
Behavioral Risk Monitoring and rule-based fraud detection systems have distinct approaches to tackling financial fraud. Here's the key takeaway: static rule-based systems often fail to keep up with modern fraud tactics, while behavioral monitoring analyzes user behavior in real-time to catch threats before they escalate.
Key Points:
Rule-based systems rely on predefined criteria (e.g., transaction limits or flagged IPs) to detect fraud, but they’re rigid and struggle with new fraud techniques.
Behavioral monitoring focuses on how users interact - like typing speed, mouse movements, and navigation patterns - to detect subtle anomalies.
Rule-based systems generate false positive rates of 85%-99%, overwhelming teams with irrelevant alerts. Behavioral monitoring reduces false positives by up to 90%.
Continuous monitoring allows behavioral systems to detect threats mid-session, while rule-based systems only check at specific points (e.g., login or checkout).
Behavioral systems leverage machine learning for real-time analysis, while rule-based systems require manual updates, making them slower to adapt.
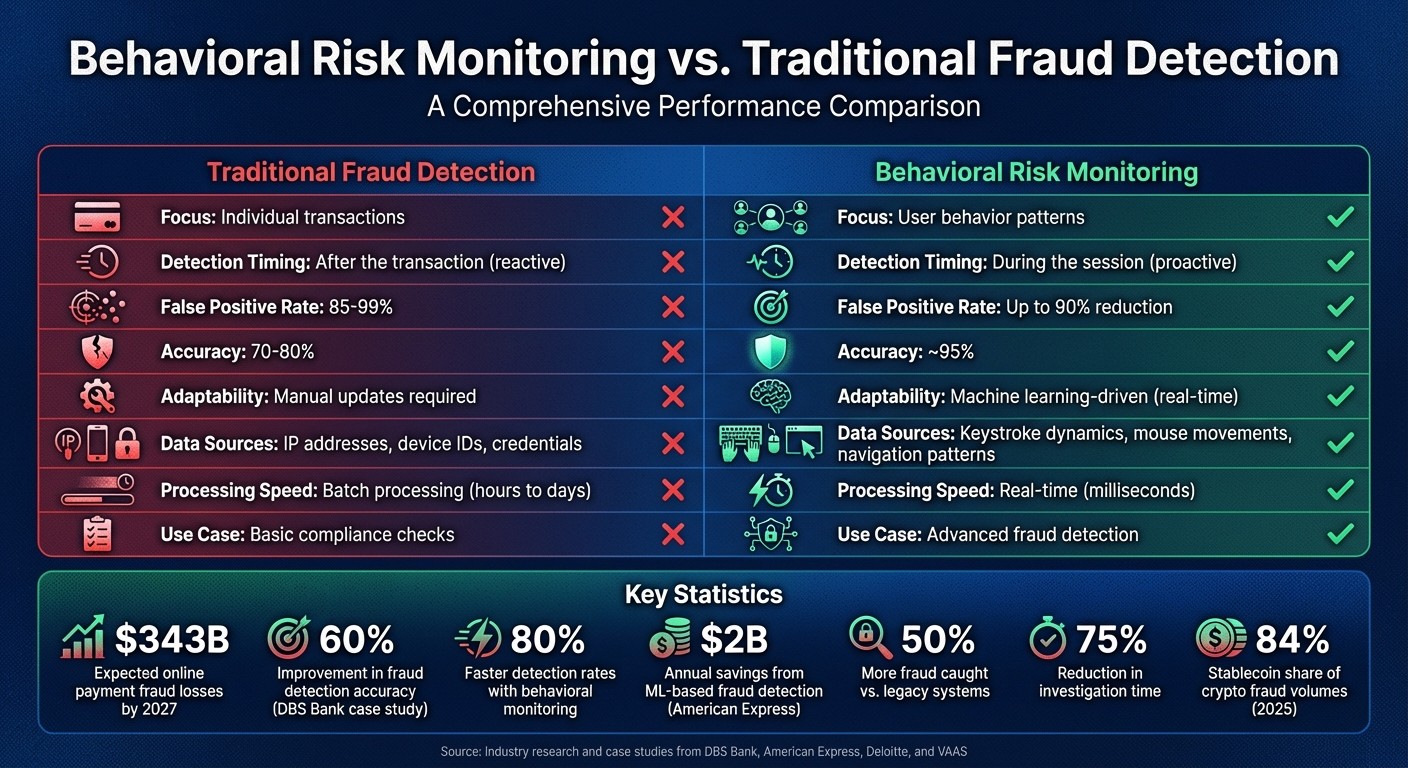
Quick Comparison
Feature | Rule-Based Systems | Behavioral Monitoring |
|---|---|---|
Focus | Individual transactions | User behavior patterns |
Detection Timing | After the transaction | During the session |
False Positive Rate | 85%-99% | Up to 90% reduction |
Adaptability | Manual updates | Machine learning-driven |
Use Case | Basic compliance checks | Advanced fraud detection |
Behavioral monitoring is a game-changer for fraud prevention, especially in high-risk areas like stablecoins, where fraud accounted for 84% of crypto fraud volumes in 2025. By analyzing behavior in real-time, it offers a smarter, faster way to identify risks while reducing unnecessary alerts.
