
When sending high-value stablecoin payments (like USDC), the risks are real: compliance failures, exposure to sanctioned wallets, or losses from compromised smart contracts. Blockchain transparency offers tools to mitigate these risks, but many organizations still rely on outdated, manual processes. This checklist provides a structured approach to evaluate counterparties before making a transaction, helping you identify risks early and avoid costly mistakes.
Key Takeaways:
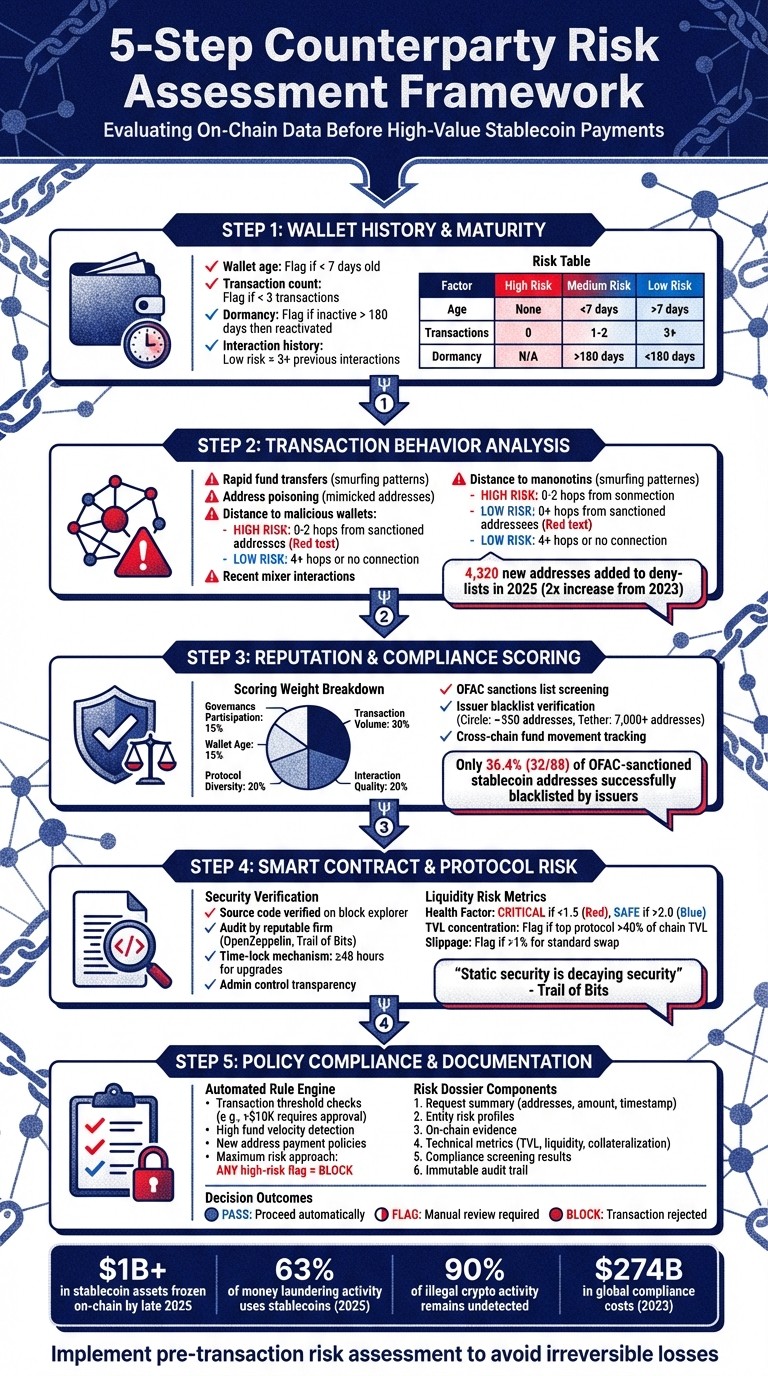
Assess Wallet History: Check wallet age, transaction history, and dormancy. New or reactivated wallets can signal higher risk.
