
Audit-ready self-custody ensures organizations maintain full control over their digital assets without relying on third parties. This approach minimizes risks like unauthorized access, insider threats, and operational errors. To meet audit standards, self-custody systems must integrate strict controls, automated policy enforcement, and detailed transaction records. Here's what you need to know:
Self-Custody Defined: Your organization holds private keys and signing authority, ensuring assets remain secure and outside third-party balance sheets.
Why It Matters for Audits: Auditors require proof of compliance, including documented rules, approvals, and risk assessments for every transaction.
Key Features of Audit-Ready Systems:
Policy Enforcement: Converts business rules into automated controls, blocking transactions that don't meet set criteria.
MPC Wallets: Multi-party computation (MPC) distributes signing authority, reducing single points of failure.
Pre-Transaction Checks: Includes risk screening, spending caps, and transaction simulations.
Detailed Audit Trails: Records every decision, ensuring transparency and accountability.
Self-custody systems with these features provide a secure, efficient way to manage stablecoin transactions while meeting regulatory and audit requirements.
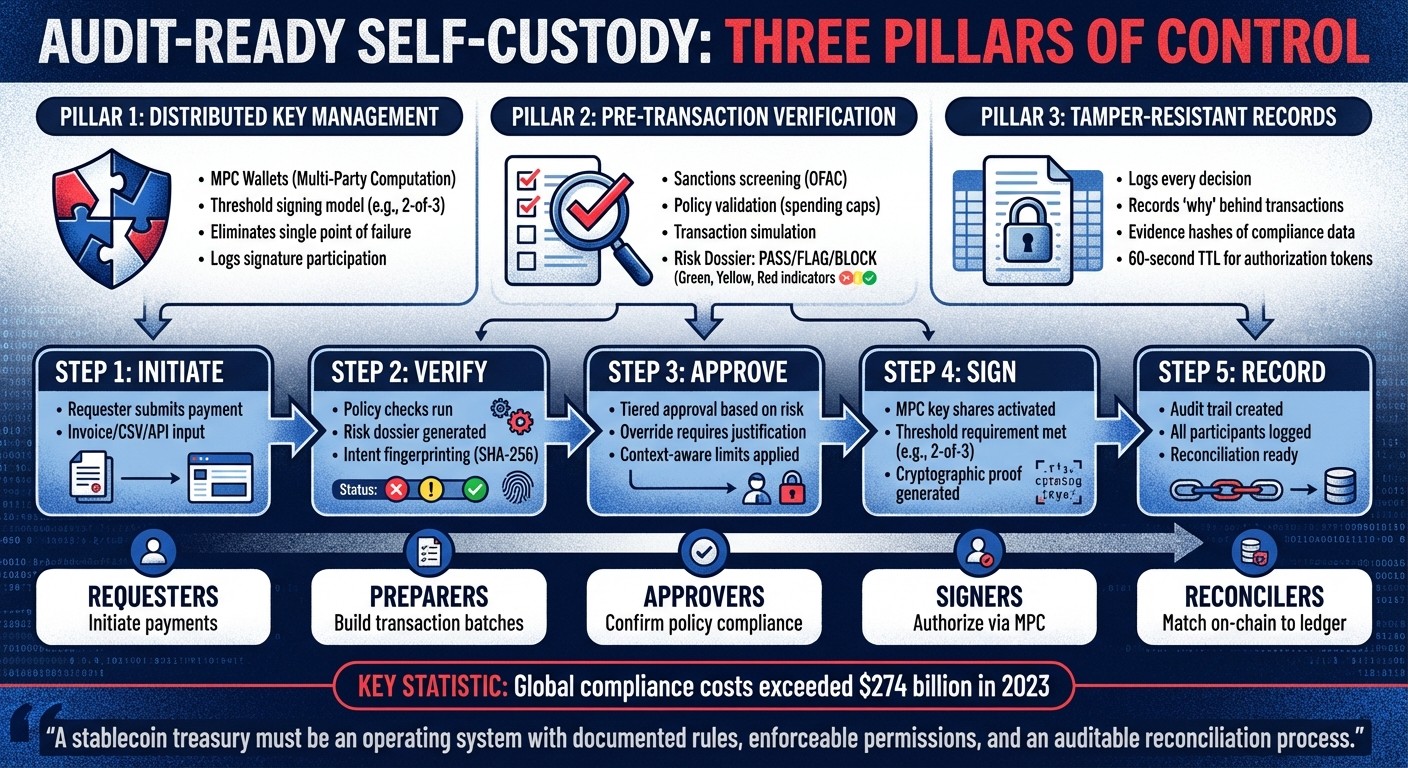
Audit-Ready Self-Custody System Architecture and Transaction Flow
What Makes a Self-Custody System Audit-Ready
An audit-ready self-custody system rests on three key pillars: distributed key management to prevent unilateral control, pre-transaction verification to ensure every payment is screened before approval, and tamper-resistant records that document every decision. Without these, your treasury's controls can't be verified by auditors, and accountability becomes difficult for regulators to trace. Let’s break down these layers.