Behavioral Risk Monitoring vs Traditional Fraud Detection: Key Differences and Performance Metrics
Revolutionizing Fraud Prevention with Behavioral Intelligence
What Is Traditional Fraud Detection?
Traditional fraud detection systems work on a straightforward principle: flag any transaction that meets certain predefined criteria. These systems rely on fixed rules to identify suspicious activity, making them predictable and easy to understand. This predictability helps compliance officers justify decisions to regulators, but it also makes the approach rigid and inflexible.
These systems typically analyze individual transactions or isolated events, focusing on specific data points like IP addresses, device fingerprints, or transaction amounts at key moments - such as during login or checkout. For example, if a transaction exceeds a preset threshold in terms of volume, frequency, or velocity, the system triggers an alert. This method works well for spotting familiar fraud patterns, such as large wire transfers to sanctioned countries or a rapid series of transactions that might signal an account takeover.
However, this rigidity is also a weakness. Criminals take advantage of these static rules by structuring their activities to avoid detection. For instance, instead of making a single $50,000 transfer, they might split it into ten $5,000 transactions to stay under the radar. Since these systems require manual updates to address new fraud tactics, they often lag behind evolving schemes. As Satish Lalchand from Deloitte points out:
"AI is often a key part of banks' fraud prevention strategies... to detect unknown cases of known fraud schemes".
This highlights a major limitation: static rules alone can't keep up with constantly changing fraud tactics.
The operational challenges of these systems are significant. False positive rates range between 85% and 99%, forcing teams to spend countless hours investigating alerts that turn out to be irrelevant. Meanwhile, global online payment fraud losses are expected to surpass $343 billion by 2027. A survey of 4,000 payments professionals revealed that 75% of industry leaders believe fraud is evolving faster than their organizations can adapt.
Despite their limitations, traditional systems still serve a purpose. They are effective for meeting basic regulatory requirements, such as screening transactions against OFAC sanctions or enforcing country-specific limits. However, the reactive nature of these methods underscores the pressing need for a more dynamic approach. Unlike these static systems, behavioral risk monitoring provides proactive insights by analyzing user behavior - a concept explored further in the next section.
What Is Behavioral Risk Monitoring?
Behavioral risk monitoring changes the way organizations approach fraud detection and prevention. Instead of depending solely on traditional user-provided data like passwords, device IDs, or transaction details, these systems focus on analyzing how users interact with platforms. It's like observing a user's digital "body language" - keystroke rhythms, mouse movements, navigation habits, and how quickly forms are completed.
Machine learning plays a key role here, creating baseline behavioral profiles for individual users or groups. Every interaction is compared to this profile in real-time, often within milliseconds. This allows the system to differentiate between legitimate activity and potential fraud. Sahil Kataria from FluxForce puts it this way:
"Behavioral analytics... doesn't look at what is being done; it studies how it's being done. Every keystroke, mouse movement, and login pattern tells a behavioral story."
This method is proactive, not reactive. Instead of waiting for a transaction to violate a predefined rule, behavioral systems detect subtle deviations from normal patterns - those hard-to-spot "unknown unknowns" that static rules often miss. For instance, if a user navigates a payment form unusually fast or exhibits mechanical mouse movements typical of bots, the system flags the session immediately.
Real-World Success Stories
The effectiveness of this approach is backed by real-world results. In early 2024, DBS Bank introduced an AI-powered monitoring system capable of analyzing 1.8 million transactions per hour. This upgrade led to a 60% improvement in fraud detection accuracy and cut false positive alerts by 90%, compared to their older manual, rule-based methods. Similarly, between May and July 2025, TickPick integrated an AI tool to strengthen its fraud detection. Within just three months, the system approved $3 million in legitimate transactions that would have been wrongly flagged by their traditional rules.
