
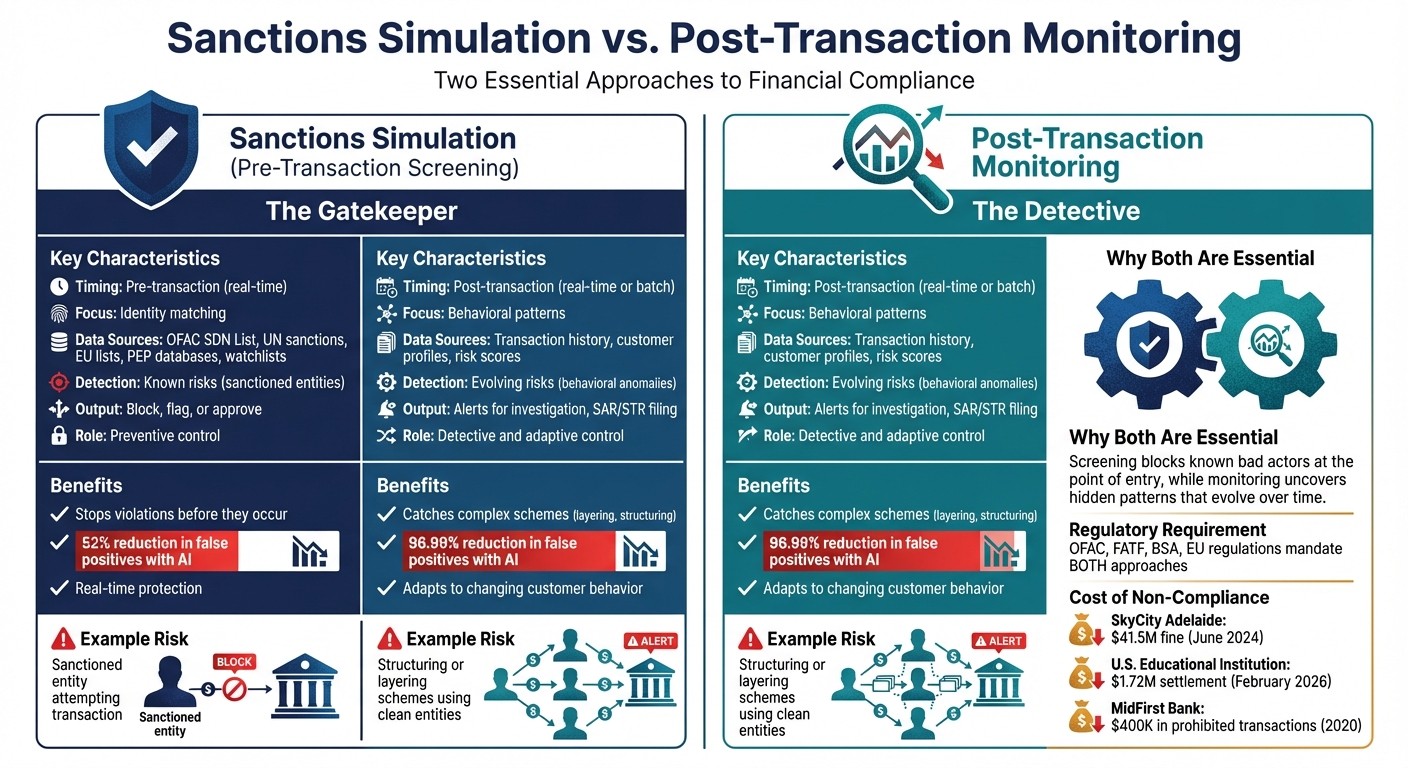
Compliance failures are costly and unavoidable. Whether you're screening transactions before approval or analyzing them afterward, both approaches are critical to avoiding penalties. For example, in February 2026, a U.S. educational institution settled for $1.72 million with OFAC for sanctions violations.
Here’s the difference:
Sanctions Simulation (pre-transaction screening): Stops prohibited transactions before they happen by checking names, entities, and wallet addresses against sanctions lists in real time.
Post-Transaction Monitoring: Examines completed transactions to detect suspicious patterns like layering or structuring that screening might miss.
Both methods are essential for compliance:
Screening prevents immediate violations.
Monitoring identifies risks that emerge over time.
Quick Comparison:
Both approaches work together to meet regulatory requirements and protect against financial crimes. Without them, organizations risk penalties, damaged reputations, and operational inefficiencies.
