
Mistakes in payments are costly and often irreversible, especially with near-instant stablecoin transactions. Contextual risk scoring helps finance teams reduce errors by analyzing the full business context before approving payments. This approach goes beyond basic checks by evaluating factors like recipient history, transaction patterns, and timing anomalies.
Key Takeaways:
What it does: Identifies risks by analyzing recipient reputation, invoice alignment, and behavioral patterns.
Why it matters: Stablecoin payments settle in under 2 seconds, leaving no room for manual error correction.
How it helps: Flags unusual transactions, ensures compliance, and documents decisions for audits.
By integrating contextual risk scoring into payment workflows, businesses can avoid costly errors, improve compliance, and protect their financial operations.
How Transaction Monitoring System TMS Calculates 'Transaction Risk Score' to generate AML Alert
What is Contextual Risk Scoring?
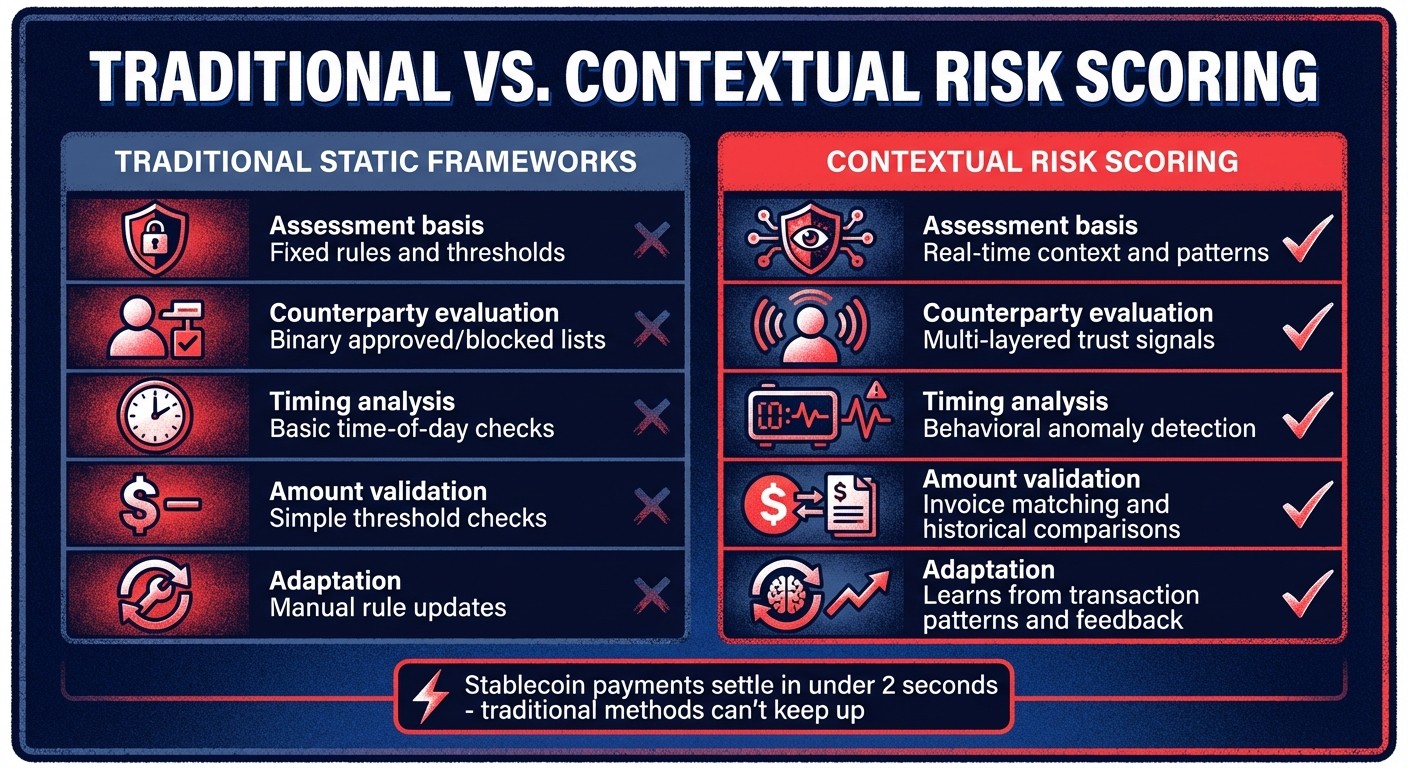
Traditional vs Contextual Risk Scoring for Stablecoin Payments
Contextual risk scoring evaluates payments by examining the complete business context. It doesn’t just ask, “Is this wallet on a sanctions list?” but digs deeper: “Who is the recipient?” “What’s their transaction history?” “Does the payment amount match the invoice?” and “Is the timing unusual?” This broader perspective allows for a more accurate assessment of risk.
