
Managing treasury funds securely and efficiently is no longer just about controlling private keys. Companies need systems that evaluate the context of every transaction in real time to prevent fraud, ensure compliance, and reduce risks with a checklist. Policy-driven logic, or policy-as-code, adds a decision-making layer that evaluates transactions against rules before they are executed. This ensures payments align with company policies and reduces human error.
Key highlights:
Policy-as-code: Enforces rules like "Payments over $5,000 to new addresses require CFO approval."
Risk screening: Detects anomalies, sanctions violations, and counterparty risks before transactions.
Automation: Speeds up workflows, cutting approval times from days to hours.
Audit trails: Provides detailed records of decisions, ensuring compliance and accountability.
Example platform: Stablerail
Combines machine-enforced rules with user-controlled wallets.
Offers tools like vendor whitelists, risk scoring, and automated cool-off periods for high-risk payments.
Generates "Proof-of-Control" receipts for auditors and regulators.
1. Stablerail

Governance Layer
Stablerail operates as a governance layer, bridging custody and transaction signing by enforcing business rules through machine-executable constraints. Using a policy-as-code approach, it translates these rules into enforceable policies. Through the Policy Console, teams can customize roles, set transaction limits, and design approval workflows that fit their operational needs. This aligns with a growing trend in 2026 toward constrained transfers, where automated policies replace manual oversight to ensure compliance.
The platform enables a tiered wallet topology, dividing funds into Cold/Reserve, Warm/Operations, and Hot/Automation tiers. This structure ensures that the largest balances are stored in environments with the strongest controls and minimal exposure. Stablerail also enforces Separation of Duties (SoD), ensuring no single individual can request, approve, and execute a payment alone. This approach embeds compliance directly into the payment process, turning traditionally manual steps into automated, real-time controls.
Once policies are in place, the system moves to dynamic risk screening, evaluating the context of each transaction before execution.
Risk Screening
Before any transaction is executed, specialized AI agents perform detailed pre-sign checks. These checks validate the intent and context of the transaction, while human signers maintain ultimate control. The system generates detailed risk dossiers with clear verdicts - PASS, FLAG, or BLOCK - backed by evidence-based explanations rather than subjective judgment. Risk checks include sanctions screening, taint and exposure analysis, behavioral anomaly detection (e.g., unusual transaction times or amounts), and counterparty risk scoring.
Stablerail addresses "freeze-risk" by identifying tainted counterparties that could lead stablecoin issuers to freeze corporate funds. For high-value or high-risk transfers, such as those exceeding $100,000, the platform introduces Smart Cool-Off Periods - typically four hours - to reduce the chances of social engineering or internal fraud. Additionally, the system simulates payments before execution to catch issues like first-time destinations, address changes, or duplicate transfers, preventing blind approvals. Automated sanctions screening integrates on-chain oracles or off-chain APIs to block sanctioned addresses at the policy level before the signing stage.
Approval Workflow
After risk validation, Stablerail ensures only compliant transactions move forward through a streamlined three-step approval process. Users initiate a transaction (via invoice PDF, CSV, or API), automated checks confirm compliance and assess risk, and approvers either sign off or the system locks flagged transactions.
The platform maintains a "Golden Source", a verified vendor whitelist. If a vendor’s address changes, the system automatically locks the payment, requiring mandatory escalation. To enhance privacy, Stablerail supports One-Time Deposit Addresses for each invoice, keeping primary treasury wallet addresses hidden from competitors and blockchain scanners. Typically, Stablerail works with companies managing $1 million to $50 million annually in stablecoin transactions. Pricing is based on an annual subscription, scaling with the number of entities, active users, and total on-chain volume.
Audit Trail
At the end of the workflow, Stablerail creates an immutable audit trail that documents every decision made during the transaction process. Actions such as intent creation, risk checks, flags, overrides, approvals, and signatures are all recorded. The platform generates "Proof-of-Control" receipts, which detail what was paid, why it was paid, who approved it, and the corresponding risk assessment. These receipts are designed to meet the needs of auditors, boards, and regulators, providing clear evidence that proper controls were in place at the time of the transaction.