Continuous Authentication for Better Security
Beyond detection, behavioral monitoring also enables continuous authentication throughout a user session. Unlike traditional systems that verify identity only at login, these solutions monitor behavior throughout the interaction. If a user's typing rhythm or device usage suddenly shifts mid-transaction, the system triggers a review. This allows for the detection of account takeovers that might otherwise go unnoticed.
In highly sensitive areas like the stablecoin ecosystem, continuous monitoring is critical. These systems analyze interaction patterns (such as protocol relationships), network activity (like multi-hop fund transfers), and timing data (such as transaction bursts) to identify laundering tactics and other fraudulent activities. This level of scrutiny directly counters the advanced evasion techniques used by bad actors.
Key Differences Between Behavioral Risk Monitoring and Traditional Fraud Detection
The main distinction between these two approaches lies in how they perceive and manage risk. Traditional fraud detection works like a checkpoint, examining individual transactions against predefined rules. For instance, a payment exceeding a certain limit or coming from a flagged source might trigger an alert. Behavioral risk monitoring, however, takes a broader view by analyzing entire user sessions, focusing on behavioral patterns rather than isolated actions. This shift allows for a more nuanced approach to identifying potential fraud.
Traditional systems focus on what is happening - things like transaction amounts, device identifiers, or login credentials. In contrast, behavioral systems emphasize how actions are performed. They monitor details such as typing speed, mouse movements, and navigation habits. This makes it much harder for fraudsters to replicate, as mimicking someone’s natural behavior is far more complex than duplicating static data points.
Another key difference is how adaptable these systems are. Rule-based traditional systems are static and reactive. They depend on manual updates to address new fraud tactics. Behavioral systems, on the other hand, use machine learning to dynamically adjust risk thresholds in real time as they process new data. This adaptability enhances their ability to detect threats proactively.
The timing of detection also sets these methods apart. Traditional systems often verify users only at specific points, like login or checkout, and stop monitoring afterward. Behavioral risk monitoring provides continuous authentication throughout the session, allowing it to catch suspicious activity mid-interaction. For example, American Express implemented a machine learning-based system that identifies anomalies within milliseconds, saving the company $2 billion annually in fraud losses.
The table below highlights the core differences between these approaches.
Comparison Table
Attribute | Traditional Fraud Detection | Behavioral Risk Monitoring |
|---|---|---|
Primary Focus | Individual transactions, static rules | Patterns, context, and user behavior |
Data Sources | IP address, device ID, credentials | Keystroke dynamics, mouse movements, navigation patterns |
Detection Timing | Point-in-time (e.g., login, checkout) | Continuous (throughout session) |
Adaptability | Manual updates for new threats | Real-time, machine learning-driven |
False Positive Rate | 85–99% | Up to 90% reduction |
Accuracy | 70–80% | ~95% |
Benefits of Behavioral Risk Monitoring
Switching to behavioral monitoring brings clear advantages, improving critical areas that static systems often fall short on.
One standout benefit is the ability to detect fraud schemes that haven’t been seen before. By analyzing user interactions and adapting to new patterns, behavioral models stay ahead of evolving threats. As Satish Lalchand from Deloitte puts it:
"AI is often a key part of banks' fraud prevention strategies... to detect unknown cases of known fraud schemes and to find how criminals are changing to evade detection".
This adaptability is crucial. Unlike static systems, behavioral monitoring continuously learns and adjusts in real time. It doesn’t rely on manual updates when fraud tactics change. In a world where online payment fraud losses are expected to surpass $343 billion by 2027, being proactive can mean the difference between stopping a threat early and incurring massive losses.
The benefits go beyond just better detection. Behavioral screening can recover revenue by reducing false positives - those legitimate transactions wrongly flagged as fraud. This approach can save millions in approved orders that traditional methods might have declined. It also frees up fraud teams to focus on actual threats instead of wasting time on unnecessary checks.
Another key advantage is the seamless experience it provides. Behavioral monitoring works in the background, analyzing interactions without adding extra steps for users. Multi-factor authentication or manual verifications are only triggered when a real anomaly is detected. This ensures a smooth experience for legitimate users while maintaining strong security - something static systems often struggle to balance effectively.