Traditional risk frameworks rely on fixed thresholds. Payments either pass or fail based on predetermined criteria, like amount limits, approved vendor lists, or basic sanctions checks. However, these systems often miss critical nuances. For example, they might treat a $10,000 payment to a trusted vendor during regular hours the same as one sent to a new wallet late at night - even though the risks are vastly different.
Contextual scoring shifts the game by incorporating real-time signals tied to business operations. It evaluates factors like counterparty reputation, transaction patterns, and behavioral anomalies. For instance, a payment to a wallet with a long history of successful transactions is treated differently than one sent to a new address. Similarly, a $50,000 payment might seem routine for one vendor but suspicious for another if it deviates from past invoices or occurs at an unusual time.
This approach is particularly crucial for stablecoin payments, which settle almost instantly - under two seconds on Layer 2 networks. Traditional manual reviews can’t keep up with this speed. By mid-2025, stablecoin-based B2B payments exceeded $6 billion monthly, highlighting the need for intelligent, real-time transaction screening before funds move irreversibly on-chain.
By embedding business context into every transaction, contextual scoring catches errors before they happen. This proactive analysis is essential for systems that verify intent before signing. It not only reduces error rates but also safeguards treasury operations. This dynamic method stands in stark contrast to traditional scoring, as explained below.
Traditional vs. Contextual Risk Scoring
Traditional risk scoring applies uniform rules to all transactions. For instance, it may ask: Is the amount below $25,000? Is the recipient on an approved vendor list? Does the wallet clear sanctions screening? If the answers are “yes,” the payment proceeds. While this works for bank wires - where settlements take days, allowing for manual reviews - it falls short for near-instant stablecoin transfers.
The core issue with traditional systems is their lack of business context. They don’t account for factors like a recipient’s transaction history, whether the payment aligns with past invoices, or if the timing is unusual. This blind spot means they often miss behavioral patterns that could signal fraud or errors.
Contextual scoring, on the other hand, integrates multiple layers of trust signals. For new wallets, it evaluates on-chain credentials like asset holdings. For established relationships, it examines past transaction patterns and on-chain reputation. This layered approach adapts based on the counterparty’s history and lifecycle stage, offering a more nuanced risk assessment.
Feature | Traditional Static Frameworks | Contextual Risk Scoring |
|---|---|---|
Assessment basis | Fixed rules and thresholds | Real-time context and patterns |
Counterparty evaluation | Binary approved/blocked lists | Multi-layered trust signals |
Timing analysis | Basic time-of-day checks | Behavioral anomaly detection |
Amount validation | Simple threshold checks | Invoice matching and historical comparisons |
Adaptation | Manual rule updates | Learns from transaction patterns and feedback |
Consider edge cases: a traditional system might block a legitimate $15,000 payment to a new vendor because it exceeds a preset threshold. Contextual scoring, however, evaluates whether the amount matches the invoice, checks for credible on-chain activity, and considers the timing. Instead of outright blocking the payment, it might flag it for review, offering a smarter way to manage risk.
The Cost of Payment Errors
Payment errors can be costly - far beyond the immediate financial loss. For example, if a company mistakenly sends $50,000 to the wrong wallet, the funds are often irrecoverable due to the irreversible nature of on-chain transactions.
Operational costs quickly pile up. Finance teams may spend hours investigating the mistake, tracing the approval process, and explaining the loss to executives. Worse, if the error involves a compliance issue - like sending funds to a sanctioned wallet - the company could face regulatory penalties. Stablecoin issuers may even freeze wallets that interact with flagged addresses, disrupting operations.