The audit trail goes beyond recording outcomes - it captures the entire decision-making process, including invoked policy clauses and timestamps for every step. This level of documentation shifts compliance from being reactive to proactive, offering proof that every payment adhered to established rules before execution.
2. Standard Custody Tools
Governance Layer
Standard custody tools rely on role-based access control (RBAC) to manage permissions. This means permissions are static, allowing teams to restrict transfers to pre-approved counterparties using whitelists. While this setup provides a basic framework for access control, it doesn't have the adaptability of policy-as-code systems, which can adjust rules dynamically based on factors like transaction context, time of day, or counterparty history.
Most top custodians store 90-95% of assets in cold storage. These tools primarily focus on controlling who can sign transactions and how many signatures are required. However, they don't assess whether a payment aligns with a company's policies or past vendor interactions. Instead, these tools rely on compliance controls for real-time restrictions.
Risk Screening
Standard custody tools integrate real-time compliance controls into their signing processes. This includes sanctions screening (via APIs like Chainalysis), AML/KYT (Know Your Transaction) monitoring, and address whitelisting. These measures can flag sanctioned addresses or suspicious activity but fail to consider the broader business context.
Static permissions pose a significant limitation. Even when all required signatures are present, they can't distinguish between legitimate and malicious transfers. For example, the 2022 Wormhole bridge hack, which resulted in over $200 million in losses, happened because a stolen private key was used within a static multi-signature system. A policy-based system could have flagged the unusual minting transaction before it was executed. Additionally, standard tools are vulnerable to oracle and governance risks, where attackers might manipulate price feeds or take over governance systems to gain immediate access to funds. After compliance checks, approval processes still depend heavily on manual interventions.
Approval Workflow
Traditional custody platforms require multiple signers for transaction approvals, which can delay urgent payments. For instance, simple treasury actions managed through Snapshot and Gnosis Safe typically take 7 to 14 days to complete. This creates operational challenges for time-sensitive transactions. As a result, over $30 billion in DAO treasury assets remain underutilized or are manually managed due to the limitations of static multisig models. While these tools are effective at key management and signing, they don't capture the underlying business purpose of payments - such as whether a payment is tied to an invoice, a recurring vendor, or a new counterparty.
Audit Trail
Standard custody platforms generate transaction logs that include wallet addresses, transaction hashes, timestamps, and signer identities. These logs provide a basic level of auditability but require manual reconciliation to link blockchain activity to business purposes. More advanced tools can use node records to trace the origin of a side effect back to its triggering event.
However, these audit trails lack the detailed context required for regulatory compliance. They don't include important information like jurisdiction data, risk scores, counterparty types, or specific policy clauses that influenced decisions. This forces finance teams to manually map blockchain transactions to their business intents, highlighting the need for systems that embed decision-making context directly into the audit record.
