only generated when both sender and recipient meet the pre-set rules. By verifying compliance before a transaction is signed or broadcast, Stablerail eliminates the chaos of reacting to fraudulent transfers after the fact. Additionally, a detailed audit trail ensures transparency, with every decision recorded for review.
Audit Trail Robustness
To support its governance and compliance measures, Stablerail maintains a comprehensive, CFO-grade audit trail for every action. This includes intent creation, risk assessments, flags, overrides, approvals, and the final signing process. These records provide clear, verifiable evidence that finance teams can present to auditors, boards, or regulators.
The audit trail uses transfer event data from smart contracts to document value flows accurately, even in complex multi-step transactions. This structured workflow replaces the disorganized "wallet + spreadsheet + Slack approvals" approach with a streamlined process: create an intent (via invoice PDF, payout CSV, or API), review the Risk Dossier, approve with documented reasoning, sign using MPC, and receive a transaction receipt complete with evidence.
2. Rule-Based Detection Systems
Rule-based systems act as a straightforward, first layer of defense in pre-signature checks. They rely on static thresholds and straightforward "if-then" logic to flag suspicious activity based on predefined rules. For example, these systems might block transfers exceeding specific monetary limits, detect sudden bursts of transaction activity within a short timeframe, or automatically reject interactions with wallets flagged on blacklists, such as those maintained by the U.S. Office of Foreign Assets Control (OFAC) Specially Designated Nationals list.
Their simplicity and transparency make them appealing to finance teams and regulators. For instance, a rule might flag any transaction above a certain dollar amount, providing a clear and auditable compliance trail. This aligns with regulatory mandates like the EU's Markets in Crypto-Assets (MiCA) and the U.S. GENIUS Act, which emphasize the importance of clear compliance records and reserve backing requirements. However, these systems often struggle to keep up with the ever-changing tactics used in financial crimes.
Anomaly Detection Accuracy
The primary weakness of rule-based systems lies in their rigidity. Sophisticated laundering techniques like chain hopping, mixers, and cross-chain bridges are designed to bypass static thresholds, fragmenting transaction patterns to avoid detection. For instance, while a single large transfer might trigger an alert, multiple smaller transactions that collectively represent a significant amount could go unnoticed. Research from Duke University highlights this inefficiency, showing that traditional rule-based systems often generate false positive rates exceeding 95%.
Despite stablecoins accounting for over 84% of verified crypto fraud volumes in 2025, these systems manage to intercept only about 0.1% of global criminal funds. The problem becomes even more pronounced in high-volume environments, where legitimate businesses process thousands of payments daily. In such cases, static rules often fail to distinguish between normal activity and illicit transactions.
False Positive Rates
One of the biggest challenges with rule-based systems is their high rate of false positives, which significantly drives up compliance costs. With false positives exceeding 95%, compliance teams often spend most of their time investigating legitimate transactions that inadvertently trigger alerts. In Europe alone, these false positives contribute to an estimated $136.5 billion in annual compliance costs.
A recent example highlights the stakes: In November 2023, the U.S. Department of Justice reached a $4.3 billion settlement with Binance after uncovering major failures in anti-money laundering (AML) and sanctions-screening processes. As part of the resolution, Binance was placed under a five-year monitorship and required to meet specific transaction monitoring benchmarks, such as "time-to-freeze" metrics - how quickly suspicious activity leads to an on-chain wallet freeze. This case underscores the urgent need for more precise detection systems that can reduce false positives while improving the ability to intercept illicit activity.
Governance and Policy Integration
Despite their shortcomings, rule-based systems remain essential for enforcing deterministic policies. For example, stablecoin issuers have used these systems to freeze over $4 billion in USDT and more than $1 billion in USDC. These freezes are triggered when rule-based alerts activate smart contract privileges, allowing issuers to blacklist wallets and block transfers or redemptions.
To improve effectiveness, organizations should shift from broad risk labels to specific, measurable metrics. Key performance indicators (KPIs) like "time-to-freeze", "unfreeze error rate", and the percentage of alerts leading to on-chain actions can transform rule-based systems into more precise tools within a broader compliance strategy.
Audit Trail Robustness
One clear advantage of rule-based systems is their ability to produce deterministic audit trails. Every flagged transaction can be traced back to the exact rule that triggered it. For even greater accuracy, these systems should monitor smart contract "Transfer" events rather than raw blockchain transactions. Event logs provide a clearer picture of the actual sender and recipient, even in cases involving relayers or meta-transactions.
