
Stablecoin payments can be fast and efficient, but without proper controls, they can expose your business to risks like fraud, errors, and compliance failures. Here's how to establish vendor payment controls that safeguard your funds, ensure compliance, and streamline operations:
Use Secure Wallets: Implement MPC wallets for treasury operations to split private keys, reducing reliance on a single individual and enhancing security.
Set Automated Payment Rules: Define rules like transaction limits, approved vendors, and compliance checks to prevent errors and unauthorized transfers.
Conduct Pre-Sign Risk Checks: Automate checks for sanctions, anomalies, and policy compliance before signing payments. Implementing sanctions screening for stablecoins is critical to avoid regulatory penalties.
Add Human Oversight: Require human approval for high-value or flagged transactions, ensuring accountability.
Create Unified Workflows: Replace manual processes (like Slack approvals and spreadsheets) with centralized, automated systems for faster and error-free payments.
By combining secure wallets, automated rules, risk checks, and human oversight, you can manage stablecoin payments with confidence and accountability. This approach reduces errors, speeds up processing, and ensures a clear audit trail for compliance.
Key Takeaway: Stablecoin payments need structured controls to mitigate risks, enforce compliance, and improve efficiency. Follow these steps to build a reliable system for managing vendor payments.
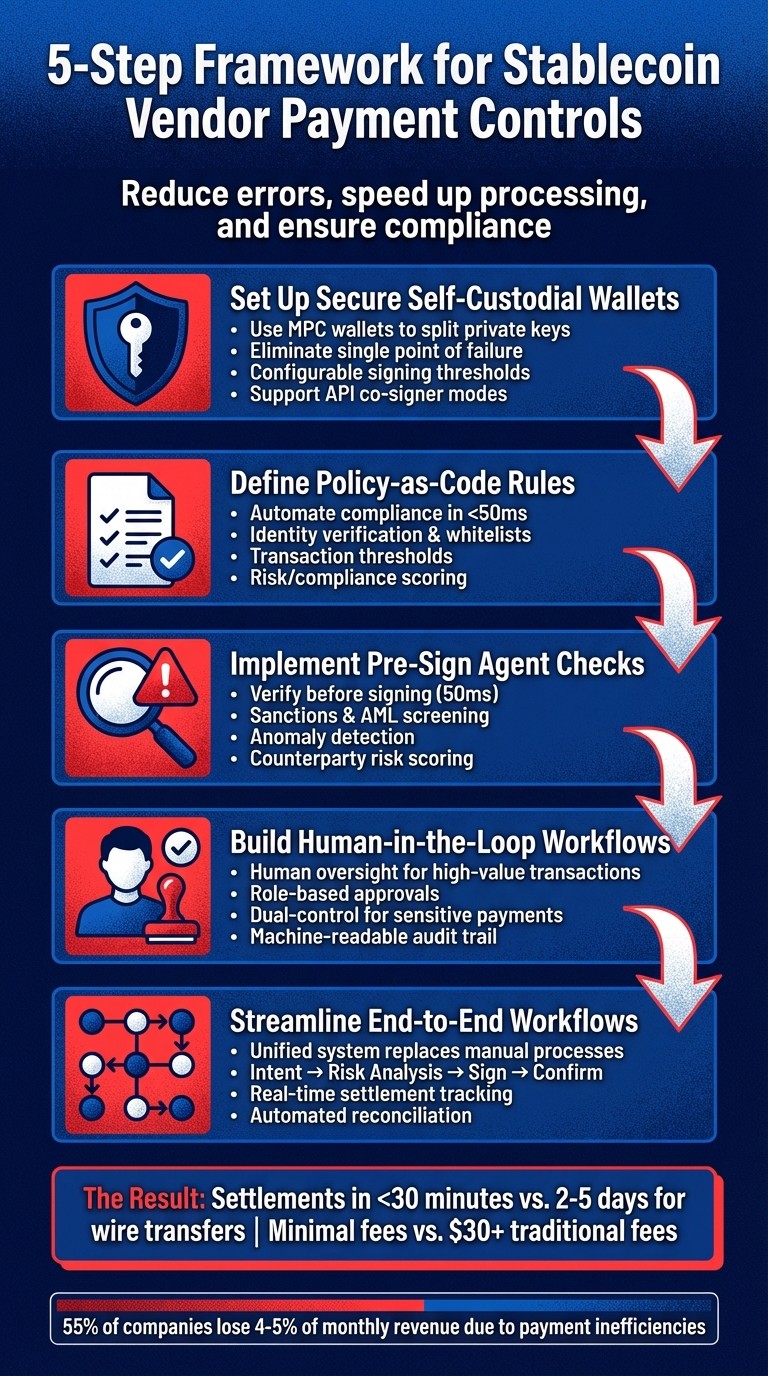
5-Step Framework for Building Stablecoin Vendor Payment Controls
Stablecoins to Scale A Compliance Playbook After GENIUS
Step 1: Set Up Secure Self-Custodial Wallets
Self-custodial wallets using Multi-Party Computation (MPC) technology are designed to address the risks associated with relying on a single individual for key management. By splitting private keys into multiple shards distributed across different parties, these wallets ensure that no single person or device holds the complete key. This eliminates a single point of failure, reducing the risk of financial loss.
