
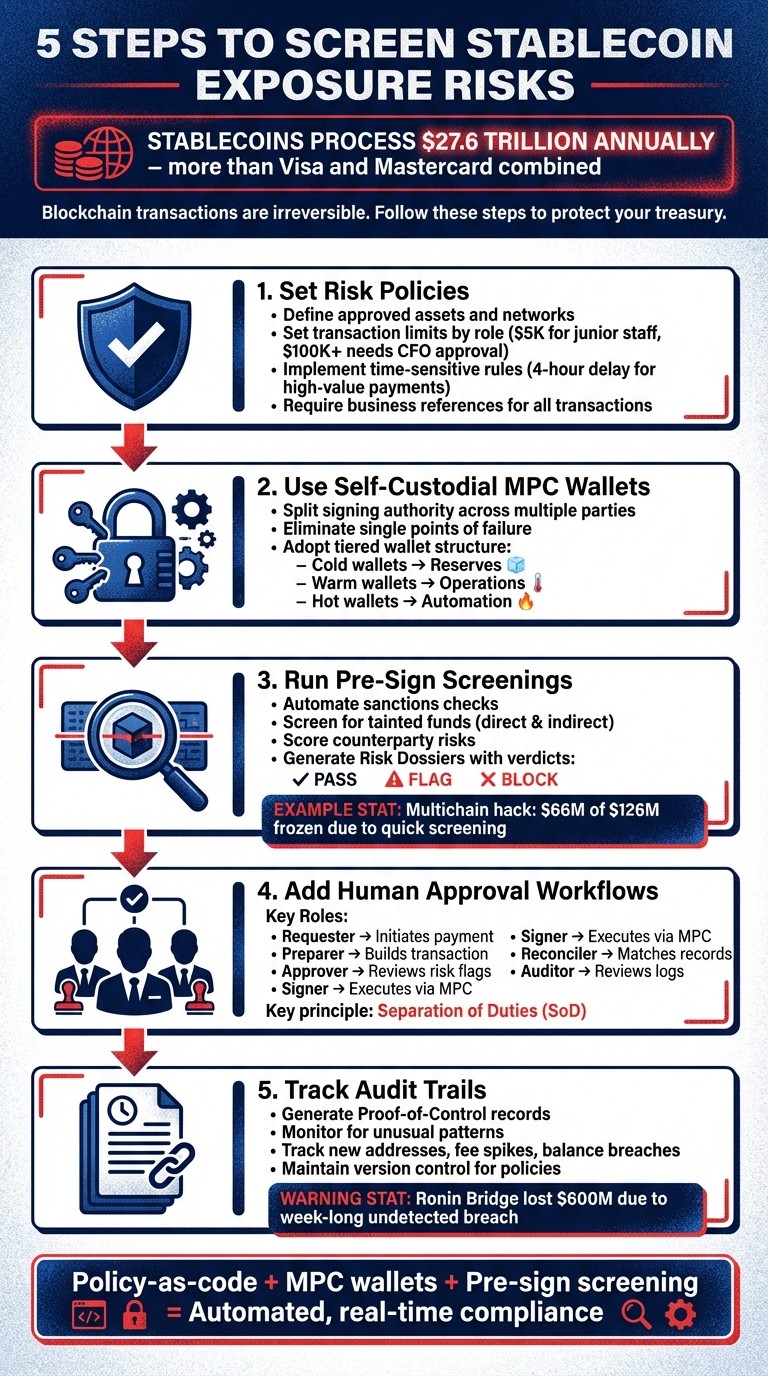
Stablecoins process over $27.6 trillion annually, more than Visa and Mastercard combined. But unlike traditional bank transfers, blockchain transactions are irreversible. Sending funds to risky wallets - like those tied to hacks or sanctions - can freeze your treasury and disrupt operations. To avoid these pitfalls, follow these five steps to manage stablecoin risks effectively:
Set Risk Policies: Define rules like approved networks, transaction limits, and mandatory delays for high-value payments.
Use Self-Custodial MPC Wallets: Secure your funds by splitting signing authority across multiple parties, reducing single points of failure.
Run Pre-Sign Screenings: Automate checks for sanctions, tainted funds, and counterparty risks before signing transactions.
Add Human Approval Workflows: Implement role-based reviews to ensure flagged transactions are properly evaluated.
Track Audit Trails: Maintain detailed records of every transaction for compliance and monitoring.
5 Steps to Screen Stablecoin Exposure Risks
ACCESS 2026 | Session 3: A Framework for Analyzing & Rating Stablecoin Risk
Step 1: Set Your Exposure Risk Policies
Start by establishing clear risk policies to avoid costly on-chain errors. In traditional finance, processes like approval matrices, vendor lists, and spending limits are standard. On-chain payments require a similar approach but with policy-as-code - automated rules that execute before any transaction is signed.