Analyze Behavior: Look for irregular patterns like rapid transfers, address poisoning, or proximity to flagged wallets.
Evaluate Smart Contracts: Verify audit status, admin controls, and protocol risks like liquidity and governance centralization.
Check Compliance: Screen addresses against sanctions lists and issuer blacklists to avoid regulatory exposure.
Document Decisions: Compile a risk dossier with wallet data, compliance checks, and transaction details for audit readiness.
5-Step Counterparty Risk Assessment Framework for On-Chain Stablecoin Payments
Pre-Transaction Assessment Framework
When considering a $50,000 USDC payment to a new vendor, it’s essential to evaluate counterparty risk systematically. While the blockchain’s public ledger offers visibility, raw data alone won’t confirm whether a wallet is trustworthy or linked to any sanctioned entities. A well-structured framework integrates various data sources to provide a comprehensive evaluation.
The objective is straightforward: spot potential red flags before releasing funds. This process revolves around three critical questions: Who is the counterparty? What does their on-chain activity reveal? And what risks could they pose to your organization? Below, we break down how blockchain data and behavioral metrics come together to answer these questions.
Understanding On-Chain Data Sources
Effective counterparty assessment starts with knowing where to find reliable information. Core blockchain data - like account balances, transaction histories, and nonce counts - can reveal patterns such as capital velocity and automated behaviors.
But to dig deeper, wallet behavioral metrics come into play. These include wallet age, transaction frequency, diversity of interactions (how many protocols the wallet has engaged with), and periods of dormancy. For instance, a wallet reactivating after 180+ days of inactivity is often a warning sign of potential compromise or links to laundered funds.
Smart contract events provide additional insight by showing transaction intent. Parsing logs for events like Transfer or Swap can clarify the purpose behind specific transactions.
Another layer of verification comes from reputation and attestations. Tools like Ethereum Attestation Service (EAS) or Verifiable Credentials (VCs) allow you to check whether a wallet has been vouched for by trusted entities or has earned on-chain credentials. Additionally, compliance and sanctions labels help cross-reference wallets against OFAC sanctions lists and deny-lists maintained by issuers like Circle and Tether.
Connection analysis powered by machine learning evaluates how close a wallet is to known malicious addresses. For example, if a wallet is just 1–2 hops away from a sanctioned entity, that proximity could justify blocking the transaction. Likewise, attributed address databases can confirm whether a wallet belongs to a known exchange, protocol, or system address, reducing the risk of false positives.
These tools and data sources form the foundation for identifying specific risk categories, which we’ll explore next.
Types of Risks Found in On-Chain Data
Addressing the core questions reveals four major risk categories:
1. Financial and Liquidity Risks
These risks stem from factors like TVL (Total Value Locked) concentration, liquidity depth, slippage, and collateral health. For example, if the top 10 wallets hold over 70% of a protocol’s assets, it signals systemic vulnerability. Similarly, when a single protocol accounts for more than 40% of a chain’s TVL, it raises concerns about over-reliance on that protocol.
2. Counterparty and Behavioral Risks
This category focuses on wallet-specific issues. High-risk indicators include new wallets (less than 7 days old or with no transaction history), dormant wallets suddenly reactivating, or address poisoning (where malicious actors mimic trusted wallet prefixes or suffixes). In 2025 alone, over 4,320 new addresses were added to on-chain deny-lists - double the count from 2023.
3. Security and Governance Risks
Smart contract vulnerabilities are another major concern. Key areas to monitor include upgrade frequency, changes to admin keys, and governance centralization. A notable example occurred in October 2024 when Radiant Capital lost $53 million due to a weak 3-of-11 multisig configuration - attackers only needed to compromise three signers to bypass security.
