
When following stablecoin treasury management best practices, mistakes can be costly - transactions are irreversible. Custom approval chains help prevent errors by enforcing automated, rule-based workflows. These workflows ensure payments meet specific conditions - like transaction limits, verified addresses, or multi-level approvals - before funds are sent. By splitting decision-making among multiple stakeholders and automating compliance checks, businesses can reduce risks, improve oversight, and maintain audit-ready records.
Key Takeaways:
Prevent Errors: Automate checks for sanctions, whitelisted addresses, and transaction limits.
Four-Eyes Principle: Require multiple stakeholders to approve high-risk payments.
Audit Trails: Log every decision for compliance and transparency.
Pre-Sign Checks: Use automated tools to flag risks before human review.
This approach is ideal for companies handling $1M–$50M in stablecoin transactions annually, ensuring payments are secure, policy-compliant, and error-free.
Core Components of Approval Chains
What Makes Up an Approval Chain
An approval chain relies on three key elements: roles, trigger conditions, and approval steps. Roles define responsibilities within the chain. For instance, a Treasury Analyst might initiate payments, while a CFO approves high-value transactions. Trigger conditions determine when a specific chain is activated, based on factors like payment amount, currency type, destination address, or even the time of day.
Approval steps can follow a sequential order (e.g., Manager → CFO → Treasurer) or use a quorum-based approach, where only a certain number of approvals (e.g., 2 out of 5) are required. More advanced chains incorporate limits on transaction amounts and velocity, flagging or escalating reviews if a wallet exceeds daily transaction counts or total value thresholds within a set time frame. A crucial safeguard in these chains is the four-eyes principle, which ensures no single individual has sole approval authority.
Another essential feature is the fallback mechanism. This acts as a default safety chain that activates when no specific policy conditions are met, ensuring every payment is reviewed appropriately until the next step in the process. Think of it as a safety net, catching any scenario not explicitly addressed by the primary rules.
With these components in place, automated policy enforcement becomes a critical tool to ensure consistency and reduce human error.
Why Automated Policy Enforcement Matters
Manual approval processes can be slow and prone to inconsistencies. Automation solves this by turning treasury policies into enforceable, real-time rules, often referred to as policy-as-code.
Before allowing a transaction to proceed, automated systems verify it against preset rules. For example, they might check if the destination address is whitelisted, if a vendor's address has been altered, or if the transaction exceeds a daily velocity limit. A specific example: if a stablecoin’s peg deviates by more than 0.5% for 30 minutes, automated rules can temporarily halt all outgoing transactions until stability returns.
