
Managing treasury access securely is critical, especially in high-stakes environments like stablecoin operations. Role-Based Access Management (RBAC) ensures team members only access what they need, reducing risks like fraud or policy violations. Here's a quick summary of how to set up RBAC effectively for your treasury:
Define Roles: Assign clear responsibilities (e.g., Requester, Approver, Signer, Reconciler) and enforce separation of duties so no one person controls the entire process.
Set Permissions: Use the least privilege principle, limiting access to specific tasks, assets, and networks. Implement multi-signature thresholds and transaction value caps for added security.
Integrate Controls into Workflows: Automate policy enforcement with tools like Stablerail, which handles risk checks, sanctions screening, and policy validation before transactions are approved.
Test & Validate: Simulate scenarios to ensure controls work as intended, including emergency procedures like halting treasury activity during key compromises.
Monitor & Update: Continuously audit roles, permissions, and workflows. Use real-time alerts for unusual activity and regularly review policies to stay secure.
This structured approach minimizes errors, ensures compliance, and protects your treasury from potential breaches.
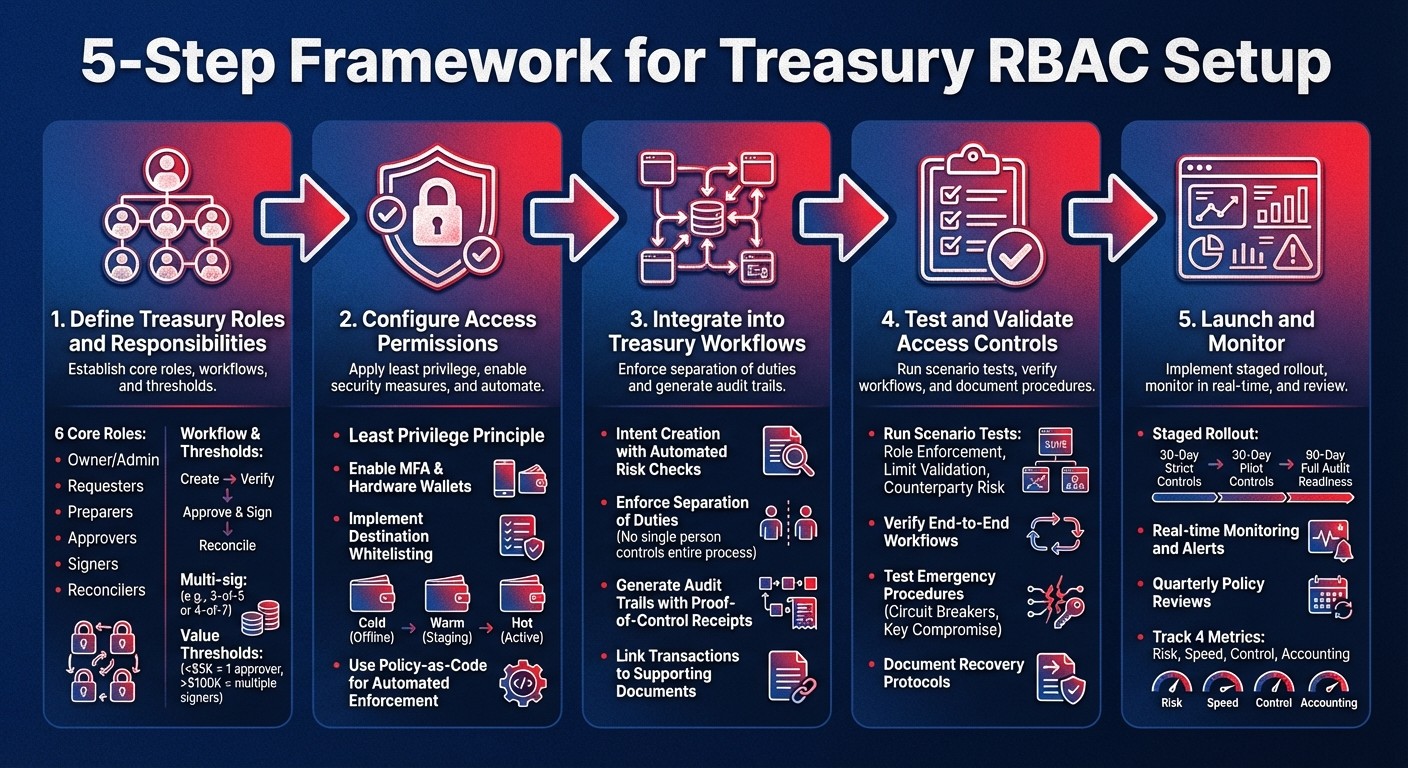
5-Step Framework for Treasury Role-Based Access Control Setup
Step 1: Define Treasury Roles and Responsibilities
Core Roles in Stablecoin Treasury Management
Establishing clear roles and following stablecoin treasury management best practices is key to maintaining secure and efficient operations. This begins with a Separation of Duties (SoD) approach, ensuring no single person has unchecked control over the entire process. By assigning specific roles, you create a structure that supports policy enforcement and simplifies audits.