"Static security is decaying security." - Trail of Bits
4. Compliance Risks
These risks are particularly pressing for corporate treasury operations. Real-time screening can identify exposure to OFAC-sanctioned addresses, AML violations, or non-compliance with the "Travel Rule." By late 2025, over $1 billion in stablecoin assets had been frozen across major networks. However, only 36.4% (32 out of 88) of OFAC-sanctioned stablecoin addresses had been successfully blacklisted by issuers, underscoring the limitations of relying solely on issuer-level controls.
To manage these risks, assessments often assign a Low/Medium/High score or a numerical rating (e.g., 0–24 scale). These scores determine whether the transaction proceeds automatically, requires manual review with justification, or gets blocked entirely. Crucially, these decisions must occur before signing the transaction to avoid irreversible consequences.
Wallet History and Transaction Behavior Checklist
This checklist is designed to complement the pre-transaction framework by honing in on wallet history and transaction behavior - two crucial factors in assessing on-chain reputation. By examining these elements, you can identify patterns that might indicate risk before releasing funds to a counterparty. For a broader assessment of asset-specific threats, you can also use a stablecoin risk calculator to generate a detailed risk score. The focus here is on three main areas: wallet maturity, transaction behavior, and fund origins.
Verify Wallet Age and Transaction History
Start by checking the wallet's activity level to gauge its credibility. A wallet with no transactions is a clear red flag, while those with fewer than three transactions or created less than seven days ago are considered medium risk. On the other hand, established wallets with a solid transaction history provide a level of reassurance.
Be cautious with dormant wallets that suddenly become active. If a wallet has been inactive for over 180 days and then initiates a transaction, this warrants a medium-risk classification. Such behavior could indicate a compromised account or a "sleeper" wallet being misused for illicit purposes.
Once you've assessed wallet maturity, move on to analyzing transaction patterns for further insights.
Analyze Transaction Success Rates and Patterns
Look for irregular transaction behaviors. Money launderers often use techniques like rapid fund transfers across multiple wallets to obscure the origins of funds. This method, sometimes referred to as smurfing, involves breaking large sums into smaller transactions or conducting sequential transfers to create distance from criminal sources.
Be on the lookout for address poisoning, where a malicious wallet mimics parts of a legitimate address to deceive you into sending funds to the wrong destination. Additionally, note that first-time interactions carry a higher risk compared to wallets you’ve transacted with multiple times. A wallet with no prior interactions is high risk, while three or more previous transactions lower the risk significantly.
"The number of steps doesn't change how the money was acquired." - Liat Shetret, Vice President of Global Policy and Regulation, Elliptic
Review Fund Sources and Movement
Building on transaction behavior analysis, it’s crucial to trace the origins and movement of a counterparty's funds. Examine how close the wallet is to known illicit entities. Wallets that are 0-2 hops away from sanctioned, ransomware, or darknet addresses are high risk, while those 4+ hops away or with no connection to such wallets are considered low risk.
Also, pay attention to interactions with known mixers. If a wallet has recently interacted with mixers or received funds from addresses flagged for sanctions violations, treat this as a serious warning sign. Use attribution databases to cross-check wallet addresses against those belonging to reputable exchanges, protocols, or system addresses. This helps reduce the likelihood of false positives while ensuring legitimate transactions aren’t mistakenly flagged.
Reputation Score and Credibility Indicators Checklist
This section dives into reputation scores and compliance indicators, complementing wallet history and transaction behavior to create a thorough risk profile. Reputation scores simplify risk assessment by consolidating various data points into a single metric, enabling consistent comparisons and decision-making across your organization. This process is further strengthened by using MPC wallets for treasury operations to enforce pre-signature policies.
Review On-Chain Reputation Scoring
A well-constructed reputation score incorporates behavioral, financial, and historical metrics. Typically, these scores weigh factors like transaction volume (30%), protocol diversity (20%), wallet age (15%), interaction quality (20%), and governance participation (15%) to evaluate counterparty risk comprehensively. For instance, a wallet with diverse protocol engagement and consistent transaction success is statistically less risky than one with sporadic activity or limited usage patterns.