Reputational damage adds another layer of risk. Vendors may lose trust if payments are delayed or misdirected, and auditors or board members could question the company’s internal controls. For businesses handling high volumes of micro-transactions, a single configuration error can trigger thousands of incorrect payments before anyone notices.
Traditional credit card processing costs at least $0.30 per transaction, making micro-transactions under $0.50 impractical. Stablecoin transfers on Layer 2 networks, by contrast, are nearly instant and cost mere fractions of a cent. But this speed can become a liability without proper risk scoring. Payments that take days to clear through traditional banking channels - and allow time for error detection - can settle irreversibly in under two seconds.
Contextual risk scoring minimizes these risks by identifying anomalies before signing. For example, it can flag a payment to a new wallet that mimics a trusted address (a form of address poisoning) by detecting no prior interaction history. Similarly, an unusually large payment outside normal business hours can trigger a manual review before execution.
Meeting Regulatory Requirements
When it comes to stablecoin payments, compliance requires more than just basic sanctions checks. Finance teams must show they’ve done due diligence on every counterparty, followed proper approval workflows, and maintained audit trails detailing who approved what - and why.
Contextual risk scoring embeds these compliance checks into the pre-execution workflow. Before signing any payment, the system performs mandatory verifications, including sanctions screening, taint analysis (to identify flagged wallets), policy enforcement, and behavioral anomaly detection. Each step generates documentation for audit purposes.
The system evaluates specific risk factors that regulators prioritize:
Risk Factor | Risk Level Criteria | Regulatory Relevance |
|---|---|---|
New Wallet Detection | HIGH: 0 transactions; MEDIUM: <3 transactions or <7 days old | Identifies high-risk counterparties requiring extra checks |
Interaction History | HIGH: 0 interactions; MEDIUM: 1–2 interactions; LOW: 3+ interactions | Differentiates established relationships from new ones |
Malicious Connection | HIGH: 0–2 hops from known malicious addresses | Prevents exposure to fraudulent wallet networks |
Dormant Wallet | MEDIUM: Last transaction >180 days ago | Flags reactivated wallets that might be compromised |
Regulators demand more than a simple “we checked the sanctions list.” They want evidence of business context: Why was this payment approved? Who reviewed it? What risk factors were considered? Contextual scoring automatically generates this documentation, creating a detailed audit trail from intent to execution.
As transaction volumes grow, manual compliance checks become unsustainable. McKinsey predicts that agentic commerce will drive $1 trillion in U.S. retail revenue by 2030. With this scale, systematic, policy-driven risk scoring becomes essential.
Core Components of Contextual Risk Scoring
Contextual risk scoring involves four main components to identify payment risks before execution: counterparty identity, transaction behavior, policy compliance, and real-time threats. Together, these elements provide a layered approach to safeguarding your financial operations.
Counterparty Risk Assessment
This step focuses on evaluating the payment recipient, moving beyond basic sanctions checks. It considers details like the recipient's wallet history, on-chain reputation, and previous interactions with your organization. For instance, a wallet with no transaction history carries a different risk level compared to one with multiple successful interactions.
For new wallets, potential red flags include proximity to malicious addresses. For example, a wallet located within two hops of a flagged entity is marked as high risk. On the other hand, established counterparties with three or more successful prior transactions are considered more reliable.
"Every payment is simulated before execution. First-time destinations, address changes, and duplicates are caught before you sign." - Stablerail
Address poisoning is another threat addressed here. Attackers may create wallets that imitate trusted addresses by mimicking key characters. To counter this, recipient addresses are compared against known contacts, and any suspicious matches are flagged. This prevents errors like copying an incorrect address from transaction histories.
Behavioral and Historical Analysis
This component analyzes payments by comparing them to historical patterns. Factors like transaction frequency, amounts, and wallet activity are monitored to detect unusual behavior. For example, dormant wallets reactivating after 180 days, new wallets less than seven days old, or those with fewer than three transactions are flagged as medium to high risk. Specifically:
Zero interactions = high risk
One to two interactions = medium risk
Three or more interactions = low risk.
