
Want to secure your crypto payments while maintaining control? Time-based rules can help you manage risks like fraud, errors, and compromised keys by introducing delays, transaction limits, and restricted operational hours.
Here’s how these rules work:
Cool-off periods: Delays for large transfers (e.g., 4 hours for payments over $100,000) allow time for reviews.
Spending limits: Daily or hourly caps prevent excessive transactions in short periods.
Restricted hours: Sensitive actions, like exporting keys, are limited to business hours.
Timelocks: Scheduled delays (e.g., 48 hours) for protocol changes ensure time for review.
These safeguards improve oversight, prevent risky transactions, and create audit trails for compliance. Tools like Stablerail enforce these rules automatically, flagging unusual activity and requiring approvals for high-risk transactions.
Bitcoin Time Locks: Game Changer for Future Generations
How to Set Time-Based Rules
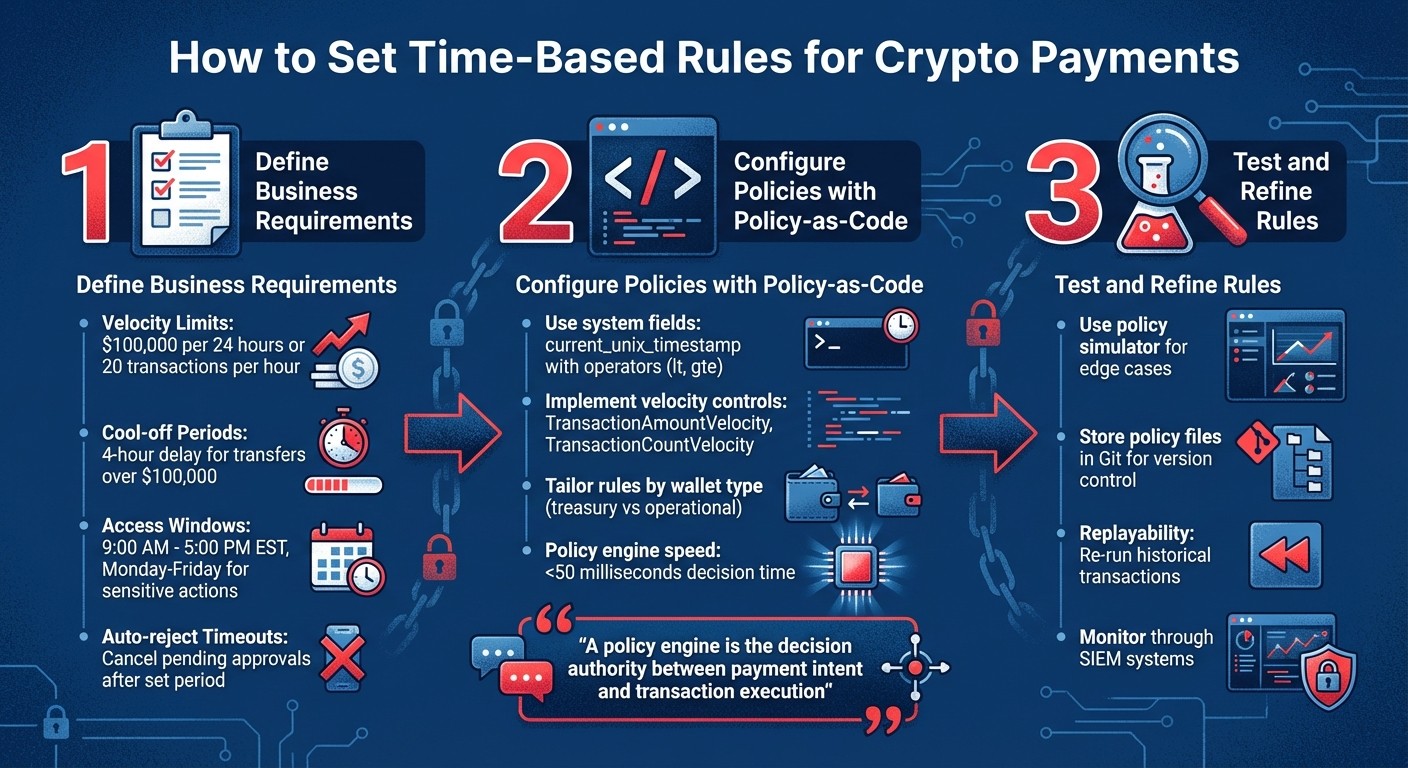
How to Implement Time-Based Rules for Crypto Payments: 3-Step Process
Establishing time-based rules for crypto payments involves creating machine-enforceable policies that align with your risk tolerance and operational needs. These steps help ensure every transaction complies with your organization's stablecoin treasury governance framework.