This approach creates what researchers call "transparent choke points" - auditable records that remain intact even with privacy-enhancing technologies. For finance teams preparing for audits or regulatory reviews, these records offer concrete evidence of compliance efforts. While rule-based systems excel in providing clear audit trails and compliance support, their lack of flexibility highlights the need for more adaptive methods to address evolving threats effectively.
3. Machine Learning-Based Detection Systems
Machine learning (ML) systems bring a fresh approach to detecting stablecoin anomalies by examining patterns in transaction histories, network activities, and timing. Unlike rule-based systems that rely on fixed parameters, ML systems adapt as patterns evolve. This dynamic capability enables them to identify laundering tactics like chain hopping, multi-hop transfers, and the use of mixers - methods designed to evade static rules. By layering real-time behavioral insights on existing frameworks, ML systems enhance anomaly detection.
Anomaly Detection Accuracy
Switching from static rules to adaptive learning has led to better results. For example, the HyPV-LEAD framework, designed for detecting cryptocurrency anomalies, achieved a Precision-Recall Area Under Curve (PR-AUC) score of 0.9624 during testing. This is a stark contrast to traditional systems, which intercept only 0.1% of global criminal funds.
The strength of ML in stablecoin environments lies in its focus on behavioral features rather than network structures. Tree ensemble models like XGBoost and Random Forest perform better than Graph Neural Networks (GNNs) because they don’t depend on uninterrupted transaction graphs. When privacy tools like mixers or zero-knowledge proofs fragment the network, GNNs falter, but tree ensembles continue to detect anomalies by analyzing factors like transaction frequency, speed, and timing.
"By shifting anomaly detection from reactive classification to proactive early-warning, HyPV-LEAD establishes a robust foundation for real-time risk management, anti-money laundering (AML) compliance, and financial security." - Minjung Park, Lead Author
Platforms such as Stablerail incorporate ML-based anomaly detection into their pre-signature verification process. Before a payment is signed, the system evaluates factors like time-of-day activity, transaction amounts compared to historical trends, and payout patterns. This proactive approach - described as "copilot, not autopilot" - flags suspicious transactions before they are executed, giving teams the opportunity to review flagged payments with clear, evidence-based explanations.
False Positive Rates
A major benefit of ML systems is their ability to reduce false positives. Traditional rule-based systems often generate false positive rates above 95%, overwhelming compliance teams with unnecessary alerts. In contrast, ML models use domain-specific feature engineering to differentiate legitimate unusual activities from actual threats. For instance, a layered ML framework used in Canadian high-value payment systems achieved a 93% detection rate for unusual payments while significantly lowering false alerts.
What makes this possible is customized modeling. Instead of applying one-size-fits-all rules, ML systems adapt to the behavior of individual wallets. For example, a $50,000 transfer might be routine for a corporate account but highly unusual for a personal wallet. By learning these nuances, ML systems reduce the compliance burden on teams, allowing them to focus on genuine risks rather than investigating routine transactions. This not only streamlines operations but also ensures smoother policy enforcement.
Governance and Policy Integration
ML systems are most effective when aligned with governance frameworks. By extracting risk signals directly from stablecoin smart contract Transfer events - rather than raw blockchain data - ML systems operate within "deterministic compliance tunnels". This ensures that even when privacy layers obscure blockchain visibility, the audit trail remains intact and adheres to regulations like the EU’s MiCA and the U.S. GENIUS Act.
"ML frameworks must evolve to operate within deterministic compliance tunnels, where decision-making is restricted to exclusive, permissioned transfer logs." - StableAML Research Team
This integration empowers finance teams to encode policies as rules - such as "new address payments over $5,000 require CFO approval" or "weekend transfers over $10,000 need additional verification." Meanwhile, ML agents continuously evaluate whether transactions align with expected patterns. If an anomaly is detected, the system halts automated signing and triggers a manual review, ensuring human oversight.
Audit Trail Robustness
ML systems enhance audit trail reliability by focusing on smart contract event logs. Transfer events capture the true sender and recipient, creating an immutable record. Researchers call these "ML-enhanced transparent choke points" - auditable records that remain accessible even when privacy tools obscure blockchain data.
For organizations under regulatory scrutiny, this approach provides tangible evidence of due diligence. Each flagged transaction includes detailed information about the behavioral indicators that triggered the alert, the policy rules applied, and the decision process - complete with timestamps. Stablecoin issuers like Tether and Circle, which have frozen over $5 billion in illicit funds using smart-contract blacklist functions, rely on these ML-generated audit trails to justify enforcement actions to regulators.