MPC-based wallets are particularly effective for vendor payments, as they allow your finance team to maintain full control of assets while adhering to institutional-grade security standards that satisfy both board requirements and auditor expectations.
Why Choose MPC Wallets for Vendor Payments?
MPC wallets bring several key benefits compared to traditional hardware wallets or custodial exchange accounts:
They mitigate key-person risk by ensuring no single individual has full control over the private keys.
They allow for configurable signing thresholds, enabling enhanced security for high-value transactions. For instance, payments exceeding a set limit can require dual approval from senior finance team members.
They support API co-signer modes, enabling secure and automated processing of routine payments.
Unlike custodial exchange accounts, where a third party has control over your funds, MPC-based self-custody ensures that the platform itself cannot initiate transfers. For example, Stablerail employs an MPC-based wallet system across major blockchains like Ethereum and Base, supporting stablecoins such as USDC and USDT. However, the platform itself has no unilateral signing authority, keeping your funds fully under your control.
Best Practices for Wallet Setup
To maximize security and efficiency, consider these best practices when configuring your wallets:
Implement role-based signing thresholds: Use single signatures for smaller payments and require multiple approvals for larger transactions.
Ensure compatibility with required chains and tokens: Focus on EVM-compatible chains like Ethereum and Base, which are reliable for supporting major stablecoins commonly used in B2B payments.
Simplify gas management: Use sponsored transfers or dedicated gas wallets to ensure your main treasury wallet can send stablecoins without needing native tokens for transaction fees.
Set up a vendor whitelist: Restrict payments to pre-approved addresses to prevent unauthorized transfers. Additionally, integrate your wallets with a policy engine using SHA-256 intent fingerprinting. This ensures that any changes to a transaction after approval will trigger automatic rejection.
Step 2: Define Policy-as-Code Rules for Payments
Policy-as-code takes the guesswork out of compliance by automating your finance team's manual processes. Instead of relying on spreadsheets, Slack approvals, or individual judgment, you can create a centralized system that enforces payment rules in real time. With this setup, every payment intent is evaluated against your custom rules - usually in under 50 milliseconds.
This method reduces reliance on specific individuals and helps avoid costly mistakes, like sending funds to the wrong address, exceeding budget limits, or using unsupported blockchains. Think of policy-as-code as a safety net that prevents these errors before they happen. Below, you'll find examples of how these rules can be applied.
Examples of Payment Rules That Work
Payment rules typically cover three main areas: identity verification, transaction thresholds, and technical constraints. Here are some examples of rules that finance teams commonly use:
With tools like Stablerail's policy console, you can define rules such as "New address payments over $5,000 require CFO approval and verification" or "Weekend transfers over $10,000 need an additional approval." These rules are automatically applied to every payment intent before it gets signed.
