
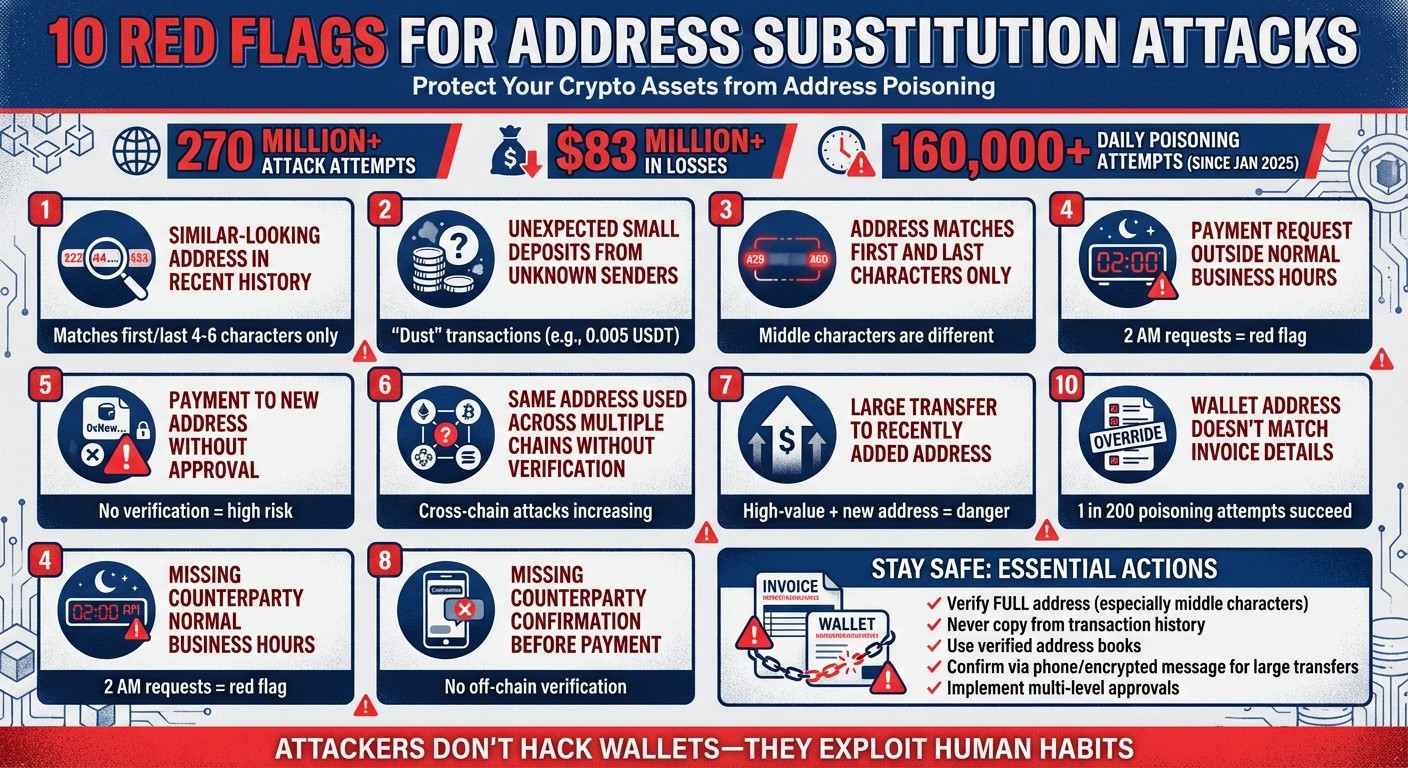
Address substitution attacks, also known as "address poisoning", are a growing threat in cryptocurrency transactions. These scams manipulate transaction histories by inserting fake wallet addresses that mimic legitimate ones, exploiting users' tendency to copy familiar-looking addresses. With over 270 million attack attempts and losses exceeding $83 million, these attacks are becoming increasingly sophisticated.
Here’s what you need to know to protect yourself:
Fake addresses in transaction history: Scammers use vanity address generators to create lookalike addresses that match the first and last characters of trusted ones.
