
Policy-as-code transforms audits by automating compliance checks and creating real-time, audit-ready records. Instead of relying on manual processes, this approach embeds rules directly into workflows, ensuring every transaction is validated before execution. Here's why this matters:
Time saved: Finance teams spend less time gathering evidence, with automated systems generating detailed, tamper-proof records.
Error reduction: Policies are applied consistently, eliminating gaps caused by human error.
Proactive compliance: Transactions that don't meet rules are blocked instantly, preventing violations.
Why enterprise teams succeed with Policy as Code using OPA
The Audit Problem: Manual Work and Compliance Risks

Policy-as-Code Impact on Audit Efficiency and Compliance Costs
Time-Consuming Audit Preparation
Audit season often feels like a marathon for finance teams. Hours are spent sorting through spreadsheets, piecing together approval chains buried in email threads, and pulling evidence from systems that don’t talk to each other. This manual grind doesn’t just eat up time - it drives up operational costs. In fact, 46% of security and IT leaders report compliance or operational issues tied directly to manual workflows.
The numbers highlight the inefficiency. Managing user identities manually takes an average of 15 hours per user - split between provisioning (7 hours) and deprovisioning (8 hours). Meanwhile, finance teams act as "human middleware", manually stitching together data from disconnected systems. This tedious process creates room for compliance gaps, leaving organizations vulnerable when it’s time for audits.
Compliance Gaps and Inconsistent Policy Application
Manual workflows don’t just slow things down - they also lead to uneven policy enforcement. When policies are tucked away in PDFs or Word documents, employees are forced to memorize or repeatedly reference them for every transaction. Not surprisingly, this approach is prone to errors. It’s no wonder that 60% of data breaches stem from human mistakes, manipulation, or malicious activity.
The financial stakes are steep. Non-compliance costs can double an organization’s total compliance budget, and companies lose about 5% of their annual revenue to occupational fraud due to weak internal controls. A McKinsey survey revealed that many banks struggle with control systems, particularly in areas like automation, monitoring, and analytics. These inconsistencies make real-time compliance validation an uphill battle.
Proving Compliance at the Moment of Decision
Beyond preparation and policy enforcement, proving compliance at the exact moment a decision is made is another major hurdle. Traditional systems often check for compliance after the fact, but auditors want proof that key steps - like sanctions screening - happened before a transaction was approved. When approvals are scattered across messaging apps or email threads, telling a clear, auditable story becomes nearly impossible.
"Approvals are buried in Telegram, Slack, or email threads. There's no clean story for auditors, boards, or regulators." - Stablerail
This reactive approach not only delays the discovery of issues but also drives up the cost of remediation.
How Policy-as-Code Creates Audit-Ready Evidence
Policy-as-code transforms the way audits are conducted. Instead of frantically gathering evidence after the fact, this approach ensures that defensible records are automatically created during every transaction. By embedding compliance rules directly into workflows, organizations shift from reactive audits to a system of continuous, provable compliance. This creates a tamper-proof, always-enforced compliance framework.
Policies Built Into Workflows
Unlike static policies buried in PDFs or Word documents, policy-as-code turns them into executable rules that actively govern transactions in real time. For example, limits, role-based approvals, velocity checks, and counterparty whitelists are encoded directly into the system. When a finance team member initiates a payment, the system automatically verifies it against these rules before funds are moved.
These policies act as checkpoints, blocking transactions until all necessary approvals are in place. Automated checks - like sanctions screening, taint analysis, and anomaly detection - happen instantly during transaction creation. This ensures complete coverage and eliminates the gaps often found in traditional, sample-based audits. Every decision is recorded digitally, creating a comprehensive record.
Immutable Evidence
Each decision made by the policy engine is captured in detail, including timestamps, applied rules, requester identity, and outcomes. This creates a unified, unalterable audit trail, replacing fragmented evidence often scattered across emails or Slack threads. Because these records are generated automatically and stored in immutable logs, they can’t be tampered with. This provides a clear, timestamped narrative for auditors, boards, and regulators, ensuring defensibility and transparency.
Enforcing Policies in Real Time
With robust, unchangeable records as a foundation, policy-as-code enforces compliance in real time by preventing non-compliant transactions before they occur. Acting as a digital gatekeeper, it ensures that only approved actions move forward. This proactive approach removes the need for costly post-event remediation and prevents out-of-policy transactions from ever happening.
