
Override logs are essential for ensuring accountability and audit-ready stablecoin operations. While blockchain records transactions, it doesn’t capture the decision-making context behind manual overrides - like who approved them, why they were necessary, and what policies were bypassed. This gap can lead to audit challenges, regulatory risks, and weakened governance.
Key takeaways:
Override logs document who authorized a decision, the evidence reviewed, and the policies bypassed.
They address transparency gaps in stablecoin transactions, especially under regulations like the GENIUS Act (2025), which mandates detailed audit trails.
Poor documentation risks audit failures, fraud, and regulatory violations.
Audit-ready logs must be tamper-proof, include timestamps, policy context, and approval roles.
Tools like Stablerail offer pre-transaction checks and detailed audit trails to ensure compliance.
Without override logs, organizations struggle to prove their actions were justified, risking fines and reputational damage. Structured, tamper-proof logs bridge the gap between on-chain transactions and off-chain decision-making, safeguarding both operations and compliance through stablecoin treasury management best practices.
Audit Risks of Poor Override Documentation
Stablecoin Treasury Governance Challenges
Stablecoin transactions settle almost instantly, posing unique challenges for traditional governance practices. For instance, when a USDC payment is processed on-chain, the blockchain records the transaction but leaves out critical details like approval processes, policy exceptions, or supporting documentation. Without centralized workflows, it becomes nearly impossible to trace these approvals or understand the rationale behind them.
The rapid pace of settlement creates a major issue: reactive controls simply don’t work. Unlike traditional bank wires, which offer a window of time to intercept errors, stablecoin transactions are irreversible once broadcasted to the network. This creates a "critical window" where undocumented overrides can lead to fraud, policy breaches, or regulatory violations before anyone has a chance to step in. Beyond governance, this lack of contextual detail also weakens forensic analysis, making it harder to investigate issues after the fact.
Risks of Undocumented Overrides
When override decisions are poorly documented, they undermine the integrity of the audit trail. Auditors rely on detailed records to verify whether controls, like segregation of duties or dual-approval workflows, were followed over time - not just at a single point in time. Without tamper-proof logs showing who authorized an override, what evidence they reviewed, and which policies were bypassed, the forensic value of the audit trail is essentially nullified.
The March 2023 USDC de-pegging event highlights how operational gaps can have ripple effects. When $3.3 billion of Circle’s reserves were temporarily locked at Silicon Valley Bank, USDC’s value dropped to $0.87 on Coinbase. This triggered over 3,400 automatic liquidations on DeFi platforms like Aave and MakerDAO within hours. Despite Circle’s reserves being "100% backed", as confirmed by Deloitte’s monthly attestations, the delay in liquidity and the absence of clear override documentation during the crisis exacerbated the impact across the ecosystem.
Another concern is the centralization risk posed by undocumented overrides. Administrators with elevated permissions can bypass access controls without leaving an audit trail. This undermines the "programmable trust" that makes stablecoins appealing in the first place. Manual interventions that override compliance mechanisms - such as whitelists, transaction limits, or sanctions checks - without proper logging strip organizations of the ability to demonstrate that their actions were justified and not arbitrary.
Regulatory Requirements for Override Controls
In response to these risks, regulators have tightened their expectations around override documentation. Modern regulatory frameworks demand continuous control verification, making well-documented override logs essential for compliance. For example, the GENIUS Act, enacted in July 2025, requires monthly attestations and mandates that stablecoin reserves be held in segregated, bankruptcy-remote accounts. Similarly, the EU’s MiCA regulation imposes daily reserve monitoring and requires stablecoins to maintain a 1:1 backing with high-quality liquid assets.
U.S. regulations like the Bank Secrecy Act (BSA) add further complexity. Transactions exceeding $2,000 that raise suspicion must include documentation explaining the rationale behind the decision. Additionally, the Travel Rule mandates sharing sender and recipient information for transactions over $3,000. When teams override automated risk filters to process urgent payments, structured logs become the only way to prove compliance with these thresholds.
"The future of compliance won't just watch what happens on-chain. It will decide what's allowed to happen in the first place." - Natalia Latka, Head of Regulatory Affairs, ComPilot
This growing emphasis on "compliance-by-design" means that any overrides must be documented with the same level of precision as the automated controls they bypass. Without detailed override logs, organizations cannot demonstrate to auditors that their deviations from policy were authorized, justified, and in line with regulatory standards.
What Auditors Expect from Override Logs
Required Elements in Override Logs
Auditors rely on override logs to ensure governance is transparent and accountable. These logs must clearly identify the decision-maker using wallet addresses, DIDs, or institutional account IDs. This eliminates any uncertainty about who was responsible for the decision.