Small or zero-value deposits: Attackers send "dust" transactions to poison your wallet's transaction history.
Timing manipulation: Bots monitor small test payments and insert fake addresses into your history within minutes.
Skipping verification steps: Relying on transaction history instead of verified sources increases the risk of errors.
Off-hours payment requests: Scammers exploit reduced scrutiny during non-business hours.
Cross-chain attacks: Fake addresses may appear across multiple blockchains, increasing the likelihood of confusion.
Key prevention tips:
Always verify the full recipient address, focusing on the middle characters.
Avoid copying addresses directly from transaction history.
Use verified address books or trusted sources for new payments.
Implement strict pre-transaction policies, such as multi-level approvals for large transfers.
Confirm payment details through secure, independent channels, like phone calls or encrypted messages.
Attackers are not hacking wallets - they’re exploiting human habits. By staying vigilant and enforcing strong verification processes, you can reduce the risk of falling victim to these scams.
10 Red Flags for Address Substitution Attacks in Cryptocurrency
How Address Poisoning Scams Steal Millions (And How to Avoid Them)
1. Similar-Looking Address in Recent Transaction History
Even slight similarities in wallet addresses can be a warning sign of a substitution attack. One of the most common red flags is spotting an address in your recent transaction history that looks almost identical to a trusted one, except for a few characters in the middle. Scammers use tools like vanity address generators to create fake addresses that mimic the first and last 4–6 characters of legitimate ones. This is particularly dangerous because these are the portions most wallet interfaces display when abbreviating long hexadecimal strings.
Address History Anomalies
Unusual activity in your transaction history can be a major clue. Look out for zero-value transfers or small "dust" amounts (e.g., 0.005 USDT) from unknown addresses. Scammers often use the transferFrom function in ERC-20 tokens to carry out zero-value transactions, specifically to manipulate your recent activity list. Research has shown a significant number of these attacks. For example, one campaign generated 82,031 fake addresses, making up nearly 1% of all new Ethereum addresses during that time.
Transaction Timing and Behavior Patterns
Timing is another critical factor. Advanced attackers use bots to monitor the mempool for test transactions. As soon as a small test payment is detected, they quickly create a lookalike address and send a dust transaction. This ensures their fraudulent address appears at the top of your "Recent" list, often within 1–2 minutes of the legitimate transfer.
A striking example occurred in December 2025, when an investor lost $50,000,000 USDT. After sending a 50 USDT test transaction to a secondary wallet, an automated bot detected the payment, generated a fake address, and sent a dust transaction. The victim, assuming the top entry in their recent history was correct, transferred the remaining 49,999,950 USDT to the scammer just 26 minutes later. This case highlights the need for thorough verification of recipient addresses.
Recipient Verification and Validation
Avoid copying a recipient's address directly from your transaction history, even if it seems familiar. Scammers rely on users focusing only on the first and last few characters of an address. To stay safe, always cross-check at least 4–6 random characters from the middle of the address using a trusted, independent source before making high-value transfers.
2. Unexpected Small Deposits from Unknown Senders
Those tiny, unsolicited deposits in your wallet? They're not a gift - they're a trap. Scammers use these "dust" transactions, often worth mere pennies, to clutter your transaction history with addresses that mimic legitimate ones. The idea is to trick you into accidentally copying their fake address for a future transfer, setting the stage for potential theft. This sneaky tactic not only messes up your transaction records but also opens the door to more elaborate scams.
Address History Anomalies
Dust attacks take advantage of how wallets display transaction histories. Scammers use tools like vanity address generators to create fake addresses that look almost identical to those of your trusted contacts. This makes it extremely hard to spot the difference, especially when reviewing unexpected deposits. Some fraudsters even exploit ERC-20 transferFrom events to insert zero-value transactions into your history, further complicating things.
The numbers are shocking. Since January 2025, over 65.4 million address poisoning transactions have been identified - an average of more than 160,000 every single day. In one case, a single attacker managed to send around 3 million dust transactions to over 1 million wallets, spending just $5,175 to do so.
Transaction Timing and Behavior Patterns
Scammers have taken this strategy to the next level by deploying advanced bots. These bots monitor the blockchain for small "test" payments - something users are often advised to do for security. As soon as a test payment is detected, the bot sends a lookalike dust transaction to push the malicious address to the top of your transaction history.
