
Manual payment processes can't keep up with the speed and risks of stablecoin transactions. Errors in invoices, delays, and inefficiencies cost companies up to 10% of their monthly revenue. Meanwhile, blockchain payments settle instantly and are irreversible, requiring smarter controls to prevent fraud and mistakes.
Behavioral anomaly detection addresses these challenges by analyzing transaction patterns in real time - flagging unusual behaviors like spending spikes, geographic shifts, or abrupt counterparty changes before payments are executed. Advanced models such as GANs and VAEs improve accuracy, detecting subtle irregularities that traditional methods miss.
Key takeaways:
Stablecoin risks: Instant, irreversible transactions demand sanctions screening.
Behavioral monitoring: Tracks deviations in amounts, timing, and counterparties.
AI-driven models: Use machine learning to detect fraud with high precision.
Operational improvements: Reduces manual intervention by up to 95%.
Compliance support: Creates audit trails to meet regulatory standards. (See our stablecoin compliance checklist for more details.)
Anomaly detection is reshaping how finance teams manage payments, combining speed with safeguards to minimize risks and streamline operations.
3.2 AI for Fraud & Anomaly Detection
What Is Behavioral Anomaly Detection in Payments
Behavioral anomaly detection works by understanding what "normal" looks like in your transaction patterns and flagging anything that seems off. These systems analyze your typical transaction behaviors - such as amounts, timing, counterparties, and frequency - and identify deviations.
This method is a major departure from traditional fraud detection techniques. Older approaches rely heavily on manual reviews, signature matches, and static thresholds, which often fail to catch sophisticated or evolving threats. Researchers at the University of Michigan highlight this limitation:
"Traditional anti-money laundering (AML) and anti-fraud measures often rely on fixed rules and manual reviews. Although they can detect abnormal behaviors to some extent, these traditional methods face significant limitations in identifying high complexity and diverse fraudulent activities."
Behavioral anomaly detection flips the script. It uses deep generative models like Generative Adversarial Networks (GANs) and Variational Autoencoders (VAEs) to detect subtle irregularities in transaction patterns - without needing explicit labels. For instance, a combined GAN-VAE model achieved an F1-score of 0.795 in identifying suspicious transactions, outperforming standalone GAN (0.720) and VAE (0.740) models. This dynamic approach provides a more nuanced way to combat fraud.
How Behavioral Anomaly Detection Works
At its core, this method relies on baseline profiling. It examines historical transaction data to establish what’s typical for each account, including amounts, timing, counterparties, and frequency.
Advanced systems take this a step further by modeling payment flows as graphs. These graphs capture relationships and interactions between accounts, enabling the system to detect not only individual anomalies but also suspicious patterns across multiple accounts. For example, if funds move through an unusual chain of wallets or a dormant account suddenly makes high-value transfers, the system flags it.
Detection accuracy varies depending on the complexity of transactions. Research shows these models excel at identifying normal transactions (with an F1-score of 0.92), though their accuracy is slightly lower for fraudulent patterns (0.88) and complex money laundering schemes (0.85). Data sparsity also plays a role - when data is limited, F1-scores can drop from 0.92 to 0.75.
Common Behavioral Signals That Indicate Anomalies
Behavioral detection systems monitor multiple factors at once, including spending velocity, unusual timing, significant amount deviations, geographic shifts, and sudden changes in counterparties.
Amount irregularities: Transactions that deviate significantly from historical patterns raise red flags. For instance, if your typical vendor payments range from $500 to $2,000, a sudden $25,000 payment to the same vendor would trigger scrutiny.
Counterparty behavior: Changes in who you’re paying or receiving funds from are just as telling. Systems track account relationships and look for sudden shifts. Repeated transaction failures - especially in rapid succession - can signal brute-force attacks or testing before a larger fraudulent transfer.
These signals demonstrate why real-time detection is critical, especially for stablecoin operations.
Why Stablecoin Payment Flows Need Anomaly Detection
Stablecoins settle transactions instantly and irreversibly, making real-time, pre-execution oversight essential. As Malgo Technologies explains:
"The system does not solely use the concept of static blocklists or signature matching; instead, it uses dynamic risk scoring to all transactions."
The scale of stablecoin transactions further underscores the need for automation. For example, x402 protocol transactions are projected to grow by 10,780% in October 2025 due to increasing enterprise demand for AI-integrated payment systems.
