
Stablecoin transfers carry risks like fraud, regulatory violations, and security vulnerabilities. Following treasury management best practices and using policies can help prevent these risks by analyzing transactions before they’re signed. Key safeguards include:
Blocking payments to flagged or suspicious addresses.
Setting transaction limits based on value, frequency, or destination.
Automating compliance checks for sanctions, AML, and other regulations.
Using policy-as-code to enforce rules consistently and efficiently.
How Circuit Makes Crypto Insurance Affordable | Harry Donnelly | Stablecoin Conference LATAM 2025
Building a Policy Framework for Stablecoin Transfers
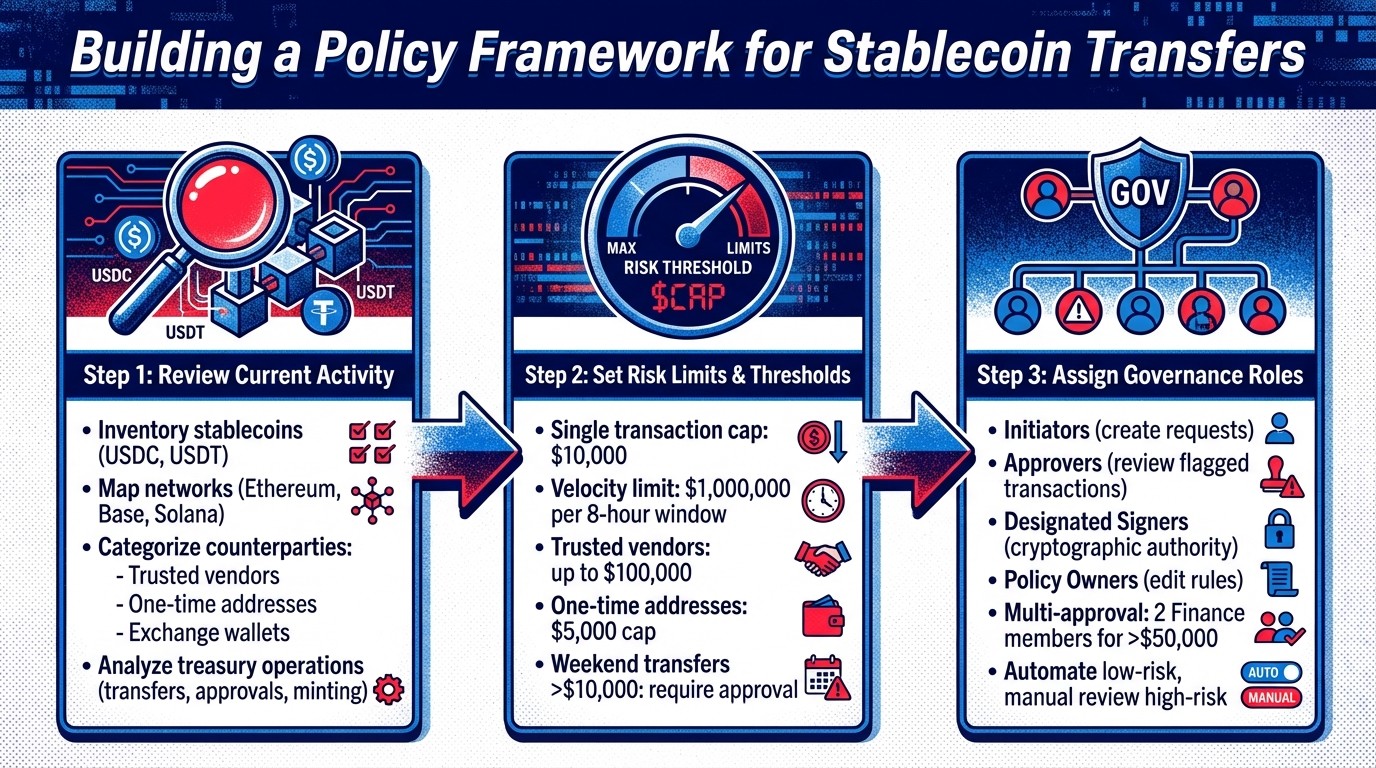
3-Step Framework for Building Stablecoin Transfer Policy Controls
A policy framework transforms your organization's risk tolerance into actionable rules that screen transactions automatically. The idea is to block risky transfers upfront while flagging unusual activity for further review by the appropriate team members.
Review Your Current Stablecoin Activity
Start by taking stock of your stablecoins, such as USDC and USDT, the networks you operate on (like Ethereum, Base, and Solana), and the counterparties you interact with. Look at your recent transaction history and group counterparties into categories: trusted vendors you work with regularly, one-time addresses for new suppliers, and exchange wallets used for managing liquidity. This process highlights areas where your exposure is highest and where tighter controls might be needed.
Don’t stop at simple transfers. Consider other treasury operations, such as using smart contracts for yield, setting token spending limits on decentralized exchanges, or minting assets. Each type of operation - whether it's transferring, approving, or minting tokens - comes with its own risks and should have separate rules. Also, make sure to adjust token units as needed. These steps lay the groundwork for setting up targeted risk controls.