How Policy-as-Code Works in Practice
Here’s how it plays out: When someone initiates a payment - whether by uploading an invoice, submitting a payout file, or through an API - the system instantly checks the transaction against your rules. If it spots an issue, like a non-whitelisted address, a breached velocity limit, or a restricted jurisdiction, the system takes action. It might block the payment, flag it for review, or trigger an approval workflow.
For added security, advanced systems use SHA-256 intent fingerprinting. This involves creating a unique hash based on the transaction details (amount, recipient, chain, token). If any of these details change after the policy check but before signing, the transaction fails verification and is rejected. This ensures no one can sneak in last-minute changes to an approved payment.
Every policy check is logged, creating an audit trail that includes details like the invoice ID, transaction hash, approval timestamps, and the specific rules that were enforced. This generates a machine-readable record for auditors, regulators, or your board - replacing scattered email or Slack approvals with a clear, traceable log.
Step 3: Implement Pre-Sign Agent Checks
After establishing payment rules, the next step is to introduce pre-sign checks. These checks act as a verification layer between initiating a payment and cryptographically signing it. Automated agents scan transaction details, on-chain data, and internal policies to identify risks before funds are transferred. Impressively, this process completes in just 50 milliseconds, maintaining the fast pace of workflows. Unlike traditional wallets that depend on manual reviews or post-transaction monitoring, this method shifts the focus to proactive measures - stopping potential issues before they occur.
Here’s the guiding principle:
"The AI can only block, flag, and explain - never spend".
This "copilot, not autopilot" approach ensures human approval is always required while providing clear, actionable insights.
To ensure the integrity of transactions, SHA-256 intent fingerprinting is used. This method generates a SHA-256 hash from transaction details (like recipient address, amount, chain, and token). If any changes are made after the check, the system automatically rejects the transaction.
These checks set the stage for more in-depth risk evaluations, as described below.
Types of Pre-Sign Checks
Pre-sign checks tackle various risk areas, each serving a specific purpose:
These checks are applied to every payment intent automatically. For instance, if someone initiates a large payment to a new vendor during off-hours, the system might flag it for several reasons - such as counterparty risk, unusual timing, or non-compliance with policy. The flagged transaction won't proceed until a designated approver reviews and resolves the issues.
After completing these checks, the system generates a detailed Risk Dossier summarizing the findings.
Benefits of Risk Dossiers
Once the automated checks are complete, the system produces a Risk Dossier - a structured, actionable report. This report provides a clear verdict (PASS, FLAG, or BLOCK) along with straightforward explanations. Instead of vague error messages, the dossier offers specific reasons, such as "JURISDICTION_BLOCKED" or "POLICY_THRESHOLD_EXCEEDED", making it easier for approvers to understand why a transaction was stopped.
Risk Dossiers also include evidence trails that reference specific policy clauses, timestamps, and data sources that triggered the decision. For example, if a payment is blocked due to sanctions screening, the dossier might cite the exact OFAC list entry and related on-chain data. This level of transparency creates a machine-readable audit trail that regulators, auditors, and boards can rely on.
Step 4: Build Human-in-the-Loop Approval Workflows
Automated systems are great at spotting risks, but they can’t replace human judgment - especially when dealing with high-value or unusual transactions. Once the initial risk assessments are complete, human oversight is essential for finalizing decisions on flagged transactions. The guiding principle here is simple:
"Nothing moves without a human signature. The AI can only block, flag, and explain - never spend".
This "copilot, not autopilot" philosophy ensures that while automated systems handle compliance checks and flag potential issues, they don’t have the authority to act independently. Humans remain the ultimate decision-makers.
Integrating Human Oversight at Key Moments
To make this system work, it’s crucial to design workflows that bring in human oversight at the right time - without creating unnecessary delays. For instance, you could set a rule like requiresHumanApprovalAbove: $5,000. In this setup, payments below that amount proceed automatically after passing initial checks, while larger transactions are escalated for approval by finance leaders.
When a transaction triggers a flag - whether for policy, risk, or compliance reasons - the system should automatically route it to the right approver. This process should include all relevant details from the Risk Dossier, enabling approvers to make informed decisions. They can either approve, reject, or override the flag with a documented reason. Every action leaves a clear, machine-readable record of human authorization.