Limitations of Traditional Fraud Detection
Traditional fraud detection systems are struggling to keep up with the pace of modern threats. Despite $136.5 billion spent annually on compliance in Europe alone, these systems manage to intercept just 0.1% of global criminal funds. Clearly, something isn’t working.
The main issue lies in their outdated design. These systems were developed for simpler fraud scenarios and depend heavily on static "if-then" rules. For example, a system might flag transactions over $10,000. While this approach works for known patterns, it falls apart when criminals change their tactics. Adjusting to new schemes requires manual intervention, with analysts painstakingly hand-coding new rules. This slow process makes it impossible for these systems to keep up with evolving threats, leading to inefficiencies and delays.
Another major problem is the high rate of false positives. Rule-based systems often generate false positives exceeding 95%, with some estimates ranging from 85% to 99%. This overwhelms fraud teams with irrelevant alerts, leaving them less time to focus on actual threats. Meanwhile, fraud losses continue to rise - from $28.4 billion in 2020 to $33.5 billion in 2022 - and are expected to hit $43.47 billion by 2028.
Legacy processing methods add to the problem. Many older systems rely on batch processing, which means transactions are analyzed hours or even days after they occur. By the time fraud is detected, the damage is often irreversible. On top of that, these systems primarily focus on static signals like IP addresses or device fingerprints. Criminals can easily spoof, recycle, or rotate these signals at scale, exploiting these weaknesses.
Another critical flaw is the reliance on siloed, outdated data. Traditional systems typically pull information from a single institution, making it impossible to get a full picture of a user's financial activity across multiple platforms. This fragmented view creates blind spots, leaving room for sophisticated fraudsters to operate undetected. Without a comprehensive risk profile, these systems remain vulnerable. As SEON points out:
"Traditional methods such as device checks, two-factor authentication, biometrics, and security questions are increasingly outdated against sophisticated new fraud techniques".
How Stablerail Implements Behavioral Risk Monitoring

Stablerail takes a proactive approach to behavioral risk monitoring by focusing on transactions before they are signed, rather than reacting after they’re recorded. This pre-signature layer combines behavioral anomaly detection with policy enforcement, acting as a decision-support system rather than an automated blocker. Whenever a payment intent is initiated - whether through an invoice upload, a CSV batch, or an API call - the system evaluates the transaction by comparing it against both historical patterns and real-time risk signals.
The system watches for behavioral red flags, like unusual time-of-day activity, atypical transaction amounts, or irregular payout patterns - anomalies that traditional rule-based systems might miss. For example, if a vendor typically receives payments between $2,000 and $5,000, a $15,000 transfer at 2:00 AM on a Saturday would stand out as suspicious. Instead of automatically blocking such a transaction, Stablerail generates a Risk Dossier that assigns one of three outcomes: PASS, FLAG, or BLOCK. This dossier includes clear, clause-specific explanations for its decision.
This process is made possible through policy-as-code compliance governance. Finance teams can define machine-enforceable rules like, “New address payments over $5,000 require CFO approval and verification” or “Weekend transfers over $10,000 need additional approval”. These policies are automatically applied to every transaction. Stablerail’s system integrates both on-chain data (like transaction hashes, gas fees, and blockchain events) and off-chain context (such as API logs, KYC/AML data, and vendor histories) to create a thorough risk profile.
Feature | Stablerail Behavioral Risk Monitoring | Traditional Fraud Detection |
|---|---|---|
Timing | Pre-transaction (Pre-sign) | Post-transaction or reactive |
Governance | Policy-as-code (automated enforcement) | Manual "if-then" static rules |
Audit Trail | Cryptographic "Policy Trace" & Risk Dossier | Basic on-chain transaction hashes |
Context | Combines on-chain data with off-chain identity/KYC | Limited to basic on-chain data |
Every step in the process - whether it’s the creation of a payment intent, an approval, an override, or the final signature - is logged in a detailed audit trail secured with cryptographic proofs. This trail includes wallet addresses, timestamps, risk scores (on a scale of 0–100), triggered policy clauses, and Merkle proofs that link these entries to blockchain records. If an auditor or regulator questions a flagged transaction, Stablerail provides CFO-level evidence, showing who reviewed the payment, what anomalies were flagged, and why any overrides occurred. This encrypted, comprehensive audit trail not only satisfies regulatory requirements but also demonstrates the system’s reliability.
