

Stablecoin payments are growing fast, but their speed and irreversibility increase risks like fraud and errors. CFO-grade approval thresholds are a key safeguard, ensuring high-value or high-risk transactions are reviewed before hitting the blockchain. Here's why they matter and how to implement them:
Why It Matters: In 2024, 79% of businesses faced payment fraud attempts, with 63% linked to email scams. Threshold policies reduce risks by requiring multiple approvals for large or unusual transactions.
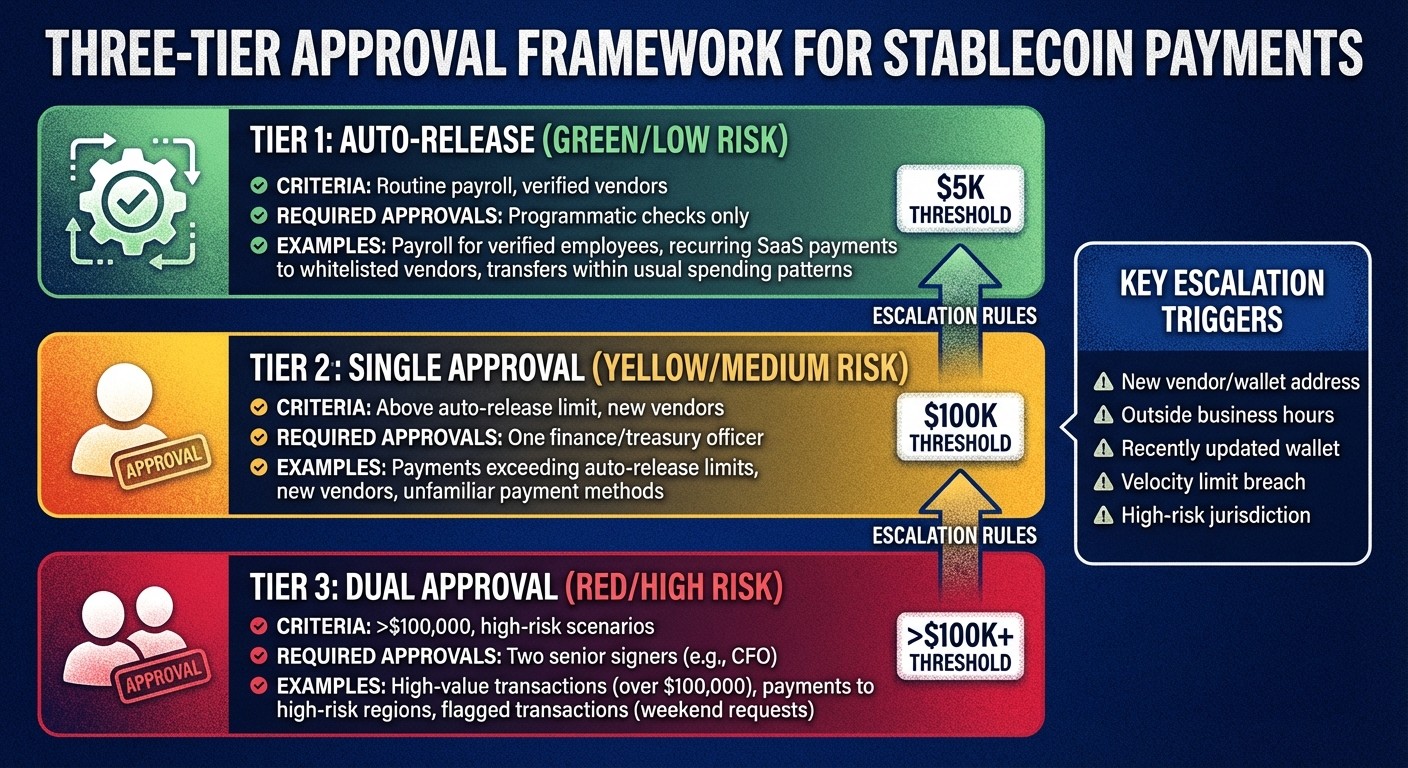
How It Works: Payments are categorized by risk, with dollar limits and escalation rules. For example:
Routine payments may be auto-approved.
Mid-range amounts need single approval.
High-value or flagged payments require dual approval.
Automation: Modern tools enforce these rules automatically, flagging anomalies like payments to new vendors or outside business hours.