Strengths and Weaknesses
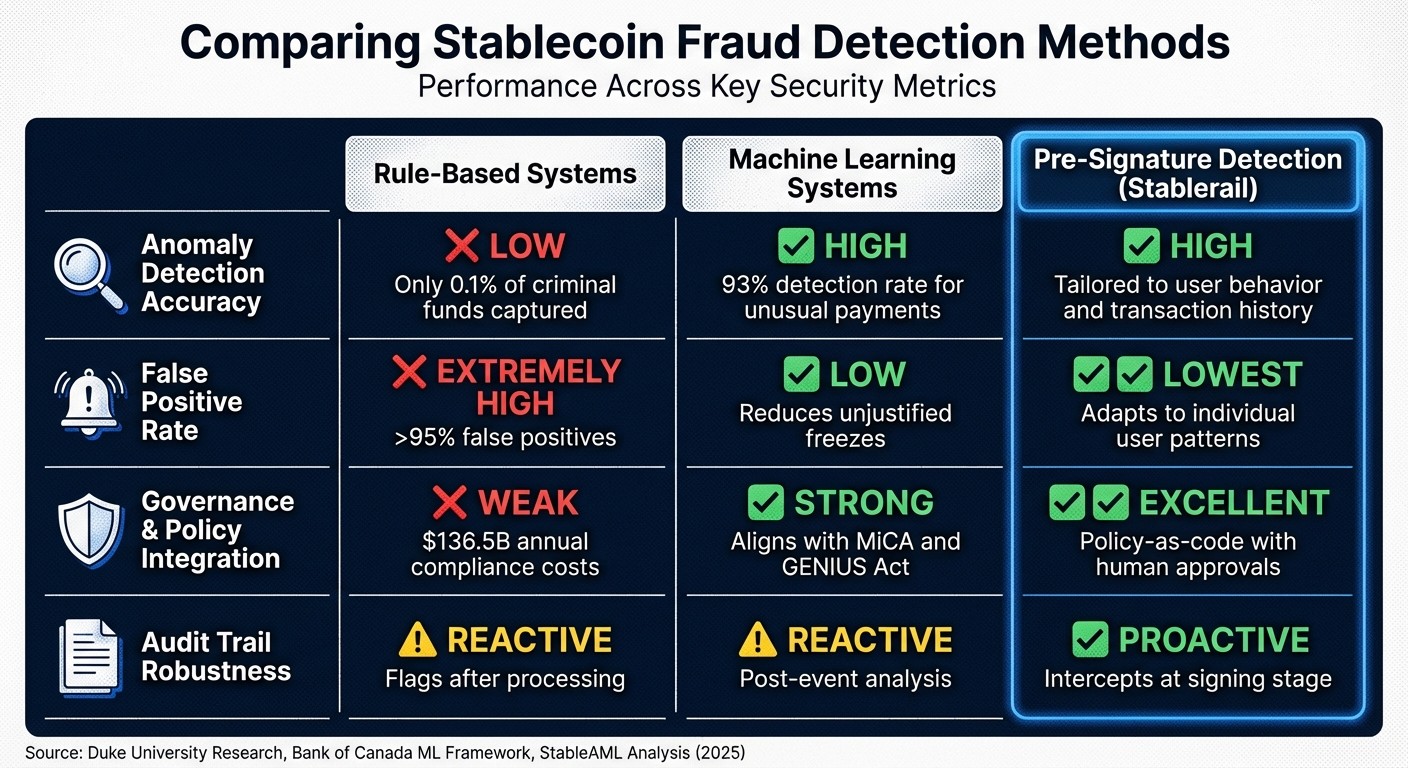
Stablecoin Fraud Detection Methods Comparison: Rule-Based vs Machine Learning vs Pre-Signature
When it comes to protecting stablecoin transactions, different detection methods bring their own pros and cons. Rule-based systems are straightforward but tend to overwhelm teams with excessive false alerts. Machine learning models offer greater precision but require ongoing updates to stay effective. Pre-signature systems, on the other hand, take a proactive approach by intercepting risks before transactions are finalized.
Here's a comparison of these methods across four key areas:
These differences show how each system's design impacts operational efficiency and accuracy.
Rule-based systems, while easy to implement, often come with a major drawback: an overwhelming number of false positives. This inefficiency is costly for compliance teams.