Interaction diversity is particularly insightful, acting as a measure of genuine usage versus automated or bot-like behavior. For example, a wallet actively lending on Aave, trading on Uniswap, and participating in governance activities demonstrates a level of engagement that's challenging for malicious actors to mimic at scale. For lending or borrowing counterparties, financial health metrics become critical. Indicators such as the "Health Factor" (collateral-to-debt ratio), collateral diversity, and repayment history provide insight into a counterparty's ability to meet obligations. A health factor below 1.0 signals an undercollateralized position at immediate risk of liquidation.
"Credit is a data problem. Traditional models rely on opaque, lagging data. On-chain activity provides a real-time, immutable ledger of financial behavior, enabling continuous solvency proofs."
ChainScore Labs
Transparency is key when it comes to scoring models. The most reliable systems openly share their methodology, allowing you to understand why a counterparty received a specific score. This openness ensures confidence in the assessment process.
Once the reputation score is established, the next step involves evaluating compliance and regulatory exposure.
Evaluate Compliance and Regulatory Exposure
Compliance exposure builds on earlier risk metrics by cross-referencing wallet addresses against sanctions lists and issuer-specific blacklists. As of late 2025, over $1 billion in stablecoin assets have been frozen on-chain by issuers across major networks. However, only 36.4% (32 out of 88) of OFAC-sanctioned stablecoin addresses have been correctly blacklisted on-chain by major issuers. This highlights the limitations of relying solely on issuer enforcement.
Different issuers exhibit varying levels of proactivity. For example, Tether has blocked over 7,000 addresses, while Circle has blacklisted approximately 550. These discrepancies underscore the need to assess whether a counterparty's clean status on one network might not hold on another.
Interestingly, only 0.04% of the total frozen stablecoin value - roughly $419,320 - is tied to OFAC-sanctioned addresses. This suggests that most blacklisting stems from issuer-driven risk detection rather than official regulatory lists. Consequently, a counterparty not appearing on sanctions lists could still be flagged based on behavioral patterns or associations with high-risk entities.
"Relying solely on issuer-level blacklisting from Circle or Tether is not sufficient for meeting regulatory obligations - especially for protocols with user-facing frontends or operational exposure in regulated jurisdictions."
Range Security
It's also crucial to track cross-chain fund movements. Malicious actors increasingly transfer assets across blockchains (e.g., Ethereum to Solana) to evade single-chain blacklists. For example, a counterparty blacklisted on Ethereum could remain active on Solana. Cross-chain tracing tools can help identify these evasive patterns and ensure a more comprehensive risk assessment.
Smart Contract and Protocol Risk Checklist
Once you've assessed reputation scores and compliance exposure, the next step is to evaluate the smart contracts and protocols your counterparty interacts with. Even if a wallet appears trustworthy, it can still pose risks if it engages with poorly secured or unstable protocols. This part of the process focuses on examining the security of these systems and identifying liquidity risks that could affect your counterparty's ability to meet their obligations.
Verify Smart Contract Audit Status
Start by confirming that the smart contract's source code is verified on platforms like Etherscan or Arbiscan. Verified code ensures that the deployed bytecode matches the audited version, reducing the likelihood of tampering after deployment. Check whether the audit was conducted by reputable firms, such as OpenZeppelin or Trail of Bits, and ensure that upgradeable contracts have corresponding audit reports. Be cautious of rapid upgrades - those implemented in under 24 hours - without a public audit, as they can signal potential issues. Audits are a critical step before launching on the mainnet, though it's important to remember they represent the state of security at a specific point in time.
Review administrative controls to understand who has the authority to upgrade contracts. Look for a time-lock mechanism - ideally 48 hours or longer - that provides a buffer to address malicious or buggy changes.
"Static security is decaying security."