Define Your Policy Parameters
Lay out the specifics of your policies:
Approved assets and networks: For instance, allow USDC on Ethereum and Base, but restrict USDT on Tron if compliance issues arise.
Transaction limits by role: Junior accountants might handle payments up to $5,000, while transfers exceeding $100,000 require CFO approval.
Time-sensitive rules: To combat social engineering, implement safeguards like additional verification for weekend transfers over $10,000 or a mandatory 4-hour waiting period for high-value payments to new beneficiaries.
Additionally, every transaction should be tied to a business reference - such as an invoice ID, payroll batch, or vendor contract. This ensures traceability and prevents "blind signing." To further safeguard your treasury, adopt a tiered wallet system: cold wallets for reserves, warm wallets for operations, and hot wallets for automation. The most stringent approval rules should protect your largest balances.
Once these rules are in place, the next step is to ensure they are enforced without fail.
Turn on Automated Policy Enforcement
After defining your parameters, use tools like Stablerail's Policy Console to convert them into actionable code. This code runs before every transaction is signed. For example, if someone attempts to send $50,000 in USDC to an unverified address, the system will block the transaction and issue a Risk Dossier with a BLOCK verdict. Overrides are only possible with a recorded justification, which becomes part of the audit log.
This approach eliminates error-prone manual processes. Instead, you achieve deterministic enforcement - the same inputs always lead to the same outcomes, based on your policy. Auditors value this consistency because it demonstrates a reliable, repeatable governance process, independent of who is handling the payment request at any given time.
Step 2: Configure Self-Custodial MPC Wallets
After defining your policies and following a stablecoin compliance checklist, it’s time to secure your funds in wallets that you control - not a third party. Self-custodial MPC (Multi-Party Computation) wallets offer a high level of protection for your stablecoins. Even if a provider fails, your funds remain safe because you hold the keys.
Protect Your Funds with MPC Technology
MPC technology works by splitting signing authority across multiple parties, ensuring no single person or system can move funds alone. This setup eliminates the risks of blind signing - approving transactions without verifying the details. With MPC, every payment request is simulated and checked against your policies before the private key is used to sign.
To further enhance security, adopt a tiered wallet structure. This approach matches security controls to risk levels, minimizing damage if a hot wallet is breached. For example, even if an attacker compromises one wallet, they won’t have access to your entire treasury.
For seamless management, integrate your secure MPC wallets with governance tools that enforce your policies in real time.
Link Wallets to Governance Tools
The true power of MPC wallets comes to life when connected to a governance layer. This integration ensures your policies are enforced at the moment of signing. Tools like Stablerail's agentic control plane act as a safeguard between your wallet and the blockchain, performing mandatory pre-sign checks before any transaction is executed. When a payment request is made, specialized agents create a Risk Dossier with a verdict: PASS, FLAG, or BLOCK.
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money." - Stablerail
This system helps prevent costly mistakes. For instance, if a vendor’s wallet address unexpectedly changes, the payment is automatically flagged and locked for further review. This kind of runtime enforcement ensures policies aren’t just guidelines - they’re machine-enforced rules that stop non-compliant transactions before they happen.
Step 3: Run Sanctions and Taint Screening
Once you've established clear policies and secured your MPC wallets, the next step is to implement pre-sign screening for every transaction. Why is this so important? Because blockchain transfers are permanent - once the funds leave your wallet, there's no getting them back. That makes pre-sign checks for sanctions compliance, taint analysis, and counterparty risk scoring absolutely critical. These checks serve as your last safeguard, ensuring your funds don’t end up in the hands of bad actors or come from risky sources that could jeopardize your treasury. Essentially, this screening process connects your secured wallet setup with a real-time defense against illicit transactions.
Here's why this matters: In 2024, custodial stablecoins processed a staggering $27.6 trillion in transaction volume - more than Visa and Mastercard combined. With that level of activity comes increased scrutiny. Take the Multichain hack as an example - stablecoin issuers froze $66 million of the $126 million stolen because they acted quickly. If your treasury unknowingly interacts with tainted funds, you could face similar risks, like having your operational funds frozen without notice.
Turn on Pre-Sign Screening Agents
Pre-sign screening agents automate what used to be a manual, spreadsheet-heavy process for finance teams. These specialized tools check every transaction against a list of prohibited addresses, flagged jurisdictions, and suspicious blockchain activity. Stablerail's agentic control plane takes this a step further, running mandatory checks for sanctions violations, taint exposure, counterparty risk scoring, and unusual behaviors - all before your MPC keys even come into play.
Taint analysis is a key part of this process. It identifies "digital stains" by tracing how funds are connected to illicit activities, such as ransomware wallets, hacks, or sanctioned mixers. There are two types of taint to watch for:
Direct taint: Funds come straight from a known bad actor.