"Sophisticated attackers now run bots that monitor the mempool and on-chain activity for small 'test' transfers - the exact security practice that users are taught to follow." - Blockaid
Ethereum's Fusaka upgrade on December 3, 2024, slashed transaction fees by about sixfold, making these mass-poisoning campaigns even cheaper. Within just two months, poisoning attempts skyrocketed - rising from 628,000 in November 2025 to 3.4 million in January 2026, a 5.5x increase. This highlights why verifying recipient addresses independently is more important than ever.
Recipient Verification and Validation
Never rely on your transaction history to copy recipient addresses, no matter how familiar they seem. A chilling example occurred on January 30, 2026, when a cryptocurrency holder lost 4,556 ETH (around $12.4 million). The attacker had spent two months dusting the victim's wallet with a vanity address that matched their legitimate OTC deposit address. Just 32 hours before the theft, a final dust transaction ensured the fraudulent address appeared at the top of the victim's history.
To avoid such disasters, always retrieve recipient addresses from verified sources, like official invoices, saved contacts, or direct communication through a separate channel. For large transfers, confirm the details of test transactions through a phone call or encrypted message before proceeding with the full payment. And don’t just skim the address - check the entire string. Vanity addresses are designed to fool quick glances.
3. Address Matches First and Last Characters Only
Attackers take advantage of our habit of verifying only the beginning and end of wallet addresses. When you see a long address like 0x1234...ABCD, chances are you only check the edges. Scammers exploit this by using tools to create "vanity" addresses that mimic the first and last 4–8 characters of a legitimate address, leaving the middle altered. This trick relies on partial address verification, setting up future fraudulent actions.
Address History Anomalies
This scam often begins with a tactic known as "poisoning" your transaction history. Scammers monitor the blockchain for your legitimate transactions and then send a tiny "dust" payment from a lookalike address to your wallet. This positions the fake address at the top of your transaction list, making it more likely you'll accidentally copy it for your next transaction.
The scale of these attacks is alarming. In one 2024 campaign alone, attackers generated 82,031 fake addresses - nearly 1% of all new Ethereum addresses created during that time. Across four EVM-compatible chains in a single month, researchers identified 1.37 million addresses tied to poisoning scams. Though only 0.03% of these fake addresses received more than $100, the few successful cases yielded massive rewards.
Transaction Timing and Behavior Patterns
This approach highlights how attackers are evolving their tactics to exploit partial address verification. Bots are programmed to monitor the mempool and generate lookalike addresses almost instantly. These fake addresses are often inserted into your transaction history within the same block or just minutes after your legitimate transaction, ensuring they appear at the top of the list.
"The attacker does not need to hack your wallet. They simply need 4 seconds to create a mask that looks like your destination, and then they rely on your brain to fill in the blanks." – Coin Frontier Research Team
In one high-profile case from December 2025, a victim lost $50 million USDT after copying a spoofed address from their transaction history following a test payment.
Recipient Verification and Validation
Relying on the edges of an address is risky. While attackers can mimic the first and last characters, they can't copy the entire string. This underscores the importance of verifying the full address, as discussed in earlier sections.
For high-value transfers, use a hardware wallet with a physical screen to confirm the entire address - it’s isolated from malware and clipboard attacks. Additionally, check 4–6 random characters from the middle of the address using a trusted, independent source. Maintaining a verified address book can also help you avoid relying on your transaction history.
4. Payment Request Outside Normal Business Hours
Receiving a payment request at an odd hour - like 2:00 AM on a Sunday - should immediately raise red flags. Attackers often exploit these off-hours, knowing that finance teams are less alert, approval processes may be looser, and the urgency they create can lead to missed verification steps. These anomalies highlight the importance of having strict pre-transaction controls and carefully reviewing the timing of payments. Since January 2025, an average of 160,000 address poisoning transactions occur daily.
