
Emergency overrides are essential tools in fast-moving environments like finance and crypto. They allow authorized individuals to halt risky operations during emergencies. However, without proper audit trails, these overrides can lead to serious issues like compliance violations, financial mismanagement, and loss of trust.
Here’s why audit trails matter:
Accountability: They document who acted, when, and why, ensuring decisions are traceable.
Compliance: Regulations like SOX and MiCA demand clear records of emergency actions.
Trust: Stakeholders lose confidence when organizations can't prove proper oversight.
Untracked overrides can result in penalties, fraud, and operational failures. Implementing clear policies, real-time monitoring, and post-incident reviews, supported by tools like Stablerail, ensures every action is logged and verifiable. This protects organizations from risks while maintaining transparency and trust.
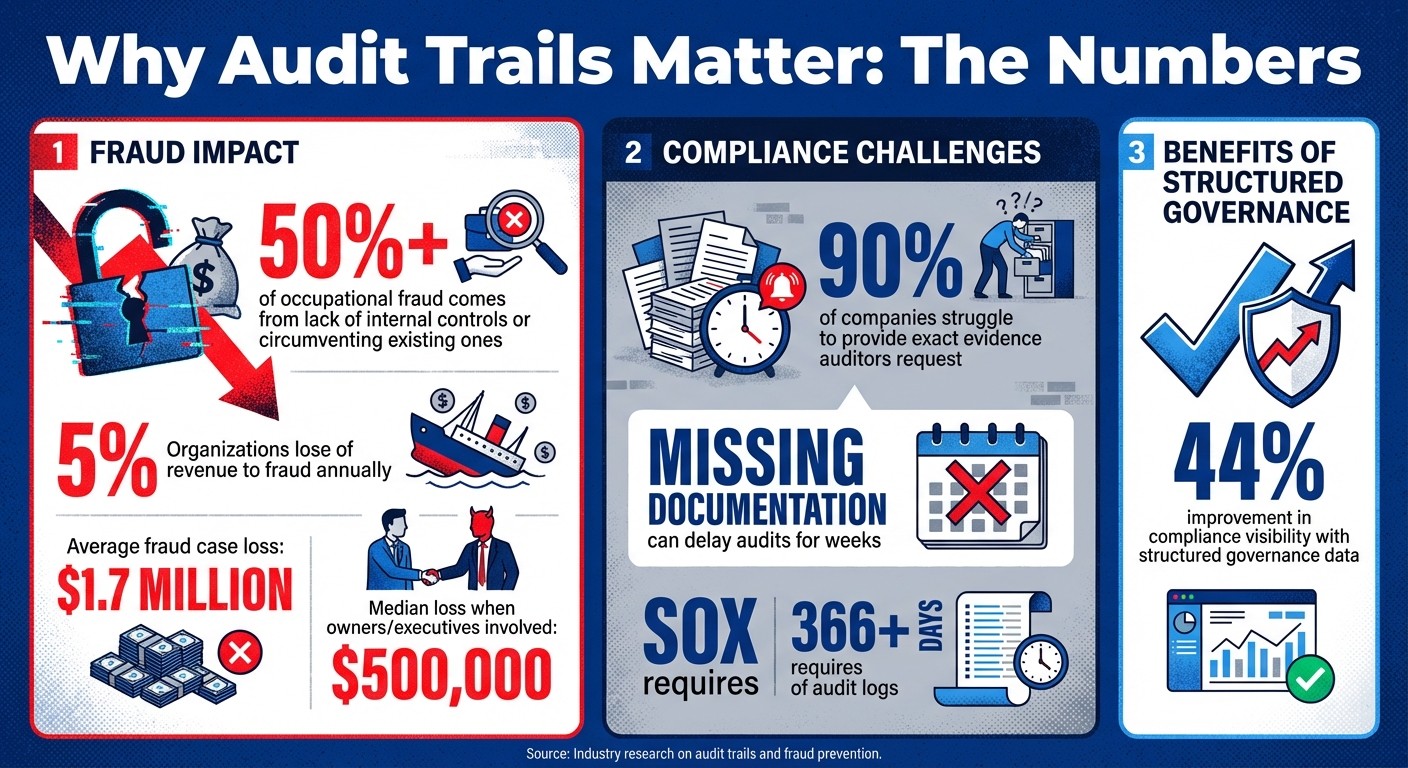
The Cost of Poor Audit Trails: Key Statistics on Fraud and Compliance
The Risks of Untracked Emergency Overrides
Untracked emergency overrides can lead to a range of serious risks, particularly when it comes to accountability, compliance, and stakeholder trust. Let’s break down why these risks matter so much.
