
When managing access to stablecoin treasuries, documenting every revocation event is non-negotiable. Why? Without proper records, audits become a nightmare, compliance risks skyrocket, and financial losses can occur. Here's what you need to know:
What to Log: Key details include timestamps, actor identities, action types, before/after states, justifications, and policy versions.
Why It Matters: These records help prove compliance, prevent mishandling, and provide clarity during audits or disputes.
How to Ensure Accuracy: Automated systems reduce errors, while immutable logging (e.g., blockchain) ensures records can't be altered.
Regulatory Stakes: Frameworks like MiCA and the GENIUS Act demand clear evidence of access controls, with penalties reaching $100,000 per day for non-compliance.
The stakes are high, but with the right systems in place, you can maintain secure, audit-ready records while avoiding regulatory pitfalls. Let’s explore how to build and maintain these logs effectively.
What Is The Process For Revoking SaaS User Access?
Core Components of Access Revocation Audit Trails
Essential Data Points for Access Revocation Audit Trails
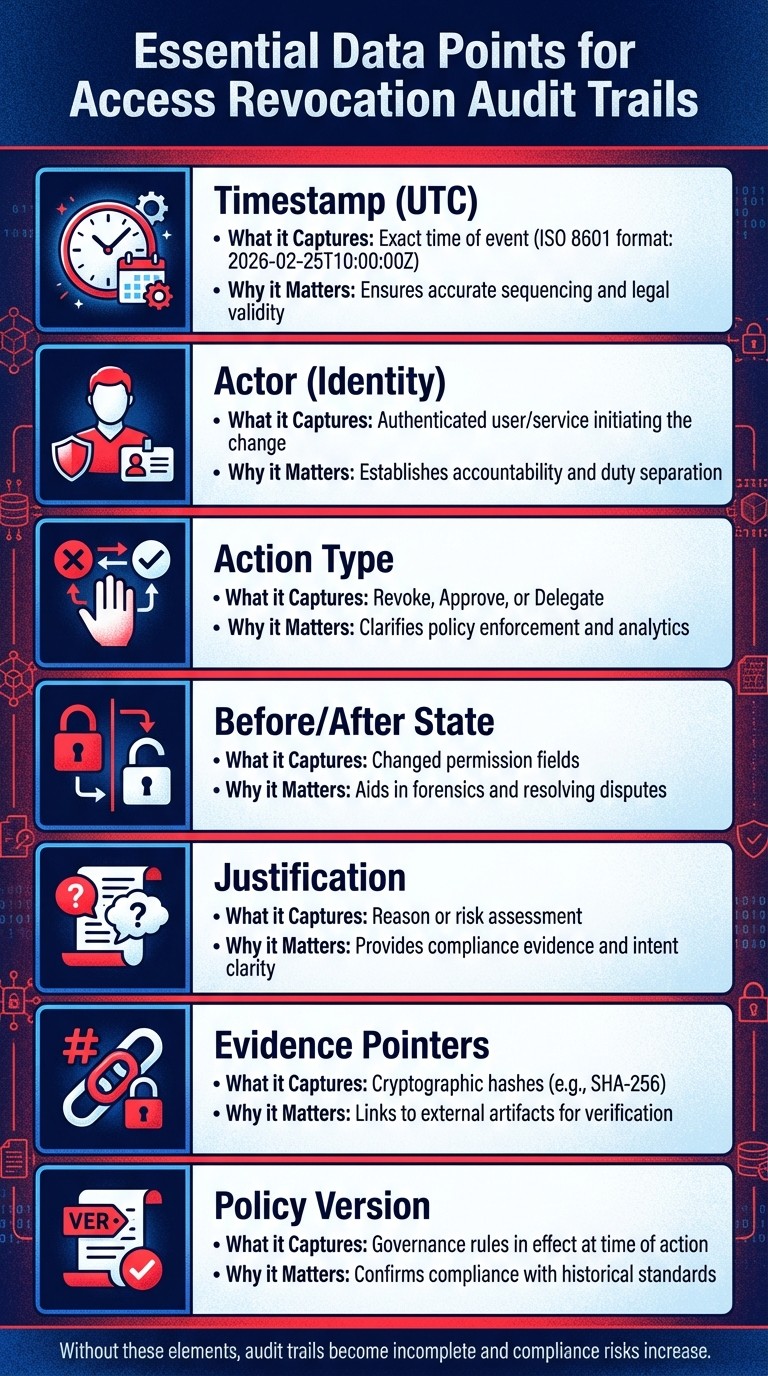
Building a thorough audit trail for access revocation requires capturing specific, detailed information at the moment changes occur. Without these key elements, the record becomes incomplete, leaving gaps that make it difficult to verify authority, compliance, or intent. A well-documented trail can mean the difference between passing an audit smoothly and facing regulatory consequences by following a stablecoin compliance checklist. Let’s break down the core components that create these robust records.