Sanctions Simulation vs Post-Transaction Monitoring: Key Differences
Mock Interview on Sanctions & Transaction Monitoring | AML & Compliance Case Studies
What is Sanctions Simulation?
In a world where sanctions evolve rapidly, pre-transaction screening acts as a crucial safeguard. Sanctions simulation - commonly referred to as transaction screening or payment screening - is a preventative measure that checks transaction details against sanctions lists, Politically Exposed Persons (PEP) databases, and other watchlists before payments are processed. This real-time process acts as a gatekeeper, intercepting and blocking prohibited transactions before any funds are transferred.
The screening process evaluates key transaction details, such as sender and recipient names, transaction amounts, currency, routing information, and the purpose of the payment. It also examines intermediaries and other parties involved in the transaction chain to ensure compliance. If a match with a sanctioned entity is detected, the system can take immediate action - freezing, suspending, or rejecting the transaction. This proactive approach is essential for maintaining compliance and mitigating risk.
"Transaction screening prevents prohibited transactions from occurring by detecting sanctions risks in real-time." - Napier AI
The importance of real-time screening is clear. For instance, in September 2020, MidFirst Bank in Oklahoma City processed 34 payments for two individuals who had just been added to the OFAC SDN List. Unfortunately, their screening vendor did not update the bank for 14 days, allowing 98% of these transactions - totaling $400,000 - to occur within six hours of the designation. This oversight led to a Finding of Violation from OFAC. Real-time screening could have stopped these payments immediately.
How Sanctions Simulation Works
Sanctions screening relies on advanced matching techniques to identify high-risk parties, even when there are spelling errors, aliases, or transliterations. Tools like fuzzy matching (e.g., catching "Muhammed" vs. "Mohamed"), phonetic matching, and natural language processing help uncover risks hidden in free-text fields.
The system extracts details about senders, recipients, and intermediaries, comparing them against global watchlists. These typically include databases such as OFAC's Specially Designated Nationals (SDN) List, UN Security Council sanctions, EU consolidated lists, and others specific to different jurisdictions. The system also flags Politically Exposed Persons (PEPs) and scans adverse media sources to identify reputational risks before relationships are established.
For high-speed payment systems like FedNow or instant stablecoin transfers, the screening process must deliver results in milliseconds to keep legitimate transactions flowing smoothly while blocking risky ones.
Frequent updates are critical to ensure that newly sanctioned entities don’t slip through the cracks. Systems relying on scheduled updates instead of real-time alerts create dangerous gaps, during which prohibited transactions could occur. By addressing these challenges, sanctions screening strengthens compliance efforts and reduces exposure to regulatory risks.
Benefits of Sanctions Simulation
Pre-transaction screening offers three major advantages: prevention, efficiency, and regulatory assurance.
Prevention: Stopping violations before they occur is far better than dealing with penalties after the fact. For example, in 2023, J-Dee Remittance Services faced a $170,000 fine for failing to adequately screen customers and related parties.
Efficiency: Screening powered by AI has been shown to reduce false positives by 52%, minimizing unnecessary manual reviews and keeping legitimate transactions moving quickly.
Regulatory Assurance: Organizations are expected to block transactions with sanctioned entities. Regulators like OFAC, the UN, and the EU impose strict liability for non-compliance, which can result in hefty fines. A documented screening process demonstrates a company’s commitment to compliance, offering protection during audits.
"A red flag at this stage prevents harmful activity from progressing further." - Guest User, Castellum.AI
In a fast-moving financial ecosystem, where transactions settle in seconds and operate 24/7 across borders, pre-transaction screening is non-negotiable. Without it, organizations risk sending irreversible payments to sanctioned entities - a costly mistake that post-transaction reviews cannot fix.
What is Post-Transaction Monitoring?
Think of pre-transaction screening as the bouncer at the door, while post-transaction monitoring is the detective working behind the scenes. Post-transaction monitoring involves the ongoing review of completed transactions to spot anomalies or illicit activities. Unlike screening - which happens once at a specific moment - monitoring continually evaluates risks throughout the customer’s lifecycle. This is crucial because customer behavior isn’t static; it can shift over time, introducing new risks.