Set Risk Limits and Transaction Thresholds
Once you’ve reviewed your assets and activities, define clear risk limits. For example, you could set a single-transaction cap at $10,000 and introduce a velocity limit to block transactions if total transfers exceed $1,000,000 within an 8-hour rolling window. Velocity limits are especially useful for stopping draining attacks, where multiple small transfers might bypass single-transaction caps but still pose a significant threat to your treasury.
You can also apply thresholds based on the destination of funds. For trusted vendors, allow transactions up to $100,000. However, for one-time addresses, cap transfers at $5,000 and require CFO approval for anything larger. To monitor unusual activity, implement time-sensitive rules, such as requiring additional approval for transfers over $10,000 on weekends, when business operations are less active.
Assign Governance Roles and Control Objectives
With your risk limits in place, assign roles to enforce these policies effectively. Each rule should have a clear purpose - whether it’s to prevent sanctions violations, control unauthorized spending, or ensure compliance during audits. Establish multiple layers of approval to separate duties. For instance, require two Finance team members to approve any transfer over $50,000 before it can proceed.
Divide responsibilities into tiers: Initiators (who create payment requests), Approvers (who review flagged transactions), Designated Signers (who have cryptographic authority), and Policy Owners (who can edit the rules). Limit the ability to modify policies to a small group of senior leaders, such as the CFO, Controller, or Head of Treasury. This prevents unauthorized changes to critical risk limits.
For trusted, low-risk transactions - such as routine payments to whitelisted addresses - allow automated approvals to keep operations efficient. Reserve manual oversight for high-value transfers or one-time addresses, where the stakes are higher, and additional scrutiny is worth the extra time. This layered governance model ensures your policies remain scalable without creating unnecessary bottlenecks in day-to-day operations.
Implementing Policy-as-Code to Block Risky Transfers
Turn your written policies into machine-readable rules that analyze every payment intent before signing. This eliminates the need for manual reviews and ensures that every transaction is evaluated consistently. Once implemented, this method allows for precise rule and workflow configurations.
Configure Core Policy Rules
Start by using your risk framework to define the structure of each rule. Each rule typically consists of three key components: an Action (like ALLOW, BLOCK, or escalate), an Asset (such as a specific stablecoin), and Source/Destination parameters that specify where funds can flow. For example, you could configure a rule to block transfers exceeding a specific amount when sent to one-time-use addresses, while permitting higher limits for transactions involving trusted counterparties.
To maintain consistent risk management, set limits in USD. Arrange rules from the most specific (e.g., high-risk transfers) to the most general (e.g., transactions with trusted entities). You can also apply velocity limits by setting cumulative thresholds over a specific time period. For instance, you might block an account if it attempts to send more than $15,000 in total within a 12-hour window, even if each individual transaction stays within the single-transaction limit.
Add Pre-Sign Transaction Checks
Once your rules are in place, integrate them into pre-sign checks to catch risky transactions before they’re signed. Automate screening for sanctions, illicit activities, and unusual behavior using real-time assessments, with a default setting where DENY overrides ALLOW.
For smart contract transactions, use ABI decoding to confirm that function calls and parameters (like the transfer value) comply with your policy limits. Additionally, establish risk-based outcomes that align with your governance model. Severe risks can trigger automatic rejections, while moderate risks might require further human review. To add another layer of protection, implement netUSDChange criteria to calculate the total dollar value of all assets involved in a transaction. This can help minimize losses from compromised wallets.
Set Up Escalation and Approval Workflows
For high-risk or unfamiliar transactions, create multi-step workflows that pause the transaction until it receives the necessary approvals. Designate approval groups with multiple sign-offs and ensure the initiator cannot approve their own transaction. Use AND/OR logic to combine approval conditions based on the level of risk, and enforce a "four-eyes" principle, which ensures that no single person has complete control over a transaction. As highlighted in AP2 Documentation:
"Policies can require human approval above certain thresholds, during disputes, or whenever a counterparty has a low reputation score. Approvals happen through signed delegation records so the transaction remains machine-readable."
AP2 Documentation
Set up instant notifications for flagged transactions while automating approvals for low-risk ones to streamline the process.
Monitoring and Maintaining Policy Controls
Make sure your policy-as-code setup effectively blocks risky transactions while ensuring legitimate payments are processed without delays. These strategies connect your policy enforcement with ongoing risk management, creating smoother operational oversight.
Optimize Transaction Workflows
Pinpoint where manual processes might be slowing down transactions. For instance, if your CFO frequently reviews low-value transfers because of overly strict thresholds, it’s time to revise those rules. Focus manual reviews on high-risk payments instead. Use tiered approval workflows to streamline the process: routine transfers from trusted vendors can be auto-approved through a self-custodial stablecoin treasury, while higher-risk payments - like those going to new addresses - should require multi-person sign-offs. Structure your rules to prioritize efficiency, starting with the most specific (e.g., allowlisted addresses) and working towards general rules. This approach reduces unnecessary checks and speeds up repeat payments.