Audit-Ready: Every decision is logged, creating a clear, traceable record for auditors.
Invoice Fraud: The Two Tactics to Watch For!
What Are Threshold-Based Approval Policies?
Three-Tier Stablecoin Payment Approval Framework
Threshold-based approval policies are structured frameworks designed to determine how transactions are reviewed based on specific factors like dollar amount, risk indicators, or the type of counterparty involved. These policies ensure payments are routed through the appropriate approval process before being executed.
At the core of these policies is the "t-of-n" logic, which requires a minimum number of participants (t) from a group (n) to authorize a transaction. This approach enforces separation of duties (SoD), preventing any single person from having unchecked control over a payment. For example, a $150,000 payment might need approval from two out of three senior executives before it can proceed. A typical SoD framework divides roles into Requester, Preparer, Approver, Signer, and Reconciler, creating a system of checks and balances to guard against errors and fraud.
Implementing these policies is a key step toward automating payment approvals while ensuring they meet audit standards. The following sections will explore how to classify transactions by risk, set escalation rules, and implement these policies programmatically. But first, let’s look at why thresholds are so important for stablecoin treasuries and the key components of an effective policy.
Why Thresholds Matter for Stablecoin Treasuries
Stablecoin transactions are settled almost instantly and cannot be reversed, making it essential to have well-defined threshold policies in place. These policies provide a structured decision-making process for high-value transactions, replacing informal methods like "Slack approvals" or email chains with a documented system that auditors, boards, and regulators can easily review.
As Peyman Khosravani puts it:
"Governance is a design problem, not a headcount problem: Adding approvers creates bottlenecks and diffuses accountability."
By automating routine payments and escalating only high-risk ones, organizations can maintain both speed and control. This balance is crucial when dealing with the risks of instant, irreversible settlements, as it ensures that critical transactions are reviewed thoroughly without slowing down operations.
Core Elements of a Threshold Policy
An effective threshold policy is built on four main components: transaction categories, approval tiers, dollar limits, and escalation rules.
Transaction categories: These group payments based on their type and associated risk. For instance, payroll for verified employees has a lower risk profile than payments to a new vendor. Categories might include recurring SaaS payments, vendor invoices, contractor payments, or treasury transfers.
Approval tiers: These define who reviews each transaction. A common three-tier structure looks like this:
Tier
Category
Criteria
Required Approvals
Tier 1
Auto-Release
Routine payroll, verified vendors
Programmatic checks only
Tier 2
Single Approval
Above auto-release limit, new vendors
One finance/treasury officer
Tier 3
Dual Approval
>$100,000, high-risk scenarios
Two senior signers (e.g., CFO)
Dollar limits: These thresholds determine which tier a transaction falls into. For example, payments under $5,000 to pre-approved vendors might be auto-released, while transactions between $5,000 and $100,000 require single approval, and those above $100,000 demand dual approval. These limits should align with the organization's risk tolerance and typical transaction patterns.
Escalation rules: These are conditions that push a transaction to a higher approval level, regardless of its dollar amount. For instance, a $3,000 payment to a new vendor might need single approval, even though it’s below the standard limit. Payments made outside business hours or to recently updated wallet addresses are other examples of scenarios that might trigger escalation.
Modern systems set up MPC wallets to enforce these policies through automation rather than manual processes. When a payment request is submitted, the policy engine evaluates it against the rules and delivers one of five outcomes: Approve, Deny, Hold (for further checks), Route (select the best payment method), or Step-up (require additional verification). This automated approach ensures consistency and minimizes the risk of human error.
Setting Transaction Tiers and Approval Levels
Understanding threshold policies is just the first step. The real challenge lies in assigning transactions to the right approval levels. This isn't about piling on approvers - it’s about directing payments based on their actual risk. For example, a US$200,000 payment to a trusted payroll provider carries a very different risk than a US$3,000 transfer to a brand-new vendor. Your approval structure should reflect these differences, ensuring transactions are both secure and efficient.
Classifying Transactions by Risk
Classifying risk involves several factors: transaction amount, counterparty status, asset and chain selection, wallet type, and timing patterns. While dollar thresholds are often the first trigger - like requiring dual approval for payments over US$100,000 - they aren't the whole picture.