"Screening is preventative, while monitoring is detective and adaptive." - sanctions.io
The key to post-transaction monitoring lies in its ability to detect risks that emerge after funds have moved, rather than just identifying risks present during the initial transaction. This makes it a cornerstone for long-term compliance.
For instance, in June 2024, SkyCity Adelaide, an Australian casino, faced a penalty of AUD 67 million (around $41.5 million) for failing to monitor high-risk customers effectively. Even when initial screening is done right, neglecting ongoing monitoring can lead to severe regulatory repercussions.
How Post-Transaction Monitoring Works
Post-transaction monitoring operates on a foundation of continuous oversight, leveraging rule-based thresholds, behavioral profiling, and advanced technologies like AI to flag suspicious activity.
Rule-Based Thresholds: These systems generate alerts for transactions that exceed pre-set parameters, such as transfers over $10,000 or more than five transactions in a single day. These thresholds can be tailored to align with a customer’s risk profile or business type.
Behavioral Profiling: This method analyzes a customer’s historical activity to identify unusual deviations. For example, a dormant account suddenly processing multiple high-value transfers would raise alarms. Similarly, transactions tied to high-risk regions that don’t match the customer’s stated business purpose are flagged.
AI and Machine Learning: These technologies excel at spotting subtle irregularities that basic rules might miss. By analyzing massive datasets - up to 50 million transactions per second - they can identify evolving criminal tactics.
Some common red flags include:
Structuring (Smurfing): Breaking large amounts into smaller transactions to avoid detection.
Layering: Moving funds through multiple accounts or entities to obscure the original source.
Velocity: Rapid fund transfers or sudden bursts of activity in previously inactive accounts.
Geographic Inconsistencies: Transactions involving high-risk jurisdictions or regions inconsistent with the customer’s profile.
A real-world example of layering occurred in June 2018, when the North Korean Lazarus Group stole cryptoassets from South Korean exchange Bithumb. They used a "peeling chain" method, funneling funds through numerous intermediate wallets and exchanges to mask their origin before depositing them into a Russia-based exchange. This kind of activity is exactly what post-transaction monitoring aims to catch.
When a monitoring system flags suspicious activity, analysts investigate further. If deemed suspicious, a Suspicious Activity Report (SAR) or Suspicious Transaction Report (STR) is submitted to agencies like FinCEN. In 2024, Ukraine’s State Financial Monitoring Service received 1,750,940 reports on transactions under scrutiny, with 82% triggered by threshold-based systems.
Benefits of Post-Transaction Monitoring
While screening acts as the first line of defense, monitoring steps in as the backup, addressing threats that evolve over time. It delivers three major benefits: identifying complex schemes, ensuring regulatory compliance, and adapting to dynamic risks.
Catching Complex Schemes: Monitoring uncovers patterns that screening alone would miss. For instance, pre-transaction screening might block known sanctioned entities but fail to detect money laundering schemes using seemingly legitimate accounts.
Regulatory Compliance: Ongoing monitoring is not optional - it’s a regulatory mandate. Compliance is viewed as a continuous process, and failures in monitoring are often cited in enforcement actions, even when initial onboarding was thorough. Globally, an estimated 2% to 5% of GDP is laundered every year.
Adapting to Changing Risks: Customer behavior evolves. An account considered low-risk during onboarding might later display high-risk activity. Monitoring identifies these shifts, enabling timely interventions before minor issues escalate into major violations.
"Monitoring is designed to capture emerging risk rather than existing risk. It is therefore essential for long term compliance." - sanctions.io
Sanctions Simulation vs. Post-Transaction Monitoring
This section dives into the timing, detection focus, and efficiency of two critical approaches: sanctions simulation and post-transaction monitoring. Each method brings unique strengths to the table, and understanding their differences helps clarify their roles in compliance strategies.
When Each Approach Operates
The key distinction lies in timing. Sanctions simulation - often called transaction screening - works instantly, intercepting transactions before they are executed or approved. On the other hand, post-transaction monitoring reviews transactions after they’ve been completed. This can happen in real time as transactions finalize or in scheduled batches, analyzing historical data to uncover patterns that develop over time.
Sanctions simulation is all about stopping violations at the point of execution. In contrast, post-transaction monitoring excels at spotting intricate schemes that unfold across multiple transactions.
