
Fraud is a growing threat to businesses and consumers alike. In 2024, 80% of U.S. companies faced payment fraud attempts, while consumer fraud losses rose to $12.5 billion - a 25% increase from the prior year. With blockchain transactions being irreversible, detecting fraud before it happens is more important than ever.
This guide provides actionable steps to assess counterparty risks, verify identities, analyze transaction patterns, and screen for cryptocurrency-specific threats. Highlights include:
Identity Verification: Confirm legal entity details, jurisdictional registrations, and beneficial ownership.
Transaction Analysis: Spot irregular timing, structured transactions, or sudden dormant account activity.
Blockchain Risks: Review wallet histories, flag privacy tools, and check for sanctioned addresses.
Entity Risk Assessment: Evaluate licensing, AML programs, and on-chain exposure.
Audit Trails & Automation: Maintain detailed records and use real-time tools like Stablerail for pre-sign checks.
Fraud detection requires thorough processes, ongoing monitoring, and the right tools to stay ahead of evolving threats.
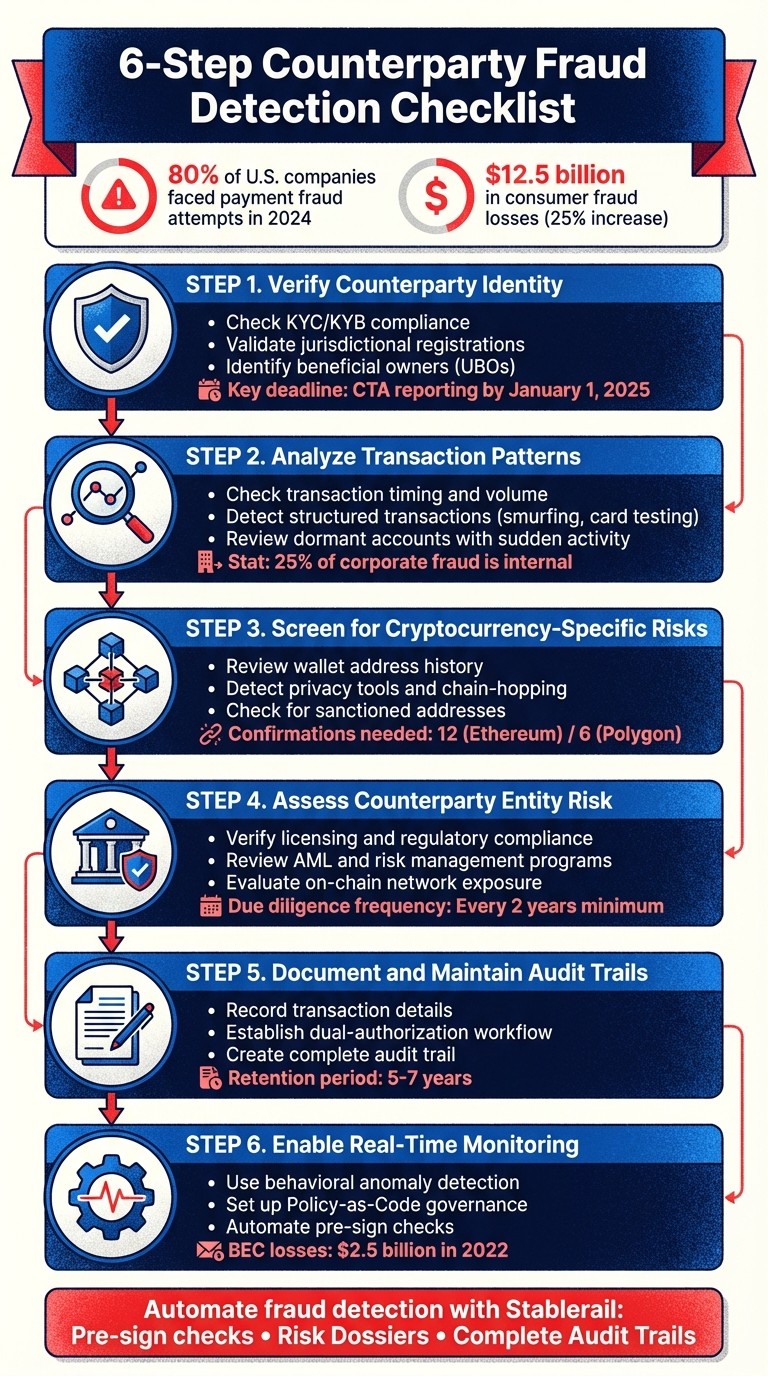
6-Step Counterparty Fraud Detection Checklist for Blockchain Payments
Illegal activities in blockchains and how Chainalysis helps trace them
Step 1: Verify Counterparty Identity
The first step in fraud prevention is confirming the identity of the counterparty. Before any payment is processed, you need solid proof that the counterparty is legitimate - not a shell company, a fraudulent actor, or a front for hidden interests. This step forms the foundation of the fraud detection process, ensuring that all subsequent checks are based on confirmed identities.
