
False positives waste time. Missed threats cause damage. This is the reality for stablecoin treasury teams struggling with outdated anomaly detection systems. The solution? Policy-as-code governance. By embedding clear, rule-based policies directly into transaction logic, you can reduce false alarms, catch real risks, and streamline operations.
Here’s what you need to know:
The Problem: Statistical models often fail to understand transaction context, flagging legitimate payments or missing threats entirely.
Policy-as-Code: Integrates business rules directly into transactions, ensuring every action aligns with predefined criteria before execution.
Key Benefits:
Clear rules reduce false positives.
Automated enforcement ensures consistency.
Hybrid models (rules + AI) improve detection accuracy.
Real-World Results: Teams using policy-driven systems report faster detection, fewer false positives, and better compliance.
Policy-driven detection transforms compliance from a reactive process to a proactive safeguard, saving time, reducing errors, and improving security.
3.2 AI for Fraud & Anomaly Detection
The Problem with Anomaly Detection in Stablecoin Transactions
Stablecoin payment teams often grapple with detection systems that flag legitimate transactions while failing to catch actual threats. The main issue stems from rigid statistical baselines built on historical averages. For low-volume treasury operations, this approach falls short, leading to frequent errors in detection. On top of that, these systems usually evaluate transactions within narrow timeframes, so legitimate spikes during busy periods are mistaken for suspicious activity. The result? Operational headaches and inefficiencies, as explained below.
How False Positives Disrupt Treasury Operations
False positives create a frustrating cycle of manual intervention for finance teams. When detection systems operate in "reject mode", legitimate transactions get blocked, forcing staff to manually reprocess payments and adjust policies through support tickets. The scale of this issue is staggering: 56% of accounts payable teams spend over 10 hours a week on manual invoice and payment processing, and it takes an average of 14.6 days to complete manual payment tasks.
The financial toll adds up quickly. For example, 55% of firms lose between 4% and 5% of their monthly revenue due to inefficiencies in payment processes, while 23% lose between 6% and 10%. These delays are made worse by the fact that 39% of invoices contain errors requiring manual corrections. Frustrated by these inefficiencies, teams often disable automated enforcement altogether, running systems in "log only" mode until the detection engine becomes more reliable.
Why Behavioral Anomalies Are Hard to Detect
The challenge grows when detection systems fail to account for the context behind transactions. Most systems evaluate transaction values and speeds without understanding the "why" behind the activity. They lack critical business insights, such as user roles, asset details, or specific operational intents. For instance, a planned large-scale withdrawal might look no different from an unauthorized transaction to these systems.
The problem is further compounded by instant settlement, which leaves little time for reaction. Many systems only update their transaction history averages on a weekly basis, making it hard to detect nuanced behavioral changes or seasonal trends. Without this context, detection models become hypersensitive to normal variations yet fail to identify genuine risks. This forces finance teams to manually reconcile data from various APIs and settlement windows, creating a disjointed process that requires constant attention. To improve accuracy, precise and context-aware policy controls are essential.
How Policy-as-Code Rules Improve Detection Accuracy
Policy-as-code governance integrates business rules directly into transaction logic, setting clear definitions for what qualifies as "normal" operations. For example, it might evaluate a US$50,000 payment to a new vendor by checking if it’s made on a weekend, whether it has CFO approval, or if it passed sanctions screening - rather than relying on statistical patterns.
The main advantage here is clarity: policy-as-code explains the reasoning behind transactions that traditional behavioral systems might overlook. By establishing specific operational boundaries - like transaction limits, allowlisted addresses, or jurisdictional restrictions - you give the system the ability to differentiate between legitimate business activities and actual threats. This approach embeds risk management into the transaction process itself, creating a solid framework for accurate, risk-based policy enforcement.
Setting Up Risk-Based Policies
Risk-based policies create a clear baseline for acceptable transaction behavior. These policies typically focus on three key areas:
Transaction-level controls, such as spending limits or restrictions on specific asset types.