"Sentinel is going to be that bouncer in a club that allows you to go in or out. For us, that gives us 100% confidence that anything provisioned by Terraform is following our security postures." - Scaling innovation: ADB's cloud journey with Terraform
If a transaction violates a rule - such as exceeding a limit, targeting a flagged address, or occurring outside approved hours - the system immediately blocks it and provides an explanation. Human reviewers can step in to assess the context and, if necessary, approve exceptions with proper documentation. Every decision, whether automated or manual, is logged for full transparency.
This shift from manual, after-the-fact controls to real-time verification changes compliance into an always-on process. Finance teams gain a complete, audit-ready record of every decision, eliminating the chaos of traditional audits.
Stablerail (https://stablerail.com) applies these principles to secure business decisions and financial operations seamlessly.
Core Layers of Policy-as-Code for Audits
When it comes to ensuring compliance, policy-as-code plays a crucial role by automating processes and creating audit-ready evidence in real-time. It operates through three tightly connected layers, each designed to handle specific aspects of compliance: controlling access, regulating actions, and documenting decisions. Together, these layers reduce the need for manual audits and provide a secure framework for financial operations.
Identity and Access Controls
The first layer focuses on defining who can do what through role-based access controls (RBAC). This step ensures that only authorized individuals can initiate or approve transactions. Instead of catching problems after they occur, these controls prevent unauthorized actions from happening in the first place. For example, a junior accountant might be allowed to create a payment intent, but only a CFO would have the authority to approve transfers over $5,000 to new vendor addresses.
Modern systems enhance these controls with tools like SSO (Single Sign-On), MFA (Multi-Factor Authentication), and hardware keys. They also use multi-step approvals secured by MPC (Multi-Party Computation) and purpose-binding, which limits actions to specific assets or destinations. This setup not only strengthens security but also creates a detailed audit trail, tying every user to their permissions and actions. For auditors, this means complete accountability is baked into the system.
Once access is controlled, the focus shifts to evaluating each transaction.
Transaction-Level Policy Checks
Every transaction is scrutinized in real-time against predefined rules before it is executed. These checks cover a range of criteria, including sanctions screening, taint analysis, anomaly detection (verified via a crypto compliance checker) (e.g., unusual time-of-day patterns), and counterparty risk scoring. The system evaluates factors like transaction value, destination address, currency type, and user role to decide whether to approve, flag, or block a payment.
For instance, a policy might automatically block any USDC transfer over $10,000 on weekends unless a CFO provides additional approval. Similarly, transactions directed to flagged addresses from external compliance providers could be rejected outright. These checks happen instantly and log detailed contextual evidence for every decision. The system records the rules applied, the outcome, and the reasoning behind it, creating a clear and defensible record that aligns with specific policies and timestamps.
Complete Audit Trails
The final layer ensures that every action - whether it’s a decision, approval, override, or signature - is recorded in immutable logs. These logs use secure cryptographic methods to capture critical details like the requester's identity, timestamps, applied rules, and outcomes. By automating evidence collection, these logs eliminate the need for weeks of manual preparation, enabling near-instant audit reporting.
This approach transforms audits from occasional, reactive events into a continuous process of provable compliance. With everything securely documented, auditors can trace any decision back to its source with confidence.
For example, Stablerail (https://stablerail.com) applies these three layers to manage stablecoin treasury operations. Their system creates CFO-grade audit trails, ensuring that every payment decision is defensible to auditors, boards, and regulators alike.
Implementing Policy-as-Code for Audits
Transitioning to automated policy enforcement involves turning regulatory requirements into code, integrating these policies with existing systems, and maintaining ongoing oversight. This approach ensures compliance is continuously monitored and automatically documented, laying the groundwork for smoother implementation as discussed in the following sections.