Counterparty status is a critical consideration. A US$50,000 payment to a long-time vendor you’ve worked with for years is likely low-risk. But the same amount sent to a newly created wallet address? That’s a red flag. Some companies even implement a "cool-off period", delaying high-value transfers to new beneficiaries by four hours to help prevent fraud or social engineering attacks.
Timing also matters. Payments made outside of usual business hours, on weekends, or during holidays should prompt extra scrutiny. For instance, a US$75,000 transfer requested at 2:00 AM on a Saturday deviates from normal patterns and deserves a closer look. Similarly, velocity limits - where spending spikes sharply in a short time - can signal suspicious activity. If a department that usually spends US$20,000 per week suddenly requests US$80,000 in one day, that should trigger a review.
Wallet categorization adds another layer of control. Funds can be divided into three tiers: Cold/Reserve wallets for high-value holdings with strict multi-party controls, Warm/Operations wallets for regular payouts with standard approvals, and Hot/Automation wallets for low-value automated transactions with balance caps. By tagging wallets based on their risk level, policies can be tailored - automated payouts may bypass human approvals, while higher-risk wallets remain tightly monitored.
Creating Approval Tiers and Escalation Rules
Using these risk indicators, you can create a tiered approval system that blends control with efficiency.
Tier 1 (Auto-Release): This tier includes routine transactions like payroll for verified employees, recurring payments to whitelisted vendors, or transfers within usual spending patterns. These payments pass through automated checks for sanctions and velocity limits without requiring manual intervention.
Tier 2 (Single Approval): Transactions that exceed auto-release limits, involve new vendors, or use unfamiliar payment methods fall here. A single team member - typically from finance or treasury - reviews the payment details, ensuring invoices match amounts, vendor information is correct, and the expense aligns with the budget.
Tier 3 (Dual Approval): High-value transactions (over US$100,000), payments to high-risk regions, or flagged transactions (like weekend requests) require dual approval. This involves two senior approvers, often including the CFO or Treasurer, to ensure no single person can authorize a high-stakes payment alone.
Escalation rules allow flexibility within this structure. For example, a US$3,000 payment to a new vendor might usually need just one approval. But if the vendor’s wallet address was created recently, the policy could escalate it to dual approval. Similarly, any request to override a policy - like paying a sanctioned address or exceeding velocity limits - should require CFO-level authorization and a documented explanation.
Modern policy engines go beyond simple approvals or denials. They can flag payments for further review, route them to specific chains based on fees or liquidity, or require additional verification steps like multi-factor authentication. This adaptability transforms edge cases - such as urgent legal payments or emergency vendor requests - into structured workflows rather than chaotic last-minute decisions on Slack.
Implementing and Automating Policy Enforcement
After setting up approval tiers and escalation rules, the next challenge is ensuring they're consistently enforced. Relying on manual methods like spreadsheets or Slack for enforcement isn't practical - it’s error-prone and struggles to keep up with the speed of stablecoin payments, which settle in minutes instead of days. To achieve real-time oversight for stablecoin transactions, automation is key. Enter policy-as-code: a way to convert your rules into machine-enforceable logic that runs automatically before any transaction is approved.
Using Policy-as-Code for Governance
Policy-as-code transforms compliance rules into executable software. Instead of simply documenting rules like "payments over $100,000 require CFO approval", you program the system to enforce them automatically. This approach replaces manual back-office processes with real-time oversight.
Platforms such as Stablerail make it possible for finance teams to write policies in plain language that are then converted into enforceable rules. For example, you could establish policies such as:
Payments over $5,000 to new addresses require CFO approval and verification.
Weekend transfers exceeding $10,000 need additional approval.
These policies are treated like software - they’re version-controlled, tested for edge cases, and go through approval workflows before being activated. This ensures that decisions are consistent: the same inputs will always produce the same outcomes, no matter who initiates the payment or when.
The policy engine evaluates each payment request by incorporating risk data - like counterparty risk scores, jurisdictional considerations, and transaction history - which can be quantified using a stablecoin risk calculator, and returns a clear decision: Approve, Deny, Hold, Route, or Step-up. By separating where policies are defined (the engine) from where they’re enforced (the signing service), you ensure consistency across all payment methods and eliminate potential workarounds.
Once these automated rules are in place, the next step is to ensure every payment undergoes thorough pre-sign verification.