For the most sensitive transactions, consider using dual-control or quorum approvals. This means requiring sign-off from multiple people in authorized roles, spreading accountability and reducing the chances of unauthorized or fraudulent activity.
Currently, more than half of accounts payable teams spend a significant amount of time managing invoices and payments. Often, approvals are scattered across emails, Slack messages, and spreadsheets, making it difficult to track decisions. Centralizing approvals in a dedicated policy console eliminates this fragmentation, creating a single source of truth for every payment decision.
Role-Based Approvals for Smarter Oversight
Not every transaction needs the same level of scrutiny. By using role-based access control (RBAC), you can assign approval responsibilities based on the nature of the transaction and the hierarchy within your organization. For example, Treasury Operations might handle routine vendor payments up to $10,000, while flagged transactions are escalated to Compliance Officers for further review.
This tiered approach ensures that low-risk transactions are processed quickly, while high-risk ones get the attention they deserve. It also helps avoid overwhelming senior executives with minor approval requests. Combined with automated checks, the system can adapt dynamically: payments to trusted vendors that meet all criteria can move forward with minimal friction, while payments to new or unverified recipients - especially during unusual times - are flagged for senior review with detailed explanations.
Creating a Reliable Audit Trail
To maintain transparency and stablecoin compliance, it’s essential to keep a secure, tamper-proof log of every transaction. This audit trail should include all the details, from the initial payment request to the final settlement, making it easy for auditors, boards, or regulators to review.
A complete audit trail should capture:
Payment intent: Who requested the payment, when, and why.
Policy evaluation trace: Which rules were checked and their outcomes.
Human approval records: Who approved or rejected the transaction and their justification.
Settlement proof: Cryptographic confirmation that the transaction was executed as approved.
This detailed execution tree allows compliance teams to track funds at every step and ensures that on-chain operations meet the same high standards as traditional banking processes.
The benefits are clear: manual payment processing takes an average of 14.6 days, and about 39% of invoices contain errors that require manual corrections. By using a structured, machine-readable audit trail, organizations can speed up processing, reduce errors, and improve accountability. When auditors or regulators come knocking, you’ll have a complete record showing who approved what, when, and why - backed by the risk assessments and policy checks that informed each decision.
Step 5: Streamline End-to-End Payment Workflows
After setting up secure wallets, enforcing policies, conducting risk checks, and establishing approval processes, the next challenge is tying everything together into a unified workflow. This step eliminates the inefficiencies of scattered, manual processes - like approvals lost in Slack threads, invoices buried in email attachments, and payment statuses tracked in spreadsheets. Instead, a streamlined workflow automates repetitive tasks while maintaining essential controls.
The cost of manual inefficiencies is substantial. For example, 55% of companies lose 4-5% of their monthly revenue due to payment delays and errors.
From Intent to Execution: Key Steps
Building on the secure wallet infrastructure, policy-as-code, and human-in-the-loop models, this workflow integrates every step, ensuring a smooth transition from intent to execution:
Create a Payment Intent: Start by gathering all the transaction details: amount, recipient's wallet address, stablecoin type, blockchain network, and any supporting documents like invoices or payout files. This intent acts as the single source of truth for the payment.
Trigger Risk Analysis: Automated agents handle tasks like sanctions screening, taint analysis, and policy checks. These checks include velocity limits, approved lists, and jurisdictional rules. If a transaction is flagged or exceeds thresholds, it’s routed to an approver who reviews the Risk Dossier and decides to approve, reject, or document an override.
Sign and Execute: Routine, low-risk payments are signed automatically by programmable API co-signers based on pre-set rules. For higher-risk transactions, human signatures are added using an MPC-secured vault. Once everything is signed, the transaction is sent to the blockchain, where it settles in minutes - far faster than the 2-5 days typical for traditional wire transfers.
Confirm Settlement and Generate Receipt: The system monitors the blockchain for transaction confirmation and creates a tamper-proof receipt linking the transaction back to the original intent and policy checks. Real-time webhooks can trigger follow-up actions, like updating internal records or notifying vendors, without requiring manual input.