Required Data Points: Timestamps, Approver IDs, and Policy Versions
For an audit trail to hold up under scrutiny, every event must provide clear accountability. At a minimum, each revocation event should include standard metadata that establishes a verifiable chain of custody. This includes:
UTC Timestamps: Using the ISO 8601 format (e.g., 2026-02-25T10:00:00Z), timestamps ensure precise sequencing for legal and operational evidence.
Actor Identity: The authenticated user or service initiating the change must be recorded to uphold accountability.
Action Type: Whether it's a revoke, approve, or delegate action, this field clarifies the nature of the change.
Before/After State: Documenting what permissions were altered provides clarity for forensic investigations or dispute resolution.
Another crucial element is policy versioning. Recording which governance rule version was in effect at the time of the decision allows you to trace back the exact logic behind the action. For example, if a treasury policy changed on January 15, 2026, to require two approvers instead of one, your audit log must show whether a February 10 revocation adhered to Policy v2.3 or v2.4. Without this, proving compliance with the rules in place at the time becomes impossible.
Capturing justifications for each revocation adds the necessary "why" to the log. For instance, notes like "Employee offboarded per Section 4.2 of employment agreement" or "Vendor contract terminated" provide the context auditors need. To enhance security, link these justifications to cryptographic pointers (e.g., SHA-256 hashes), which allow external verification without exposing sensitive data directly in the log.
"An approval audit trail is the backbone of accountable operations... it becomes a single source of truth for regulators, auditors, and business leaders - evidence-grade, searchable, and ready for real-time analytics." - Sirion
While these data points are essential, how they are captured - manually or automatically - can make or break the system's reliability.
Manual vs. Automated Audit Trail Systems
Recording these details requires a process that minimizes risk and maximizes transparency. Manual systems, like using spreadsheets or emails, can capture the context behind decisions but are prone to errors, inconsistencies, and gaps. For example, if a finance manager manually updates a Google Sheet and emails IT for an access change, there’s no guarantee that the process is properly documented or that unauthorized changes didn’t occur in the interim.
Automated systems, on the other hand, centralize evidence and reduce the chance of human error. Organizations using immutable audit trails often see faster compliance checks and fewer reconciliation issues. For instance, Visa's use of Solana for USDC settlements, which handles over $3.5 billion in annualized stablecoin volume, highlights the scale at which automated systems can operate effectively.
The best approach combines the strengths of both. By linking manual justifications - like an invoice number or employee ID - to automated logs, you create a hybrid model. For example, cryptographic hashes of manual documents (e.g., KYC files or policy memos) can be stored in automated systems to tie human context to machine-executed actions. This ensures you have both the precision of automation and the business logic auditors need to see.
Setting Up Immutable Logging for Access Changes
One of the biggest challenges in managing access records is ensuring they remain unchangeable. Immutable logging ensures that once an access revocation or change is recorded, it cannot be altered or deleted. This is especially important for audits or regulatory checks, where proving the integrity of records is non-negotiable.
The backbone of immutability lies in cryptographic anchoring. When an access change happens, the system generates a cryptographic hash (like SHA-256 or Keccak256) and logs it onto a blockchain or an append-only ledger. This hash acts as a digital fingerprint - if anyone tries to alter the original record, the hash will no longer match, exposing the tampering attempt.
For large-scale operations, cost-efficiency also plays a role. On high-performance blockchain networks like Solana, logging events costs just $0.0005–$0.0007 per transaction. Additionally, Visa's projected $3.5 billion annualized stablecoin settlement volume by 2025 highlights how scalable and economically viable blockchain-based audit trails have become.
Using Blockchain for Tamper-Proof Logs
Blockchain technology offers tamper-proof logging by design. Smart contracts generate standardized events - like RoleRevoked or AccessChanged - for every state-changing action. These events capture critical details (such as who made the change, what was changed, and why) and store them as logs on the blockchain. Since each block is cryptographically tied to the one before it, rewriting historical records would require altering the entire chain, which is nearly impossible.
In practice, many systems use a hybrid approach. Full event data, including justifications and supporting documents, is stored in traditional databases or decentralized storage solutions like IPFS. A cryptographic hash of this data is then written to the blockchain. This method combines the searchability of conventional databases with the tamper-proof guarantees of blockchain technology.
For further accountability, multi-signature wallets enhance access control. For example, if a change requires three out of five executive approvals, each signature is recorded on-chain. This creates a transparent trail of who authorized the change and when.