Translating Audit Requirements into Policies
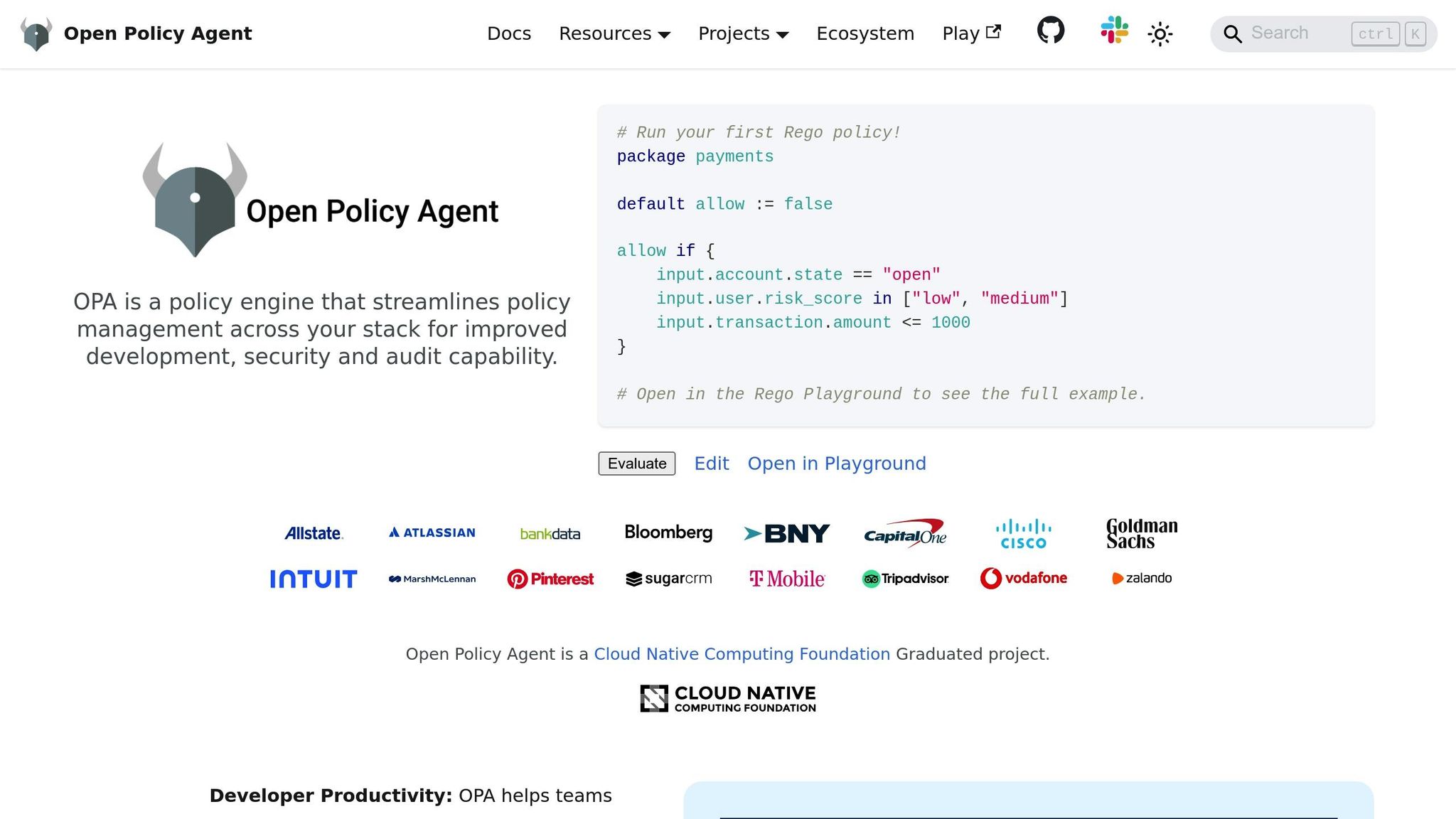
The first step is translating audit requirements into code. This process is essential for achieving real-time compliance, which simplifies audits significantly. Organizations use policy languages like Rego or Sentinel to codify rules. For instance, GDPR's Article 12 requirement to respond to data subject requests within 30 days can become a validation rule that flags overdue responses. Similarly, a PCI DSS control mandating encryption of cardholder data might translate into a policy file (e.g., pci_dss_3_4_1.rego) that blocks any attempt to store unencrypted payment details.
"Policy as code gives you an automated way to check, in minutes or seconds, if your IT and business stakeholders' requirements are being followed in your infrastructure deployments." - Kashaf Salaheen and Mitch Pronschinske, HashiCorp
This method shifts away from informal processes by introducing version-controlled code that can be peer-reviewed, tested, and updated, much like application software. For example, in stablecoin treasury operations, policies might specify rules such as "Weekend transfers over $10,000 require CFO approval" or "Block payments to flagged addresses identified by Chainalysis or TRM Labs." Each rule includes criteria like transaction value, destination address, time of day, and user role, which the system evaluates before execution.
Connecting with Existing Systems
Once policies are codified, the next step is integrating them with the organization’s financial systems. Policy-as-code frameworks need to work seamlessly with the tools finance teams already rely on. This might involve embedding policy checks into CI/CD pipelines for infrastructure deployments or connecting directly to treasury management systems for real-time governance.
A good example is Stablerail (https://stablerail.com), which acts as a bridge between custody and transaction signing. It integrates with external compliance intelligence providers to block risky transactions and feeds audit-ready evidence into the organization’s reporting systems. This eliminates the need for manual reconciliation, syncing the speed of on-chain settlement with the governance standards expected in traditional banking.