In stablecoin treasury management, responsibilities are divided into two main levels: organizational (team management and billing) and wallet operations (funds and policy management). At the wallet level, six essential roles form the operational framework:
Owner/Admin: Oversees wallet settings, creates policies, and manages signers. Typically, this role is held by a CFO or Treasury Director.
Requesters: Initiate payment requests and provide supporting documentation, such as invoices or purchase orders.
Preparers: Assemble transaction batches while ensuring compliance with internal policies and documentation standards.
Approvers: Validate the business purpose, ensure policy adherence, and confirm the legitimacy of counterparties before approving transactions.
Signers: Use cryptographic keys to authorize and broadcast transactions after all approvals are in place. For security, they should always use hardware wallets instead of browser extensions.
Reconcilers: Have read-only access to balances and transaction logs to match on-chain activity with the general ledger. They cannot move funds.
The workflow follows a structured process: Create (Requester) → Verify (Policy Engine/Approver) → Approve & Sign (Signer) → Reconcile (Auditor). This ensures every payment is justified, documented, and overseen at multiple levels, minimizing the risk of errors or fraud.
Align Roles with Business Functions
Once core roles are defined, the next step is to integrate them into your organization’s structure. Assigning these roles to the appropriate individuals ensures smooth implementation. For instance, the CFO often acts as the Owner, while the CEO might retain Admin rights for oversight. Finance team members can be given tailored roles with specific spending limits - for example, a procurement manager might approve vendor payments up to $10,000 without requiring further sign-offs. Meanwhile, accounting teams should have view-only access for reconciliation purposes.
For added security, consider implementing multi-signature thresholds. These thresholds require multiple signers to authorize high-value transactions, balancing security with operational efficiency. A common setup might involve a 3-of-5 or 4-of-7 configuration, where operational leads (like the CFO or Treasurer) are included alongside offline hardware wallets held by board members. This setup not only prevents unauthorized access but also ensures continuity in emergencies.
Additionally, establish transaction value thresholds to determine approval requirements based on payment size. For example, routine payments under $5,000 might only need one approver, while transfers exceeding $100,000 could require multiple signers and a mandatory cooling-off period. This delay helps mitigate risks like social engineering attacks. These thresholds should align with your organization’s risk appetite and operational priorities.
Treasury Tips | How to Add or Manage Users & Permissions
Step 2: Configure Access Permissions
Once roles are clearly defined, the next step is to translate those roles into actionable permissions. This ensures your treasury remains secure while still allowing your team to operate efficiently.
Apply the Least Privilege Principle
The key here is simple: give each role only the access it needs to perform its tasks - nothing more, nothing less. As Stablecoin Insider puts it, "Access should be granted only for the smallest set of actions needed to do a job". This means moving away from broad labels like "Admin" or "Member" and assigning more precise, task-specific permissions.
For instance, team members like accountants or external auditors may only need read-only access to review financial data. On the other hand, operational roles, such as a procurement manager, might require spending permissions - but with limits. For example, you could set a $1,000 cap per transaction for that role.
It’s also essential to restrict access to specific assets and networks. A finance team member, for example, might only be allowed to send USDC on Ethereum or Base. To further secure transactions, implement destination whitelisting. This involves maintaining a "Golden Source" of approved vendor addresses, ensuring any attempt to send funds outside this list is blocked or escalated for executive approval.
For handling high-value funds, consider a tiered wallet system:
Cold wallets: For long-term reserves with the highest security measures.
Warm wallets: For operational funds with moderate security.
Hot wallets: For automated payments, where speed is prioritized.
Stricter approval processes should apply as the value of the funds increases. Regularly review access permissions to ensure they’re up to date, especially when team members change roles or leave the organization.
With these permissions in place, technical essential controls can strengthen your treasury's defenses even further.
Enable Security Hardening Features
Technical safeguards transform your permission policies into enforceable security measures. Start with identity and access management tools like Single Sign-On (SSO), System for Cross-domain Identity Management (SCIM), and mandatory Multi-Factor Authentication (MFA) across your treasury platform.
For transaction signers, physical security measures are a must. Require tools like YubiKeys or dedicated hardware wallets (e.g., Ledger or Trezor). This step is crucial, especially considering that nearly 80% of companies reported payment fraud incidents in 2024.