"A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process." - Stablecoin Insider
Off-chain indexers like The Graph, Subsquid, or Covalent make blockchain logs more accessible. These tools listen for on-chain events, decode the information, and store it in searchable formats. To improve efficiency, smart contract events should include up to three indexed parameters (e.g., address indexed actor) for easier filtering by actor, target, or role.
Maintaining Complete and Real-Time Records
Immutability is only effective if every relevant event is captured in real time. An event-driven architecture ensures immediate logging, which is vital for identifying unauthorized access or social engineering attempts.
Logs should be stored using append-only methods, such as WORM (Write Once, Read Many) or object-lock storage, to prevent modifications. Separating responsibilities for executing revocations and reconciling logs further reduces the risk of unauthorized changes.
It's equally important to track changes to access policies themselves. For instance, if an approval threshold is updated from $5,000 to $10,000, this change should be logged with a timestamp and the identity of the person who made the update.
Emerging technologies like zero-knowledge proofs are also making compliance checks more efficient. These proofs allow systems to verify compliance without revealing sensitive data, simplifying what would otherwise be a labor-intensive reporting process.
To bring all these practices together, integrate audit logs with Security Information and Event Management (SIEM) systems. This enables real-time alerts for unauthorized access attempts or unusual patterns. Additionally, schedule regular exports of evidence packs, which consolidate logs, approvals, and supporting documents, to streamline audits and reduce manual work.
"The ultimate goal is operational security and trust minimization. A well-designed audit trail allows for real-time monitoring and automated alerting for anomalous transactions." - ChainScore Labs
How Stablerail Records Access Revocation Decisions

Stablerail meticulously documents every access revocation decision, capturing the reason, authority, and applicable policy in an audit-grade narrative. This transforms what might otherwise be simple logs into robust evidence suitable for regulators and auditors. It's especially useful for companies managing stablecoin volumes between $1 million and $50 million annually. The system's goal is to create immutable, audit-ready access records.
Before any change is permanently recorded on the blockchain, the system verifies the access adjustment. The policy engine ensures that every request aligns with pre-defined, programmatically enforced rules. These rules are encoded, making it impossible for even top executives to bypass limits, roles, or approval thresholds without the action being documented. As Stablerail puts it:
"Policy engine: Limits, roles, whitelists, and time windows are enforced programmatically. Even the CEO cannot bypass the code." - Stablerail
Every action generates a Proof-of-Control Receipt, which includes the action's details, a plain-English explanation, the identities of all approvers, and a risk verdict - either PASS, FLAG, or BLOCK. This receipt is directly linked to the system's verification layer, creating a secure and traceable chain of custody between finance teams and the blockchain.
Policy-as-Code Documentation for Revocation Decisions
Stablerail's policy-as-code approach ensures that every rule and modification is enforced automatically during access revocation. For example, if a policy states, "New address payments over $5,000 require CFO approval", the system translates this into enforceable code. Every access request is checked against these coded policies before execution, guaranteeing a verifiable record of compliance.
If a revocation request involves a user with signing authority for transfers exceeding $10,000, the system flags it as high-impact and routes it through the appropriate approval chain. Additionally, Stablerail logs any policy modifications, creating a complete history of both access changes and the evolution of access rules over time.
Risk Dossiers and Audit-Ready Evidence
Before finalizing an access revocation, Stablerail generates a Pre-Flight Risk Dossier. This dossier provides a verdict - PASS, FLAG, or BLOCK - alongside plain-English explanations referencing specific policy clauses, timestamps, and historical actions. As Stablerail explains:
"PASS / FLAG / BLOCK verdicts with plain-English reasons backed by evidence - not vibes." - Stablerail
For instance, if a finance team member with a history of initiating high-volume transfers is subject to an access change, the dossier documents each relevant transaction to ensure granular tracking.
In cases where an action is flagged but leadership decides to proceed - such as revoking access for a critical vendor relationship - the system delays execution until a documented override justification is provided. This override is permanently logged, creating a defensible record of any exceptions to standard procedures.
The final output is a comprehensive evidence package that includes the original request, the risk assessment, all approvals and override justifications, and the execution record. This structured, timestamped documentation allows auditors or board members to easily trace the decision-making process without needing to sift through scattered communications.
Stablerail also strengthens audit readiness by integrating with SSO and SCIM for identity management and enforcing MFA and hardware keys. These measures ensure that every identity in the audit trail is cryptographically verified and that there’s a clear separation between those executing revocations and the system recording them. This framework lays the groundwork for the maintenance practices discussed in the next section.
Maintaining Audit-Ready Access Records
Ensuring audit readiness goes hand in hand with maintaining accurate, reliable records. For finance teams following stablecoin treasury management best practices, this means keeping records precise and complete at all times. Under the GENIUS Act, signed into law on July 18, 2025, stablecoin issuers are required to publish monthly reports reviewed by independent accounting firms, with CEOs and CFOs personally certifying their accuracy. Below, we’ll explore the daily, weekly, and monthly practices needed to keep your audit logs consistently verified.