Trail of Bits
You should also assess the protocol's commitment to security by checking for active bug bounty programs and reviewing disclosures of past incidents. Some protocols now enhance transparency by storing audit reports on IPFS or Arweave, with content hashes recorded on-chain to create an immutable record. Additionally, decentralized reputation protocols like the Ethereum Attestation Service (EAS) can help you find signed claims or audit reports tied to a contract address.
Once the smart contract's security is verified, move on to analyzing the protocol's participation and liquidity risks.
Assess Protocol Participation and Liquidity Risks
The next step is to evaluate the protocols your counterparty interacts with. If they participate in lending platforms like Aave or Compound, monitor their Health Factor, which measures the collateral-to-debt ratio. A Health Factor below 1.0 indicates a position is at risk of liquidation, posing an immediate concern. Classify positions by risk: a Health Factor under 1.5 is critical, while anything above 2.0 is considered safer.
Look at Total Value Locked (TVL) concentration to identify systemic risks. For instance, if a protocol controls more than 40% of a blockchain's TVL, it could present heightened risk. Similarly, centralization risks increase if the top 10 wallets hold over 70% of a protocol's TVL, or if the top five pools account for more than 60%.
Liquidity depth is another key factor. Measure slippage at price deviations of 1%, 5%, and 10%. High slippage - anything over 1% for a standard swap - or shallow liquidity can signal significant volatility risks for your counterparty's assets. For example, during the March 2023 banking crisis, USDC dropped to $0.87 and DAI fell to $0.85, showing how even well-audited stablecoins can experience severe depegging under systemic pressure. This highlights the need to monitor oracle reliability, as price discrepancies of more than 2% between primary oracles (like Chainlink) and secondary sources could indicate vulnerabilities to manipulation.
Lastly, consider protocol dependencies, such as reliance on bridges or yield aggregators. In July 2023, the Multichain hack resulted in $126 million in stolen funds, though stablecoin issuers were able to freeze $66 million within hours. This incident underscores the importance of understanding issuer-level freeze controls and their role in mitigating losses. Governance participation is also worth tracking - low voter turnout (below 5%) or concentrated voting power in a few addresses can signal increased centralization and associated risks.
"The goal is not to eliminate risk but to illuminate it, providing a comparative lens through which to view protocols."
Chainscore Labs
Behavioral Anomaly and Policy Compliance Checklist
When it comes to managing counterparty risk, looking beyond smart contract audits is essential. Evaluating on-chain behavior adds another layer of protection, as even wallets that pass security checks can pose threats if they engage in unusual activities or fail to meet compliance standards. This process involves spotting irregular transactions and ensuring that counterparties adhere to your organization's rules before approving any transfers.
Detect Behavioral Anomalies
Start by examining the wallet's lifecycle. Certain patterns, such as fewer than three transactions, an account less than seven days old, or reactivation after 180 days of inactivity, can signal elevated risk levels.
Transaction patterns also hold valuable clues. Be wary of behaviors like "peel chains", where funds are distributed across multiple wallets, or sudden spikes in transaction activity - such as a 10x increase compared to the wallet's 30- or 90-day average. Other red flags include first-time interactions and round-number transfers, particularly in cross-chain payments.
Another critical factor is proximity to malicious entities. A "distance-to-malicious" score provides context beyond basic wallet history, identifying addresses that are zero to two hops away from blacklisted wallets as high-risk. Addresses further removed generally pose less concern. Additionally, watch for address poisoning tactics, where fraudulent addresses mimic legitimate ones by matching the first or last four characters to mislead users.
Interactions with high-risk protocols also warrant attention. For instance, wallets engaging with unverified smart contracts or services like Tornado Cash could indicate risky behavior. Consider that by late 2025, stablecoin issuers had frozen over $1 billion in assets on-chain, with 4,320 new addresses added to deny-lists in that year alone - more than double the total from 2023. Yet, enforcement remains inconsistent, as only 36.4% of OFAC-sanctioned stablecoin addresses have been effectively blacklisted by major issuers.