Multi-signature controls add another layer of security. For routine operations, a 2-of-3 approval scheme works well, while treasury reserves might require a stricter 3-of-5 model. For larger transactions, time-lock contracts can be introduced, adding a delay (commonly around 4 hours) to give your team time to catch and stop any fraudulent activity.
Platforms like Stablerail further enhance security with MPC-secured vaults, which distribute key management among multiple parties. This ensures your treasury remains non-custodial and resilient. Additionally, Stablerail enforces strict separation of sandbox, staging, and production environments, reducing the risk of configuration errors affecting live operations.
To complement these technical measures, programmatic governance ensures your rules are consistently enforced.
Set Policy-as-Code Rules for Access Control
Policy-as-code allows treasury policies to be automatically enforced by the system. As Stablerail notes, "Policy-as-code rules are enforced programmatically. Even the CEO cannot bypass the code". This ensures governance is consistent, no matter who initiates a transaction.
Use velocity limits and threshold step-ups to require extra approvals or waiting periods for high-value transactions. Time-based restrictions can also reduce risks, such as blocking transfers during off-hours (e.g., 10:00 PM to 6:00 AM) or requiring additional approvals during high-risk periods.
To counter social engineering risks, introduce automatic delays for transactions to new beneficiary addresses. Address-change locks can also help prevent fraud by enforcing a waiting period when a vendor’s payment address is updated. Additionally, require a business reference ID - like an invoice number - for every transaction to ensure it aligns with a legitimate business purpose.
Stablerail’s Policy Console simplifies this process by allowing rules to be written in plain language. These rules are enforced before any transaction is signed, with pre-flight checks that include sanctions screening, policy validation, and anomaly detection. The system generates a detailed Risk Dossier (e.g., PASS, FLAG, or BLOCK), providing clear, evidence-based explanations for every decision.
Step 3: Integrate Role-Based Access into Treasury Workflows
Once roles are set and permissions are in place, the next move is weaving these controls into your treasury workflows. The goal? To ensure every payment navigates a secure, traceable path from initiation to execution. This step builds the backbone of a structured and secure treasury process.
Intent Creation and Approval Workflow
Every transaction should begin with an intent - a document or digital record that includes the recipient’s address, the amount, the business rationale, and a unique identifier. Before moving forward, validate this intent against established policy-as-code rules. Once that’s done, notify the appropriate approvers.
Stablerail offers a practical example of this process. When an intent is created, their system uses specialized agents to run automated checks like sanctions screening, policy validation, anomaly detection, and counterparty risk scoring. The result? A detailed Risk Dossier with a verdict (PASS/FLAG/BLOCK) and a clear explanation in plain language. Only after these automated checks are complete does the request go to approvers, who receive all the information they need to make a sound decision.
The approval process itself follows a structured, multi-step logic. Transactions move through states - such as Pending, Approved, and Executed - based on predefined thresholds. For simple transactions, approvals might require fewer steps, while higher-risk payments may demand stricter controls, like a 3-of-5 approval setup, to ensure thorough oversight.
A clear division of responsibilities is essential to further protect your treasury workflows.
Enforce Separation of Duties
A strong Separation of Duties framework is key to preventing any single person from having unchecked control over payments. Your system should ensure that no individual can single-handedly request, approve, and execute a transaction.
Responsibilities should be divided into distinct roles:
The Requester initiates the payment and provides supporting documentation.
The Approver ensures the payment aligns with company policies.
The Signer uses cryptographic methods to authorize the transaction.
The Reconciler verifies that blockchain activity matches internal records.
By keeping these roles separate, you prevent conflicts of interest. For example, someone who creates a payment intent shouldn’t have the authority to approve or sign it. For particularly sensitive tasks - like adding a new address to an allowlist or modifying signer groups - implement dual control, requiring approvals from senior executives or other high-level roles.
Generate Audit Trails for Compliance
Every action in your treasury workflow should leave a traceable record. As Vaultody highlights:
"Audit readiness is a foundational requirement for treasury teams managing digital assets".
This means documenting not just the transaction but also its full context: who initiated it, who approved it, what risk checks were completed, and whether any policies were bypassed.
Stablerail takes this a step further with its "Proof-of-Control" receipts. These receipts document the What, Why, Who, and Risk Verdict for every transaction and are designed to meet the needs of auditors, boards, and regulators. They include details like which devices or roles contributed to MPC (multi-party computation) signatures, timestamps for governance policy changes, and results from pre-flight checks like freeze-risk alerts or flagged addresses.