Behavioral anomaly detection enables real-time transaction evaluations based on policy graphs, assessing identity, transaction patterns, and business rules before funds are transferred. AI-powered platforms can reduce manual intervention in payment governance by up to 95% and cut compliance efforts by 80%. For high-volume stablecoin operations, this proactive approach is no longer optional - it’s a necessity.
Research Findings: Anomaly Detection in Financial Systems
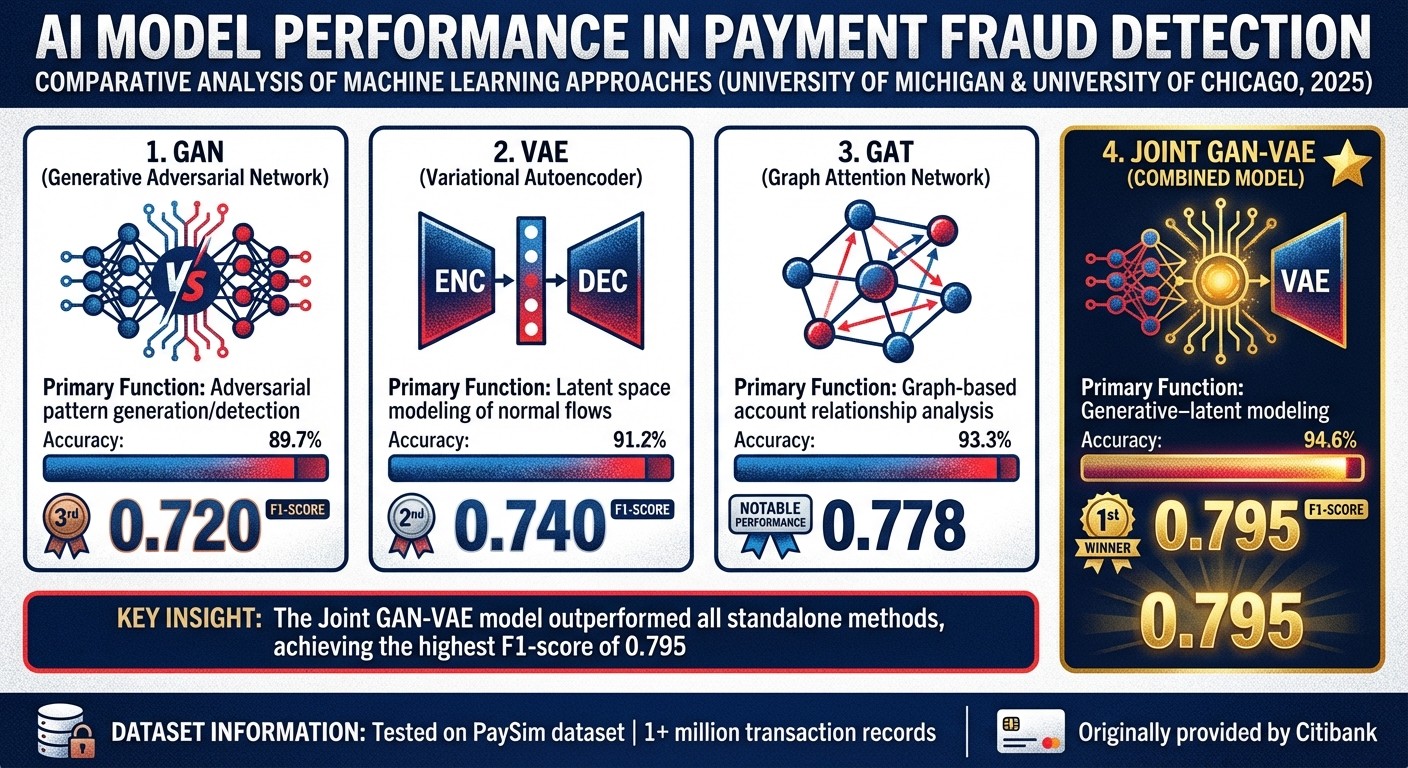
AI Anomaly Detection Model Performance Comparison for Payment Fraud Detection
Financial institutions have been leveraging machine learning to detect fraudulent activities, and recent research suggests these techniques could also improve governance in stablecoin payments.
Anomaly Detection Models Used in Traditional Finance
The most effective fraud detection systems rely on a mix of advanced approaches. Generative Adversarial Networks (GANs), for example, create synthetic transaction data to identify subtle irregularities in patterns. Similarly, Variational Autoencoders (VAEs) simplify transaction data into core representations and then measure how far actual transactions deviate from these learned norms.