The GENIUS Act: What Stablecoin Regulation Means for Treasury
Advantages and Disadvantages
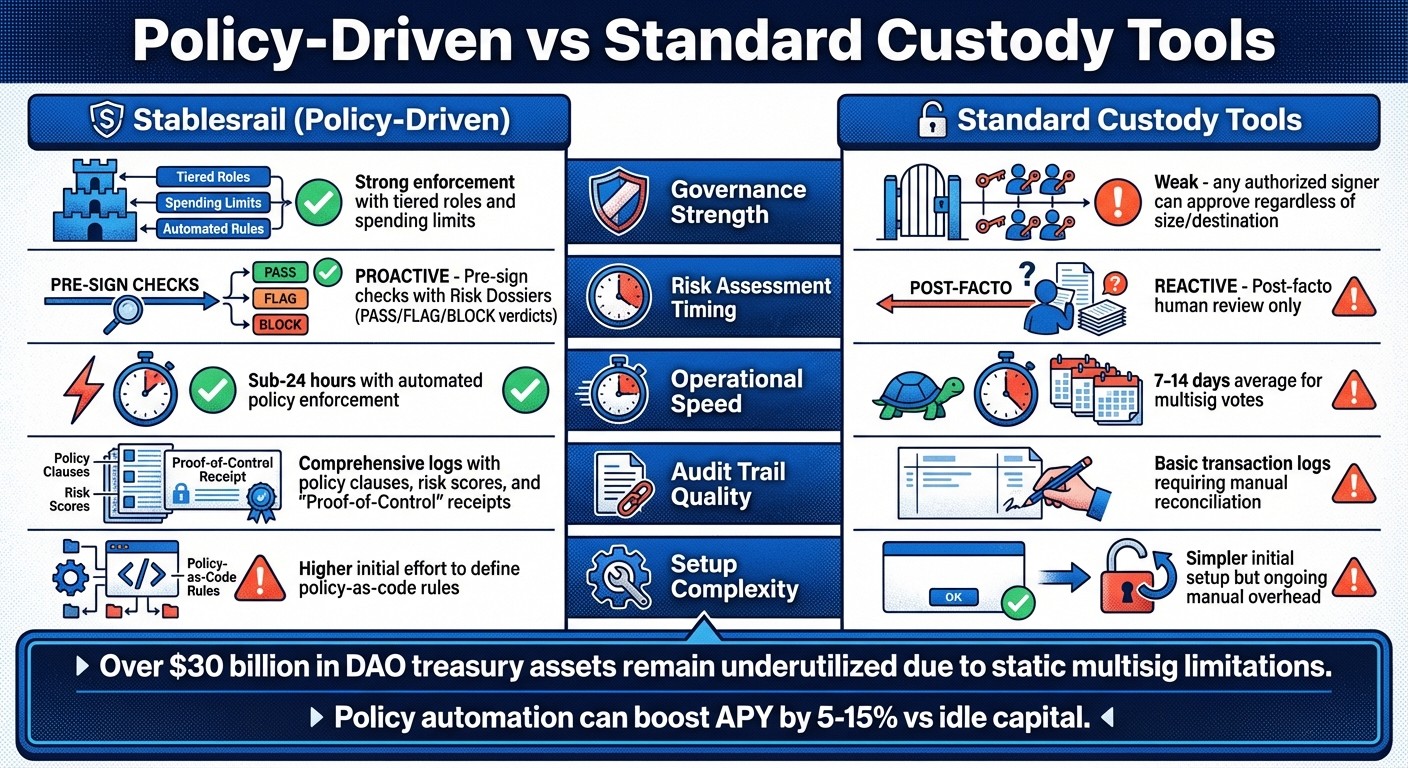
Policy-Driven vs Standard Custody Tools: Key Differences in Treasury Management
Policy-driven systems bring a layer of business context to payment processes, setting them apart from standard custody tools that rely on reactive oversight. For example, Stablerail's proactive approach evaluates transactions before signing, while traditional multisig setups depend on human intervention after the fact. This means a policy-driven system can flag high-value or unusual transfers that exceed preset thresholds, whereas static permissions treat all payments the same, regardless of size or counterparty.
When it comes to key management, standard custody tools perform well. However, they often fall short in terms of operational speed. Traditional multisig approvals can take anywhere from 7 to 14 days, while automated policy enforcement cuts execution time down to under 24 hours. This delay creates inefficiencies, leaving over $30 billion in DAO treasury assets underutilized.