The key is making policies accessible to non-technical stakeholders. When finance, legal, and compliance teams can easily understand and collaborate on policy definitions, the system becomes a shared, transparent resource instead of a technical enigma.
Continuous Compliance Through Automation
Policy-as-code transforms periodic audits into continuous, automated monitoring. By embedding compliance checks into every workflow, organizations ensure full coverage instead of relying on sample-based audits. For example, if a developer tries to deploy non-compliant infrastructure or a finance team member attempts a payment that violates policies, the system immediately blocks the action and logs the attempt with detailed context.
"Sentinel is going to be that bouncer in a club that allows you to go in or out. For us, that gives us 100% confidence that anything provisioned by Terraform is following our security postures." - ADB (Asian Development Bank)
This shift from occasional audits to ongoing compliance reduces risk and allows internal teams to focus on strategic initiatives instead of manual evidence collection. With 89% of firms reporting that manual payment management drains internal resources, automation offers immediate operational relief. Continuous monitoring not only minimizes risks but also ensures compliance evidence is always up-to-date and readily available through policy-as-code.
Conclusion: Why Policy-as-Code Simplifies Audits
Policy-as-code is redefining how organizations handle compliance by turning manual, labor-intensive audit preparation into a seamless, automated process. Instead of spending weeks piecing together evidence, finance and compliance teams now have instant access to audit-ready documentation generated in real time as transactions occur. This automation removes the delays and inefficiencies that often bog down traditional audits.
By embedding compliance checks directly into workflows, policy-as-code ensures complete coverage rather than relying on the inconsistent, sample-based methods of conventional audits. Every transaction is automatically verified against pre-set rules, stopping non-compliant actions before they even reach production. This real-time enforcement aligns with earlier discussions on immutable records and continuous monitoring. It prevents costly remediation efforts and guarantees that audit evidence remains secure and tamper-proof, supported by cryptographic integrity and a version-controlled history of policy changes.
Key Takeaways
Policy-as-code shifts audits from being reactive, one-off events to continuous compliance processes that run quietly in the background. This approach offers three major benefits:
Automated evidence generation: Eliminates the need for manual evidence gathering.
Real-time enforcement: Prevents compliance violations before they happen.
Centralized policy management: Ensures consistent application across all systems.
Together, these features create a compliance framework that can grow alongside a business without adding unnecessary complexity or cost.
For finance teams handling stablecoin payments, platforms like Stablerail (https://stablerail.com) showcase how policy-as-code operates in the real world. By embedding governance rules into transaction approval workflows, these platforms create detailed audit trails for every decision and provide plain-English explanations that auditors can easily understand. This method combines the speed of on-chain settlement with the governance rigor of traditional banking, proving that compliance and efficiency can work hand in hand.
The move to policy-as-code isn’t just about smoother audits - it’s about creating scalable governance. When compliance rules are managed in version-controlled code instead of spreadsheets or email threads, organizations can track every policy change, understand the rationale behind each rule, and quickly adjust to new regulations without disrupting operations. This not only simplifies audits but also strengthens governance as businesses grow.
FAQs
How does policy-as-code streamline real-time compliance checks?
Policy-as-code integrates your rules and policies directly into automated workflows, streamlining real-time compliance. This means every transaction or request is automatically checked against set policies - like approval limits or risk thresholds - without needing manual reviews.
One of the key benefits is the creation of instant, defensible compliance records. These include details like timestamps and specific policy references, which make audits quicker and more straightforward. By automating these processes, policy-as-code not only minimizes human error but also ensures rules are applied consistently across all operations.
How does policy-as-code make audits easier?
Policy-as-code makes audits easier by automatically generating detailed, real-time audit trails. It logs every action, decision, and compliance check, so organizations can quickly provide accurate documentation whenever auditors, regulators, or boards request it.
This method eliminates the need for slow, error-prone manual processes by introducing continuous, proactive monitoring. By integrating compliance controls directly into workflows, policy-as-code minimizes the chances of audit failures, improves transparency, and ensures consistent compliance with governance policies. Plus, it saves finance and compliance teams a significant amount of time and effort.
How does policy-as-code help create secure and reliable audit trails?
Policy-as-code makes it easier to maintain secure and reliable audit trails by automatically logging every step in a transaction workflow. This includes actions like creating intents, performing policy checks, raising flags, granting approvals, and handling overrides. Every decision is documented with clear, traceable evidence.
These detailed and tamper-proof records offer a comprehensive audit trail, simplifying the process of proving compliance to auditors, regulators, and other stakeholders. Plus, it reduces the need for manual tracking, saving time and effort.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