Automating Pre-Sign Checks
Automation, powered by Stablerail’s pre-sign agents, ensures that every payment is screened for sanctions, policy compliance, behavioral anomalies, and counterparty risk before it’s signed. The system generates a Risk Dossier with a clear verdict - PASS, FLAG, or BLOCK - accompanied by plain-English explanations tied to specific evidence, like policy details and timestamps.
This eliminates the risk of "blind signing", where payments are approved without full context. For instance, imagine a team member requests a $50,000 transfer at 2:00 AM on a Saturday to a vendor whose wallet address was recently updated. The system would flag this request for further review instead of letting it proceed unchecked. The policy engine might escalate the request for dual approval, trigger additional security checks, or impose a delay. If the decision is anything other than "Approve", the cryptographic key remains locked, preventing unauthorized actions even if someone tries to bypass the workflow.
Every step - policy version, requester identity, rule evaluations, and final decisions - is logged to create an immutable Proof-of-Control receipt. This gives auditors a transparent, detailed record to review. By automating pre-sign checks, compliance shifts from a manual burden to an efficient, audit-ready process. Despite advancements, as of 2025, 98% of companies still handle some payment operations manually. Automating these checks not only reduces workload but allows finance teams to focus on exceptions rather than routine validations.
Creating an Audit-Ready Approval Workflow
Once you've set up automated enforcement, the next step is making sure every decision can stand up to scrutiny from auditors, regulators, or your board. An audit-ready workflow does this by meticulously documenting the what, why, who, and the supporting evidence for every decision. This is particularly important for stablecoin payments, which settle directly on-chain. Unlike traditional payment systems like ACH or wire transfers - which offer error correction windows - stablecoin transactions are final as soon as they're executed. That means all compliance reviews must be completed before signing off on the transaction.
Logging Evidence for Each Approval
To create a solid audit trail, you need to capture specific details at every step of the approval process. Each payment should generate a Proof-of-Control receipt that includes the payment amount, its purpose, the authorizer, and the risk assessment at the time of signing. This receipt becomes your primary defense during audits or regulatory checks.
Here’s a breakdown of the key data points to log:
Component | Recorded Data | Purpose |
|---|---|---|
Identity Logs | Requester ID, Approver ID, Signer ID | Ensures accountability and segregation of duties |
Policy Trace | Policy version, rules triggered, reason codes | Shows adherence to approved compliance guidelines |
Risk Dossier | Sanctions status, anomaly flags, risk score | Records pre-transaction compliance checks |
Business Context | Invoices, vendor history, override rationale | Links on-chain transactions to their business purpose |
Execution Data | Blockchain TX ID, timestamp, asset, chain | Ties internal approvals to on-chain transaction finality |
For high-risk actions, like overrides, additional documentation is critical. Overrides must be logged with independent authorization to ensure transparency and accountability. This is particularly important given the rise in payment fraud. In 2024, 79% of organizations faced payment-related fraud attempts, with 63% citing business email compromise as the primary tactic. Treating overrides as structured workflows - not informal exceptions - can help prevent these types of attacks.
Linking Business Context to Approvals
Adding business context to automated compliance checks makes your audit trail even stronger. Auditors often require proof that each payment is tied to a specific business purpose - whether it’s settling an invoice, paying a vendor, or funding payroll.
Platforms like Stablerail simplify this process by generating Risk Dossiers that align payment requests with your governance policies. When a payment is initiated - whether through an invoice PDF, payout CSV, or API - the system automatically extracts the relevant business details and evaluates them against your compliance rules before any approval is granted. For instance, if a vendor’s wallet address changes, the system flags the payment for manual review to confirm the change is legitimate before any funds are sent.
Requiring a business reference for every transaction - such as an Invoice ID, Payroll Batch ID, or Refund Ticket - ensures every payment has a clear purpose. With 98% of companies still handling some payment operations manually and 49% relying on five or more different systems, automating this linkage closes governance gaps that auditors frequently highlight. By connecting every on-chain transaction to its business rationale, you turn your audit trail into a clear record of informed business decisions.
Deploying and Scaling Threshold Policies
After automating pre-sign checks and setting up an audit trail, the next step is to deploy and scale your threshold policies. This process works best when done through a controlled, phased rollout.