Automation also ensures strict separation of duties. As Stablerail explains, “Even the CEO cannot bypass the code”. This programmatic enforcement creates a tamper-proof audit trail, logging every check, flag, and approval with timestamps. This transparency provides CFO-grade documentation for auditors and regulators. Ultimately, automation leads to quicker decisions, fewer errors, and compliance seamlessly integrated into the workflow - laying the groundwork for thorough risk analysis before any signature is made.
How Modern Treasury Built AI Agents for Financial Payment Operations with LangGraph
How to Build Custom Approval Chains
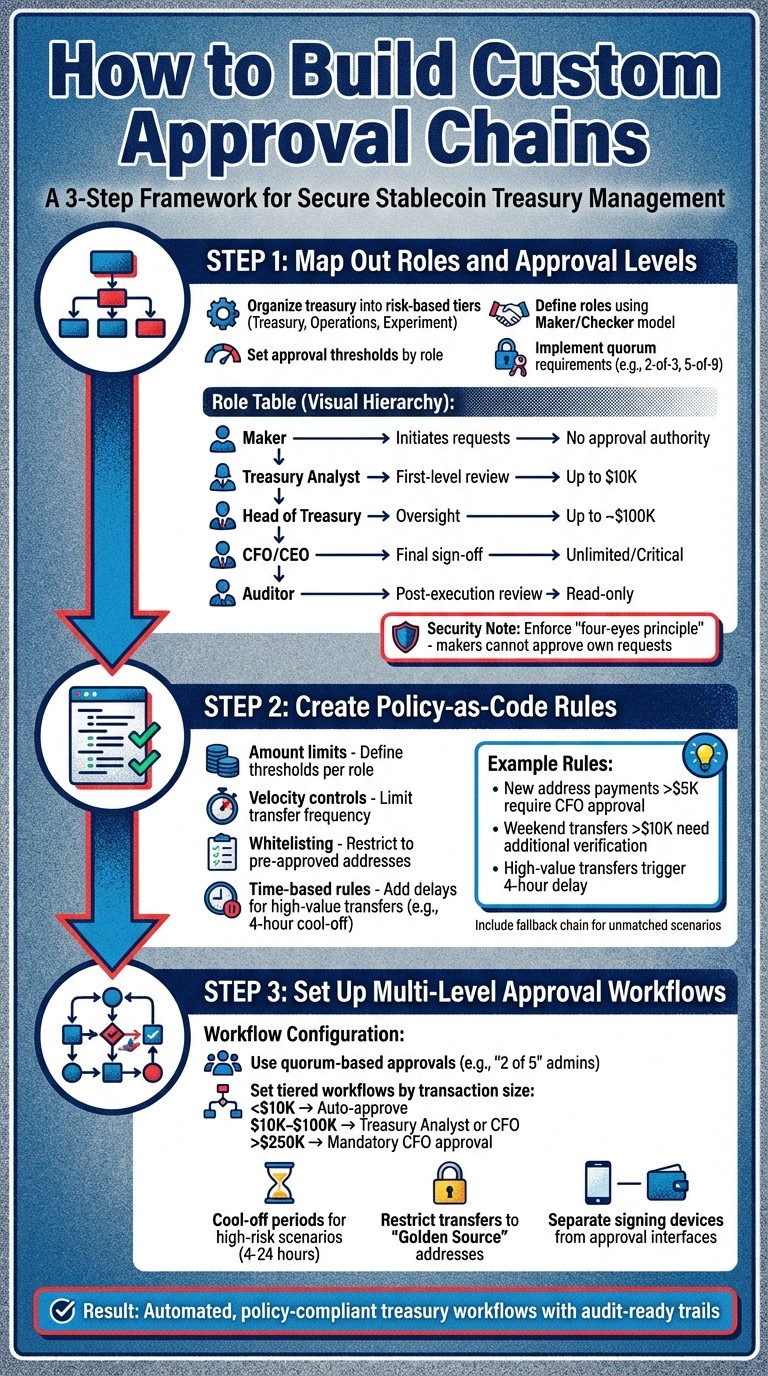
3-Step Process to Build Custom Treasury Approval Chains
Step 1: Map Out Roles and Approval Levels
Start by organizing your treasury into risk-based tiers. A common setup includes:
Treasury tier: Cold storage for long-term holdings.
Operations tier: Warm wallets for vendor payments and payroll.
Experiment tier: Hot wallets with minimal balances for testing purposes.
Each tier demands a different level of oversight and approval. Then, define roles using a Maker/Checker model:
The Maker initiates payment requests.
The Checker reviews and approves those requests.
Custodians hold cryptographic key shares in your MPC (multi-party computation) setup.
Auditors have read-only access for compliance purposes.
To enhance security, enforce the "four-eyes principle", ensuring makers cannot approve their own requests. Set clear thresholds for each role. For example:
A Treasury Analyst may approve payments up to $10,000.
Transfers exceeding $250,000 might require CFO review.
For high-value assets, use quorum requirements like "2-of-3" or "5-of-9" signatures, ensuring multiple key holders approve transactions. An example is the Safe protocol, which secures over $100 billion in assets with this M-of-N approach.
For added security, senior signers like CFOs should use hardware wallets for their signing keys. Test your approval chains with small transactions ($10 to $100) to ensure everything works smoothly before scaling up.
Step 2: Create Policy-as-Code Rules
Policy-as-code automates your treasury guidelines, turning them into rules that evaluate every transaction. For example, in Stablerail's Policy Console, you can set rules like:
"New address payments over $5,000 require CFO approval."
"Weekend transfers over $10,000 need additional verification."
These rules ensure that no transaction bypasses the system without proper checks. Key policies to implement include:
Amount limits: Define thresholds for different roles.
Velocity controls: Limit the frequency of transfers.
Whitelisting: Restrict transfers to pre-approved addresses.
Time-based rules can further enhance security. For example, high-value transfers might trigger a 4-hour delay, giving your team time to verify the transaction and prevent social engineering attacks.
Apply wallet tags to customize approvals. For instance, strict rules might apply to human-managed wallets, while automated service accounts handle low-risk tasks with fewer checks. If a transaction triggers multiple policies (e.g., one for the amount and another for the recipient), the system should require approvals from all relevant groups before proceeding.
Include a fallback approval chain for scenarios that don’t match predefined rules.