Check KYC/KYB Compliance
Proper documentation is key to effective verification. Collect and cross-check details like the legal entity name, registration number, and jurisdiction of incorporation against official records. Self-reported information isn't enough - it must be backed by verifiable documents.
"Answers matter, but documents and verifiable proof matter more." - Rule Ltd
Gather corporate registration documents, certificates of incorporation, and proof of good standing, and confirm their authenticity with official sources. For regulated entities like Virtual Asset Service Providers (VASPs) or banks, request scanned copies of licenses, regulator-issued confirmation letters, and expiration dates. Use regulatory registries, such as FinCEN (U.S.), FCA (U.K.), or MAS (Singapore), to independently verify license numbers and statuses.
It's also essential to ensure that the counterparty's jurisdictional registrations align with their official filings.
Validate Jurisdictional Registrations
Any mismatch between declared and registered information can be a red flag. Confirm that the legal entity signing contracts and issuing invoices is the same as the registered entity. If the counterparty is publicly traded, check whether it’s listed on a recognized exchange within a jurisdiction with strong regulatory oversight.
Dig deeper into the counterparty’s jurisdictional presence - where their headquarters are, where they serve customers, and where their operational teams and servers are located. If they refuse to provide basic evidence or offer inconsistent information, treat this as a high-risk indicator. In such cases, enhanced due diligence or even terminating the relationship may be necessary.
Once jurisdictional details are verified, the next step is to identify who really controls the entity.
Identify Beneficial Owners
Understanding who ultimately controls the entity helps uncover risks like shell companies or hidden agendas. Under the US Corporate Transparency Act (CTA), entities must complete beneficial ownership reporting by January 1, 2025. Similar requirements are being adopted in regions like the EU and Asia-Pacific.
Request an organization chart and a signed ownership declaration that details the percentage held by each Ultimate Beneficial Owner (UBO). Ask whether any owners are linked to trusts, nominees, or layered holding companies, and require explanations for complex ownership structures. Screen UBOs for Politically Exposed Person (PEP) status or government connections that could increase corruption or sanctions risks. Frequent ownership changes within the past 12–24 months or a refusal to provide clear evidence of control should also raise red flags and prompt deeper scrutiny.
Step 2: Analyze Transaction Patterns
Once you’ve verified the identity of your counterparties, the next step is to dive into their transaction behaviors. Fraudsters often leave behind distinct behavioral patterns - irregular timing, inconsistent amounts, or sudden spikes in activity. By closely examining these patterns alongside verified identities, you can uncover hidden fraud risks. According to the 2024 Association for Financial Professionals (AFP) Payments Fraud and Control Survey, 80% of companies reported actual or attempted payments fraud. This makes transaction analysis an essential tool in the fight against fraud.