Organizations that adopt audit trail analytics have reported an impressive 3.2x return on investment (ROI) and millions in annual savings on governance programs. However, achieving these results demands a disciplined approach to record maintenance - merely storing logs isn’t enough.
Regular Log Reviews and Data Validation
To ensure records remain audit-ready, implement weekly control attestations. These reviews should confirm that no unauthorized access revocations occurred and verify that any flagged exceptions have been resolved with proper documentation. Importantly, this task should be handled by a team member who is not involved in executing access changes.
For operations with higher volumes, consider daily reconciliations. This involves matching on-chain activities with internal records for access changes, such as employee terminations or vendor offboarding. Any discrepancies should be investigated immediately rather than delayed until the next scheduled review.
"A stablecoin treasury cannot be 'a wallet that holds funds.' It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process." - Stablecoin Insider
On a monthly basis, revoke any stale token approvals to limit unnecessary risk and keep records up to date.
Tools like Stablerail can simplify these processes. Their system automates validation by generating evidence packs that include cryptographic proofs and blockchain transaction IDs. This automation reduces the need for manual data collection, making regulatory examinations more efficient.
Meeting Regulatory Documentation Standards
Maintaining compliance with external documentation standards is just as important as routine validation. Every access revocation event must include standardized metadata to meet both internal governance needs and external regulatory requirements.
Under the GENIUS Act, stablecoin issuers with a market capitalization exceeding $10 billion must adhere to federal regulations, including those outlined in the Bank Secrecy Act. Violations can result in civil penalties of up to $100,000 per day, so thorough documentation is not just advisable - it’s a financial necessity.
To stay ahead of potential issues, configure automated alerts for role changes, failed revocations, and unusual after-hours modifications. These alerts can help identify gaps before they become problems during audits. Stablerail’s system also monitors for behavioral anomalies, such as unexpected time-of-day access changes or deviations from normal patterns, and flags them for immediate review.
Lastly, prepare incident runbooks for scenarios like key compromises or phishing attacks. These protocols should include clear "halt" procedures to pause all operations while access is audited. When auditors ask, "What’s your plan if…?", having a predefined, documented response will demonstrate readiness and professionalism - not improvisation.
Conclusion
Thorough audit trails for access revocation decisions are at the heart of maintaining operational security, meeting regulatory requirements, and ensuring financial accountability in stablecoin treasury management. These trails document essential details - who revoked access, when it happened, and why - and without them, a treasury's security can quickly become a liability.
"If you can't answer 'who did what, when, why, with whose approval, and what exactly changed,' you don't have an agent system - you have a liability with a chatbot UI." - Hash Block
The importance of such evidence is hard to overstate. Immutable audit trails have been shown to deliver measurable returns on investment and cost savings, while global compliance spending surpassed $274 billion in 2023.
For stablecoin treasuries, which operate under the pressure of irreversible transactions and intense regulatory oversight, strong audit trails are non-negotiable. They offer three essential advantages:
Evidence-grade traceability: This creates a reliable source of truth for regulators and auditors.
Rapid forensic reconstruction: Instead of taking weeks, treasury teams can resolve disputes and investigate incidents in just minutes.
Separation of duties: By enforcing programmatic controls, audit trails ensure no single individual can dominate the access-change process.
When implemented effectively, audit trails are more than just a compliance tool - they are a safeguard for the integrity and efficiency of stablecoin treasury operations.
FAQs
What’s the minimum I should log for every access revocation?
To maintain a thorough audit trail, make sure to record the action taken, the identity of the person carrying out the revocation, the timestamp, and the reasons or evidence behind the decision. This level of detail helps provide clear justification for the decision, whether it's reviewed by auditors or regulators.
How do I make revocation logs tamper-proof without storing sensitive data on-chain?
To keep revocation logs secure and tamper-proof without revealing sensitive information on-chain, an immutable audit trail backed by cryptographic methods is key. Use cryptographic hashes or summaries stored off-chain, anchoring them with tamper-evident techniques like digital signatures. Additionally, tools such as secure multi-party computation (MPC) and policies-as-code can strengthen governance. This approach ensures a transparent and auditable system that safeguards log integrity while maintaining privacy.
How long should we retain access revocation audit logs for audits and regulators?
There’s no single rule for how long access revocation audit logs should be kept. However, it's generally recommended to retain them for a period that aligns with regulatory requirements, compliance standards, and audit needs. Depending on the jurisdiction and an organization’s internal policies, this could mean keeping logs for a few years - or even indefinitely.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