Step 3: Set Up Multi-Level Approval Workflows
Once your policy rules are in place, configure multi-level workflows to enforce them. This ensures that all necessary approvals are completed before any transaction is executed.
Instead of assigning approvals to a single individual, use quorum-based approvals. For example, requiring "2 of 5" admin approvals prevents delays when someone is unavailable. You can also set up workflows based on transaction size:
Payments under $10,000 might auto-approve.
Payments between $10,000 and $100,000 could require a Treasury Analyst or CFO signature.
Transfers over $250,000 may need mandatory CFO approval.
For added protection, introduce cool-off periods for high-risk scenarios. For instance, first-time beneficiaries or transactions exceeding $100,000 could face a delay of 4 to 24 hours, allowing time to catch errors or suspicious activity. Restrict outbound transfers to a "Golden Source" of pre-approved addresses, and ensure any changes to these addresses prompt mandatory escalation.
Finally, separate signing devices from approval interfaces. For example, initiate transactions via a web dashboard, but require co-signing with secure mobile devices or hardware wallets. This physical separation adds a critical security layer while maintaining efficiency for routine payments.
Adding Pre-Sign Checks and Risk Analysis
Automating Risk Screening with Pre-Sign Agents
Approval chains need more than just human intervention - they require a smart, automated layer to evaluate transactions before they even reach a human reviewer. That’s where pre-sign agents come in. These automated tools perform compliance and security checks in real-time, typically in less than 50 milliseconds.
Here’s how they work: pre-sign agents sit between the payment request and the signing process, scanning for issues like sanctions violations, tainted funds, or unusual activity. For instance, Stablerail’s pre-sign agents can flag first-time payment destinations, detect changes to vendor records, or spot duplicate payment attempts. If anything deviates from the verified "Golden Source", the system locks the payment and requires a manual review.
Before any key is used to authorize the transaction, the platform runs a pre-flight simulation. This ensures the recipient gets the correct amount and confirms there are no unexpected interactions with smart contracts. This step is critical for avoiding costly mistakes or falling victim to social engineering schemes.
The system also uses time-based detection to add another layer of security. For example, if someone initiates a high-value transfer outside of regular business hours, it can trigger a cool-off period - say, four hours - before the transaction proceeds. Once all these automated checks are completed, the system logs the results, providing clear guidance for human approvers.
Creating Risk Dossiers for Approvers
After the automated screening, the system compiles its findings into a detailed Risk Dossier. This dossier makes decision-making straightforward by providing a clear verdict: PASS, FLAG, or BLOCK.
"PASS / FLAG / BLOCK verdicts with plain-English reasons backed by evidence - not vibes." - Stablerail
A PASS means everything checks out. A FLAG signals potential risks that need further review, like a new beneficiary or an unusual payment amount. A BLOCK stops the transaction entirely, often due to sanctions or severe taint issues.
What makes this dossier so effective is its ability to translate complex blockchain data into plain-English explanations. Instead of overwhelming approvers with raw addresses or cryptographic details, it provides context. For example: "This recipient address was added to your vendor list three days ago and has no prior payment history. Policy requires CFO verification for new addresses exceeding $5,000." This clarity allows approvers to make quick, informed decisions.
For companies dealing with stablecoins, the dossier also flags freeze-risk patterns. If a counterparty has connections to sanctioned addresses, it warns that issuers like USDC or USDT could freeze your treasury wallet. This helps protect your company’s funds from unexpected disruptions.
Finally, these dossiers integrate seamlessly into your audit trail as part of a broader stablecoin compliance checklist. They document every transaction, including what was paid, the reasons for approval, and the associated risk verdict. This ensures that your treasury operates with clear, defensible controls, rather than relying on spur-of-the-moment decisions.
Deploying and Monitoring Your Approval Chains
Testing Your Approval Workflows
Before moving to production, it's crucial to test your approval chains in a controlled environment like a testnet (e.g., Sepolia) or a local fork. This allows you to simulate the entire lifecycle - from creating a payment to its final execution - without putting real funds at risk.
Your testing plan should cover both compliant and non-compliant transactions. For example, run payments that should process without issues while also testing edge cases like overlapping approval requests or conflicts in policy rules. Chainscore Labs highlights the importance of testing non-compliant transactions to ensure unauthorized actions are correctly rejected.
To preview how a transaction will behave, tools like Tenderly's Simulation API or eth_call can help simulate outcomes before signing. For more comprehensive testing, frameworks like Foundry or Hardhat enable automated tests that cover every step of the approval process. These tools ensure your policy-as-code rules function as intended, even under unusual conditions.