"Conventional rule-based systems... represent a staggering inefficiency, producing false positive rates that exceed 95%." - Luciano Juvinski, Researcher, Duke University
Machine learning systems step up the game by analyzing behavioral patterns. For instance, the Bank of Canada’s layered ML framework achieved an impressive 93% detection rate for unusual payments. Tree ensemble models, such as StableAML, also outperform Graph Neural Networks because they don’t rely on complete transaction graphs. However, like rule-based systems, machine learning models are reactive, meaning they analyze transactions after they've been broadcast.
Pre-signature detection takes a more proactive approach. It excels in anomaly detection accuracy, minimizes false positives, and strengthens audit trails by evaluating transactions before they’re signed and executed. Platforms like Stablerail give finance teams a final checkpoint to review flagged payments with detailed, evidence-based explanations. By learning what’s normal for each wallet, these systems reduce false positives and create an immutable audit trail that includes decision rationale, policy rules, and timestamps. For organizations navigating regulatory frameworks like MiCA and the GENIUS Act, this approach turns compliance challenges into a strategic advantage.
Conclusion
Selecting the right anomaly detection method hinges on factors like transaction volume, risk tolerance, and operational complexity. Rule-based systems are suitable for basic compliance tasks, such as sanctions list screening. However, their high false positive rate - reaching 95% - makes them unsuitable for high-volume stablecoin operations. While these systems are quick and predictable, they lack the flexibility to handle emerging threats or sophisticated laundering tactics. This is where advanced techniques come into play.
Machine learning (ML) systems complement traditional checks by improving detection accuracy and adapting to evolving threat landscapes. For instance, the Bank of Canada's layered ML framework achieved an impressive 93% detection rate for unusual payments. Similarly, tree ensemble models perform effectively in fragmented stablecoin networks. Despite these strengths, ML systems are inherently reactive, as they analyze transactions only after they are broadcast. For organizations dealing with complex transfers, such as multi-hop or chain-hopping schemes, ML-based detection is crucial - but it leaves a critical gap before transactions are finalized.
This gap is addressed by pre-signature detection, which intercepts risks before transactions are signed. Solutions like Stablerail operate at this critical juncture, combining behavioral anomaly detection, policy-as-code governance, and human-in-the-loop approvals. By learning the normal behavior of each wallet, this approach reduces false positives while maintaining an immutable audit trail that records decision rationale, policy rules, and timestamps. For finance teams managing $1–50 million annually in stablecoins, this proactive layer transforms compliance into a strategic advantage.
The most effective strategy combines all three approaches into a layered framework: rule-based systems for immediate sanctions checks, machine learning for analyzing behavioral patterns, and pre-signature verification for operational safeguards. As Minjung Park puts it:
"By shifting anomaly detection from reactive classification to proactive early-warning, HyPV-LEAD establishes a robust foundation for real-time risk management".
This layered approach is crucial for mitigating risks before irreversible losses occur, especially in a landscape where stablecoins accounted for 84% of verified crypto fraud volumes in 2025.
FAQs
What is pre-signature detection in stablecoin payments?
Pre-signature detection in stablecoin payments focuses on examining and confirming the intent behind a transaction before it’s signed and executed. This step is crucial for spotting potential risks such as policy violations, suspicious behavior, or issues with the counterparty, ensuring both compliance and security.
For instance, the process might involve sanctions screening, anomaly detection, and risk scoring. These checks result in a verdict - pass, flag, or block - that helps determine whether the transaction should proceed. By incorporating this layer of scrutiny, organizations can minimize fraud and policy violations without compromising the speed of on-chain settlements.
How does Stablerail decide to PASS, FLAG, or BLOCK a payment?
Stablerail evaluates payments with a pre-signature verification process to decide whether to PASS, FLAG, or BLOCK them. This involves specialized checks, including sanctions screening, policy enforcement, anomaly detection, and counterparty risk scoring. Each transaction gets a verdict: PASS for compliance, FLAG for further review, or BLOCK if problems are identified. To support human approvers, the system provides clear explanations and audit trails, ensuring decisions meet governance standards and help mitigate risks before final approval.
What do I need to integrate Stablerail into our approval workflow?
To bring Stablerail into your approval workflow, here’s how you can get started:
Connect your systems: Link your treasury and payment platforms to Stablerail’s modules for centralized control and management.
Set governance rules: Define policy-as-code rules to automatically enforce approval requirements.
Enable pre-signature checks: Add risk and compliance verification steps before signatures are completed.
Incorporate human oversight: Set up human-in-the-loop approvals to review and, if necessary, override automated decisions.
Streamline intent and signing: Integrate intent creation and signing directly into your existing systems to ensure smooth workflows.
These steps help you create a more efficient and secure approval process.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