Unauthorized Access and Fund Mismanagement
When emergency overrides aren’t documented, accountability disappears. Without records, it becomes easier for individuals to bypass established controls. This lack of oversight creates opportunities for insiders to carry out unauthorized transactions or even tamper with logs.
The absence of a detailed, chronological record leaves finance teams unable to answer critical questions like: How did this happen? When did it occur? Was it intentional or accidental? This makes it nearly impossible to determine whether changes to treasury ledgers were honest mistakes or deliberate actions.
"The most expensive audit finding is not 'the agent exceeded its authority' but 'we cannot prove what authority the agent had at the time of the action.'" – Aptly Resources
This lack of documentation doesn’t just undermine internal accountability - it also invites regulatory scrutiny and potential penalties.
Compliance Violations and Regulatory Penalties
For publicly traded companies, untracked overrides can lead directly to SOX violations. The Sarbanes-Oxley Act (SOX) requires companies to maintain strict controls over financial reporting. When emergency overrides bypass standard procedures without leaving evidence, auditors see this as a major internal control gap. This can result in negative audit opinions and hefty fines.
The problem becomes even more pronounced during regulatory reviews. Companies are expected to maintain at least 366 days of audit logs for SOX compliance. Yet, 90% of companies struggle to provide the exact evidence auditors request. Missing documentation can delay audits for weeks, adding to costs and frustrations.
What’s more, frameworks like the EU AI Act (Article 14) and MiCA now require clear authority structures and human oversight for automated systems. Untracked overrides fail to meet these standards, leaving organizations exposed to even stricter penalties under emerging regulations.
But the fallout doesn’t end with compliance issues - it also damages relationships with stakeholders.
Loss of Stakeholder Trust
The impact of untracked overrides goes beyond fines or regulatory setbacks. When boards, regulators, or auditors demand post-incident documentation and the organization can’t deliver, stakeholder trust takes a hit.
Companies with structured governance data report a 44% improvement in compliance visibility. Those without it, however, face growing skepticism with every unanswered question. Missing logs also make it harder to detect insider threats, like unauthorized file transfers or individuals posing as legitimate users.
If stakeholders realize that an organization can’t verify who had the authority to act during a crisis, it erodes confidence. Over time, this lack of trust can lead to constant scrutiny and diminished credibility.
The solution? Establishing robust audit trails to mitigate these risks - something we’ll explore in the next section.
How Audit Trails Reduce Override Risks
Audit trails serve as a powerful defense against unauthorized access, compliance issues, and trust erosion. By creating a permanent and verifiable record of every emergency override, they transform potential blind spots into a transparent and accountable process.
Tracking Every Action and Decision
An effective audit trail captures the who, what, when, and why behind every override. It logs key details like the user ID, the specific action taken, the exact timestamp, and the justification for bypassing automated controls. This level of precision ensures non-repudiation, making it impossible for individuals or systems to deny their actions.
Audit trails also verify "as-of" authority, proving that the individual performing the override had valid, delegated authority at that precise moment. This requires maintaining versioned delegation records with clear effective and expiration dates. Without this mechanism, organizations risk failing audits due to an inability to demonstrate proper authorization.
To safeguard these logs, cryptographic methods such as signed hashes or Merkle trees can ensure data integrity. For environments requiring heightened security, hardware-enforced write-once-read-many (WORM) media prevents tampering. This meticulous tracking not only deters unauthorized actions but also builds confidence with regulators.