Velocity monitoring, which tracks transaction frequency and cumulative amounts over set timeframes (hourly, daily, or weekly).
Identity guardrails, which limit transactions based on factors like KYC status or geographic location.
For example, you could implement rules like: “Payments to new addresses over US$5,000 require CFO approval and verification” or “Weekend transfers exceeding US$10,000 need additional approval.” These policies are then enforced automatically, ensuring they’re applied consistently before any transaction is finalized. The benefits are tangible: businesses adopting adaptive rules that combine AI with issuer-specific policies reported a 1.3 percentage point increase in payment success rates. With these policies in place, automated enforcement simplifies and strengthens transaction screening.
Automated Policy Enforcement
Automated enforcement takes these predefined rules and applies them upfront, filtering transactions before they even reach more complex anomaly detection systems. This method uses a "DENY-overrides-ALLOW" model, meaning explicit deny rules (e.g., “Deny if amount > US$1,000”) always take precedence, ensuring security measures are never bypassed.
Low-risk, trusted transactions are approved automatically, while high-risk anomalies are flagged for further review. This reduces the need for manual intervention and ensures consistent enforcement. If a policy is triggered, the system can respond instantly - rejecting the transaction, freezing associated wallets, or requesting additional information - all without human involvement. This streamlined process not only improves efficiency but also strengthens overall security.
How Stablerail Uses Policy Rules for Better Detection
Stablerail takes a proactive approach to compliance by enforcing policy-as-code governance before payment signing. Instead of waiting to address problems after settlement, every transaction intent is evaluated upfront against a policy graph. This graph incorporates identity checks, transaction heuristics, and specific business rules. Acting as a "copilot, not autopilot", the system performs mandatory pre-sign checks, including sanctions screening, policy enforcement, behavioral anomaly detection, and counterparty risk scoring. Users can also evaluate stablecoin risks to further refine their security parameters. This setup combines automated checks with deeper behavioral analysis for a seamless and thorough detection process.
Behavioral Anomaly Detection with Business Context
Stablerail uses a mix of statistical analysis and business context to differentiate routine operational changes from potential threats. A forecasting engine analyzes historical transaction data to establish a behavioral baseline, which includes average transaction values. This baseline is updated weekly to reflect current trends. Transactions that deviate significantly - like unusually high amounts, transfers during off-hours, or payments to unfamiliar addresses - are flagged for review.
Velocity checks monitor transaction frequency over specific time periods. For instance, if a treasury department normally processes three payments a day but suddenly initiates fifteen within an hour, the system flags this unusual activity. To improve accuracy, Stablerail integrates external intelligence, such as real-time sanctions lists and counterparty risk scores, through policy oracles. By grounding anomaly detection in both internal patterns and external threat intelligence, the platform minimizes false positives and enhances detection reliability.
"On-chain policy enforcement turns that sequence on its head. Instead of catching non-compliant activity once it's visible, it embeds the rule where the risk originates: inside the transaction logic itself." - Natalia Latka, Head of Regulatory Affairs, ComPilot
Human Approvals and Audit Trails
While automated checks are effective at identifying anomalies, Stablerail ensures that critical transactions are reviewed by humans for added context before final approval. When an anomaly is detected, the system doesn't immediately block the transaction. Instead, high-risk intents are escalated to a Review state, where human approvers evaluate the flagged payment and its context. This process helps prevent legitimate but unusual transactions - like first-time vendor payments or emergency weekend transfers - from being wrongly rejected. For particularly sensitive or high-value transactions, quorum-based approvals may be required, ensuring multiple stakeholders review the payment before it proceeds.
Every step of the process - intent, checks, flags, approvals, overrides, and signatures - is recorded in a tamper-evident audit trail. These cryptographic records link fund movements to the authorizing policy rules. They provide CFO-grade evidence for auditors, boards, and regulators, clearly showing why a transaction was approved or rejected. Additionally, the system logs detailed policy evaluation outcomes (e.g., POLICY_THRESHOLD_EXCEEDED), which can be integrated into SIEM systems or risk dashboards for real-time monitoring. This comprehensive documentation not only enhances detection accuracy by enabling post-mortem rule analysis but also ensures compliance with AML and Travel Rule standards.