Define Business Requirements
Start by setting velocity limits - these define the maximum number of transactions or the total value allowed within a specific timeframe. For example, you might limit a wallet to $100,000 per 24 hours or restrict automated accounts to 20 transactions per hour.
Next, implement mandatory cool-off periods for high-risk transactions. A typical setup might include a 4-hour delay for transfers exceeding $100,000 or payments to first-time beneficiaries. This delay provides a buffer to identify potential fraud, such as social engineering or unauthorized access, before funds are released.
Define access windows for sensitive actions like private key exports or temporary signer permissions. These actions could be restricted to business hours - say, 9:00 AM to 5:00 PM EST, Monday through Friday - when oversight is available. Additionally, configure auto-reject timeouts to cancel pending approvals that remain inactive beyond a set period, ensuring outdated transactions don’t linger.
Once these requirements are outlined, translate them into executable rules.
Configure Policies with Policy-as-Code
Policy-as-code frameworks allow you to convert business requirements into automated, enforceable rules. For example, you can use system fields like current_unix_timestamp with operators like lt (less than) or gte (greater than or equal to) to restrict actions to specific dates or times. Velocity controls can be implemented using rules like TransactionAmountVelocity or TransactionCountVelocity, which monitor the total value or frequency of transactions within a sliding time window.
Consider tailoring rules based on wallet usage. For instance, a treasury wallet dedicated to vendor payments might have stricter weekend limits compared to an operational wallet handling routine transactions . Policy engines enforce these rules quickly - typically in under 50 milliseconds - ensuring efficient decision-making.
"A policy engine is the decision authority between payment intent and transaction execution, returning outcomes like approve, deny, hold, route, or step-up."
Stablecoin Insider
Once policies are coded, focus on testing and refining them.
Test and Refine Rules
Use a policy simulator to ensure your rules don’t disrupt legitimate transactions . Test edge cases, such as high-value payments submitted just before the weekend - does the cool-off period extend into Monday, or does it pause over the weekend?
Store policy files in Git for peer reviews and easy rollback if needed . Advanced systems often include replayability, which lets you re-run historical transactions against updated policies to confirm expected outcomes before full deployment. Monitor policy events through SIEM systems to detect anomalies and fine-tune rules as necessary.
Enforcing Time-Based Policies with Stablerail

Stablerail takes your defined and coded policies and ensures they're enforced before any transaction gets signed. Acting as a programmatic policy engine, it operates between the payment intent and the transaction execution. This control layer checks the business context before any signature happens, without having unilateral signing power. Here's how automated checks and approval workflows add an extra layer of security for time-sensitive transactions.
Automated Pre-Sign Checks
Before signing off on any payment, Stablerail's agents run pre-sign checks using behavioral anomaly detection to analyze time-of-day patterns. For instance, if a $50,000 transfer is initiated at 2:00 AM on a Saturday, and weekend payments over $10,000 are restricted, the system flags it immediately. These rules are enforced in milliseconds, preventing even top-level executives from bypassing them.
For high-risk situations, such as transfers over $100,000 or payments to new beneficiaries, the system imposes a 4-hour delay. This delay provides a critical buffer to detect potential social engineering or unauthorized access before funds are released. It also helps prevent rapid consecutive transactions, which could signal compromised credentials.
Approval Workflows for Time-Sensitive Transactions
When a transaction is flagged - whether it’s outside allowed time windows or triggers a high-risk alert - Stablerail holds it until all necessary approvals are completed. The process follows three key steps: creating the payment intent, reviewing the Risk Dossier with a PASS/FLAG/BLOCK decision, and approving and signing with a documented override reason.
Transactions that clear all checks can proceed with one-click execution, while flagged ones require human approval. This workflow works hand-in-hand with the time-based rules, ensuring routine payments remain efficient while escalating high-risk scenarios for review.
Audit Trails and Compliance Evidence
Every transaction generates a Proof-of-Control receipt, which includes details like the payment amount, purpose, approver, risk verdict, and timestamps. This creates a thorough audit trail that serves as evidence for auditors, boards, and regulators.