What Each Approach Detects
Although both methods aim to combat financial crime, they target different risks. Sanctions simulation focuses on verifying identities by comparing transaction details - like names and addresses - against global watchlists maintained by organizations such as OFAC, the UN, and the EU. Post-transaction monitoring, however, analyzes behavioral patterns such as transaction volume, frequency, and consistency, comparing them against a customer’s usual activity.
“Screening by itself can’t do anything about [layering] since clean entities are used... monitoring would realise the unusual pattern.” – Sanction Scanner
This quote underscores a critical limitation: sanctions screening struggles to detect "clean" entities used in layering schemes because they don’t appear on sanctions lists. Monitoring bridges this gap by identifying unusual patterns that screening alone would overlook.
Comparison of Pre- and Post-Transaction Approaches
This table highlights how these approaches complement each other, offering a balanced strategy that addresses both immediate and long-term risks.
Accuracy and Efficiency
Examining their operational focus reveals how each method contributes to a robust compliance framework. Advances in AI have significantly reduced false positives for both screening and monitoring. For example, AI-powered transaction screening cut false positives by 52% in 2024. Some solutions now achieve up to an 88% reduction in false positives compared to manual processes. Meanwhile, AI-enhanced monitoring systems report a 96.99% drop in false positives and an 80% workload reduction.
These efficiency gains are vital given the sheer volume of transactions compliance teams handle. In 2024, Ukraine’s State Financial Monitoring Service received 1,750,940 reports on financial transactions, with 82% involving threshold transactions. Without AI, manually reviewing such a massive volume would be nearly impossible.
The technology driving these improvements is impressive. Screening tools now use fuzzy matching algorithms to account for variations in names, typos, and transliterations. Monitoring systems establish baselines for normal customer behavior, making it easier to flag deviations automatically. Together, these tools create a robust system capable of addressing both established and emerging threats.
Regulatory Requirements
Financial regulators around the globe emphasize the importance of both sanctions screening and post-transaction monitoring, treating them as equally essential compliance measures. For instance, the U.S. Office of Foreign Assets Control (OFAC) requires financial institutions to block transactions in real time if they involve sanctioned individuals, entities, or countries. Similarly, the Financial Action Task Force (FATF) categorizes screening as a "preventive control" and monitoring as a "detective and adaptive" measure designed to track evolving risks over time.
In the United States, the Bank Secrecy Act (BSA) mandates that institutions actively monitor transactions for suspicious activity, such as structuring or layering, and file Suspicious Activity Reports (SARs) when such patterns are detected. This is because static screening alone cannot uncover "clean" entities that may be used in sophisticated money laundering schemes. Post-transaction monitoring bridges this gap by identifying behavioral anomalies that initial checks might overlook. Together, these measures create a regulatory framework that demands both preventive and adaptive approaches.
Frequent updates to sanctions lists add another layer of complexity, making continuous monitoring indispensable. A customer who appears compliant today could be sanctioned tomorrow, which is why regulators stress the importance of ongoing surveillance.
"Regulatory enforcement actions frequently cite failures in ongoing monitoring rather than failures at onboarding. This reflects a clear expectation that compliance is continuous, not a one-time exercise." – sanctions.io
Failing to meet these compliance standards can result in substantial penalties. For example, in June 2024, SkyCity Adelaide was fined $41.5 million for neglecting to monitor high-risk customers and their transaction patterns over time. Just a few months later, in February 2026, a prominent educational institution paid a $1.72 million settlement to the U.S. Treasury after OFAC determined it had violated sanctions regulations. These cases highlight why both screening and monitoring are indispensable. Screening addresses immediate risks, while monitoring uncovers threats that emerge over time. This dual strategy forms the backbone of modern compliance systems, including those designed by companies like Stablerail.
How Stablerail Supports Both Compliance Approaches

Stablerail functions as an agentic control plane, seamlessly integrating pre-transaction screening and post-transaction monitoring into payment workflows. Its proactive compliance measures block transactions that fail pre-sign checks while also generating a cryptographic audit trail for every payment.
This dual strategy fills a crucial gap in corporate stablecoin payments. While custody platforms excel at managing keys, they lack the ability to consider the business context of transactions. For instance, they cannot determine if a transaction violates internal policies or involves a counterparty exposed to sanctions. Stablerail steps in as "the brain on top", ensuring compliance and safeguarding business decisions - not just the keys.
Pre-Transaction Screening with Stablerail
Stablerail prioritizes risk reduction by screening transactions before they are signed.