"Blacklisting is not driven by regulatory lists alone. Instead, issuers appear to rely on internal risk detection, incident reports, or ecosystem feedback, resulting in a much broader, more discretionary enforcement scope."
Andres M, Range
Verify Policy Compliance
Once you've flagged potential anomalies, the next step is to ensure the counterparty aligns with your organization's payment policies. Automated rule engines can help identify transactions that exceed specific thresholds - such as amounts over $10,000 - or those involving high fund velocity or recent interactions with mixers.
To enforce these policies, codify them into executable rules. For example, you could set a policy like "New address payments over $5K require CFO approval" and implement it using domain-specific languages. These rules act as pre-sign filters, automatically applied to every transaction before approval.
Adopting a maximum risk approach is crucial. If any individual assessment - such as detecting a new wallet, identifying connections to malicious entities, or spotting dormant wallet reactivation - indicates high risk, flag the entire transaction. This ensures no warning sign is ignored.
"Compliance must therefore shift from retrospective paperwork to pre-trade and in-flight controls."
Newton Protocol
For organizations handling corporate stablecoin payments, platforms like Stablerail provide tools to streamline these processes. Stablerail automates behavioral anomaly detection and policy compliance checks before transactions are signed. Its pre-sign features include time-of-day analysis, comparisons of transaction amounts against historical baselines, and reviews of payout patterns. These checks are governed by policy-as-code frameworks and generate detailed audit trails with plain-English explanations, linking specific policy clauses and timestamps. This ensures compliance documentation meets the standards required by auditors and regulators.
Finally, compile these findings into a risk dossier to support governance and audit readiness. These pre-sign measures complete the on-chain evaluation process, helping organizations manage risk effectively before a transaction is finalized.
Decision and Documentation Checklist
After conducting detailed risk assessments, the next step is to organize and document your findings into a well-structured dossier. This serves as a defensible record for every transaction decision.
Compile a Risk Dossier
Start by summarizing critical insights from wallet history, reputation scoring, smart contract audits, and behavioral analyses. This dossier becomes your go-to reference for decision-making. Begin with the request summary, which should include sender and recipient addresses, the transaction amount in USD, the network, token type, and an ISO 8601 timestamp. Follow this with entity risk profiles that detail the legal entity name, jurisdiction, leadership information, and any licenses held by the counterparty.
Break down each risk factor using identifiers, risk levels (Low, Medium, or High), and clear descriptions. Ensure the dossier highlights the highest risk detected. Include on-chain evidence such as wallet addresses, transaction history, fund movement patterns, and any prior interactions between the parties.
For protocol-based transactions, technical metrics are crucial. Incorporate data on Total Value Locked (TVL) distribution, liquidity depth, collateralization ratios, and the status of smart contract audits. From a compliance perspective, document sanctions screening results, Travel Rule metadata (originator and beneficiary details), and any connections to suspicious addresses. Specify the number of "hops" between your counterparty and known illicit entities.
"If we didn't have TRM by our side, it would take a lot of manual effort on our end to capture the information that's readily available within TRM itself, in terms of the off-chain profile and tracking down blockchain data."
Visa Representative
Platforms like Stablerail simplify this process by automating risk dossier creation. Their pre-sign workflow produces verdicts (PASS/FLAG/BLOCK) with plain-English explanations tied to policy clauses, timestamps, and on-chain evidence.
Ensure Governance and Audit Readiness
Once your dossier is complete, the next step is to formalize governance processes to support each transaction decision. Record every action - from initial screening to final approval - in an immutable audit trail. This includes logging analyst IDs, decision rationales, the specific policy version applied, and cryptographic proof hashes. Archive data snapshots used during the evaluation, as on-chain risk scores can change over time. This ensures you can demonstrate what information was available at the time of the decision.