Check Transaction Timing and Volume
Legitimate counterparties typically follow predictable payment cycles, such as monthly invoices, quarterly settlements, or payroll disbursements. Any deviations - like payments at odd hours, unusual amounts, or unexpected frequency - should raise a red flag. High transaction velocity, where multiple payments occur in rapid succession, might indicate automated bot activity or an account compromise. Bob Stark, Head of Market Strategy at Kyriba, emphasizes:
"Payments are the most popular target for cybercriminals and fraudsters as they represent the most direct way to steal money from an organization".
Geographic anomalies also deserve attention. Transactions originating from unexpected locations could point to risks like Business Email Compromise (BEC), which caused losses exceeding $2.5 billion in 2022.
Analyzing timing and volume is just the start. Looking into how transactions are structured can further expose fraudulent activities.
Detect Structured Transactions
Fraudsters often use techniques like smurfing, where large sums are broken into smaller transactions to avoid detection thresholds. Another common tactic is card testing (or carding), where bots run a high volume of small transactions to validate stolen credit card numbers. If you notice a flood of micro-transactions from a single source, it could indicate fraudulent testing in preparation for a larger attack. Real-time screening tools can help flag these irregularities by comparing payments against established patterns.
But structured transactions aren’t the only risk. Sudden activity in dormant accounts can also signal trouble.
Review Dormant Accounts with Sudden Activity
Dormant accounts that suddenly process high-value transactions should be reviewed immediately. Fraudsters often exploit these accounts as "money mules", using them to transfer illicit funds under the guise of legitimacy. These accounts are also prime targets for account takeovers (ATO), where unauthorized access is gained through phishing or data breaches. Alarmingly, internal fraud accounts for over 25% of all corporate fraud incidents, with employees sometimes using dormant accounts to redirect payments.
When a dormant account becomes active, it’s crucial to re-verify the Ultimate Beneficial Owner (UBO) to ensure the account hasn’t been handed over to a high-risk entity. If the counterparty struggles to explain the sudden spike in activity or provides conflicting responses, enhanced due diligence should be triggered. To minimize risk, regularly review and close unused accounts.
Step 3: Screen for Cryptocurrency-Specific Risks
This step focuses on addressing the distinct risks tied to blockchain payments. Cryptocurrency transactions differ from traditional banking - they're pseudonymous and irreversible, which can make them appealing to fraudsters. While blockchain records all activity, effective risk detection requires targeted expertise.
Review Wallet Address History
Every wallet address leaves a trail of transactions on the blockchain. By analyzing this history, you can trace funds back to centralized exchanges, faucets, or even illicit sources. Key indicators like gas usage, transaction timing, and rapid, small-value transfers (often referred to as "velocity") can point to automated or suspicious activity. On Ethereum Virtual Machine (EVM) networks, transaction data can also reveal interactions with bridges or token swaps, which might suggest laundering attempts. As a rule of thumb, consider payments settled only after 12 confirmations on Ethereum or 6 confirmations on Polygon.
Once the wallet's history is mapped, look for any deliberate obfuscation tactics commonly used by fraudsters.
Detect Privacy Tools and Chain-Hopping
Fraudsters often rely on privacy tools like mixers (also known as tumblers) or privacy-focused cryptocurrencies such as Monero and Zcash to hide the origins of funds. Another common tactic is chain-hopping - moving assets across different blockchains to disrupt audit trails. To flag these activities, examine transaction data for cross-chain bridge calls and decentralized exchange (DEX) swap contracts. Risk intelligence APIs, such as those from TRM Labs or Chainalysis, can significantly boost detection capabilities.
Check for Sanctioned Addresses
Screening wallet addresses against global sanctions databases is crucial. Use risk APIs to cross-check addresses with sanctions lists from bodies like OFAC, the EU, and the UK. Transaction graph analysis can also reveal indirect links to sanctioned entities or high-risk regions, even if the immediate counterparty isn't listed. As highlighted by the Financial Conduct Authority (FCA):
"Wilful blindness in relation to sanctions checks will be considered a 'red flag for complicity' in sanctions offences."