To tighten compliance even more, link every transaction to supporting documents. If an exception to policy occurs, require a written explanation for the override. Regular reconciliations are also crucial - compare on-chain balances with internal records, and ensure logs include timestamps and flags for any discrepancies. This keeps your records organized and always ready for audits.
Step 4: Test and Validate Access Controls
Before launching your system, it's crucial to ensure that your access controls function as intended. Simulate real-world scenarios in a controlled setting to identify potential vulnerabilities before they become actual risks.
Run Treasury Scenario Tests
Conduct tests to confirm that roles and permissions are properly enforced. For example, simulate an unauthorized action, such as an auditor attempting to initiate a transfer. The system should block the action and log the attempt for review.
Next, test threshold logic and risk-screening processes. For instance, if your policy mandates CFO approval for transactions exceeding $100,000, initiate a $150,000 transfer and verify that the system escalates the request appropriately. Similarly, test transfers to non-whitelisted addresses to ensure they either trigger a lock or initiate a mandatory cool-off period.
Sanctions and risk screening should also be tested. Simulate transactions involving flagged entities or first-time counterparties to confirm that the system blocks or flags these actions before they proceed.
Emergency scenarios need attention too. Test whether your "circuit breaker" can halt all treasury activity in cases like a compromised signer key. As Trail of Bits emphasizes:
"The strongest security control isn't any single technical measure, but the organizational muscle memory that translates 'that happened to them' into 'here's what we changed to prevent it from happening to us'".
Once you've verified these individual scenarios, proceed to test the entire payment workflow.
Verify End-to-End Workflows
After confirming that specific scenarios work as expected, validate the entire payment process. Start with creating a payment intent, run it through automated risk checks, and route it to the correct approvers. Ensure that separation of duties is maintained throughout - no single individual should have the power to request, approve, and execute a transaction.
Use transaction simulation tools to preview outcomes before signing. For example, Stablerail's pre-flight Risk Dossiers provide PASS/FLAG/BLOCK verdicts based on your policy limits and anomaly checks, giving approvers a complete picture before unlocking keys. These tools help catch hidden issues, like malicious state changes in smart contracts, that could slip past manual reviews.
Also, automate reconciliation between on-chain balances and internal ledgers. Any discrepancies beyond defined tolerance levels should trigger immediate alerts, allowing you to detect unauthorized transfers or policy violations early.
Once the end-to-end workflow is validated, focus on documenting emergency protocols.
Document Emergency Procedures
Prepare for failure scenarios by clearly defining recoverable and non-recoverable situations. For example, losing one signer but maintaining quorum is recoverable, while losing multiple signers and failing to reach quorum is not.
Document step-by-step procedures for replacing compromised signer keys or updating multisig thresholds. These procedures should ensure smooth operations even during key rotations. Past incidents highlight the critical need to confirm that approval thresholds prevent a small group of compromised signers from draining the treasury.
Additionally, outline escalation paths and evidence preservation protocols for post-incident reviews. If your system includes emergency overrides, require that each override includes a recorded reason to maintain a clear audit trail. As Safe{Wallet} advises:
"If recovery is not provable in advance, it does not exist when it matters".
Finally, conduct regular internal drills to test these procedures. The goal is to ensure that your team can respond swiftly, consistently, and with accountability when emergencies arise.
Step 5: Launch and Monitor Role-Based Access Setup
Once your end-to-end testing is complete, it’s time to launch the system and keep a close eye on its performance. Remember, launching isn’t just a one-time event - it’s the beginning of an ongoing process that demands regular monitoring and updates to ensure your treasury stays secure and compliant.
Complete the Go-Live Checklist
Before launching, confirm that authorized actions, approved roles, and auditable records are in place. If you can’t confidently check off all three, it’s better to hold off until you can.
Start with a staged rollout:
Begin with strict controls and daily reconciliations for the first 30 days.
Introduce a small user group for pilot transactions over the next 30 days.
Aim for full audit readiness and scalability by the 90-day mark.
A Shadow Audit can help uncover potential issues - gaps in separation of duties, missing approval thresholds, or incomplete audit trails - before you go live. Fixing these problems early on is much simpler than addressing them after real funds are in play. Also, ensure your onboarding and offboarding processes are formalized, with approvals and timestamps documented for every change.
Monitor and Audit Access Controls
Once live, the focus moves to ongoing monitoring and auditing. Leverage tools like Tenderly, Forta, or OpenZeppelin Defender to receive real-time alerts for unusual activities - such as large transfers, wallet balance breaches, or unexpected changes to destination addresses. Set triggers for critical events like signer set modifications, new address additions, and sudden increases in network fees.