Providing Transparency for Regulators and Auditors
Audit trails offer a clear, verifiable record - often referred to as a "single source of truth" - that regulators like the SEC, FINRA, or MiCA auditors can review programmatically. This automated transparency reduces manual reporting delays and accelerates compliance reviews, saving organizations significant time during audits. In fact, well-designed audit trails can eliminate weeks of delays often caused by the need to reconstruct events.
"Audit trails can make the difference between the successful operation of internal controls and control deficiencies." – Vice Vicente, AuditBoard
Standardized formats further enhance usability, allowing regulators to seamlessly analyze and correlate data across systems. This is especially critical for publicly traded companies, where SOX requires annual independent audits. Beyond meeting compliance obligations, a robust audit trail also helps organizations learn from incidents and improve their processes.
Enabling Post-Event Reviews
Audit logs are invaluable for post-incident analysis. They help identify process failures, detect internal fraud, and reveal weaknesses in access control policies that led to overrides. NIST guidelines (AC-3) even recommend audited overrides for automated access controls during emergencies or critical missions.
These logs enable teams to quickly perform root cause analyses, uncover cybersecurity threats, and address operational inefficiencies. This transforms audit trails into more than just a compliance tool - they become a strategic resource for refining policies and preventing future issues.
"A well-maintained audit trail is more than a compliance tool; it's a strategic asset in safeguarding the institution's reputation and operational resilience." – Empowered Systems
The ability to trace actions in detail - what some call "Theseus's string" - makes audit trails essential for understanding events and maintaining trust.
Stablerail's Audit Trail Approach for Emergency Overrides

Stablerail operates as a control layer between MPC-based custody and signing, ensuring that every stablecoin payment decision - including emergency overrides - leaves behind CFO-grade evidence. This evidence satisfies the needs of auditors, boards, and regulators, directly addressing the gaps in audit trails highlighted earlier.
Comprehensive Audit Trail for Every Step
Stablerail meticulously documents every stage of the payment process: from intent creation to risk checks, flags, approvals, overrides, and signing. Each action is tied to versioned delegation records, proving "as-of" authority. This means the system can confirm that an individual had the proper authority at the exact time they acted.
By addressing the common challenge of producing audit evidence - an issue faced by 90% of companies - Stablerail provides immediate, unchangeable records. These immutable records eliminate the typical three-week delays associated with audits.
"The most expensive audit finding is not 'the agent exceeded its authority' but 'we cannot prove what authority the agent had at the time of the action.'" – Aptly
Policy-as-Code for Automated Enforcement
With Stablerail's Policy Console, finance teams can define enforceable rules that the system applies automatically before any payment is signed. For instance, you can require CFO approval for payments to new addresses exceeding $5,000 or set additional checks for weekend transfers over $10,000.
This Policy Console ensures that each execution log is automatically tied to its corresponding authority record, meeting NIST (AC-3) standards. Organizations using this structured governance approach report a 44% improvement in compliance visibility.
By automating checks, only genuine exceptions are escalated for human review, streamlining the process while maintaining oversight.
Human-in-the-Loop for Exception Approvals
Stablerail emphasizes human oversight for exception approvals - actions that go beyond predefined rules. When an override is needed, the system logs the approver's identity, timestamp, and justification, linking their decision directly to the execution record.
This process generates a "Risk Dossier", which includes a verdict (PASS/FLAG/BLOCK) and detailed, clause-linked explanations. Approvers can review the evidence and either approve or override with documented reasons. This targeted approach minimizes unauthorized access risks and ensures regulatory compliance. It also provides clear answers to critical questions: who granted the authority, under what constraints, and with what specific approvals.
Best Practices for Building Compliant Emergency Override Protocols
Creating a compliant emergency override protocol involves establishing robust controls and maintaining thorough documentation to meet regulatory standards. A well-constructed protocol can mean the difference between a justified override during a crisis and a compliance issue.
Defining Clear Override Policies
Start by outlining specific conditions that justify emergency access, such as situations threatening human safety or critical business operations. Clearly define the roles authorized to initiate overrides and, for high-risk actions, introduce a dual-authorization system. This setup requires two individuals to approve the action, minimizing the risk of collusion. Known as "two-person control", this process ensures no single individual can bypass safeguards.