Graph Neural Networks (GNNs) and Graph Attention Networks (GATs) take a different approach by treating financial data as a network, where accounts are nodes and transactions are edges. This allows them to uncover complex relationships that traditional linear models might miss. Meanwhile, Bidirectional Transformers excel at analyzing the sequence and timing of transactions, capturing patterns that develop over extended periods.
In a 2025 study conducted by researchers from the University of Michigan and the University of Chicago, a Joint GAN-VAE model outperformed standalone methods. Using the PaySim dataset - comprising over one million transaction records originally provided by Citibank - the combined model achieved an impressive F1-score of 0.795 for detecting suspicious activities. For comparison, GANs alone scored 0.720, and VAEs scored 0.740. Tengda Tang, the study's lead researcher, highlighted:
"The joint model... combines the strengths of both GAN and VAE. It optimizes the generative capacity of the generator and the latent space modeling of the encoder, achieving the best performance across all metrics."
Despite these advancements, incorporating these models into live systems presents unique challenges.
Implementation Challenges
Even the most advanced models face hurdles when applied to real-world scenarios. One major issue is data sparsity - fraudulent transactions are rare, providing limited examples for models to learn from. Additionally, the complexity of financial data, which includes variables like account details, transaction amounts, timestamps, payment methods, and geographic locations, requires systems capable of fusing this data while maintaining speed.
Another challenge lies in the black box nature of deep learning models. Regulators and auditors often demand clear explanations for flagged transactions, but many machine learning models struggle to provide transparent reasoning.
Real-time processing adds further complexity. High-frequency transaction flows demand systems that are not only accurate but also computationally efficient. These challenges underscore the need for tailored solutions, particularly in stablecoin governance, where instant settlements and irreversibility amplify the stakes.
Applying Research Insights to Stablecoin Governance
Stablecoin operations, with their immediate settlement times and irreversible transactions, require robust pre-execution screening. Insights from traditional finance can be adapted here by modeling blockchain ledgers as graphs, where wallets are nodes and transfers are edges. This enables GATs to track fund flows across wallets and flag suspicious patterns before transactions are finalized.
Policy-as-Code systems take these insights a step further by automating responses. Anomaly detection can trigger actions like requiring additional approvals or temporarily freezing transfers using MPC wallets acting as co-signers. These systems evaluate transactions in real time, checking against identity verifications, velocity limits, and behavioral baselines to block suspicious activity before funds are moved.
The rapid adoption of stablecoins has made such automation indispensable. In October 2025, transactions using the x402 protocol - a standard for AI-driven stablecoin payments - skyrocketed by 10,780%. AI-powered platforms have shown they can cut manual intervention by up to 95% and reduce compliance efforts by 80%. For finance teams managing high transaction volumes, these research-backed models have transitioned from experimental ideas to operational necessities.
How Anomaly Detection Improves Payment Governance
Anomaly detection transforms payment governance by shifting the focus from fixing issues after transactions occur to controlling them before they happen. This approach empowers finance teams to enforce rules, minimize errors, and ensure compliance - all before any funds are transferred. This is especially important given the irreversible nature of blockchain payments.
Enforcing Policies Before Transactions Execute
In September 2025, AP2 Protocol demonstrated this capability by applying a Policy Evaluation Graph to a $749.00 USDC Payment Intent (ID: ap2_pi_7f0cf3). The system evaluated the payment against specific rules, such as a maximum single payment limit of $1,000 and jurisdictional allowlists for the US and Canada. Only after passing these checks did the payment status change from pending to authorized.
These graphs handle a range of critical tasks: verifying identities through sanctions screening and KYC processes, analyzing transaction patterns like spending velocity, and enforcing jurisdictional rules. If a transaction violates any policy, it is automatically rejected with error codes like POLICY_THRESHOLD_EXCEEDED or JURISDICTION_BLOCKED. AI-powered tools further enhance security by assigning dynamic risk scores based on patterns like rapid transaction bursts or geographic inconsistencies.
By November 2025, Utila had implemented an "AML Policy Engine Flow" for stablecoin platforms. This system integrates tools like Chainalysis or TRM Labs to enforce rules automatically. For example, it can freeze incoming deposits if a counterparty's live risk score exceeds a set threshold, with all screening events logged in tamper-proof records. Programmable authorization adds another layer of governance, requiring human approval for high-value transactions, such as those exceeding $5,000 USDC.