These insights ensure that risk scores reflect consistent patterns, helping you address potential issues early.
Policy and Regulatory Alignment
Behavioral insights are further enhanced by embedding internal and regulatory policies into the scoring system. These policies are encoded as machine-enforceable rules. For example:
Require CFO approval for new wallet payments exceeding $5,000.
Block weekend transfers above $10,000.
Regulatory compliance is also critical. Sanctions screening, taint analysis, and exposure checks are applied to every payment before execution. If a recipient wallet has any indirect ties to sanctioned addresses, the transaction is flagged or blocked for further review.
To minimize risk, a "maximum risk" approach is often applied. If any single factor is deemed high risk, the transaction is either halted or manually reviewed. This ensures no critical warning goes unaddressed.
Real-Time Threat Intelligence
This component relies on live data feeds to track sanctions, malicious addresses, and fraud patterns. If new information identifies a previously safe wallet as risky, pending payments are re-assessed immediately.
How to Implement Contextual Risk Scoring
To avoid costly payment errors, contextual risk scoring is a proactive way to identify and mitigate risks before they escalate. The process involves three core steps: understanding your payment landscape, building a weighted scoring framework, and embedding automated checks into your workflow. Each step is designed to work together, creating a robust system that flags potential risks early.
Map and Classify Your Payment Ecosystem
Start by taking a close look at your payment ecosystem. Catalog all recipient wallets and classify them based on their transaction history. For instance:
Low risk: Wallets with 3 or more successful transactions.
Medium risk: Wallets with 1–2 successful transactions.
High risk: First-time recipient wallets.
Additionally, identify the relationships between internal accounts, such as subsidiaries or treasury accounts. These "Own-Account" transfers require different handling compared to external vendor payments. For example, they may need detailed audit trails and streamlined approval processes. Establish behavioral baselines for each category to better understand typical transaction patterns.
Once your payment ecosystem is fully mapped, you’ll be ready to create a scoring model that quantifies these risks.
Build a Scoring Framework
A scoring framework helps evaluate risk by considering key dimensions such as malicious connections and wallet age. Each factor should be weighted based on your organization’s risk tolerance. For example, if compliance is a top priority, proximity to sanctioned addresses might carry more weight than wallet age.
Here’s a helpful rule: always let the highest risk factor determine the overall score. For instance, even if a transaction is flagged as "low risk" in counterparty screening, but behavioral analysis marks it as "high risk", the transaction should be treated as high risk.
Risk Factor | High Risk | Medium Risk | Low Risk |
|---|---|---|---|
Interaction History | 0 interactions | 1–2 interactions | 3+ interactions |
Wallet Age | 0 transactions | <3 transactions OR | ≥3 transactions AND |
<7 days old | >7 days old | ||
Malicious Proximity | 0–2 hops away | 3 hops away | 4+ hops or none |
Dormancy | N/A | Last transaction | Active within |
>180 days ago | 180 days |
Refer to earlier definitions for a more detailed breakdown of these risk factors.
Once your scoring framework is ready, the next step is to integrate it directly into your payment workflow.
Run Pre-Execution Risk Checks
The final step is embedding automated risk checks into your payment workflow - before any signatures are applied. Every payment should trigger simultaneous checks, such as sanctions screening, taint analysis, and policy enforcement. For example:
Flag dormant wallets inactive for over 180 days.
Flag new wallets with fewer than three transactions.
Set up automated processes to halt payments flagged as high risk, route medium-risk transactions for manual review, and allow low-risk payments to proceed. The goal is to make these checks mandatory, ensuring no payment advances to the signing stage without passing through your risk-scoring framework. These automated safeguards close the loop, reinforcing treasury operations and preventing errors before they occur.
How Stablerail Enables Contextual Risk Scoring

Stablerail steps up to meet the demand for real-time risk evaluation by offering a suite of tools that secure payment decisions. Acting as a control plane, it integrates contextual risk scoring into stablecoin transactions before they are signed. Tailored for finance teams managing $1M to $50M annually in stablecoin volume, it combines the governance of traditional bank wires with the speed of blockchain settlements.