Transaction Timing and Behavior Patterns
The timing of a payment request can often hint at malicious activity. Off-hour requests are a classic red flag in substitution attacks because they take advantage of reduced scrutiny during unconventional times. Adding to this, attackers have become more sophisticated, using bots to monitor the blockchain mempool for small "test" transactions. These bots can detect test payments - intended as a security measure - and quickly insert lookalike addresses into your transaction history.
"Sophisticated attackers now run bots that monitor the mempool and on-chain activity for small 'test' transfers - the exact security practice that users are taught to follow before sending large amounts." – Blockaid
Although these attacks can occur at any time, they are especially dangerous during off-hours when rushed or skipped verification can leave systems vulnerable.
Policy Compliance and Governance
To mitigate risks during off-hours, organizations should enforce strict operational windows and automated governance rules. Limiting transaction approvals to standard business hours creates an additional layer of oversight. These restrictions ensure that high-stakes transfers requiring manual review or multi-signature approvals happen when teams are fully alert.
Modern governance tools, like Stablerail's policy-as-code engine, allow finance teams to establish rules such as: "Weekend transfers over $10,000 require additional approval" or "Payments to new addresses outside 9:00 AM–6:00 PM EST need CFO verification." These rules are automatically enforced by the system before any transaction is signed. For high-risk actions initiated during off-hours, additional identity verification - such as a phone call or encrypted message confirmation - can be required to proceed.
5. Payment to New Address Without Approval
Sending funds to an unverified address in the crypto world is a risky move. Unlike traditional bank transfers, where fraud might be reversed, blockchain transactions are final. Once funds are sent to the wrong address, they’re gone for good. This highlights the importance of strict verification protocols before approving payments.
Address History Anomalies
Hackers often exploit transaction histories with a tactic called "poisoning." They send zero-value or dust transactions from vanity addresses designed to resemble legitimate ones. This trick can lead to unapproved payments to malicious addresses. For instance, in a 2024 campaign, a single attacker generated 82,031 fake addresses, making up nearly 1% of all new Ethereum addresses created during that time. A shocking example occurred on January 30, 2026, when a crypto holder lost 4,556 ETH (around $12.4 million) while transferring funds to an OTC deposit address. The attacker had spent months dusting the victim’s wallet with a fake vanity address that mimicked the legitimate one’s prefix and suffix.
Policy Compliance and Governance
A common vulnerability for organizations is "blind signing", where signers approve transactions without fully understanding the context or verifying the recipient.
"This vulnerability, also known as blind signing, has resulted in billions of losses." – Chainalysis
To combat address substitution attacks, companies must implement stringent governance protocols. These include maintaining allowlists or whitelists - registries of pre-approved addresses that block or flag transactions to unverified destinations. Tools like Stablerail’s policy-as-code engine help enforce such rules. For example, finance teams can set up automatic policies like: "Payments to new addresses over $5,000 require CFO approval and verification."
Recipient Verification and Validation
Even the best policies need to be paired with thorough recipient verification. Avoid copying addresses directly from transaction histories, as they may have been tampered with. Instead, use a verified address book and confirm new addresses through secure methods like phone calls or encrypted messages. For large transactions, take the time to verify every character of the recipient’s address. Vanity addresses are specifically designed to exploit quick, superficial checks.
"Checking every single character is the only way to be completely safe." – MetaMask Help Center
6. Same Address Used Across Multiple Chains Without Verification
Attackers are now exploiting the compatibility of wallet addresses across multiple EVM-compatible chains - like Ethereum, BNB Chain, and Polygon - to escalate address substitution attacks. These wallets function the same way across these chains, allowing attackers to insert fake addresses on multiple networks. Relying on a familiar prefix or suffix to trust an address across chains can leave your organization vulnerable.
Address History Anomalies
Attackers often observe transaction patterns on one blockchain and then manipulate transaction histories on others. They do this by introducing vanity addresses that mimic the first and last characters of legitimate ones. For example, on December 20, 2025, a trader lost $50 million in USDT when an automated script swapped in a fake address during a transaction. This spoofed address matched only the first five and last four characters of the intended recipient's address. The issue became more widespread after Ethereum's Fusaka upgrade, with cross-chain poisoning attempts jumping from 628,000 in November 2025 to 3.4 million by January 2026. In one case, an attacker used 3 million dust transfers targeting over one million addresses, spending just $5,175 to execute the scheme. These incidents highlight the urgent need for stronger governance protocols to avoid blind approvals.