Eliminating Manual Bottlenecks
Manual payment processes often depend on a single "crypto person" using a hardware wallet, with approvals buried in Slack or email threads and reconciliation handled through spreadsheets. This approach is inefficient - 60% of B2B payments still require manual reconciliation, and finance teams spend over 40 hours each month matching transactions to records.
Automation tools like Stablerail replace these fragmented workflows with a centralized control system. All payment requests, risk analyses, and approvals are managed in one Policy Console. For instance, the system can enforce rules like "Payments over $5,000 to new addresses need CFO approval and verification" or "Weekend transfers above $10,000 require additional sign-off."
Additionally, automated workflows can use sponsored transfers, where a dedicated gas wallet pays network fees on behalf of the sender. This allows vendors to receive stablecoins without needing to manage native tokens, simplifying the process and reducing friction in vendor payments.
Core Modules for Vendor Payment Controls
Managing vendor payments effectively requires a system that combines visibility, governance, and execution into a single, unified platform. Relying on multiple wallets, exchange accounts, and spreadsheets often leads to inefficiencies and risks. By adopting a modular architecture, finance teams can integrate secure funds management, automated governance, and streamlined payment processes. Here’s a closer look at the three core modules that make this possible.
Treasury Hub for Wallet and Chain Management
The Treasury Hub acts as the central command center for all stablecoin transactions. Instead of juggling multiple wallets and exchanges, finance teams gain a consolidated overview of funds across entities, blockchain networks (like Ethereum, Polygon, and Base), and wallet types. This centralized approach reduces dependency on any one individual and enhances security.
The hub categorizes wallets into cold, warm, hot, and dedicated gas wallets, ensuring assets are segregated to minimize risk. For example, if a hot wallet is compromised, the majority of funds remain secure in cold storage. It also enforces address hygiene with a categorized address book and whitelisting, reducing the chances of sending funds to an unverified or incorrect address.
In 2025, Slash Finance scaled its stablecoin operations to over $150 million in annual revenue by using a "Flow of Funds" orchestration engine. This system bridged the gap between 24/7 on-chain settlements and traditional banking batch processes, enabling the management of more than $1 billion in total volume with full auditability.
Policy Console for Rule Definition and Governance
Once funds are centralized, enforcing stablecoin treasury management best practices becomes the next priority. The Policy Console allows finance and compliance teams to translate rules into machine-enforceable logic - no engineering expertise required. For example, policies like "Payments over $5,000 to new addresses require CFO approval" can be implemented automatically, reducing reliance on key personnel.
The console also supports role-based access controls (RBAC) and separation of duties (SoD), ensuring no single individual can request, approve, and execute a transaction. Considering that 56% of accounts payable teams spend over 10 hours weekly on manual invoice processing, automating these processes saves significant time.
Dynamic thresholds allow for human review only when necessary, such as for high-value payments or transactions involving low-reputation parties. Routine payments, on the other hand, proceed automatically. Each decision is documented through a Policy Trace, offering a clear record of why a payment was approved or rejected - critical for audits and regulatory compliance.
Vendor & B2B Payment Module
This module simplifies the entire payment process by managing every detail of a "Payment Intent." Before funds are moved, it captures the amount, recipient, stablecoin type, blockchain network, and any supporting documents, such as invoices or purchase orders. This structured approach eliminates the inefficiencies of fragmented invoice handling.
The module also integrates vendor catalogs, whitelists, and real-time AML/KYT (Anti-Money Laundering/Know Your Transaction) screening, ensuring payments are only sent to approved addresses. When combined with the Treasury Hub and Policy Console, the module creates a complete audit trail for every transaction. This level of control is essential, especially when manual processing takes an average of 14.6 days and nearly 39% of invoices require human intervention due to errors.
Together, these three modules form the backbone of Stablerail's stablecoin payment control system. The Treasury Hub offers visibility across MPC-secured vaults on multiple blockchains, the Policy Console enforces governance rules, and the Vendor & B2B Payment Module streamlines the entire payment workflow. Stablerail’s modular architecture is designed for companies managing $1 million to $50 million annually in stablecoins, offering a scalable subscription model based on entities, users, and transaction volume.