Precise timestamps and block numbers are another critical requirement. These details establish the exact timing of events, helping auditors understand the context - like network congestion or system conditions - at the moment the override occurred. This level of detail is essential for accurate forensic analysis.
The policy context is equally important. Logs should specify the exact rule that was overridden, such as “maxSinglePayment exceeded by $15,000” or “jurisdictional block for sanctioned address.” Vague labels won’t suffice. Auditors also expect justification and evidence to explain the reasoning behind the decision. This often involves linking off-chain documentation - like wire receipts, PDFs, or vendor quotes - via cryptographic hashes (CIDs) to validate that the override served a legitimate business purpose.
Another key element is authorization and roles. Logs must demonstrate a separation of duties, showing that different individuals handled the submission and approval of the override. For instance, roles like "Submitter" and "Verifier" should be clearly defined to prevent conflicts of interest. Finally, integrity proofs, such as cryptographic signatures or Merkle proofs, ensure that records are tamper-proof and traceable back to the original policy evaluation. Together, these factors not only establish accountability but also provide auditors with the tools they need for thorough testing and investigation.
How Auditors Use Override Logs
Override logs play a vital role in several auditing processes: control testing, forensic analysis, and regulatory compliance.
In control testing, auditors use these logs to confirm whether internal controls - like dual approval workflows or spending limits - were consistently followed over time. This goes beyond attestations, which only verify balances at a specific point.
"An attestation tells you there's $40 billion in the vault on March 31. An audit tells you whether the company has proper processes to keep that $40 billion safe, whether they're following stated policies, and whether their financial statements fairly represent their financial condition." - Torsion.ai
For forensic analysis, override logs are indispensable. They allow auditors to reconstruct the sequence of events and confirm whether controls operated as intended. Detailed records help trace which risk controls were bypassed and assess whether those overrides were justifiable based on the circumstances.
The third major use case is regulatory compliance. When teams override automated sanctions filters or velocity limits to address urgent payments, these logs become the primary evidence proving the organization adhered to regulatory frameworks. Structured and detailed logs ensure that every decision aligns with compliance requirements, providing a clear audit trail.
Why blockchain is not optional and how to create an irrefutable audit trail
How to Build Audit-Ready Override Logs
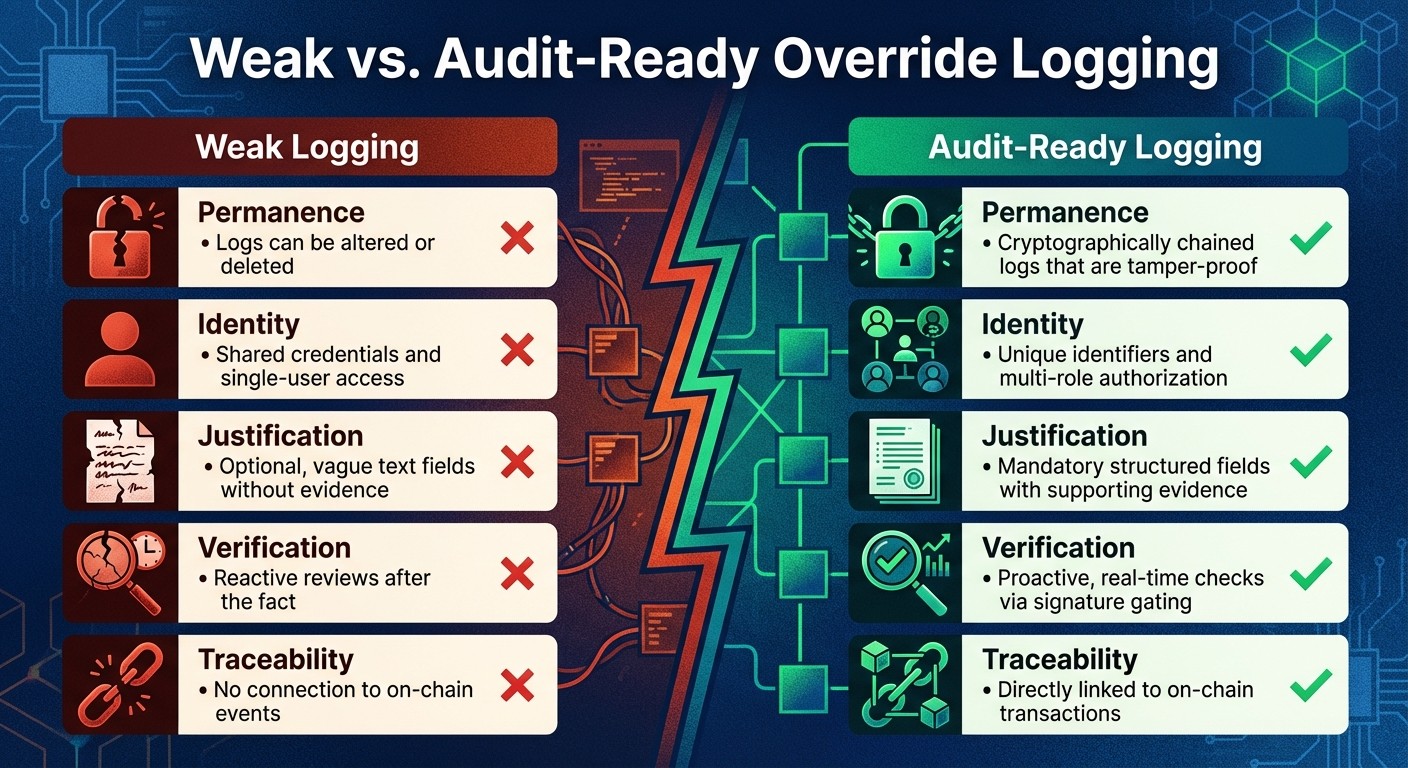
Weak vs Audit-Ready Override Logging: Key Differences for Compliance
To meet the demands of auditors and comply with regulatory standards, override logs need to be built with precision and care.