Policy Compliance and Governance
To combat these risks, finance teams should adopt chain-specific address verification policies. Wallet interfaces often display limited details, making it easy to confuse a spoofed address with a legitimate one. As part of a broader pre-sign control process, these policies can help prevent errors. For instance, Stablerail’s policy-as-code engine allows users to create rules like "Only allow USDC transactions on Base/Ethereum" or "Require CFO approval and verification for payments over $5,000 to new addresses on any chain." These automated checks are enforced before transactions are signed.
Recipient Verification and Validation
Even if an address shares a familiar prefix, always verify the entire 42-character string on each chain to ensure the recipient controls it. Pay special attention to the middle portion of the address, which attackers often count on users overlooking. Maintain a verified address book for each chain and perform small test transactions before transferring large amounts. This extra step ensures the recipient truly controls the address.
7. Large Transfer to Recently Added Address
Large transfers to newly added addresses carry significant risk. High-value transactions, in particular, demand thorough pre-sign checks to guard against substitution attacks. These attacks often exploit rushed decisions by finance teams, especially when recipient details aren't re-verified.
Transaction Timing and Behavior Patterns
Attackers often take advantage of the common practice of sending small test transactions. Here's how it works: when a test payment is sent, bots quickly generate a lookalike address and send a tiny "dust" transaction (e.g., 0.005 USDT) to push the malicious address to the top of the transaction history. For example, on December 20, 2025, an investor lost $50,000,000 USDT after sending a $50 test transaction to a secondary wallet. Within minutes, an attacker’s bot sent a dust transaction, manipulating the victim into using the poisoned address for the remaining $49,999,950 transfer.
These attacks happen fast. With modern tools like NVIDIA RTX 4090 GPU clusters, attackers can create lookalike addresses that mimic the first and last four characters of a legitimate address in about four seconds. Some attackers go further, running sustained "dusting" campaigns over months. On January 30, 2026, a cryptocurrency holder lost 4,556 ETH (about $12.4 million) during a transfer to an OTC deposit address. The attacker had spent two months dusting the victim's wallet with a vanity address that matched both the prefix and suffix of the legitimate address. The final dusting occurred just 32 hours before the theft. The speed and precision of these attacks make them particularly dangerous.
Policy Compliance and Governance
To counter these evolving threats, organizations should adopt robust multi-level approval processes. For large transfers to new addresses, enforce separation of duties: one person proposes the transaction, and another approves it. This approach reduces the risk of a single compromised account causing significant losses.
Automated policy rules can also help. For instance, systems like Stablerail’s policy-as-code engine allow teams to set rules such as "New address payments over $5,000 require CFO approval + verification" or "Weekend transfers over $10,000 need additional approval." These rules are automatically applied to every payment intent before signing, ensuring consistent enforcement and bolstering address verification systems.
Recipient Verification and Validation
When dealing with new addresses, always retrieve them from secure sources like a verified address book or directly from the original source (e.g., an exchange deposit page or an encrypted vendor message). To guard against spoofing, focus on verifying characters in the middle of the address rather than the easily manipulated first and last characters. For high-value transactions, confirm new addresses through an independent channel, such as a phone call or encrypted message, instead of relying solely on on-chain data.
"Address poisoning is not a hack of the blockchain; it is a hack of your attention span." - Coin Frontier Research Team
8. Missing Counterparty Confirmation Before Payment
Skipping counterparty confirmation before making a payment is a gamble you don’t want to take. Blockchain transactions are irreversible, so sending funds to an incorrect or spoofed address without verifying it first can lead to a permanent loss of assets. Once you’ve signed and broadcast a transaction, there’s no calling a bank, no chargebacks, and no way to undo the transfer. This highlights the critical importance of thorough off-chain verification, especially for high-value transfers.