MPC Wallets and Transaction Security
Multi-Party Computation (MPC) wallets replace single private keys with distributed key shares using a threshold signing model (t/n). For instance, in a 2-of-3 setup, two out of three authorized parties must collaborate to generate a valid signature. This structure ensures no single individual - whether it's the CFO or another keyholder - can act alone. By eliminating the "single point of failure", MPC addresses a critical weakness auditors often flag in traditional wallet systems.
One standout feature of MPC is its signature participation record. Every transaction logs which key shares were involved, showing exactly who contributed to the signature. This creates an accountability trail that proves your organization enforces separation of duties at the cryptographic level, not just through written policies.
Additionally, MPC wallets paired with programmable guardrails prevent blind signing. Before any key share is activated, the system validates the transaction against your business rules. It also logs the participants involved, creating cryptographic proof of multi-party authorization.
Pre-Transaction Checks and Verification
Securing key participation is just one part of the equation. Ensuring transaction integrity requires thorough pre-sign verification. Every payment undergoes checks such as sanctions screening (e.g., OFAC lists), policy validation (spending caps, approved vendors), and transaction simulation to detect malicious payloads or errors in addresses. For example, systems like Stablerail generate a Risk Dossier with a clear verdict - PASS, FLAG, or BLOCK - accompanied by plain-English explanations that reference specific policy clauses and timestamps.
Advanced tools like eth_call preview transaction outcomes, identifying potential issues like incorrect addresses, duplicate payments, or hidden internal calls. Notably, Ethereum's Pectra upgrade on May 7, 2025 (epoch 364032) introduced EIP-7702. This allows Externally Owned Accounts (EOAs) to execute code from smart contracts, enabling spending controls to be enforced natively before funds leave the wallet.
Some systems also employ intent fingerprinting, which creates a SHA-256 hash of transaction metadata (chain, asset, recipient, amount). If any modification occurs between verification and signing, the hash mismatch blocks the transaction. This "fail-closed" approach ensures that if a policy engine or compliance service is unavailable, the system halts the transaction instead of bypassing critical checks.
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money." – Stablerail
Audit Trails and Transaction Records
Comprehensive audit trails provide "CFO-grade" evidence that your organization maintains strict oversight of on-chain assets. These records log details such as the initiator, timestamp, policy checks, approvals, and MPC participation, offering transparency for audits. This eliminates the need for manual reconstructions - finance teams can demonstrate control without relying on spreadsheets or Slack threads.
A vital component of these records is capturing the "why" behind each transaction. If a policy override occurs (e.g., bypassing a spending cap for an urgent payment), the system requires a recorded justification. This rationale becomes part of the permanent record, enabling auditors to trace decision-making months or even years later.
Some systems also store evidence hashes of external compliance data, such as the specific version of the OFAC sanctions list used during screening. This proves that transactions were checked against the active list at the time. Additionally, a 60-second Time-to-Live (TTL) for authorization tokens ensures that transaction intent remains secure and cannot be altered between policy approval and final signing.
These detailed records form the backbone of a policy-as-code framework, ensuring every transaction is fully traceable and auditable.
Policy-as-Code: Turning Business Rules into Enforceable Controls
Policy-as-code translates governance requirements into machine-readable rules, ensuring compliance is enforced at every step of a transaction. Instead of relying on manual reviews or after-the-fact audits, these automated safeguards block non-compliant payments before they even reach the approval stage. This framework aligns seamlessly with the pre-transaction verifications and audit trail mechanisms previously discussed, reinforcing an audit-ready operational model.