Policy automation offers the potential to boost returns, increasing APY by 5–15% compared to idle capital. But this advantage comes with a trade-off: setting up policy-as-code takes upfront effort to translate business rules into enforceable logic. On the other hand, standard custody tools are easier to set up initially but require ongoing manual reconciliation to connect blockchain transactions with business purposes. The table below highlights the key differences between these two approaches:
Criteria | Stablerail (Policy-Driven) | Standard Custody Tools |
|---|---|---|
Governance Strength | Strong; enforces tiered roles and spending limits | Weak; any authorized signer can approve transactions regardless of size or destination |
Risk Timing | Proactive; checks occur before signing with Risk Dossiers (PASS/FLAG/BLOCK) | Reactive; relies on post-facto human review |
Operational Speed | Sub-24-hour cycles with automated policy enforcement | 7–14 days on average for multisig votes |
Audit Trail | Comprehensive logs with detailed policy clauses and risk scores | Basic transaction logs requiring manual reconciliation |
Setup Complexity | Higher initial effort to define policy-as-code rules | Simpler initial setup but ongoing manual overhead |
Policy-driven systems also enforce separation of duties, ensuring no single individual can unilaterally create, approve, and execute a payment. In contrast, standard custody tools rely heavily on individual integrity, leaving systems vulnerable if a single key is compromised. While policy-driven governance enhances security, it does come with added complexity. Finance teams must create tiered wallet structures (e.g., cold wallets for reserves, warm wallets for operations, and hot wallets for automation) and define detailed policy rules.
This comparison highlights how policy-driven governance provides proactive controls, greater efficiency, and stronger security - elements that traditional custody tools often lack.
Conclusion
Policy-driven logic elevates self-custodial treasuries from simple wallets to secure, rule-enforced systems with clearly documented rules and enforceable permissions. Instead of relying on blind signing, finance teams gain decision-backed execution - pre-sign risk dossiers that clearly explain decisions in plain English before transactions proceed. This approach addresses a critical flaw in traditional custody tools: while they manage keys well, they lack business context, such as invoice history, vendor relationships, or policy rationale. Policy-driven measures fill this gap, offering a proactive alternative to conventional key management.
The shortcomings of traditional custody systems become glaring when examining real-world failures. Legacy systems have left significant treasury assets idle and underutilized. High-profile incidents, like major multisig breaches, highlight the dangers of static systems. These failures underscore the need for dynamic, policy-enforced controls that can prevent such losses.
For companies managing $1 million to $50 million in stablecoin volume annually, a few key practices are essential: adopting a tiered wallet structure (Cold for reserves, Warm for operations, Hot for automation) and defining specific roles such as Requesters, Preparers, Approvers, Signers, and Reconcilers. Additionally, implementing smart cool-off periods - automatic delays of around 4 hours for high-value transactions or new beneficiaries - helps reduce risks from social engineering attacks. These steps transform compliance from a manual, back-office task into a real-time, machine-enforced safeguard.
Active, policy-driven controls are no longer optional for modern treasury management. Stablerail demonstrates this with its immutable "Proof-of-Control" receipts, offering CFO-level evidence for auditors and regulators. With stablecoin transaction volumes projected to hit $33 trillion by 2025 and McKinsey forecasting agentic commerce to generate $1 trillion in U.S. retail revenue by 2030, the shift from passive storage to active control is a critical step for the next decade of corporate treasury operations.
FAQs
What is policy-as-code in a self-custodial treasury?
Policy-as-code in a self-custodial treasury means turning governance rules, transaction limits, and policies into machine-readable code. This ensures that every transaction is automatically checked and enforced against these rules before being signed. The result? Better compliance, stronger security, and an easy-to-follow audit trail for every financial move. For finance teams, it’s a way to maintain tight control while simplifying oversight.
How do pre-sign risk checks stop fraud before signing?
Pre-sign risk checks play a crucial role in fraud prevention by scrutinizing transactions before they are finalized. These checks include processes like sanctions screening, policy enforcement, behavioral anomaly detection, and counterparty risk scoring. By identifying potential red flags and ensuring compliance, they provide clear, easy-to-understand evidence of any suspicious activity before a transaction is approved.
How do 'Proof-of-Control' receipts assist with audits and compliance?
Proof-of-Control receipts serve as verifiable proof of transactions, ensuring that actions align with established policies and regulations. These receipts are particularly useful in audits, as they confirm compliance with governance rules and provide a dependable audit trail. This strengthens both transparency and accountability in organizational processes.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