Indirect taint: Funds pass through several intermediaries (or "hops") before reaching your counterparty.
Both types can lead to serious consequences. For example, stablecoin issuers like Circle or Tether might blacklist your entire wallet if it interacts with tainted funds. By catching both direct and indirect taint, your system ensures compliance with the governance standards you set up earlier.
Review Risk Dossiers
After the pre-sign screening agents complete their checks, they generate a detailed Risk Dossier. This document breaks down sanctions compliance, taint exposure, and counterparty risks specific to the transaction being reviewed. The dossier provides a clear verdict - PASS, FLAG, or BLOCK - along with evidence-backed explanations tied to your policies and timestamps. Instead of vague error codes, you get actionable insights based on specific on-chain data.
Here’s how the system handles each verdict:
Verdict | System Action | Team Action |
|---|---|---|
PASS | Transaction unlocked for signing | Routine review of simulation and intent |
FLAG | Transaction locked | Evidence review required; override reason must be recorded |
BLOCK | Transaction prohibited | Counterparty investigation or policy review; typically rejected |
For instance, if a vendor suddenly changes their wallet address, the system might flag the payment and lock it for review. If the counterparty has indirect taint from a sanctioned mixer, the dossier will outline the exact on-chain steps that led to the exposure. This level of transparency ensures you never approve a transaction blindly - you’ll always know why it was flagged and can make an informed decision. Plus, the detailed evidence ties back to your governance framework and policy-as-code principles, creating a solid audit trail for every decision.
Step 4: Add Human Approval Workflows
Automated screening is great for spotting potential risks, but human review is essential for making final decisions. This step ensures that no single person can request, approve, and execute a payment on their own - a principle known as Separation of Duties (SoD). When a flagged transaction arises during pre-sign screening, it stays on hold until an assigned approver steps in to confirm or override the Risk Dossier. If the approver decides the payment is valid despite the flag, they must clearly document their reasoning. This creates a solid audit trail, which is crucial for regulatory compliance. This layered approach naturally leads to role-based workflows.
Set Up Role-Based Approvals
A well-structured approval process divides responsibilities among different roles, reducing the risk of errors or fraud. Stablerail's Policy Console allows you to define these roles and assign specific permissions:
Role | Primary Responsibility |
|---|---|
Requester | Initiates payment requests with supporting business evidence. |
Preparer | Builds the transaction or batch and ensures compliance with policies. |
Approver | Reviews the payment's purpose, checks limits, and evaluates risk flags. |
Signer | Finalizes and executes the transaction using MPC. |
Reconciler | Matches blockchain activity with ledger records. |
Auditor | Has read-only access to review logs and supporting evidence. |
Flagged transactions rely on the pre-sign Risk Dossier for informed decision-making. To strengthen this process, you can implement tiered approval thresholds based on the risk level of the transaction. For instance, payments over $5,000 to new addresses might need CFO approval, while weekend transfers exceeding $10,000 could require additional sign-offs. Adding smart cool-off periods for high-value transactions - like delaying payments over $100,000 or transfers to new beneficiaries for four hours - provides extra protection against social engineering attacks.
When reviewing a flagged transaction, the approver examines the Risk Dossier to understand why it was flagged. For example, if a vendor updates their wallet address and provides proper verification, the approver can clear the flag. Stablerail requires the approver to log a clear reason for any override. This explanation becomes part of an unchangeable audit trail, offering strong evidence in case regulators or auditors later question the decision.
Sign Transactions with MPC
Once a transaction passes the approval stage, it moves to execution. This is done securely through Multi-Party Computation (MPC) signing, which splits private keys across multiple individuals. This setup ensures that no single person can move funds independently. During this "Approve & Sign" step, the approver reviews the transaction details one last time, confirms everything is in order, and completes the signing process using MPC.
MPC signing boosts security and accountability by requiring multiple parties to act together. Every signing action is logged, including timestamps, the approver's identity, and the reason for any override. Stablerail also generates a Proof-of-Control Receipt for every payment, detailing the transaction's purpose, who approved it, and the automated risk assessment. This receipt is your best defense when auditors, regulators, or boards ask for an explanation of high-risk payment decisions.
Step 5: Track Audit Trails and Monitor Activity
Once your policies are in place and transactions are approved, the next priority is ensuring complete transparency. This step wraps up the governance framework by documenting every decision. Without thorough records, you'll find it challenging to justify decisions when auditors, regulators, or board members demand explanations for a specific payment.
Build Complete Audit Trails
Every transaction should generate a Proof-of-Control record that captures the entire authorization process. These records, built on the pre-sign Risk Dossier, ensure that decisions are not only traceable but also reproducible. Key details to include are the policy version, the Risk Dossier's decision, any overrides, and timestamps.