Writing Policies That Match Your Business Rules
To be effective, policies must transform business requirements into clear, actionable rules. For example, a policy might mandate CFO approval for payments exceeding $5,000 to a new address or restrict asset usage to USDC on approved blockchain networks. These policies are built on two key components: rules, which determine whether an action is permitted or denied, and conditions, which are boolean expressions evaluated against transaction details.
A secure policy framework should always default to "deny." If a transaction doesn’t meet any defined criteria or involves an unhandled scenario, the system automatically blocks it. For example, maintaining an approved vendor address list ensures any changes trigger an immediate escalation for review.
Policies should also account for historical data to enforce cumulative limits, such as daily spending caps or transaction frequency per user or account. While a single transaction under $10,000 might be allowed, an account attempting five such transfers in an hour could signal unauthorized activity, triggering a block or review.
Applying Policies at Each Transaction Stage
The system enforces policies through a two-step process. First, it evaluates spending rules and reserves the necessary budget. Then, it verifies the transaction’s intent using SHA-256 fingerprinting before signing. Pre-flight simulations, like those conducted with eth_call, help identify potential issues early. If a transaction fails at any stage, it’s immediately stopped.
Stablerail’s workflow offers a clear example of this approach. When a transaction intent is created - whether through an invoice PDF, payout CSV, or API - dedicated agents generate a risk dossier. This dossier provides a verdict: PASS, FLAG, or BLOCK, along with plain-English explanations tied to specific policy clauses and timestamps. Only after all checks are cleared and necessary approvals are logged do the MPC (multi-party computation) key shares proceed with signing.
When to Require Human Review
While automated rules handle the majority of transactions, certain scenarios still require human oversight. Manual review is typically triggered for transactions that exceed a set dollar threshold, involve high-risk asset types, or target unapproved destination addresses. For instance, internal transfers between subsidiaries might auto-approve, but payments to a new vendor would likely require manual verification.
Escalation logic ensures routine, low-risk transfers are processed automatically, while exceptions are routed to additional co-signers. For high-value transactions or payments to unapproved recipients, companies often introduce automatic delays - such as a 4-hour cool-off period - to reduce the risk of errors. This delay gives finance teams time to validate urgent requests before bypassing standard controls.
"The Co-Signer serves as an automated signing mechanism that securely authorizes transactions based on predefined rules and policies, eliminating the need for manual intervention." – Vaultody
When a flagged transaction is approved, the system should require a documented reason for the override, ensuring transparency and accountability.
Approval Workflows and Access Controls
Approval workflows and access controls are critical for maintaining audit readiness. By combining automated policy checks with detailed audit trails, these workflows ensure that every transaction is reviewed by the right authority. The aim is straightforward: every decision is documented, every action is justified, and every step is traceable.
Setting Up Approval Tiers and User Roles
Approval structures should align with the level of transaction risk. For example, low-risk, routine transfers - like internal wallet sweeps - can often be approved by a single authorized signer. However, high-value or high-risk transactions, such as payments over $100,000 or transfers to new beneficiaries, should trigger escalated approval processes. These might include additional approvers or multi-signature requirements.
Context-aware limits add another layer of precision. A $15,000 payment to a trusted vendor might auto-approve during business hours but could require a CFO's review if sent to a new address on a weekend. Stablerail’s policy console allows finance teams to set explicit rules like, “Weekend transfers over $10,000 require additional approval,” ensuring these controls are applied automatically before a signature is even requested.
To ensure accountability, the most effective systems implement a five-role model:
Requesters: Initiate payment requests with supporting documentation.
Preparers: Build transaction batches and verify policy compliance.
Approvers: Confirm compliance with policies and limits.
Signers: Authorize execution using cryptographic signatures via MPC key shares.
Reconcilers: Match on-chain activity with accounting ledger entries.
Compliance officers and auditors should have read-only access to logs and exports, ensuring transparency without granting operational signing authority.
These clearly defined roles provide a framework for documenting any policy overrides, as discussed below.
Recording Override Decisions
Sometimes, business needs require moving forward with a flagged transaction. In such cases, the system must document the rationale behind the override. This transforms what might appear as a policy breach into a well-supported business decision.
Stablerail’s workflow enforces this automatically. If a transaction is flagged - perhaps due to a first-time destination address or an unusually large amount - the approver cannot proceed without providing a justification. This justification, combined with the approver’s identity, forms a comprehensive audit trail that can stand up to scrutiny from boards, banking partners, and regulators.