This proactive enforcement not only safeguards transactions but also helps reduce broader operational risks.
Reducing Operational Risk
Manual payment processing can be a significant drain on resources, but anomaly detection systems address this by identifying and mitigating risks early. These systems flag suspicious patterns like burst transactions (multiple rapid attempts often linked to automated attacks), unusual spending velocity, and repeated failures that might indicate compromised keys. Catching these issues early prevents fraud and streamlines payment operations.
Geographic inconsistencies and abnormal routing paths are also detected, reducing the chances of misdirected payments. Real-time screening further enhances security by freezing funds tied to flagged addresses or high-risk jurisdictions before settlement.
Beyond fraud prevention, these systems catch human errors, such as discrepancies between invoice data and payment amounts. They also monitor stablecoin peg strength to spot early signs of de-pegging and analyze cross-chain liquidity levels to avoid failed transfers or excessive slippage. This efficiency allows 56% of accounts payable teams, who previously spent over 10 hours a week on manual invoice and supplier payment tasks, to focus on more strategic activities.
By reducing errors and ensuring strict pre-transaction controls, anomaly detection systems also enhance auditability and compliance.
Creating Audit Trails and Supporting Compliance
Anomaly detection doesn’t stop at enforcing rules - it also creates robust audit trails that confirm every Payment Intent has been thoroughly evaluated. Modern systems use "Policy Traces" to document why a transaction was approved or denied, recording rule IDs, outcomes, and messages for each decision. This level of transparency is invaluable for auditors verifying that governance controls are functioning as intended.
Between February 2022 and mid-2023, the Italian bank Intesa Sanpaolo employed the WeirdFlows anomaly detection pipeline to monitor 80 million cross-border transactions. This project, led by researchers like Arthur Capozzi and Salvatore Vilella, uncovered complex patterns used to bypass EU economic sanctions. The system flagged a 66.5% increase in transaction flow weight through certain intermediary countries and successfully identified malicious activities tied to a specific bank identifier.
Settlement proofs further link transactions to their Payment Intents and policy evaluations, while on-chain recording ensures a transparent and traceable history. This allows businesses, regulators, and users to verify payment flows in real time. By integrating AI into compliance processes, stablecoin platforms can cut manual compliance efforts by up to 80% while improving accuracy.
Stablerail: Governance Solutions Based on Research Principles
Stablerail provides a governance solution for corporate stablecoin payments that combines speed with robust control. By operating above custody and before any transactions are signed, it enables finance teams to enforce governance standards comparable to those of traditional banks - without compromising blockchain efficiency. Importantly, Stablerail never assumes unilateral signing authority, ensuring companies retain complete control over their wallets.
How Stablerail Detects Behavioral Anomalies
Stablerail takes its security a step further with advanced behavioral anomaly detection. Before any transaction is executed, the system performs real-time pre-sign checks to identify unusual patterns. These checks analyze factors like timing, transaction amounts compared to usual baselines, and payout patterns. By flagging anomalies, the system helps identify potential fraud, errors, or policy violations.
With sub-second response times, the platform evaluates details such as time-of-day activity, spending velocity, and geographic irregularities before funds are moved. It also incorporates additional safeguards, such as sanctions screening, taint exposure analysis, and counterparty risk scoring. What sets Stablerail apart is its plain-English narrative explanations, which clarify why a transaction is flagged. These explanations point directly to evidence, policy clauses, and timestamps, supporting a "copilot, not autopilot" philosophy that keeps finance teams fully informed.
Policy-As-Code for Streamlined Governance
Stablerail enables teams to automate governance through machine-executable policies. For example, a company could set rules requiring CFO approval for payments to new addresses exceeding $5,000 or extra checks for weekend transfers over $10,000. These policies are managed through configurable evaluation graphs that align with a company’s risk tolerance and compliance needs.
The platform's Policy Console makes it easy to define roles, limits, and approval workflows. Policies can even integrate live risk scores from blockchain intelligence providers, automatically halting or rejecting transactions when counterparties exceed risk thresholds. Finance teams can further refine these thresholds by using a stablecoin risk calculator to evaluate specific asset profiles. By embedding signing logic into automated workflows, Stablerail streamlines routine transfers while reserving human intervention for high-risk scenarios. This approach significantly reduces the manual burden of compliance.