The platform is built around a straightforward idea: automated agents verify the context of transactions before human approval, ensuring treasury safety. Here’s a closer look at how its key modules work to protect every payment.
Self-Custodial Wallets with Pre-Sign Verification
Stablerail secures funds through MPC wallets compatible with major chains (currently EVM, with plans to support Solana) and supports stablecoins like USDC and USDT. Importantly, Stablerail itself does not have unilateral signing authority.
Before any payment is executed, the platform conducts rigorous pre-sign checks. These include sanctions screening, exposure analysis, policy enforcement, behavioral anomaly detection, and counterparty risk scoring. Each check is accompanied by plain-English explanations, complete with policy references and timestamps for clarity.
To further enhance security, Stablerail simulates transactions to detect irregularities. For instance, if a vendor’s wallet address changes unexpectedly, the system automatically locks the payment and escalates it for review. High-value transfers exceeding $100,000 are subjected to a mandatory four-hour cooling-off period, reducing the risk of social engineering or simple errors.
"The copilot can read policies, transaction context, and on-chain data. It cannot hold keys, initiate transfers, or sign. Its only role is to block, flag, and explain." - Stablerail
Another layer of protection comes from its ability to detect freeze risks. By identifying tainted counterparties or risk patterns that might lead stablecoin issuers to freeze funds, Stablerail ensures your company’s financial runway remains intact before any payment is finalized.
Policy-as-Code for Finance Teams
Stablerail empowers finance teams to automate governance by creating machine-readable policies that are enforced for every payment intent. For example, rules like “Payments over $5,000 to new addresses require CFO approval” or “Weekend transfers over $10,000 need additional verification” are automatically applied, ensuring no user - executive or otherwise - can bypass them.
This automation eliminates the inefficiencies of managing wallet operations, spreadsheets, and messaging apps for approvals. Instead, Stablerail integrates limits, roles, whitelists, and time-based restrictions directly into the system. It also maintains a “Golden Source” of approved payees, locking payments for review whenever vendor details change. This structured rule enforcement seamlessly ties into its approval and audit workflows.
Approval Workflows and Audit Trails
Every action within Stablerail is meticulously recorded, creating a comprehensive audit trail that supports regulatory compliance. This ensures you can provide transparent justification for every payment decision to auditors, boards, or regulators.
The process is simple: create a payment intent (via invoice PDF, payout CSV, or API); allow agents to generate a Risk Dossier with a verdict (PASS, FLAG, or BLOCK) and explanations; review the dossier and either approve or override it with a documented reason; then finalize the transaction through MPC. The system logs everything, producing a receipt that details what was paid, why, who approved it, and the associated risk verdict.
For larger transactions, Stablerail supports multi-tiered approvals requiring quorums (e.g., CFO and COO). Role-based access ensures that the right individuals are involved at the right stages, adding yet another layer of security.
Maintaining and Updating Risk Scoring Models
Once you've set up a contextual risk scoring framework, keeping it updated is essential to address ever-changing threats.
Risk scoring isn’t static - it has to keep pace with shifting transaction patterns, changing vendor behaviors, and updated regulatory requirements. These changes often happen faster than finance teams can manually track. Between 2024 and 2025, businesses experienced an average loss of 7.7% of annual revenue due to fraud, highlighting the costly consequences of outdated risk models that fail to adapt to evolving threats.
The most effective models continuously refine risk assessments using real-world data. Every fraud case, successful transaction, or payment dispute feeds into the system, improving future evaluations. AI-driven fraud detection models, for instance, have achieved an average 38% reduction in fraud by integrating feedback from flagged transactions. This ensures that as fraudsters shift their strategies, your risk scoring evolves to stay ahead.
Risk models also need to grow with your counterparty relationships. A vendor’s risk profile may change over time, moving from initial on-chain credentials to a more established on-chain reputation. Regularly reassessing these scores ensures that trusted, long-term vendors aren’t treated with the same caution as new, unverified payees.
Continuous Monitoring and Adjustments
Risk thresholds need constant fine-tuning based on real-time metrics. Teams should adjust these thresholds by analyzing ongoing data, such as fraud rates and false decline percentages. For example, if legitimate transactions are being flagged incorrectly, raising the threshold for those counterparties can reduce unnecessary friction without sacrificing security.