Measured Results from Policy-Driven Detection
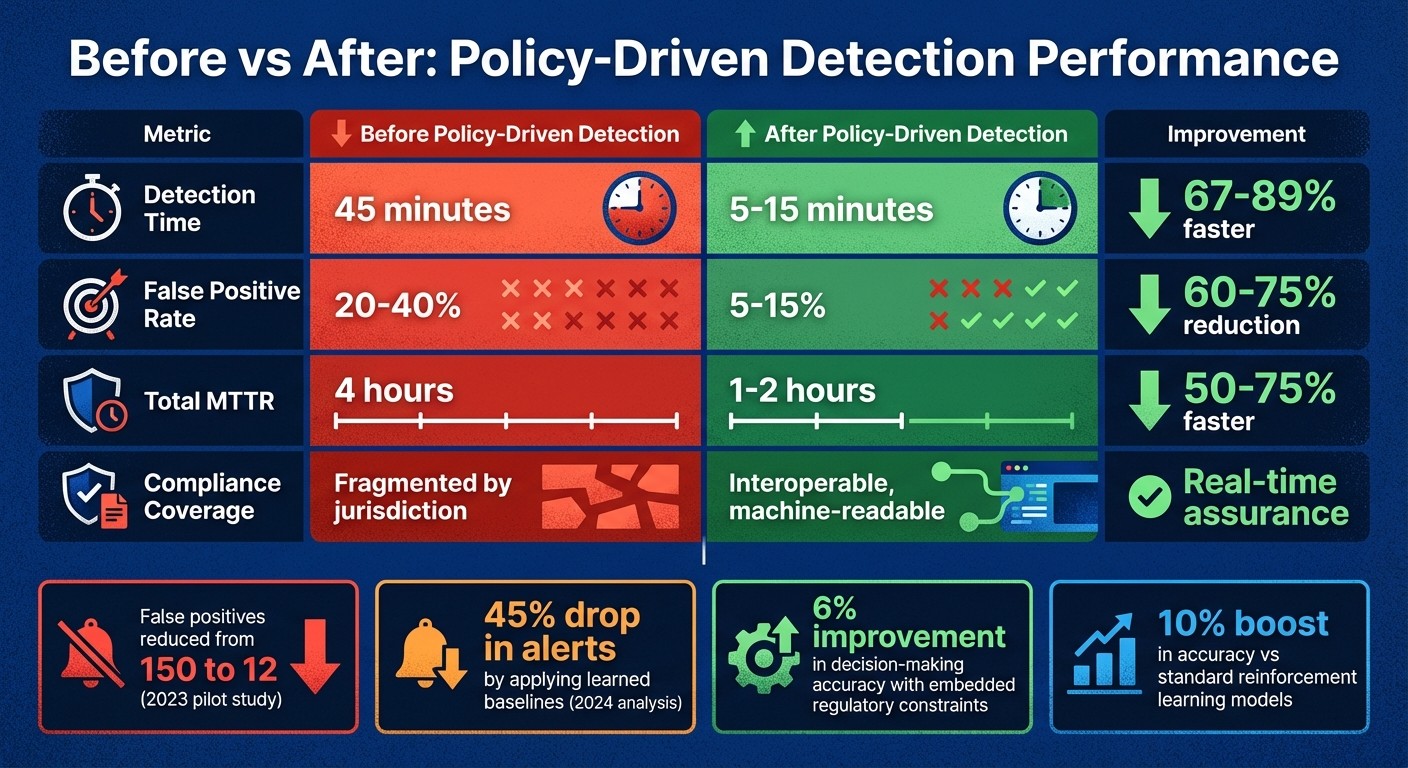
Before vs After Policy-Driven Anomaly Detection Performance Metrics
Policy-driven detection systems bring tangible benefits: fewer false alarms, quicker threat identification, and improved compliance. Organizations using this approach report noticeable improvements in daily operations and risk management. These results highlight the evolution from outdated, reactive methods to more efficient, rule-based control.