Human Oversight and Comprehensive Audit Trails
While automation handles most governance tasks, Stablerail ensures human oversight for flagged high-risk transactions. When a transaction is flagged by a Risk Dossier, designated approvers review the details and either validate or override the automated decision. Every action is meticulously logged in a tamper-evident audit trail, which links transactions back to their original intent using cryptographic Settlement Proofs.
These logs also include Policy Traces, which document the rules evaluated, the outcomes, and the reasoning behind specific decisions. This level of transparency eliminates the need for traditional tools like spreadsheets and Slack threads, consolidating all compliance records into a single, secure system. By doing so, Stablerail simplifies governance while meeting stringent compliance standards.
Conclusion
Behavioral anomaly detection shifts away from rigid rules, relying instead on dynamic systems that adapt to each organization's unique patterns. Instead of using static dollar thresholds that often trigger unnecessary alerts, modern platforms analyze statistical baselines - like medians, means, and standard deviations - to identify genuine irregularities in transaction volume, frequency, and timing. The results speak for themselves: organizations that replaced fragmented monitoring with unified anomaly detection systems reported a 93% reduction in false positive alerts.
Pairing automation with human oversight further strengthens decision-making. These systems operate at lightning speed, catching anomalies such as sudden bursts of activity or velocity spikes before transactions are executed on-chain. This rapid detection allows human approvers to evaluate flagged high-risk transactions, a critical capability as regulatory pressures and operational risks continue to grow.
In this landscape, stablecoin treasury operations demand robust governance frameworks. With regulations like the GENIUS Act enforcing strict anti-money laundering (AML) standards and the global stablecoin market projected to surpass $210 billion by the end of 2024, manual processes like spreadsheets are no longer sufficient. As Tom Armstrong, Head of Compliance Advisory at TRM Labs, emphasized:
"The GENIUS Act makes clear that technical compliance with regulations is not the bar - it's effectiveness. You have to show your program works".
Comprehensive audit trails further enhance compliance and internal controls. These logs document policy reviews, flagged anomalies, and approval decisions, equipping finance teams with the evidence needed to justify their actions to auditors and boards. By embedding policy enforcement directly into transaction workflows, organizations can reduce operational risks while preserving the speed that makes stablecoins so valuable in corporate treasury operations.
At its core, anomaly detection enables smarter, faster decision-making. Companies that leverage statistical thresholds, integrate real-time blockchain data, and maintain version control over their risk models are better positioned to scale compliance efforts proactively. In a business environment where 55% of firms lose 4-5% of monthly revenue due to inefficiencies in payment processes, combining automated governance with human expertise isn't just about meeting regulatory requirements - it’s a strategic edge.
FAQs
What makes anomaly detection different from traditional fraud detection?
Anomaly detection works by understanding what "normal" behavior looks like and flagging anything that deviates from it in real-time. Using machine learning, it examines transaction patterns - like the time they occur, the amounts involved, and payout trends. This approach allows it to spot irregularities, even in scenarios where fraud is exceptionally rare.
In contrast, traditional fraud detection relies on fixed rules, blacklists, and thresholds based on known fraud schemes. While these methods can effectively catch familiar tactics, they often fall short when faced with new or unexpected behaviors. This is especially true in fast-changing environments like crypto-asset payments. Anomaly detection, however, evolves alongside the data, making it a more dynamic tool for identifying subtle and emerging risks.
Why is real-time behavioral monitoring important for stablecoin payments?
Real-time behavioral monitoring plays a key role in spotting unusual patterns in stablecoin transactions. These patterns might include unexpected transaction amounts, irregular timing, or interactions with unfamiliar counterparties. Catching these anomalies as they happen helps stop fraud, cyberattacks, and compliance breaches before the transactions are completed.
This kind of monitoring boosts payment oversight by safeguarding system integrity and ensuring adherence to regulations. It allows finance teams to manage on-chain payments with the same level of precision and control as they would in traditional banking.
How do AI models contribute to improving payment governance?
Currently, there’s no indication that specific AI models like GANs (generative adversarial networks) or VAEs (variational autoencoders) play a direct role in payment governance or detecting irregularities in stablecoins. That said, machine learning frameworks are making strides in improving real-time anomaly detection for high-value payment systems. These systems assist in spotting unusual patterns, enforcing rules, and minimizing errors in payment processes. While generative AI tools are being studied for their potential in cash management, there’s no explicit mention of GANs or VAEs being applied in this area.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