Use Cases and Effectiveness
Behavioral monitoring shines in areas where traditional fraud detection systems struggle, especially when corporate finance teams need to identify anomalies that don’t fit rigid rule-based patterns. Take, for example, a vendor typically receiving payments between $2,000 and $5,000 suddenly requesting a $15,000 transfer at 2:00 AM on a Saturday. Traditional systems might either miss this irregularity if it falls just outside predefined limits or generate an overwhelming number of alerts, making it harder to identify real threats.
The efficiency of AI-powered behavioral monitoring is evident in recent examples. In January 2026, VAAS reported a 96.66% reduction in transaction analysis time after implementing AI-driven anomaly detection. The system processed over 1 million transactions and reduced review time from 15 minutes to just 30 seconds (). Similarly, DBS Bank introduced an AI monitoring system capable of processing 1.8 million transactions per hour. This resulted in a 60% improvement in fraud detection accuracy and a 90% reduction in false positive alerts ().
Real-world cases further highlight its effectiveness. In June 2024, Bybit, a cryptocurrency exchange, leveraged blockchain auditing to uncover eight unauthorized transactions initiated by an employee, Ho Kai Xin, to four unapproved addresses. This discovery led to a successful prosecution in Singapore’s High Court (). Another example comes from Coinbase, which, in May 2025, identified unusual audit log patterns that revealed unauthorized data access by overseas contractors. Acting quickly, the company mitigated a $20 million extortion attempt months before it could escalate ().
Behavioral monitoring also plays a critical role in corporate stablecoin transactions, where compliance demands are stringent. Stablecoins accounted for over 84% of all verified crypto fraud volumes in 2025, with traditional systems producing false positive rates exceeding 95%. Regulatory frameworks like the EU’s MiCA and the U.S. GENIUS Act (effective December 2026) now require detailed audit trails and executive accountability. Stablerail addresses these needs by generating immutable Risk Dossiers, which document every decision - who reviewed flagged payments, what triggered the alert, and why overrides occurred - before funds are transferred. This proactive approach stands in stark contrast to traditional systems that only analyze activity after transactions are complete.
These examples demonstrate how behavioral monitoring not only prevents risky transactions but also reduces unnecessary alerts, ensuring smoother and more secure processing.
Performance Metrics Comparison
When comparing performance metrics, the differences between traditional fraud detection systems and behavioral risk monitoring become clear. Traditional systems have alarmingly high false positive rates, ranging from 85% to 99%. This leads to "alert fatigue", where compliance teams waste valuable hours investigating benign activity while genuine threats go unnoticed. On the other hand, behavioral risk monitoring significantly reduces false positives and improves detection accuracy by 60%.
Speed and accuracy are equally vital. Traditional systems rely on batch processing, which delays threat detection by hours or even days. Behavioral monitoring, however, works in real time, enabling detection rates that are 80% faster by analyzing data as it moves, not after the fact. Additionally, investigation times are slashed by 75%, thanks to AI-driven analysis, allowing compliance teams to focus on complex cases instead of routine tasks.
Operationally, the benefits extend to reduced investigation time and better fraud prevention. Traditional anti-money laundering (AML) systems produce alerts where 98% are deemed non-actionable. In contrast, behavioral models detect 50% more fraud while cutting through the noise that overwhelms analysts. As Satish Lalchand from Deloitte explains:
"AI is often a key part of banks' fraud prevention strategies... to detect unknown cases of known fraud schemes and to find how criminals are changing to evade detection".
Comparison Table
Performance Metric | Traditional Fraud Detection | Behavioral Risk Monitoring | Stablerail Specific Capabilities |
|---|---|---|---|
False Positive Rate | High (85%–99%) | Low (up to 90% reduction) | Pre-sign behavioral anomaly detection minimizes noise before authorization |
Detection Speed | Batch processing (hours to days) | Real-time (milliseconds) | Instant Risk Dossier generation with PASS/FLAG/BLOCK verdicts at point of intent |
Threat Response | Reactive; post-event alerts | Proactive; pre-authorization blocking | Policy-as-code enforcement stops risky payments before signing |
Loss Prevention | Limited; reactive to known patterns | Up to 40% reduction in fraud losses | Immutable audit trail with plain-English explanations for every decision |
Investigation Time | Manual review required | 75% faster with AI-enabled analysis | Automated counterparty risk scoring and taint screening reduce manual workload |
Detection Rate | Misses 50% of sophisticated fraud | Catches 50% more fraud than legacy systems | Behavioral anomaly agents flag deviations from baseline patterns (time, amount, frequency) |
These metrics highlight how real-time, proactive monitoring - such as Stablerail's approach - delivers superior results in fraud detection and prevention.