Automate the blocking of flagged transactions by enforcing pre-signature policies, whether due to sanctions violations or heightened risk levels. Since sanctions lists and ownership details can evolve, it’s vital to conduct ongoing screenings - both during onboarding and throughout transactions. For corporate entities, verifying ultimate beneficial owners ensures they aren’t acting as proxies for sanctioned individuals.
Step 4: Assess Counterparty Entity Risk
Once individual identities and transaction patterns are verified, it’s time to dive deeper into the counterparty’s internal operations and compliance practices. A valid wallet history is helpful, but it doesn’t guarantee that the organization has strong safeguards or meets regulatory standards. This step focuses on the counterparty’s overall health - examining licenses, internal controls, and relationships. Together, regulatory compliance, anti-money laundering (AML) measures, and on-chain exposure monitoring create a clearer picture of the risks involved.
Verify Licensing and Regulatory Compliance
Start by confirming that the counterparty holds all necessary licenses for its operations and jurisdiction. For U.S.-based entities, check compliance with regulations like the Bank Secrecy Act (BSA), USA PATRIOT Act, and the Corporate Transparency Act (CTA), which mandates reporting beneficial ownership details to FinCEN. In the EU, verify adherence to the 6th Anti-Money Laundering Directive (6AMLD). If dealing with digital asset counterparties in Singapore, ensure they comply with the Payment Services Act (PSA) for Virtual Asset Service Providers (VASPs).
Request key documents, such as proof of good standing from the jurisdiction of incorporation, the legal entity name, and registration number. Additional documentation like corporate registrations, insurance summaries, and audited financial statements can provide more insight. For data security, look for third-party certifications, such as SOC 2 Type II or ISO 27001, which demonstrate adherence to industry-standard security controls.
Review AML and Risk Management Programs
After confirming licensing, evaluate the strength of the counterparty's AML and risk management frameworks. Effective AML programs typically include frequent sanctions screenings, risk-based Customer Due Diligence (CDD), and transaction monitoring that spans both fiat and crypto transactions. On the other hand, weaker programs might only screen at onboarding, fail to collect proper government documentation for Know Your Customer (KYC) processes, or use inadequate monitoring tools that don’t cover all supported assets. TRM Labs emphasizes:
"A VASP with weak or poorly enforced AML and KYC controls may become a conduit for illicit finance like money laundering, terrorist financing, sanctions evasion, or other such fraudulent transactions."
Request AML policy documents, training records for compliance staff, and summaries of their screening methods. Confirm that the counterparty undergoes regular third-party audits and investigate any history of failed regulatory reviews or penalties. Senior management must actively support compliance efforts - high-risk relationships should require approval from senior officers. For correspondent banking relationships, ensure that ongoing due diligence is conducted at least every two years.
Evaluate On-Chain Network Exposure
Analyze the counterparty’s transaction patterns to identify connections to high-risk entities. Use transaction graph analysis to trace fund flows and pinpoint wallet clusters. Pay attention to transaction volumes - both incoming and outgoing - categorized by risk factors like sanctions, terrorist financing, or darknet activity. Compare the counterparty’s risk profile to other VASPs and high-risk exchanges to determine if they stand out as an anomaly.
Be on the lookout for nesting arrangements, where the counterparty allows other financial institutions to operate through its system, potentially obscuring the true source of funds. It’s also essential to verify the locations of the counterparty’s servers and decision-makers - operating in jurisdictions with weak enforcement could signal regulatory arbitrage. By combining on-chain data with behavioral insights, you can generate a real-time risk score for each transaction.
Step 5: Document and Maintain Audit Trails
Once you've assessed counterparty risks, thorough documentation becomes essential. It’s not just about meeting compliance standards - it’s about protecting your organization. Without a complete audit trail, even legitimate transactions can raise red flags during audits or regulatory reviews. The objective here is to maintain a clear, verifiable record that ties every action to a specific individual, timestamp, and supporting evidence.