External changes also demand immediate action. If a development server transitions to production, its risk score should reflect its increased business importance right away. Similarly, integrating real-time threat intelligence - such as data from the KEV catalog or EPSS - keeps risk scores aligned with current threats. These proactive adjustments, combined with pre-execution controls, help maintain accurate and timely risk assessments.
Using Feedback to Improve Models
Feedback loops turn static rules into dynamic, adaptive systems. This continuous learning process is key to proactive risk management. For instance, transactions flagged with mid-range risk scores that are routed for manual review generate valuable training data. Each decision - whether to approve, decline, or escalate - helps the model improve, reducing the need for manual intervention over time while enhancing accuracy.
Collaboration across departments also plays a critical role. Teams from Finance, Legal, and IT contribute unique insights into impact ratings, ranging from Insignificant to Catastrophic. Their input ensures that risk scores reflect both operational priorities and regulatory demands, keeping models aligned with frameworks like DORA, GDPR, and NYDFS.
"Every payout generates a defensible receipt: what was paid, why, who approved, and the risk verdict." - Stablerail
This level of auditability doesn’t just satisfy regulators - it also provides the data needed to identify patterns in flagged transactions, refine scoring logic, and strengthen payment governance over time.
Conclusion
Contextual risk scoring takes stablecoin payments to the next level by making transactions smarter and more secure. By integrating counterparty risk assessment, behavioral analysis, and real-time threat intelligence, finance teams can stop costly mistakes before they happen. Plus, the system creates audit-ready documentation that aligns with regulatory requirements.
On a practical level, this approach simplifies legitimate transactions by applying customized verification based on actual risk levels. Trusted vendors can transact without delays, while genuinely suspicious activities are flagged for review. This not only cuts down on compliance team fatigue but also avoids the $118 average cost per false positive that comes from wrongly rejecting valid transactions.
"Agents verify the intent. Humans sign the transaction." - Stablerail
Stablerail exemplifies what an ideal contextual risk scoring solution should look like. Positioned between custody and transaction signing, the platform enforces mandatory risk checks on every payment intent. It ensures full control of your keys through pre-sign verification, policy-as-code enforcement, and a self-custodial setup. Tailored for companies managing $1M–$50M annually in stablecoins, it scales effortlessly with transaction volume, delivering CFO-level governance without slowing operations.
With global payment fraud losses surpassing $30 billion each year, the question isn't whether contextual risk scoring is useful - it's whether you can afford to operate without it. This isn't just about checking a compliance box; it's about building a resilient and efficient treasury in an on-chain world. Proactive risk management is the key to protecting your treasury and ensuring smooth, compliant payments.
FAQs
What data does contextual risk scoring use?
Contextual risk scoring is a method used to assess payment risks by analyzing various data points. These include sanctions and exposure screening, behavioral anomalies like unusual payout patterns or activity at odd hours, counterparty risk, and policy compliance details. By evaluating these factors, businesses can spot potential problems early - before agreements are finalized.
How can teams review payments before a stablecoin transfer settles?
Teams can now assess payments before a stablecoin transfer is finalized by leveraging automated pre-sign checks and risk evaluation tools built into a governance layer. These tools handle tasks like sanctions screening, policy enforcement, behavioral anomaly detection, and counterparty risk scoring.
The system generates a detailed risk dossier with outcomes such as PASS, FLAG, or BLOCK, giving approvers the ability to carefully review and decide on transactions. Every decision and action is logged in an audit trail, ensuring full accountability and transparency.
How do you reduce false flags without weakening compliance?
Reducing unnecessary alerts while staying compliant means leveraging context-aware analysis to pinpoint real risks. This involves examining behavioral trends, transaction histories, and operational guidelines to filter out noise. Tools that integrate anomaly detection, counterparty risk scoring, and evidence-backed insights help ensure alerts are relevant and actionable.
On top of that, using policy-as-code governance and incorporating human-in-the-loop reviews adds a layer of clarity and accuracy. These approaches strike a balance between cutting down false positives and maintaining strict compliance standards.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