Stablerail’s Risk Dossiers provide immutable audit trails for every payout, detailing the transaction’s creation, approval history, and governance changes . To gain deeper insights, integrate treasury monitoring with SIEM systems like Splunk or Datadog, which analyze signing attempts and policy decisions across your organization.
For high-value transfers (e.g., over $100,000), implement a cool-off period of at least four hours. This buffer allows monitoring systems and personnel to detect and respond to potential threats, such as social engineering attempts. Additionally, use circuit breakers to halt minting or redemptions if a critical balance mismatch is detected.
Review and Update Access Policies
Ongoing monitoring should be paired with regular policy reviews. Schedule quarterly assessments to reevaluate role structures and access policies as your team grows and operations evolve . Policies should be version-controlled and clearly defined so they can be tested effectively.
Automate user lifecycle management with SCIM, syncing users directly from your Identity Provider. This ensures that when someone leaves your organization, their treasury access is automatically revoked. Also, perform quarterly cryptographic key rotations to minimize risks from potential compromises, and document all changes with proper approvals and timestamps.
Regular internal drills are essential to test your incident response plans. Simulate scenarios like compromised keys or stolen funds to ensure your team is prepared. Enforce the principle of least privilege by periodically revoking permissions to critical assets, ensuring that users only have access to what’s essential for their roles. Every policy update should be documented, and post-action reviews conducted to evaluate effectiveness.
Track your success using these four metrics:
Risk: Eliminate single-actor authority.
Speed: Ensure efficient approval cycles.
Control: Maintain comprehensive policy coverage.
Accounting: Measure how quickly balances can be validated during month-end close .
These benchmarks will help you determine whether your role-based access setup is working as intended or if adjustments are needed.
Conclusion
Introducing role-based access to your stablecoin treasury creates a system designed to protect your organization from unilateral control while enabling fast and secure transactions. By following the five-step framework - defining roles, configuring permissions, integrating workflows, testing controls, and monitoring - you can ensure that no single person has the ability to create, approve, execute, and reconcile a transaction. This approach blends the principles of separation of duties and least privilege, meaning even your CFO won’t be able to override programmatic spending limits or bypass whitelists.
Stablerail enhances this process by acting as the "brain on top" of your custody layer. With its "copilot, not autopilot" philosophy, it ensures that while agents handle automated risk screening and policy enforcement, humans retain the final say by signing off on transactions. This balance provides both security and control over your funds.
Cyber threats are constantly evolving, outpacing traditional annual security updates. To stay protected, your role-based access system must remain dynamic. This includes conducting regular policy reviews, managing user lifecycles through SCIM automation, and implementing real-time monitoring to detect unusual activity before it escalates into a breach. The Radiant Capital breach in October 2024, where a weak 3-of-11 multisig setup resulted in a $53 million loss, is a stark reminder of the importance of rigorous testing and continuous updates.
Finally, measuring the effectiveness of these controls is key. Use metrics like eliminating single-actor authority (risk reduction), maintaining swift approval cycles (efficiency), achieving broad policy enforcement (control), and reconciling balances during month-end close (accounting accuracy). These indicators will help ensure your treasury remains secure and efficient.
FAQs
What’s a good default role setup for a small treasury team?
A well-thought-out role setup for a small treasury team strikes a balance between security and efficiency. A common approach involves two primary roles:
Admin: This role has full control, allowing the management of policies, approvals, and access. It’s best suited for a CFO or a treasury lead who oversees the team.
Member: This role is typically view-only, designed for operational staff or auditors who need to monitor activities without making changes.
For added security, you can introduce custom roles with approval workflows and audit trails. These setups can limit high-risk actions and ensure that larger transactions require additional approvals, reducing potential vulnerabilities.
How should we set approval thresholds and multisig for high-value transfers?
To ensure the safety of high-value transfers, set clear approval thresholds within your policy-as-code framework. For instance, you might require extra approvals for transactions exceeding $5,000 or $10,000. Implement a layered multisig system with hierarchical controls, such as treasury, operational, and delegate wallets, each having its own quorum rules. To bolster security, consider adding features like time locks or role-based permissions. These measures help ensure compliance, prevent unilateral decisions, and maintain a reliable audit trail.
What should our emergency “pause” plan cover if a signer key is compromised?
An emergency "pause" plan should focus on swift and decisive actions to protect assets. Key steps include immediately revoking or disabling the compromised key, implementing time-lock contracts to delay large transactions, and increasing the approval thresholds for multi-signature wallets. Adding hardware wallets to the security setup and maintaining a detailed audit trail can provide extra layers of protection and accountability. These measures are critical for preventing unauthorized transfers and minimizing potential financial losses.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