"All decisions - every transaction screened, every rule triggered, every analyst action - must be immutably logged, preferably on-chain or in a tamper-evident database, to satisfy regulatory examinations."
ChainScore Labs
Establish clear escalation protocols to define who reviews flagged activity and who has the authority for final approvals. If an alert is dismissed or escalated, investigators must document their reasoning, referencing the data snapshots they reviewed. Additionally, version your rule engines and governance policies to show regulators exactly which rules were in effect at the time of each transaction.
The stakes are high. In 2023, global compliance costs exceeded $274 billion, much of it tied to inefficient manual processes. In 2024, TD Bank faced $3 billion in penalties from U.S. regulators for failing to report suspicious crypto-related activity. That same year, OKX agreed to a $505 million guilty plea for anti-money laundering (AML) failures. These examples highlight the importance of thorough documentation - it’s the backbone of defensible compliance.
Stablerail addresses these challenges by creating a complete audit trail for every action in its workflow. This includes intent creation, risk checks, flags raised, overrides applied, approvals granted, and final signing. The platform generates structured, CFO-grade reports with timestamps, user IDs, policy versions, and decision rationales. It replaces the outdated "wallet + spreadsheet + Slack" method with a governed, auditable process, ensuring compliance that stands up to scrutiny from auditors, boards, and regulators.
Conclusion
Assessing counterparty risk with on-chain data is a critical step for any organization involved in stablecoin transactions. While blockchain technology offers transparency in tracking transaction flows, it doesn't reveal the identities behind wallet addresses. Using a structured compliance checklist helps close this gap by transforming passive observation into proactive risk management, allowing for real-time threat detection before funds are compromised.
The importance of managing counterparty risk becomes even more apparent when considering recent trends. By 2025, stablecoins accounted for 63% of identified money laundering activity, overtaking Bitcoin as the top choice for illicit transactions. Yet, about 90% of illegal crypto activities remain undetected. Static sanctions lists alone are insufficient; only 36.4% of OFAC-sanctioned stablecoin addresses have been blacklisted on-chain. Criminals exploit this gap by funneling funds through intermediary wallets.
The checklist approach detailed here - covering areas like wallet history, reputation scoring, smart contract audits, behavioral anomalies, and policy compliance - offers a layered defense system that captures risks often overlooked by single-metric checks. To keep up with the speed of blockchain transactions, automation is essential.
Stablerail simplifies this process by automating the creation of risk dossiers, implementing policy-as-code governance, and producing immutable audit trails for every transaction decision. Its pre-sign workflow evaluates sanctions exposure, behavioral anomalies, and counterparty risks before payments are executed. The result? Clear, plain-language verdicts backed by specific policy clauses and on-chain evidence. This modernized, automated approach replaces outdated manual methods, ensuring compliance and transparency for auditors, boards, and regulators alike.
FAQs
What on-chain signals are the biggest red flags before sending USDC?
Before transferring USDC, it's crucial to watch for on-chain red flags such as sanctions issues, taint or exposure risks, and policy violations. Behavioral anomalies, like odd transaction timings or irregular payout patterns, can also raise concerns. If a counterparty has a low risk score, it might suggest potential exposure to suspicious activity, warranting a deeper review before moving forward.
How many hops from a sanctioned wallet should trigger a block?
Blocking a wallet is usually initiated after 1 hop from a sanctioned wallet, though this can depend on your organization's risk management policies. Many in the industry consider 1 to 2 hops as the threshold for either escalating the situation or blocking the wallet entirely. The exact threshold often depends on how the organization assesses and manages counterparty risk.
What should a pre-sign risk dossier include for audit readiness?
A pre-sign risk dossier should lay out clear, evidence-based details to back up decisions. This includes elements like policy clauses, timestamps, and risk verdicts (e.g., PASS, FLAG, or BLOCK), along with explanations for why each decision was made. This approach not only ensures transparency but also helps maintain audit readiness by providing a solid, documented rationale for every action taken.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