Before and After: Detection Performance Metrics
The contrast between traditional threshold-based systems and policy-driven detection is striking when you compare performance metrics. For example, a 2023 pilot study found that refining service-level context and adjusting thresholds reduced false positives from 150 to just 12, while still identifying 70% of major incidents.
In another case, a 2024 analysis showed a 45% drop in alerts by applying learned baselines to most metrics, while critical latency metrics retained static thresholds.
The table below outlines these performance improvements:
In addition to speed and accuracy, policy-driven systems offer enhanced compliance capabilities. For instance, research on ethical reinforcement learning models (ER-DM) demonstrated at least a 6% improvement in decision-making accuracy when regulatory constraints were embedded within the system. When compared to standard reinforcement learning models, these policy-integrated systems delivered a 10% boost in decision-making accuracy.
For finance teams handling stablecoin payments, this means fewer legitimate transactions are wrongly flagged while more genuine threats are accurately intercepted. These advancements underscore the effectiveness of policy-driven detection in implementing rules, integrating behavioral agents, and ensuring oversight.
How to Implement Policy-Driven Anomaly Detection
Implementing policy-driven anomaly detection involves three key steps: defining your rules, integrating behavioral agents, and setting up human oversight. Together, these steps create a robust system that identifies potential threats without hindering legitimate transactions.
Creating Your Policy Rules
Start by defining rules in your Policy Console using logical expressions that combine factors like transaction amount, destination address, asset type (e.g., USDC or USDT), and velocity limits.
For instance, you might set a rule such as: "Payments to new addresses exceeding $5,000 require CFO approval and verification." These rules are then converted into machine-enforceable policies that are automatically applied to every transaction intent before it’s signed.
Follow a "DENY-overrides-ALLOW" strategy, where transactions are denied by default unless they meet specific trusted criteria. This ensures that high-risk flags - like a suspicious counterparty score - take precedence over other approval conditions. Adding custom attributes, such as Customer ID or Risk Tier, can further refine the granularity of these rules.
In tools like Stablerail's Policy Console, finance teams can write these rules in plain English, which are then translated into enforceable code. This process establishes clear guardrails that prevent risky transactions before they’re even initiated.
Once your rules are in place, the next step is integrating behavioral agents to monitor compliance and detect anomalies.
Connecting Behavioral Agents
With your rules defined, behavioral agents come into play to ensure continuous monitoring and baseline updates. Start by deploying these agents in "Log only" mode, allowing them to learn transaction patterns and update baselines weekly without interrupting operations.
To enhance risk assessment, integrate blockchain intelligence tools like Chainalysis or TRM Labs, which generate real-time risk scores for each transaction. Connect these agents to your internal systems using webhooks. This setup enables the system to automatically pause transactions or send alerts via platforms like Slack, Opsgenie, or SMS when anomalies are detected.
Signature gating is another critical feature. It ensures that compliance and anomaly checks occur after a transaction is proposed but before it’s signed. Natalia Latka, Head of Regulatory Affairs at Evergon Labs, highlights the importance of this approach:
"On-chain policy enforcement turns that sequence on its head. Instead of catching non-compliant activity once it's visible, it embeds the rule where the risk originates: inside the transaction logic itself".
Stablerail’s behavioral agents also generate a Risk Dossier for each transaction intent. This dossier provides a verdict - PASS, FLAG, or BLOCK - along with plain-English explanations that reference specific policy clauses and timestamps, ensuring clarity before any signature request reaches your team.
Setting Up Human Oversight and Audit Logs
To add a layer of accountability, configure escalation thresholds that require human approval for high-value transactions (e.g., CFO sign-off for amounts exceeding $5,000). Use quorum-based workflows for flagged transactions, where multiple authorized personnel must review risk reports and approve or deny the transaction.