Phased Rollout Plan
A structured 30–60–90 day roadmap can guide your rollout, helping you transition from the design phase to being fully audit-ready. Using your wallet policy and automated enforcement rules as a foundation, this timeline ensures a smooth and scalable implementation.
Days 0–30: Begin by laying the groundwork. Define the permitted stablecoins and networks, create wallet policies and tiers (Cold/Warm/Hot), and set up daily reconciliation processes. Include an exceptions queue to catch and address any early issues.
Days 31–60: Move into operationalization. Standardize counterparty onboarding procedures and run pilot tests with strict limits in place. Document every approval, flag, and override to create a robust audit trail. Use shadow audits to simulate live transactions, helping to pinpoint overly restrictive thresholds or potential logic gaps.
Days 61–90: Focus on scaling. Integrate reconciliation data into your finance systems and conduct incident drills to prepare for unexpected events. Expand transaction volumes only through formal change control processes, avoiding any informal exceptions. Platforms like Stablerail can simplify this phase by managing policies as code, complete with version control and automated testing.
Once fully deployed, continuous monitoring will help ensure that these thresholds remain effective as transaction patterns evolve.
Monitoring and Adjusting Thresholds
Monitoring is crucial to maintaining effective threshold policies. One key metric to track is the frequency of overrides - if senior leaders frequently override policy flags, it may signal the need for threshold adjustments. Additionally, keep an eye on operational anomalies such as new destination addresses, changes to signer sets, breaches in hot wallet balances, or unexpected fee spikes.
Measure success using metrics like settlement speed, cost per transfer, approval SLAs, and exception rates. As transaction volumes grow and risk profiles shift, adjust thresholds to keep pace. Include "Safe Mode" features in your system to pause execution, throttle transactions, or trigger incident protocols during periods of high risk or network disruptions. These dashboard KPIs ensure your approval logic stays aligned with the demands of instant settlement, balancing control with operational efficiency.
Conclusion
Threshold-based approval policies are redefining how stablecoin treasuries operate. They offer a structured approach that merges the fast-paced nature of on-chain settlements with the security and compliance standards finance leaders expect from traditional banking. By tailoring approval tiers to match risk levels, teams can guard against social engineering threats while maintaining operational efficiency.
This blend of speed and security is paving the way for a new governance model. Compliance-as-infrastructure shifts corporate treasury management from manual processes to automated systems. Instead of relying on back-office reviews and spreadsheet approvals, these systems enforce policies in real time, ensuring decisions are traceable and audit-ready. As Pat White, CEO of Bitwave, explains:
"You put all that into smart contracts and it's not me as the accountant being a dick making you pay this penalty... payment terms are enforced as code".
Stablecoin treasuries are evolving beyond simply being wallets for holding funds. As Stablecoin Insider highlights:
"A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process."
Building on this foundation, agentic verification - where AI tools analyze context, detect anomalies, and flag risks - eliminates blind approvals. Combined with measures like separation of duties, verified whitelists, and required business references, this creates a scalable, multi-layered defense system.
FAQs
What approval thresholds should a CFO set for stablecoin payments?
Approval thresholds for stablecoin payments should reflect your organization's risk management approach. For instance, many businesses require CFO approval for payments exceeding $5,000. For transactions over $10,000 - particularly those occurring outside normal business hours - additional approval layers are often added. These limits, enforced using policy-as-code, help maintain compliance, reduce risks like fraud, and create a clear audit trail. Adjust these thresholds based on your transaction volume, risk tolerance, and regulatory requirements.
Which risk signals should trigger step-up or dual approval?
Risk signals that call for extra scrutiny or dual approval include large or unusual transactions, policy violations, behavioral anomalies, sanctions exposure, counterparty risk concerns, and transactions exceeding predefined limits. These safeguards are in place to uphold compliance and governance by identifying high-risk activities that require closer examination.
How do you make stablecoin approvals audit-ready before signing?
Stablecoin approvals are kept audit-ready by creating a thorough audit trail at every stage - covering intent creation, checks, flags, overrides, and final approvals. Stablerail prioritizes clarity by offering plain-English explanations tied to specific policy clauses and timestamps, ensuring full transparency. Before signing, pre-approval checks include sanctions screening, policy enforcement, anomaly detection, and counterparty risk scoring, all meticulously documented for compliance and verification. This organized approach guarantees that every approval is fully traceable and prepared for audits.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