This is especially critical for corporate stablecoin payments, which accounted for 84% of verified crypto fraud volumes in 2025. Traditional systems, with false positive rates exceeding 95%, struggle to meet the dual demands of accuracy and compliance. Stablerail addresses this by mandating pre-sign checks, including sanctions screening, policy enforcement, behavioral anomaly detection, and counterparty risk scoring. These checks happen before a transaction is authorized, ensuring threats are caught at the decision-making moment rather than during post-transaction audits. This proactive strategy not only prevents losses but also establishes a solid governance framework, securing corporate stablecoin payments before they are finalized.
Conclusion
The divide between older fraud detection methods and behavioral risk monitoring isn't just technical - it’s about how operations are handled. Legacy rule-based systems often overwhelm teams with a staggering 85%–99% false positive rate, rely on reactive threat detection, and demand excessive manual reviews. Behavioral monitoring takes a different approach: it evaluates patterns in real time, predicts risky behavior before transactions are authorized, and significantly cuts down investigation times.
This operational gap becomes even more critical in the context of corporate stablecoin payments, which accounted for 84% of verified crypto fraud volumes in 2025. Traditional tools frequently lack the nuance to differentiate between genuine urgency and sophisticated fraud attempts. As Satish Lalchand from Deloitte points out:
"AI is often a key part of banks' fraud prevention strategies... to detect unknown cases of known fraud schemes".
This is where proactive, context-aware systems prove indispensable.
Stablerail integrates behavioral risk monitoring directly into the payment process. Before any transaction is finalized, specialized agents perform pre-checks, including sanctions screening, policy enforcement, behavioral anomaly detection (such as unusual times of activity, deviations from typical transaction amounts, or irregular payout patterns), and counterparty risk scoring. The system then generates a Risk Dossier with a clear PASS/FLAG/BLOCK result, accompanied by plain-English explanations linked to specific policy clauses and timestamps. This "copilot, not autopilot" strategy ensures finance teams can identify threats at the decision-making stage, rather than after the fact.
This approach doesn’t just improve fraud detection - it strengthens overall payment governance. By combining the precision of bank wire rigor with the speed of blockchain settlements, it creates a robust governance framework. Every action - intent, flag, override, or approval - is recorded in an immutable audit trail, providing CFO-grade evidence to satisfy auditors, boards, and regulators. Stablerail safeguards the decision-making process, stopping fraud before funds are released.
With global online payment fraud losses expected to surpass $343 billion by 2027, moving from reactive rule-based systems to proactive intelligence isn’t optional - it’s critical. Behavioral risk monitoring gives modern finance teams the tools to keep up with evolving threats, offering the speed, precision, and context they need. By combining real-time behavioral insights with strong governance, finance teams can finally leave static systems behind and take control of fraud prevention.
FAQs
What data does behavioral risk monitoring track during a session?
Behavioral risk monitoring involves keeping an eye on data such as transaction patterns, timing, amounts, access behaviors, and any unusual activity. These irregularities might include unexpected spikes in activity or behaviors that stray from the usual patterns observed during a session.
How does continuous authentication detect account takeovers mid-transaction?
Continuous authentication works to spot account takeovers by identifying unusual behavior. This includes detecting anomalies like odd timing of actions, irregular payout patterns, or unexpected access methods. It also runs essential pre-sign checks to catch suspicious activity before a transaction is finalized, helping mitigate risks as they happen.
How do I set pre-sign policies and approvals for stablecoin payments in Stablerail?
Using the Policy Console in Stablerail, you can establish rules that are automatically enforced by the system. For example, you might set a rule requiring CFO approval for payments exceeding a specific amount or block certain stablecoins or wallet addresses. These policies are seamlessly applied to payment intents.
Before any payment is signed, it undergoes pre-sign checks. These checks include processes like sanctions screening and anomaly detection to ensure compliance and identify potential risks. Authorized approvers then review detailed Risk Dossiers, which provide a clear PASS, FLAG, or BLOCK verdict. This step ensures that every transaction aligns with governance standards and compliance requirements before final approval.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