Conclusion and Key Takeaways
Building effective financial controls requires a combination of secure wallets, automated policies, risk monitoring, human oversight, and efficient workflows. Here's how these elements come together:
MPC wallets reduce reliance on single individuals, eliminating key-person risk.
Automated policies block unauthorized transactions before they happen.
AI agents flag unusual activity, adding an extra layer of security.
Human approvers make the final call, ensuring accountability.
Streamlined workflows provide a clear audit trail for finance teams.
The stakes are high when it comes to financial inefficiencies. A staggering 55% of companies report losing 4–5% of their monthly revenue due to payment inefficiencies. Manual invoice processing, averaging 14.6 days, often leads to errors in 39% of cases. Stablecoins, on the other hand, offer a faster and cheaper alternative: settlements in under 30 minutes with minimal fees, compared to the 2–5 days and $30+ fees typical of traditional wire transfers. However, as Slash Engineering aptly put it:
"Stablecoins are easy; stablecoin banking isn't".
That’s where Stablerail steps in. Acting as a comprehensive control system, it bridges the gap between custody and transaction execution. By integrating MPC wallets, automated policy enforcement, AI-driven risk checks, and human approvals, it ensures:
"The AI can only block, flag, and explain - never spend."
This system not only safeguards governance but also creates a audit-ready stablecoin operations for compliance reviews.
For businesses managing moderate to high transaction volumes - anywhere from $1 million to $50 million annually in stablecoins - this approach replaces fragmented manual processes with a seamless treasury solution. Key features include:
Treasury Hub: Provides consolidated visibility across multiple blockchains.
Policy Console: Enforces governance rules without requiring engineering input.
Vendor & B2B Payment Module: Simplifies the entire payment process, from initiation to execution.
This integrated system offers the best of both worlds: fast settlements and strict governance. It eliminates the errors and delays tied to manual methods like spreadsheets and Slack approvals, while ensuring businesses maintain full control over their funds.
FAQs
How do MPC wallets improve the security of stablecoin transactions?
MPC wallets bolster the security of stablecoin transactions by leveraging multi-party computation (MPC). This technology splits the control of private keys among multiple parties, ensuring that no single individual or entity can independently access or transfer funds. This setup minimizes the risk of theft, misuse, or unauthorized transactions.
By using an MPC wallet, you maintain complete control over your keys while benefiting from added layers of security. Features like compliance checks, policy enforcement, and pre-sign verification ensure that every transaction adheres to your governance rules before it gets approved and processed. This combination of control and protection makes MPC wallets a powerful tool for secure transactions.
What are the advantages of using policy-as-code for managing vendor payments?
Using policy-as-code for vendor payments brings notable benefits in automation, compliance, and security. By embedding payment rules and restrictions into machine-readable policies, organizations can automatically validate transactions before approval. This approach cuts down on manual tasks, reduces processing delays, and ensures payments stay within set limits, meet recipient criteria, and follow other specific business rules.
Another advantage is improved accountability. Policy-as-code generates a detailed audit trail for each decision, including timestamps, supporting evidence, and the reasoning behind the policy. This makes regulatory compliance simpler and provides a strong defense during audits or disputes. Ultimately, it simplifies payment processes, allowing transactions to be faster, safer, and more aligned with oversight and control requirements.
Why is human involvement important in automated stablecoin payment systems?
Human participation plays a key role in automated stablecoin payment systems, ensuring that compliance, security, and sound decision-making are upheld. While automation efficiently manages tasks like enforcing policies, conducting sanctions checks, and performing risk evaluations, some situations demand human judgment to navigate complexities, override automated decisions when needed, and retain control over financial operations.
Moreover, human oversight adds a layer of accountability by creating a clear audit trail for actions like approvals, overrides, and signatures. This makes decisions traceable and defensible, whether for auditors, regulators, or governing boards. In the rapidly evolving space of on-chain stablecoin transactions, human review serves as a vital checkpoint to prevent mistakes, enforce governance, and maintain compliance standards.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