Once your workflows pass all tests, the next step is to document every action to meet compliance standards.
Maintaining Audit Trails for Compliance
A well-maintained audit trail is essential for regulatory and governance purposes. Every action in your approval chain - from payment intent to on-chain execution - should be logged in a tamper-resistant format. This not only supports internal record-keeping but also strengthens your position during audits, board reviews, or regulatory checks. As Vaultody puts it, "Audit readiness is a foundational requirement for treasury teams managing digital assets".
For stablecoin payments handled via MPC wallets, include cryptographic proof of which key shares participated in signing. Tools like Stablerail can automatically generate receipts for every payout, detailing the amount, approvers, and the risk assessment from pre-sign agents. If a flagged transaction is manually overridden, the system should record a clear, plain-English explanation for the decision to ensure transparency during audits.
It's also important to log any changes made to the approval chains themselves. Keeping a governance history that tracks updates - who made them, when, and why - ensures you can demonstrate that payments followed the rules in place at the time they were initiated.
With detailed records in place, you can continuously adapt your workflows to meet new challenges and requirements.
Refining Your Approval Chains Over Time
Approval workflows are not static; they need regular updates to keep pace with business growth, role changes, and evolving regulations. Use real-time dashboards to monitor pending approvals and identify delays. If low-risk payments are frequently stalled, consider adjusting thresholds or delegating authority for smaller transactions.
Measure your approval process performance across three key areas: Risk (e.g., eliminating single-actor authority), Speed (how quickly legitimate payments are approved), and Control (ensuring policies cover all necessary scenarios). Revisit your workflows whenever there are changes in internal roles, higher transaction volumes, or new compliance demands.
Finally, set up fallback approval chains as a safety net. This ensures that even if a payment doesn't fit predefined rules, it still undergoes proper oversight and cannot bypass the system entirely. By refining your processes regularly, you can maintain a balance between security, efficiency, and compliance.
Conclusion
Custom approval chains reshape treasury workflows into systems that are both policy-driven and efficient. By converting internal policies into code, these chains ensure that limits, roles, and whitelists are automatically enforced - blocking even senior executives from overriding established controls. This shift replaces the inconsistencies of spreadsheet-and-Slack-based approvals with consistent, audit-ready trails. The result? A streamlined process that boosts security and strengthens governance.
Using multi-level signers adds another layer of protection by reducing insider risks and applying the four-eyes principle. Requiring different individuals to initiate, approve, and execute transactions helps catch errors and potential threats before any funds are moved.
"A stablecoin treasury is not just a wallet; it is an operating system with documented, enforceable rules, and an auditable process." – Stablecoin Insider
This clear and structured approach builds trust among stakeholders and aligns with auditor expectations.
FAQs
How do I choose the right approval thresholds for each role?
To establish approval thresholds, make sure they align with your company's internal policies and risk appetite. Set clear rules based on specific criteria, such as payment amounts or currencies. For instance, you might require CFO approval for payments exceeding $5,000. Assign approvers according to roles and thresholds, ensuring that higher-value transactions are reviewed by senior-level staff. Periodically revisit and adjust these thresholds to keep pace with changing risk policies and operational requirements.
What should my fallback approval chain look like?
A fallback approval chain is crucial to ensure treasury payments are properly reviewed when primary approvers are unavailable or certain conditions aren't met. This system often includes two levels: an initial layer, such as department managers, and a secondary layer, like senior executives. To make it effective, clearly define the activation criteria - such as large payment amounts or the unavailability of primary approvers. Make sure this process is embedded within governance policies, supported by automated triggers, and paired with transparent audit trails. This approach helps maintain compliance and ensures accountability throughout the process.
What are the key pre-sign checks to run before signing?
Before finalizing any agreements, several critical checks must be performed to ensure everything is above board. These include:
Sanctions and taint/exposure screening: Verifying that parties involved aren’t flagged for sanctions or associated with questionable activities.
Policy and limit enforcement: Making sure all actions align with established policies and thresholds.
Behavioral anomaly detection: Identifying unusual patterns that could signal potential risks.
Counterparty risk scoring: Assessing the reliability and risk level of the other party.
Plain-English narrative explanations: Providing clear, straightforward summaries with evidence to back up findings.
These steps are essential to stay compliant, reduce risks, and uphold governance standards effectively.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