Record Transaction Details
For every counterparty interaction, log all critical details. This includes the full legal entity name, registration number, jurisdiction of incorporation, and information on all beneficial owners (usually those with more than 25% ownership). For each transaction, record specifics such as value, volume, timing, ID or hash, currency, and the purpose of the payment. When dealing with electronic payments that limit end-customer data, document the "flow of funds" model and note historical ACH return rates. Additionally, track risk classifications - whether the transaction is high, medium, or low risk - and document the patterns that led to these evaluations. These detailed records not only support decision-making but also provide solid evidence for audits or inquiries.
Establish an Approval Workflow
Implement a dual-authorization system where two separate individuals must approve any money movement, such as ACH transfers, wires, or remote deposits. To strengthen security, ensure that initiators and approvers operate from different workstations to reduce the risk of unauthorized access. If an exception to policy is necessary, clearly document the reason for the exception and the individual who approved it. For high-risk relationships, require approval from a senior officer and document the arrangement in writing within 20 business days. Additionally, high-risk relationships should undergo due diligence assessments at least every two years, with the findings documented within 10 business days. This structured workflow ensures accountability and minimizes risks.
Create a Complete Audit Trail
Maintain an exhaustive electronic log that tracks every step, from the initial request to the final transmission. This includes screening results, risk assessments, SAR (Suspicious Activity Report) triggers, investigation summaries, officer approvals, and resolutions of red flags. Each action must be time-stamped and tied to a specific decision-maker. As RuleLtd puts it:
"A checklist becomes real diligence when you ask for proof. You do not need a massive file dump. You need the right documents that confirm identity, ownership, and controls."
To further demonstrate compliance, keep data access logs and records of encryption status. Retain all compliance-related documentation, including transaction logs and SAR decisions, for the legally required period - typically 5-7 years, depending on jurisdiction. Lastly, conduct independent testing of your compliance programs every 12-18 months to ensure adherence to BSA/AML (Bank Secrecy Act/Anti-Money Laundering) responsibilities. A well-maintained audit trail not only supports compliance but also builds trust and transparency.
Step 6: Enable Real-Time Monitoring and Automation
Manual checks simply can’t keep up with the speed of on-chain transactions. Any delay in flagging suspicious activity could render potential warnings useless. That’s where real-time monitoring and automation come in - helping you identify and address risks before a transaction is signed and broadcast.
Use Behavioral Anomaly Detection
Behavioral anomaly detection goes beyond static controls like spending limits, identifying unusual activities that might otherwise slip through. For example, instead of just blocking transactions over $10,000, these systems flag unusual patterns in timing, volume, or geographic location. Imagine spotting a $15,000 invoice submitted at 2:00 AM from an unfamiliar IP address - this would immediately raise a red flag.
This type of detection is particularly effective against Business Email Compromise (BEC) scams. These scams, where fraudsters impersonate executives to request urgent and "confidential" payments, caused more than $2.5 billion in losses in 2022 alone. By comparing payments against predefined scenarios, behavioral systems can instantly halt suspicious transactions for manual review.
Set Up Policy-as-Code Governance
Building on real-time detection, Policy-as-Code ensures that every transaction follows established rules automatically. This approach translates approval policies into enforceable logic. For instance, you could set rules like "weekend transfers over $10,000 require additional approval" or "payments to new addresses over $5,000 need CFO approval and verification." The system automatically blocks any transaction that violates these rules.
Policy-as-Code also ensures strict dual authorization for outbound payments, requiring at least two individuals to initiate and approve a transaction. This eliminates exploitable loopholes like "exceptions to policy" and creates a complete electronic paper trail. Every action is logged, leaving no room for unauthorized payments to go unnoticed.
Automate Pre-Sign Checks with Stablerail

To add another layer of security, Stablerail performs mandatory checks before signing a transaction. Positioned between custody and signing, Stablerail uses specialized agents to enforce policies, screen for sanctions, detect anomalies, and assess counterparty risk. It generates a Risk Dossier with a clear verdict - PASS, FLAG, or BLOCK - backed by evidence.