Core Requirements for Override Logging
Audit-ready logs must be immutable and complete. This means every override record should be stored in a write-once, read-many (WORM) environment, ensuring that no one can edit or delete them after they’re created. Each log should address the "5 Ws" from a builder's perspective:
Who: Use unique identifiers like wallet addresses, decentralized identifiers, or institutional account IDs instead of shared credentials.
What: Clearly document the specific policy rule that was bypassed.
When: Record exact UTC timestamps and, when relevant, blockchain block numbers.
Where: Capture details such as the source IP address, hostname, or request region.
Outcome: Indicate whether the override was successful or failed.
Context matters too. Logs should include the "before" and "after" states of the affected resource, along with a clear, human-readable explanation for the override. For actions involving higher risks - like large fund transfers or changes to authorized signers - require multi-role authorization. This ensures that at least two individuals (a submitter and a verifier) must approve the action, preventing a single person from bypassing controls.
Once these core elements are in place, certain design practices can elevate your logging system to meet audit compliance standards.
Design Practices for Audit Compliance
An audit-ready system doesn’t stop at basic logging. It connects override records directly to blockchain transactions. Linking each off-chain administrative action to its corresponding on-chain transaction hash or settlement proof creates an unbroken chain of evidence - a crucial feature for forensic analysis.
Replace vague free-text fields with standardized justification fields. These should detail the transaction type, method or function selector, and a mandatory explanation for the override. To enhance accountability, attach supporting evidence - like wire receipts, vendor invoices, or audit letters - using cryptographic hashes. This ensures the documentation is verifiable and existed at the time of the override.
To guard against tampering, use strong cryptographic integrity controls, such as Merkleized logs or hash chains. Store these audit logs on secure, centralized servers separate from general application logs. Restrict access with strict role-based access control (RBAC), granting access only to security and compliance teams.
Real-time enforcement is another critical feature. Compliance logic should be applied before a transaction is signed - this is often referred to as "signature gating." By doing so, you ensure that overrides meet pre-defined criteria in real time. As Natalia Latka, Head of Regulatory Affairs at ComPilot, puts it:
"The future of compliance won't just watch what happens on-chain. It will decide what's allowed to happen in the first place."
Weak vs. Audit-Ready Override Logging
To understand the difference between weak and audit-ready systems, consider the key distinctions outlined below:
Audit-ready logging isn’t just about meeting regulations; it’s a safeguard that protects against financial losses and reputational harm.
How Stablerail Strengthens Override Logging
Stablerail transforms override logging from a reactive process into a proactive system, embedding governance directly into payment decision-making.
Pre-Transaction Control for Stablecoin Payments
Instead of waiting until after a transaction settles, Stablerail enforces governance by setting up MPC wallets before a payment is signed. This signature gating approach ensures that every payment intent - whether it's a $50,000 vendor invoice or a weekend transfer flagged for unusual timing - undergoes strict pre-sign checks before being executed on-chain. During this phase, the system performs sanctions screening, enforces policy limits, detects behavioral anomalies, and evaluates counterparty risks. These measures work together to block non-compliant payments from proceeding.
If an override is required - such as when a CFO approves a new vendor address exceeding the $5,000 threshold - human approval is mandatory. The approver uses delegated credentials and must provide a structured justification. This justification is instantly logged, capturing key details like who authorized the exception, which rule was bypassed, when the decision occurred (with precise UTC timestamps), and why the override was necessary.