Transaction Timing and Behavior Patterns
Hackers have turned test transactions into a weapon. Here’s how it works: bots monitor the mempool for test payments. As soon as they detect one, they spring into action - creating a fake address that mimics the legitimate one and sending a tiny "dust" transaction to the victim’s wallet. This can happen in mere seconds. A chilling example occurred in December 2025 when an investor lost $50,000,000 USDT just 26 minutes after a test transaction. The attacker’s bot spotted the test transfer, inserted a nearly identical spoofed address, and the victim unknowingly copied the malicious address from their transaction history for the final transfer.
Some attackers play the long game, running ongoing dusting campaigns over months. Their goal? To keep their spoofed addresses visible in transaction histories, waiting for the perfect moment to strike.
Recipient Verification and Validation
When it comes to verifying recipient addresses, diligence is non-negotiable. Always confirm the counterparty’s identity through an external channel before proceeding with any high-value transfer. For payments exceeding $10,000, use methods like a phone call, encrypted message, or video call where the full address is read aloud. Pay special attention to the middle characters of the address, not just the beginning and end.
Why focus on the middle? Attackers often create vanity addresses that match the first and last few characters of a legitimate address, knowing most people only glance at these sections. To avoid falling for this trick, verify at least four random characters from the center of the address string. Better yet, rely on tools like a verified address book or whitelist feature in your wallet. And never copy addresses directly from transaction history, as it’s a public log that attackers can manipulate.
Policy Compliance and Governance
Organizations can further protect themselves by enforcing strict confirmation workflows for new recipients and high-value transfers. Tools like Stablerail’s policy-as-code engine make this easier by automating rules such as “Payments over $5,000 to new addresses require CFO approval and verification” or “Weekend transfers above $10,000 need additional layers of approval.” These automated policies ensure consistent governance, applying checks to every payment intent before it’s signed.
Stablerail’s system also generates a Risk Dossier for each transaction, providing a clear verdict - PASS, FLAG, or BLOCK - along with plain-English explanations. This helps approvers understand exactly why a transaction needs extra scrutiny. From initial intent to risk checks, approvals, and signing, every step is documented in a full audit trail, offering CFO-level evidence for auditors and regulators.
"The goal is to transform transaction approval from a trust-based process into a comprehensive verification framework that provides confidence in every transaction." – Chainalysis Team
9. Skipped Verification Steps or Policy Overrides
When finance teams bypass verification protocols or override established policies, they open the door to address substitution attacks. These protocols are designed to safeguard against such threats, and skipping them undermines the entire pre-sign control process. Unfortunately, these shortcuts often occur under pressure - tight deadlines, urgent vendor requests, or executive demands can push teams to cut corners. The consequences can be devastating. In 2025, impersonation attacks surged by 148%, fueled partly by AI tools capable of mimicking executive voices and appearances, making it easier for attackers to coerce employees into neglecting critical checks.
Policy Compliance and Governance
One of the riskiest shortcuts a finance team can take is overriding policies that require multiple signatures for large transactions. Attackers often target executives or key employees with the authority to bypass these dual approval requirements. This tactic is especially effective in mandate fraud, where scammers impersonate vendors to alter payment instructions. Without strict adherence to policies - such as confirming changes via a phone call or a separate communication channel - these fraudulent requests can lead to irreversible financial losses.
To address this, organizations need more than just basic multisig thresholds. They should adopt detailed controls, such as transaction amount limits, recipient allowlists, and time-based restrictions. Tools like Stablerail's policy-as-code engine can automate these safeguards, applying checks to every payment before approval. For instance, rules like "Payments over $5,000 to new addresses require CFO approval and verification" or "Transfers exceeding $10,000 on weekends need additional approval" can be enforced automatically. These measures ensure that no step is skipped, even under time pressure, helping maintain policy integrity and reducing vulnerabilities.
Transaction Timing and Behavior Patterns
Fraudsters often exploit urgency to bypass standard verification processes. Phrases like "transfer today" or "final warning" are designed to create panic, overriding critical thinking. High-volume periods, such as the holiday season, make this strategy even more effective. During these times, overwhelmed finance teams are more likely to miss fraudulent requests. In fact, 79% of companies that experienced fraud in 2024 reported business email compromise (BEC) attacks, where scammers impersonated executives or vendors to rush payments through.