This level of detail is critical for auditors to verify decision determinism - essentially, proving that identical inputs under the same policy produce consistent outcomes. For instance, if your payment policy requires CFO approval for transactions exceeding $5,000, auditors should be able to review this decision months later and clearly see why the system allowed or denied the payment. Tools like Stablerail's Treasury Hub simplify this process by linking every on-chain transaction ID to its business purpose, eliminating the need for manual reconciliation.
Treating treasury policies like software, complete with version control, lets you demonstrate why a particular transaction was approved at a specific time. For tax compliance, remember that the IRS treats stablecoins as property. This means your audit trail must record the fair market value in USD at the time of receipt (income) or spending (disposal) to account for any potential gains or losses.
A robust audit trail not only satisfies compliance requirements but also sets the stage for real-time monitoring, which we'll cover next.
Watch for Unusual Patterns
Continuous monitoring is your safety net, catching potential issues before they spiral out of control. Stablerail's Treasury Hub keeps an eye on red flags like new recipient addresses, unexpected fee spikes, balance breaches, rapid address changes, and unusually large transfers. When anomalies are detected, the system raises alerts.
This proactive approach has proven its worth in the past. For example, during the Multichain hack, issuers managed to freeze $66 million of the $126 million stolen by acting within hours of spotting the breach. On the other hand, the Ronin Bridge hack resulted in a staggering $600 million loss, largely because the attack went unnoticed for an entire week due to insufficient monitoring. The key difference? Real-time visibility and automated alerts.
Ongoing monitoring ensures that transactions adhere to your governance rules even after execution. For instance, Stablerail enforces "Verified Vendor Whitelists" to block address-switching attacks. If a vendor's address changes, the system automatically locks the payment for further review. High-value transfers - such as those exceeding $100,000 - or payments to new recipients trigger "Smart Cool-Off Periods", introducing a four-hour delay. This gives your team time to verify the request and detect any social engineering attempts before funds are released.
Conclusion
Managing stablecoin exposure risks requires a careful balance between speed and control. By following five essential steps - establishing exposure policies, setting up self-custodial MPC wallets, conducting sanctions and taint screenings, implementing human approval workflows, and maintaining audit trails - organizations can create a framework that turns compliance into an automated, real-time process.
This approach ensures every transaction aligns with corporate governance standards. Automated systems evaluate payment intent and context, producing risk dossiers with clear outcomes: PASS, FLAG, or BLOCK. While automation handles much of the heavy lifting, human oversight remains crucial, giving the final approval to prevent violations of sanctions, velocity limits, or interactions with flagged addresses. This eliminates the risks of "blind signing" and embeds compliance directly into the transaction process.
The move toward agent-driven treasury systems mirrors broader changes in corporate finance. In 2024, custodial stablecoins facilitated $27.6 trillion in transaction volume, surpassing Visa and Mastercard combined. Additionally, nearly 25% of businesses still using checks plan to adopt digital payment solutions by late 2026. These shifts highlight the growing demand for governance frameworks that operate in real-time and are policy-enforced.
Stablerail simplifies this transition by acting as an intelligence layer between your treasury and the blockchain. It automates policy enforcement, screens counterparties for compliance risks, and provides audit-ready Proof-of-Control receipts. Your funds remain secure in self-custodial MPC vaults, ensuring that the platform itself has no unilateral signing authority. By adopting these measures, finance teams can safeguard their stablecoin treasuries while meeting the highest compliance standards.
FAQs
What stablecoin risks can freeze our funds?
Stablecoin funds can sometimes be frozen due to compliance or security concerns. For instance, issuers might flag coins as compromised or tainted, leading to restrictions. Additionally, custodial stablecoins carry risks tied to the issuer's operations. Failures or breaches on their end could result in your funds being frozen or inaccessible. This underscores why robust security and compliance measures are essential to protect your assets.
How do MPC wallets reduce treasury risk?
MPC wallets offer a safer way to manage treasury funds by enabling self-custody with improved security measures. Instead of storing private keys in a single location, multi-party computation (MPC) technology splits them across multiple parties. This approach significantly reduces the risk of unauthorized access.
In this setup, no single party has the power to sign transactions alone, as unilateral signing authority is eliminated. Every transfer must adhere to pre-established policies, adding another layer of protection. By combining robust key management with automated, policy-based controls, MPC wallets help safeguard against unauthorized transactions, ensuring a more secure treasury management process.
How should we handle flagged transactions?
Flagged transactions must undergo review and proper documentation before any further action is taken. Stablerail ensures that flagged payments are evaluated by authorized personnel, such as CFOs, who can decide to approve, block, or override them based on established policies and the available evidence. Every decision, along with the reasoning and supporting evidence, is meticulously recorded in a detailed audit trail. This process promotes transparency, ensures accountability, and helps reduce risks while meeting the expectations of auditors and regulators.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