Every decision should be logged with detailed metadata, including the rule ID, match status, and any error messages (e.g., POLICY_THRESHOLD_EXCEEDED). Treat policy expressions as immutable, meaning that instead of altering existing rules, new versions are deployed to track changes in logic over time.
Cryptographic proofs can further strengthen your system by linking each transaction to its specific policy evaluation and signatures. This ensures that any flagged risk or exception is manually reviewed and fully documented. Stablerail’s platform maintains a complete audit trail for every action - intent creation, checks performed, flags raised, overrides applied, approvals granted, and signatures executed. This thorough record allows finance teams to justify their decisions to auditors, boards, and regulators, turning compliance into a proactive tool rather than a reactive burden.
Conclusion
Policy-driven anomaly detection weaves compliance directly into transaction processes, stopping non-compliant activities before they can be finalized. Organizations leveraging automated policy frameworks often experience a 40%–70% reduction in compliance costs, a 90% or greater decrease in compliance violations caused by human error, and up to 60% faster threat response times. For the 56% of accounts payable teams spending more than 10 hours each week on manual payment processing, automation not only eliminates bottlenecks but also ensures strong security measures.
Stablerail takes these principles a step further with its agentic control plane, which operates above custody and prior to transaction signing. Each transaction intent undergoes behavioral anomaly detection, sanctions screening, and policy enforcement. The system generates a detailed Risk Dossier, offering clear verdicts such as PASS, FLAG, or BLOCK, complete with plain-English explanations linked to specific policy rules and timestamps. This equips approvers with the evidence they need to make confident, well-informed decisions.
By minimizing false positives, accelerating legitimate payments, and maintaining comprehensive logs of every decision, this approach transforms risk management into a seamless process.
For finance teams handling stablecoin payments, policy-driven anomaly detection delivers scalable governance while preserving the speed and efficiency of on-chain operations.
FAQs
How does policy-as-code enhance anomaly detection in stablecoin payments?
Policy-as-code enhances the ability to detect anomalies by allowing finance teams to establish precise, machine-readable rules for transactions. These rules can include specifics like payment thresholds, approval protocols, and conditions based on context, all of which are automatically applied to every payment attempt.
With these policies in place, each transaction is evaluated against both the predefined rules and historical transaction patterns. This enables the system to quickly identify unusual activities - like payments that exceed typical amounts or occur at odd hours - while minimizing false alarms. The result? A more reliable detection process that upholds compliance without interrupting daily operations.
How does automated policy enforcement enhance anomaly detection and reduce risks?
Automated policy enforcement evaluates every transaction based on predefined, machine-readable rules before it’s finalized. This eliminates the need for extensive manual reviews, reduces the chance of human error, and automatically screens out potentially risky activities. For instance, policies such as “block transfers to flagged addresses” or “require approval for transactions exceeding $10,000” help maintain compliance and minimize risk without causing delays.
By continuously comparing transactions to established baselines, these automated systems can identify or block unusual activities in real time. This approach not only reduces false positives but also ensures that anomaly detection systems concentrate on genuine irregularities. Furthermore, every decision is meticulously logged with a verifiable audit trail. This simplifies compliance efforts, speeds up audits, and provides clear documentation for approvals or overrides. The result? Streamlined workflows that support faster, safer decision-making on a large scale.
How does Stablerail enhance anomaly detection compared to traditional methods?
Stablerail stands out in anomaly detection by blending policy-as-code governance with cutting-edge verification tools. This approach ensures every transaction is assessed against clearly defined rules, such as payment thresholds, approval processes, and behavioral trends. On top of that, it incorporates real-time checks like sanctions screening, counterparty risk assessments, and behavioral anomaly detection. Together, these layers reduce false positives and enhance decision-making accuracy.
What really sets Stablerail apart is its ability to go beyond static algorithms. The system offers plain-English explanations for flagged transactions, clearly linking them to specific policies and supporting evidence. This level of transparency not only helps finance teams make smarter decisions but also ensures a solid audit trail, reinforcing compliance and accountability.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