A glaring example occurred on February 21, 2025, when the Lazarus Group exploited this urgency to steal $1.46 billion from ByBit. They injected malicious JavaScript into the Gnosis Safe web UI, deceiving signers into approving unauthorized withdrawals. The interface displayed routine transactions, leading signers to "blind sign" without verifying the payload on their hardware devices. This incident highlights how skipping verification steps can result in catastrophic losses.
"The blockchain recognizes only what users sign, regardless of their intent".
Address History Anomalies
When verification steps are skipped, teams often rely on transaction history instead of a verified address book, which can be a costly mistake. Address poisoning exploits this reliance by introducing lookalike addresses into transaction logs through small "dust" transactions. Sophisticated attackers may plant these addresses over months, ensuring they appear at the top of the history when a high-value transaction is made. Sending funds to an address from the history, rather than a verified allowlist, is a clear indication that internal verification policies were bypassed for convenience.
10. Wallet Address Doesn't Match Invoice Details
When the wallet address in a payment request doesn't align with the one on the invoice, it signals an address substitution attack. Since on-chain transactions can't be reversed, this verification step becomes critical. It works alongside earlier measures designed to spot lookalike addresses and dusting schemes.
Recipient Verification and Validation
The safest approach is to manually verify every single character of the wallet address against the invoice or a trusted address book. Attackers often create lookalike addresses that match the first and last few characters of a legitimate one, knowing that many users only check those parts.
Take this example: In May 2024, a crypto whale almost lost $68 million in wrapped bitcoin after copying a fraudulent address (0xd9A1c) from their transaction history instead of the correct address (0xd9A1b). Although the attacker returned most of the funds, they kept $3 million, citing token appreciation as the reason.
Relying solely on transaction history is risky - it can be manipulated. Since January 2025, over 65.4 million address poisoning attempts have been flagged, averaging more than 160,000 incidents daily. Alarmingly, about 1 in 200 of these attempts succeed in deceiving victims into sending funds.
To avoid falling prey, ensure every character of the address matches the invoice. Automated governance tools can simplify this process by enforcing these checks before any transaction is signed.
Policy Compliance and Governance
Organizations need to implement machine-readable policies that verify payment addresses against a pre-approved address book. Policies should ensure invoice details align perfectly and block any transaction involving unverified addresses. For stablecoins, it's equally important to confirm details like the contract's decimals, name, and symbol against official documentation (e.g., Circle's directory for USDC) to avoid falling for counterfeit contracts.
Tools like Stablerail's policy-as-code engine streamline these safeguards. For instance, rules such as "Payments over $5,000 to new addresses require CFO approval and verification" can prevent unauthorized transactions. Stablerail cross-references payment intentions against an approved address registry and generates a risk report. This report highlights mismatches in plain language, identifying the exact invoice field or policy clause that caused the issue.
By enforcing strict policies, organizations can significantly reduce risks tied to timing-based manipulation.
Transaction Timing and Behavior Patterns
Attackers often rely on prolonged dusting campaigns, sending small, frequent transactions to a target wallet over weeks or months. This strategy ensures their malicious address stays prominent in the transaction history, increasing the likelihood that a victim mistakenly uses it during a legitimate payment.
"The attack requires no technical exploitation of any smart contract or wallet software. It targets the most vulnerable layer of the stack: human behavior." - Blockaid Blog
These attacks exploit trust and routine, making it essential to stay vigilant and adopt stringent verification practices.
How to Detect and Prevent These Attacks
Stopping address substitution attacks requires layered defenses that work together before a transaction is signed. Finance teams need to pair automated tools with strict approval processes because attackers now use high-speed bots to create fake addresses almost instantly, making manual checks insufficient. These layers build on the earlier warning signs, ensuring that any unusual activity triggers an immediate response.
Start with sanctions screening and counterparty risk scoring. Automated tools can match recipient addresses against global sanctions lists and blockchain intelligence feeds, which track "seeder" wallets - accounts known for generating fraudulent addresses. For example, in a 2024 Ethereum poisoning campaign, researchers discovered that 98% of phishing addresses were managed by just four entities, which collectively earned 92% of the illicit gains. Identifying these patterns early stops funds from reaching bad actors. Beyond screening, continuous anomaly detection can provide real-time alerts.