Using dedicated agents, the platform screens payments against global sanctions lists (OFAC, UN, EU, UK), evaluates counterparty risks, and enforces internal rules. Finance teams can define policies as code, such as:
"Payments to new addresses over $5,000 require CFO approval and verification."
"Weekend transfers exceeding $10,000 need additional authorization."
These rules are automatically applied to every transaction intent. Stablerail employs advanced matching algorithms to identify high-risk individuals or entities, even when aliases or name variations are used. For example, this approach could have prevented incidents like the one at MidFirst Bank in September 2020, where outdated screening data led to $604,000 in prohibited transactions over just six hours.
Once screening is complete, Stablerail generates a Risk Dossier with clear outcomes: PASS, FLAG, or BLOCK. Each result is accompanied by a plain-English explanation, ensuring transparency and clarity.
Post-Transaction Monitoring with Stablerail
Stablerail continues to ensure compliance through ongoing oversight after a transaction is processed.
Every action - intent creation, checks performed, flags raised, overrides applied, approvals granted, and signing - is recorded in a complete, unchangeable audit trail. This provides CFOs, auditors, and regulators with real-time, verifiable proof of compliance, meeting the growing demand for immediate transparency.
Additionally, Stablerail's behavioral anomaly detection identifies suspicious activities like "structuring" (splitting large amounts into smaller transactions to bypass thresholds), rapid transfers to high-risk regions, or patterns that deviate from a customer's usual behavior. By combining on-chain and off-chain data, the platform offers a detailed view of transaction activity, bridging the gap between traditional financial controls and the complexities of digital asset payments.
AI-powered screening further enhances efficiency, reducing false positives by 52% in 2024. This allows finance teams to focus their efforts on genuine risks instead of wasting time on irrelevant alerts. Stablerail’s approach ensures compliance without sacrificing operational efficiency, making it a critical tool for modern financial operations.
Conclusion
Sanctions simulation and post-transaction monitoring play distinct yet interconnected roles in compliance systems today. Screening acts as the first line of defense, stopping transactions by comparing details against global sanctions lists. Meanwhile, monitoring provides ongoing oversight, identifying suspicious behaviors like structuring or layering that only emerge when analyzing multiple transactions over time.
"Transaction screening and monitoring therefore serve as twin safety nets - screening blocks known bad actors at the point of entry, while monitoring uncovers hidden patterns that evolve over time." - Paul Keene, Shufti
Still, neither method is flawless when used on its own. Screening can't catch bad actors who operate through "clean" entities not yet flagged on watchlists. On the other hand, monitoring alone won't protect against immediate exposure to sanctioned parties. For example, a counterparty that initially clears screening could be added to a sanctions list overnight due to geopolitical changes, highlighting the need for continuous monitoring.
This is why regulators insist on a dual approach. Organizations like FATF, OFAC, and the EU require both strategies to ensure compliance. A stark reminder of the consequences came in June 2024, when SkyCity Adelaide, an Australian casino, was fined AUD 67 million (US$41.5 million) for failing to adequately monitor high-risk customers.
FAQs
When do I need both screening and monitoring?
You need both because screening and monitoring serve distinct roles in maintaining compliance. Screening acts as a proactive measure, identifying high-risk entities before a transaction takes place by reviewing sanctions lists, politically exposed persons (PEPs), and adverse media. On the other hand, monitoring is a continuous process, designed to flag suspicious activities or risks that might develop later. By combining these efforts, you create a well-rounded compliance strategy - stopping risks early while staying alert to new threats as they emerge.
How often should sanctions lists be updated?
Sanctions lists need to be updated often - many experts even suggest continuous or real-time updates. Why? Staying current helps organizations comply with the latest regulations and reduces risks tied to outdated data. Regular updates ensure your screening processes remain effective and aligned with evolving requirements.
What should happen when a transaction is flagged?
When a transaction is flagged, it goes through a thorough review process to identify potential risks or rule violations. Analysts carefully examine the alert to decide whether it represents a real concern or is simply a false positive. In platforms such as Stablerail, flagged transactions trigger the creation of a Risk Dossier. This dossier includes a verdict - PASS, FLAG, or BLOCK - along with the reasons behind the decision. Approvers then review the dossier and make the final call. Every action is meticulously documented in an audit trail, ensuring accountability and helping to prevent unlawful activities.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