"Every payout generates a defensible receipt: what was paid, why, who approved, and the risk verdict." - Stablerail
The system also logs which policy rules were evaluated and their outcomes. For example, if an auditor questions why a $150,000 payment was approved at 7:00 PM on a Friday, you can provide the policy exception, the CFO's override reason, and the associated risk assessment. This level of transparency simplifies stablecoin compliance and reinforces trust in your governance processes.
Best Practices for Managing Time-Based Payment Rules
Regular Policy Reviews and Updates
Keeping your time-based payment rules up to date is crucial. Use version control and peer reviews to ensure every update is well-documented and thoroughly vetted.
Make it a habit to review velocity metrics quarterly. This helps you confirm that transaction limits align with your current business volume. If you notice your transaction caps are getting close to actual payment volumes, adjust thresholds ahead of time to prevent legitimate transactions from being blocked. These steps help keep your controls aligned with compliance requirements and operational needs.
Use real-time dashboards to monitor sudden spikes in allowances. For every policy update, generate a cryptographic Decision Proof - a combination of policy hash and timestamp - to create records that auditors can trust. After implementing changes, step up monitoring efforts to catch any configuration errors or unexpected behavior early.
Balance Security and Operational Flexibility
Once your policies are current, the next step is to ensure they strike the right balance between security and operational efficiency. Your controls should protect transactions while still allowing smooth day-to-day operations.
One effective strategy is using tiered approval ladders. Low-risk, routine payments can go through with minimal approvals, while high-value transfers automatically trigger delays and require additional sign-offs.
Another useful tactic is wallet tagging. This allows you to distinguish between human-operated accounts that need full approval workflows and automated service accounts designed for scheduled transfers. For urgent situations, enable overrides but require a recorded reason to be logged in the audit trail.
Regularly review your smart cool-off periods to ensure they provide enough fraud protection without slowing down operations unnecessarily. Lastly, adopt a fail-closed design. This ensures that if your policy engine or network connection goes down, the system will automatically block transactions rather than allowing them through.
Conclusion
Time-based rules act as a strong safeguard for crypto payments, introducing withdrawal windows, cool-off periods, and velocity limits to reduce risks like compromised keys and social engineering attacks. To implement these controls effectively, start by defining clear business requirements - such as a 4-hour delay for transfers exceeding $100,000. Use policy-as-code to translate these requirements into enforceable policies, and regularly test them, especially velocity controls that limit transaction amounts and frequency.
Once policies are in place, enforcement becomes critical. Stablerail ensures compliance through pre-sign checks, providing a clear PASS/FLAG/BLOCK Risk Dossier with straightforward explanations in plain English. If a transaction breaches the defined rules, the system locks it and mandates a recorded override reason, which is then included in the audit trail.
This enforcement process ensures that even high-level executives cannot bypass these policies without leaving a documented record. Each action generates a Proof-of-Control receipt, outlining the payment details, its purpose, the approver, and the risk assessment. Notably, the system safeguards the treasury without ever directly handling the funds.
FAQs
What time-based rules should I set first?
To begin, establish clear rules for transaction timing and approval thresholds to improve oversight during potentially risky periods. Here are some practical examples:
Extra approval for large transactions: Require additional authorization for significant payments made on weekends or outside regular business hours.
Time delays for high-value payments: Introduce a waiting period for substantial transactions, giving time for review or cancellation if needed.
Restrict transactions to business hours: Limit payment processing to standard operating hours to align with internal policies and reduce risk.
These measures help ensure better compliance and control, particularly when handling sensitive or high-value payments.
How do cool-off periods work in practice?
Cool-off periods introduce a delay before a transaction can be finalized, giving users time to review or cancel if needed. These can take various forms, like timelocks in hierarchical multisig setups or time-locked contracts that limit when funds can be accessed or spent. In enterprise payment systems, these delays play a crucial role in enhancing security. They ensure transactions only move forward after the designated time has passed, allowing for necessary compliance checks and approvals to be completed as part of governance processes.
How can Stablerail enforce these rules without controlling my funds?
Stablerail ensures strict rule enforcement without ever taking control of your funds. It acts as an agentic control plane, positioned above custody and before any transaction signing. Your assets stay secure in MPC-protected wallets, with Stablerail having no signing authority. Instead, it conducts essential pre-sign checks - such as sanctions screening, policy enforcement, and risk evaluations - before approving any transaction. This approach guarantees compliance and security while keeping the control of your private keys entirely in your hands.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