Anomaly detection is another essential layer, designed to catch unusual behavior. Systems should flag spikes in transaction activity (like multiple small transfers in rapid succession), payments outside of normal business hours, or transfers to addresses that suddenly appear in transaction records. Since January 2025, over 65.4 million address poisoning attempts have been flagged on-chain, averaging more than 160,000 daily. These automated alerts can identify patterns that humans might overlook under time pressure.
Incorporate policy enforcement into pre-sign controls to block risky transactions before they happen. Machine-readable rules - such as requiring CFO approval and full address verification for payments exceeding $5,000 to new addresses - can prevent unauthorized transfers. Platforms like Stablerail implement this by running sanctions checks, anomaly detection, and counterparty scoring simultaneously. They generate a Risk Dossier that highlights which specific rule or behavior raised a red flag.
Lastly, for high-value transfers, enforce dual approvals and an out-of-band confirmation, like a phone call, to counteract risks from email compromise. In 2024, 79% of fraud victims experienced Business Email Compromise (BEC), where attackers infiltrated email threads to alter payment details. By combining automated measures with rigorous manual checks, finance teams can effectively guard against address substitution attacks.
Conclusion
Address substitution attacks take advantage of human vulnerabilities in corporate treasury operations. Even with secure custody and multisig solutions in place, these measures can fall short if finance teams rely on copying addresses from transaction history or skip essential verification steps. As Ledger aptly explains:
"The truth is, even if the blockchain itself is secure, the biggest point of failure is often human error; like copying the wrong address or trusting what looks familiar without checking and verifying".
The scale of these threats is growing at an alarming rate. Since January 2025, security platforms have identified over 65.4 million poisoning transactions, with an average of more than 160,000 attempts per day. Ethereum's Fusaka upgrade in December 2025, which slashed transaction fees by about six times, has only made it easier for attackers to operate at scale. For instance, one scammer managed to send 3 million dust transactions to over 1 million unique addresses for just $5,175. This shift in economics has tilted the playing field in favor of attackers, making it essential to adopt stricter transaction verification measures.
To counter these evolving tactics, layered defenses must be implemented before transactions occur. Finance teams need to stop copying addresses, verify every character meticulously, and enforce strict policies - such as requiring CFO approval for new recipients exceeding $5,000. For high-value transfers, using out-of-band confirmations ensures an added layer of security.
Pre-transaction governance tools are critical for moving from reactive to proactive defense strategies. Platforms like Stablerail provide a solution by operating above custody systems and before transaction signing. They automate processes like sanctions screening, anomaly detection, and crypto compliance checks for every payment intent. By generating a comprehensive Risk Dossier and maintaining a detailed audit trail, these tools eliminate the risks of blind signing and equip finance teams with the context they need to make informed decisions confidently.
FAQs
How can I tell a poisoned address from a real one?
To spot a poisoned address, it's crucial to recognize that scammers often design addresses that closely resemble legitimate ones to trick users. Always double-check addresses independently before transferring funds. You can do this by comparing them with previous transactions or using reliable verification tools. Avoid trusting visual similarities alone - this is exactly what scammers count on. Tools like Stablerail can help by enforcing policy checks and approvals to minimize mistakes. Staying alert and using thorough verification methods are essential to sidestep address poisoning.
Why are tiny “dust” deposits a warning sign?
Attackers often use tiny "dust" deposits as part of address poisoning schemes. These small, seemingly harmless transactions are designed to manipulate transaction histories. The goal? To confuse users and trick them into sending funds to fraudulent addresses. By tampering with transaction records, these schemes prey on users' trust, highlighting the importance of staying alert and carefully verifying addresses before making any transfers.
What should finance teams verify before signing a large transfer?
Finance teams need to check a few critical elements to keep transactions secure. These include sanctions screening, exposure analysis, behavioral anomaly detection (like spotting unusual transaction timings or amounts), and counterparty risk scoring.
It's also essential to provide clear, plain-language explanations linked to policies and maintain human oversight through approval processes that include a complete audit trail. Adhering to predefined policies - such as approval thresholds or restrictions on specific assets - helps guard against threats like address substitution attacks and safeguards the organization's resources.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