Track Policy Performance and Risk Signals
Streamlining workflows is just one part of the equation; keeping tabs on how well your rules perform is equally important. Use a centralized dashboard to monitor which rules are triggered most often. Real-time insights, captured through webhooks or dedicated endpoints, allow you to track every transaction step - authorization, policy evaluation, approval, and settlement. For example, if a single rule generates numerous POLICY_THRESHOLD_EXCEEDED errors, it might be too restrictive and require adjustment.
Maintain a detailed policy trace for every payment intent, recording the Rule ID, decision outcome (ALLOW or DENY), and supporting evidence. Export key metrics - like intent counts, failure rates, and escrow balances - to external monitoring tools or SIEM platforms. This allows your security team to spot patterns early and address potential issues before they escalate.
Maintain a Complete Audit Trail
Clear, retrievable records of all transaction decisions are essential for regulatory and audit purposes. Store an append-only log of every intent, policy decision, and approval action, including timestamps, approver identities, and the rule version in effect at the time. Christopher Grilhault des Fontaines, CEO of Dfns, emphasizes:
"A comprehensive security model must address... tamperproof audit trails, and robust authentication and authorization frameworks"
Cryptographic proofs can link on-chain transactions to policy evaluations. For cases requiring human intervention - like a CFO override on a flagged payment - record the approval as a signed delegation to keep the workflow machine-readable. Tagging rules with metadata (e.g., ticket IDs, rule owners, and severity levels) makes it easier to trace blocked transactions back to their source business requirements. A strong audit trail not only reinforces your real-time controls but also ensures regulatory compliance.
Feed these components into your SIEM system or automated reconciliation tools. As the AP2 Documentation highlights:
"In production deployments, plug these feeds into SIEM systems, risk dashboards, or automated reconciliation pipelines"
Conclusion
Policy-as-code brings a new level of governance to the table, offering features like spending limits, multi-person approvals, and cumulative thresholds - all executed at the speed of blockchain. By evaluating every transaction before it’s signed, this approach can either block or flag potential risks instantly (or evaluate them using a stablecoin risk calculator).
The result? Consistent, reliable compliance. Every transaction is thoroughly assessed and logged in a tamper-evident audit trail, ensuring that only transfers meeting your organization’s risk criteria are approved through essential controls. Whether it’s restricting large payments to pre-approved vendors, setting daily outflow limits, or requiring CFO approval for payments to new wallets, policy-as-code ensures no transaction bypasses your governance standards.
Peter Kamminga captured the essence of this shift when he said:
"The GENIUS Act transforms stablecoins from a market experiment into a regulated financial product".
Policy-as-code extends this level of rigor to internal controls, giving regulators and auditors clear, actionable proof that your risk management processes are both effective and consistently applied.
With these controls in place, organizations can move from reactive oversight to proactive policy enforcement. This not only reduces false positives but also speeds up the approval process, creating a single, reliable source of truth for all stablecoin transactions. By adopting this framework, you establish scalable governance that ensures every on-chain dollar is both authorized and compliant.
FAQs
How does policy-as-code enhance the security of stablecoin transactions?
Policy-as-code enables finance teams to automate and enforce rules like transaction limits, approval processes, and risk assessments. These automated policies are applied to every stablecoin transaction before it's signed, ensuring that any unauthorized or high-risk transfers are flagged or stopped in their tracks.
By implementing this method, organizations gain a consistent and auditable layer of control over payments. This not only strengthens governance but also minimizes the chances of errors or fraudulent activity.
What are velocity limits, and how do they protect wallets from draining attacks?
Velocity limits are policy-driven controls designed to regulate how quickly funds can move out of a wallet. These limits can be set in various ways - per transaction, across specific timeframes like hourly or daily totals, or even by the number of transactions allowed within a certain period (e.g., no more than a few transactions per minute). By implementing these restrictions, the system can detect and respond to unusual activity, such as rapid fund withdrawals, effectively preventing attackers or malicious actors from draining the wallet in a short time.
If a draining attack is detected, velocity limits can automatically trigger a BLOCK or REQUIRE APPROVAL action when activity surpasses the preset thresholds. This ensures that unauthorized transactions are halted before they’re signed and executed, keeping funds secure unless explicitly approved by a trusted individual.
Why is it crucial to keep a detailed audit trail for stablecoin transactions?
Keeping a thorough audit trail is essential for ensuring transparency, accountability, and compliance in every stablecoin transaction. It offers CFO-level documentation that can be shared with auditors, boards, and regulators, showcasing the reliability of your financial operations.
An effective audit trail doesn’t just support compliance - it also empowers finance teams to justify decisions, monitor approvals, and log every stage of a transaction, from the initial intent to final execution. This makes it an indispensable resource for governance and managing risks effectively.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