For example, consider a $250,000 payment to a new vendor. While this might trigger multiple policy warnings, a CFO’s override note citing a signed contract, vendor onboarding documents, and confirmation of a test transaction turns the decision into a defensible action. Without this context, the same transaction could appear as a control failure. Every transaction should generate a proof-of-control receipt outlining what was paid, why it was approved, who authorized it, and the risk assessment at the time of execution.
With overrides properly documented, separating duties becomes the next line of defense.
Separating Duties to Reduce Risk
Separation of duties (SoD) is a cornerstone of secure financial systems. No single individual should have control over initiating, approving, executing, and reconciling a transaction. For instance, the person who creates a transaction should not be allowed to approve it. This division reduces the chances of errors and prevents fraud by requiring multiple, independent checkpoints.
Multi-party computation (MPC) strengthens this principle at a cryptographic level. Instead of relying on a single private key that could be compromised, signing authority is distributed across multiple key shares held by different individuals or systems. Stablerail’s MPC wallets ensure that no single party - including Stablerail - can unilaterally execute a transfer.
For businesses managing $1 million to $50 million in annual stablecoin transactions, implementing tiered approval hierarchies with clear role separation isn’t just advisable - it’s essential. When paired with policy-as-code enforcement, these measures ensure that governance rules are applied programmatically at the account level, eliminating reliance on manual checklists that can be overlooked or bypassed.
Conclusion
Integrated controls are transforming treasury management, shifting the focus from simple storage to active governance. Audit-ready self-custody systems now combine MPC-based wallets - which distribute signing authority to eliminate single points of failure - with instant policy checks and tamper-resistant audit trails. These features ensure every transaction aligns with programmable business rules before execution. This makes compliance not just a task but a continuous and verifiable process.
Each transaction generates cryptographic proof of control, documenting critical details like what was paid, why, by whom, and the policy verdict at execution. Such evidence is crucial when defending decisions to boards, banking partners, or regulators. Additionally, controls like separation of duties and fail-closed logic ensure funds cannot be moved unilaterally and that system failures default to blocking transactions, enhancing security against potential threats.
For businesses handling large stablecoin volumes, policy enforcement is non-negotiable. As Stablecoin Insider aptly put it, "A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process". This approach ensures that every transaction is evaluated within a robust control framework, blending the reliability of traditional banking with the speed of blockchain settlements.
Key measures like tiered approval workflows based on transaction risk levels, policy-as-code for programmatic enforcement of business rules, and thorough reconciliation processes that link blockchain transactions to business purposes and ledger entries form the backbone of this system. These controls not only prepare organizations for audits but also enhance resilience against insider threats, social engineering, and the dangers of blind signing.
With global compliance costs surpassing $274 billion in 2023, adopting real-time programmatic controls offers a more efficient and defensible way to manage digital asset treasuries. Platforms like Stablerail demonstrate how these controls can seamlessly integrate, providing finance teams with a secure, auditable, and efficient operating system for managing stablecoins.
FAQs
What controls make self-custody audit-ready?
Self-custody achieves compliance through policy-as-code governance, pre-sign validations, and meticulous record-keeping. Policies, such as transaction limits or approval rules, are automatically enforced by machines before any signing occurs. Pre-sign validations involve steps like sanctions screening, anomaly detection, and risk scoring, all accompanied by clear, plain-English explanations to ensure transparency. Additionally, human-in-the-loop approvals document every decision - whether it's policy creation, checks, overrides, or signatures - building a detailed audit trail that bolsters accountability and supports regulatory compliance.
How does MPC stop one person from moving funds?
MPC, or Multi-Party Computation, adds a layer of security by dividing signing authority into multiple distributed key shares. This means no single person has the power to authorize a transfer on their own. By requiring multiple parties to collaborate, it ensures tighter control and reduces the risk of unauthorized access or fraud.
What should a crypto transaction audit trail include?
A crypto transaction audit trail needs to capture every step and decision made throughout the process. This includes transaction intent creation, such as invoices or payout instructions, and pre-sign checks, like sanctions screening, policy enforcement, and anomaly detection. Any flags or overrides that arise must also be documented. Additionally, it should log all human approvals, overrides, and signatures, complete with timestamps and supporting evidence. This thorough documentation ensures clear accountability and compliance for auditors, regulators, and boards.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