Here’s how it works: You create an intent (such as an invoice PDF, payout CSV, or API request). Stablerail’s agents then run the necessary checks and produce the Risk Dossier. Approvers can review, approve, or override the decision (with a documented reason), and the final signing happens via MPC. Every step - intent creation, checks, approvals, overrides, and signing - is logged, creating a full audit trail that satisfies auditors, boards, and regulators.
This "copilot, not autopilot" approach keeps humans in control of critical decisions while automating repetitive and error-prone tasks. Together, real-time monitoring and pre-sign automation form a robust defense against fraud, ensuring every transaction is thoroughly vetted before it’s finalized.
Conclusion
Counterparty fraud is constantly adapting, with criminals now using AI-generated documents and deepfakes to exploit vulnerabilities in payment systems. Industry trends show that the risks of fraud are growing, affecting both traditional and digital asset transactions. This checklist, when paired with effective monitoring tools, shifts the approach from reacting to fraud after it happens to actively preventing it.
By implementing standardized processes for identity verification, transaction analysis, and screening, this checklist strengthens every step in the payment process, closing the gaps that fraudsters often exploit. As Bob Stark, Head of Market Strategy at Kyriba, explains:
"Thieves are profiling the payment processes of finance and treasury to find inconsistent controls and exploitable weaknesses".
Structured workflows that eliminate "exceptions to policy" make it harder for criminals to find and exploit weak points.
Of course, a checklist is only as good as the systems that enforce it. Real-time monitoring and automation are key to ensuring that every payment is thoroughly screened before approval, rather than catching issues after damage has been done. Tools like Stablerail operate at a critical point - between custody and signing - conducting pre-sign checks such as sanctions screening, policy enforcement, anomaly detection, and counterparty risk scoring. These checks generate a Risk Dossier with clear outcomes (PASS, FLAG, or BLOCK), all supported by evidence. Every step is logged, providing a comprehensive audit trail that meets the needs of auditors, boards, and regulators.
Stablerail's approach - acting as a "copilot" rather than an "autopilot" - balances automation with human oversight, reducing manual errors while keeping finance teams in control. This is especially important for stablecoin transactions, which require governance that keeps up with on-chain speed without compromising on thoroughness.
Fraud detection isn’t a one-time task; it demands evidence-based practices, clear escalation protocols, and regular updates to due diligence processes. With the right tools and a well-designed checklist, finance teams can transform counterparty risk management from a reactive effort into a proactive, fortified defense.
FAQs
What are the biggest red flags that a counterparty is fraudulent?
Fraudulent counterparties often reveal themselves through inconsistent or unverifiable information, unusual behaviors, and a failure to meet key compliance standards like sanctions screening or anti-money laundering protocols. Be especially alert for red flags such as mismatched documentation, transactions occurring at odd times, or irregular payout patterns. These signs can indicate deeper issues that warrant further investigation.
How can we verify a crypto wallet address belongs to the right counterparty?
To confirm that a crypto wallet address belongs to the right counterparty, rely on pre-sign checks like behavioral anomaly detection, counterparty risk scoring, and sanctions screening. These methods evaluate factors such as identity, transaction history, and behavior patterns. When paired with governance frameworks, these tools help verify that the wallet address aligns with the intended counterparty and complies with all policy requirements before a transaction is approved.
What should we automate before signing an on-chain payment?
Before approving an on-chain payment, it’s essential to automate critical verification steps to ensure compliance and spot potential fraud. These steps include sanctions screening, taint and exposure analysis, policy enforcement, behavioral anomaly detection (such as unusual transaction amounts or irregular timing), and counterparty risk scoring.
To make the process clearer, generate plain-English explanations that include supporting evidence, like policy references and timestamps. Think of these checks as a "copilot" that reviews and validates risks and policies, helping you make informed decisions before giving the green light.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