Keep detailed, versioned records of delegations, including effective and expiration dates. Having "as-of" authority records readily available can streamline audits and demonstrate that approvals were valid at the time of the override.
Once policies are established, the next priority is implementing real-time monitoring to oversee emergency activities as they occur.
Real-Time Monitoring and Alerts
Configure your systems to send immediate alerts to designated personnel whenever emergency access is activated. These notifications allow for quick responses to anomalies, such as unauthorized use or an unusually high frequency of overrides.
"Notifications add real-time transparency." – Hoop.dev
To safeguard audit logs, set up alerts for any attempts to modify or delete logging data without authorization. Organizations that use structured governance data and monitoring tools report a 44% improvement in compliance visibility.
Regular Post-Incident Audits
Real-time alerts are critical, but they aren't enough on their own. Conducting thorough post-incident audits ensures the integrity of your systems after an override. Review audit trails immediately to assess any damage and verify system functionality. This process helps differentiate between human errors and system issues, offering insights to enhance your protocols. Comparing system states before and after an override can reveal unauthorized changes and ensure that all issues are resolved.
Additionally, perform regular recertification of override authorities to confirm their suitability within the current organizational structure. This periodic review reinforces accountability, as users are less likely to bypass security measures when they know their actions are monitored and subject to review.
Conclusion
Emergency overrides play a crucial role in financial operations, but without proper audit trails, they can quickly shift from being safeguards to becoming compliance risks and sources of mistrust. Over 50% of occupational fraud stems from either a lack of internal controls or the circumvention of existing ones, with organizations losing an estimated 5% of their revenue to fraud annually. A well-maintained audit trail mitigates these risks by documenting who authorized actions, the constraints involved, and when the decisions were made.
Organizations that adopt structured governance data experience a 44% boost in compliance visibility. Audit trails not only help meet regulatory standards by offering clear "as-of" authority proof but also enable swift root cause analysis when issues arise.
Platforms like Stablerail are designed to address these challenges effectively. They capture every intent, risk check, approval, override, and signature in an immutable audit trail, complete with time-stamped evidence and plain-English explanations. Stablerail’s policy-as-code engine enforces rules such as dual authorization for high-value transfers, while human-in-the-loop approvals ensure that CFOs and finance teams maintain oversight of emergency decisions. This approach delivers the kind of evidence auditors, boards, and regulators demand - all without delaying critical payments.
The financial consequences of inadequate audit trails are stark: the average fraud case results in a $1.7 million loss, with median losses climbing to $500,000 when owners or executives are involved. Building compliant emergency override protocols supported by robust audit trails isn't just about avoiding fines - it's about safeguarding your organization's financial health and preserving stakeholder trust. Strong audit trails reinforce governance, protect financial integrity, and inspire confidence among stakeholders.
FAQs
What should an emergency override audit trail include?
An emergency override audit trail needs to capture every action and decision made during the event. This includes details like the creation of the intent, checks and policies applied, any flags or alerts triggered, and the justification for overriding controls. Each step must be clearly timestamped and supported by evidence, such as relevant policy clauses, risk assessments, or behavioral analyses. Additionally, it should document who approved the override and their reasoning, ensuring both accountability and compliance are maintained.
How long should override logs be kept for audits?
Override logs need to be kept for a duration that aligns with audit, compliance, and regulatory obligations. This period often ranges from several years to as long as a decade, depending on your organization’s specific policies and the regulations it must follow. Maintaining these logs ensures accountability and provides essential support for detailed audits when required.
How do you prevent overrides and audit logs from being tampered with?
To keep overrides and audit logs secure, it's crucial to implement protected audit mechanisms. These can include using hardware-enforced write-once media to prevent tampering, applying strict access controls so only authorized personnel can view the logs, and setting up continuous monitoring systems that trigger alerts for any unauthorized changes. Together, these steps help ensure the integrity and accountability of audit trails.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