Audit Trail Features in Stablerail
Every action within Stablerail, from the creation of a payment intent to its final settlement, generates a Policy Trace. This structured record outlines the specific rules triggered and the resulting decision (PASS, FLAG, or BLOCK). For high-value or flagged transactions, the system produces a Risk Dossier, which includes the decision and supporting evidence for review before execution.
After a payment is completed, Stablerail generates tamper-evident Settlement Proofs. These cryptographically link the final on-chain transaction back to the original intent and policy evaluation, creating an unbroken chain of evidence. Through the Audit Log API, auditors can access this chain along with contextual metadata, such as the state of the payment intent before and after execution. This ensures that every override is meticulously documented and easily verifiable.
By combining pre-transaction checks with detailed audit trails, Stablerail ensures that all payment decisions are both secure and transparent.
Override Logging in Practice
Let’s take a real-world example: a finance team processing a $15,000 USDC payment to a new vendor on a Saturday. Stablerail’s system flags the transaction for two reasons: the amount exceeds the $10,000 weekend transfer limit, and the recipient address has no prior payment history.
The CFO steps in to review the Risk Dossier, which includes the vendor invoice (stored as a cryptographic hash), the triggered policy rules (“Weekend transfers over $10k require additional approval” and “New address payments over $5k require CFO approval + verification”), and the results of sanctions screening. After reviewing the details, the CFO provides a structured justification, signs the override, and approves the payment. Stablerail logs the CFO’s identifier, timestamp, and supporting evidence, linking the decision to the on-chain transaction.
When auditors later review the records, they can retrieve the complete decision log through the Audit Log API. This allows them to verify that the override was authorized, justified, and executed according to policy - without needing to manually compile reports.
Conclusion
Override logging isn't just a procedural checkbox - it’s the backbone of audit readiness in stablecoin treasury operations. For finance teams handling on-chain payments, every exception to policy must be recorded with care, much like in traditional banking. Without detailed logs capturing who authorized an override, which rule was bypassed, when it occurred, and why it was necessary, audits can quickly unravel. This level of documentation sets the stage for governance that anticipates issues rather than reacting to them.
The move from reactive to proactive compliance transforms the game. Instead of piecing together decisions after the fact, structured logging systems integrate governance directly into the transaction process.
"On-chain policy enforcement turns that sequence on its head. Instead of catching non-compliant activity once it's visible, it embeds the rule where the risk originates: inside the transaction logic itself".
This shift reframes compliance as a strategic advantage rather than a bureaucratic hurdle, especially as regulators increasingly demand compliance mechanisms that operate within the transaction itself.
The stakes couldn’t be higher. The rapid growth of stablecoin transactions has brought intense regulatory scrutiny under frameworks like the GENIUS Act and MiCA, which require systems capable of freezing assets and maintaining detailed audit trails. Organizations that adopt robust override logging practices now will be better equipped to navigate these demands, ensuring market access, regulatory stability, and operational integrity.
Stablerail exemplifies this forward-thinking approach. By documenting every override decision with cryptographic precision - linking CFO approvals to specific policy violations, timestamps, and supporting evidence - the platform creates tamper-proof audit trails that regulators and auditors expect. When compliance is built into the infrastructure rather than treated as an afterthought, finance teams gain both efficiency and accountability. This combination of pre-transaction controls and tamper-evident records reinforces the audit preparedness highlighted throughout this discussion.
The future of stablecoin governance will belong to organizations that prioritize override documentation as much as the transactions themselves. Structured logging systems not only safeguard against audit failures but also establish the operational trust needed to scale treasury operations with confidence.
FAQs
Why are override logs essential for stablecoin compliance and audit trails?
Override logs are essential for maintaining compliance and bolstering audit readiness by creating a secure, unalterable record of actions. These logs capture critical details such as who overrode a policy, why the override occurred, and the precise timestamp, ensuring full accountability for every decision made.
This thorough audit trail allows finance teams to provide clear evidence of compliance to auditors and regulators while strengthening internal controls. By offering a reliable record of decision-making, override logs promote transparency and build confidence in stablecoin treasury operations.
How do override logs improve the auditability of stablecoin transactions?
Override logs play a key role in maintaining transparency by recording every manual decision made during a transaction. These logs capture details like who initiated the override, the reason behind it, and relevant policy references along with timestamps. This creates a clear, tamper-proof trail of evidence, ensuring accountability and compliance in stablecoin payment processes.
How do override logs ensure audit readiness?
Override logs are built to meet audit standards by documenting a tamper-evident timestamp, the approver's identity, and a plain-English explanation that directly ties to the relevant policy rule. Each log connects to the original transaction intent and approval record, backed by unchangeable evidence. This creates a clear and reliable audit trail for every override action.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


