
Cross-chain audit trails are critical for secure and transparent blockchain operations. They provide a tamper-proof record of every transaction, but maintaining consistency across multiple blockchains is challenging. Key issues include fragmented data, lack of standardization, and off-chain vulnerabilities. Without addressing these, organizations risk compliance failures, inefficiencies, and regulatory penalties.
Key Insights:
Immutable Records: Blockchain audit trails rely on cryptographic signatures and hash-linking to secure data.
Challenges: Cross-chain audits face issues like siloed data, inconsistent confirmation rules, and off-chain risks.
Solutions: Use identity linking, cryptographic timestamping, and structured metadata to create reliable trails.
Cost Efficiency: Storing raw data on-chain is expensive; anchoring hashed logs reduces costs significantly.
Tools and Practices:MPC wallets, policy-as-code, and risk dossiers ensure secure, traceable, and compliant operations.
Quick Overview:
Problem: Fragmented logs and inconsistent standards across blockchains.
Impact: Inefficient audits, regulatory fines, and operational risks.
Solution: Unified systems like Stablerail offer secure, policy-driven audit trails with real-time verification.
This article explains how to overcome these challenges using secure systems, cryptographic methods, and structured governance.
Blockchain Intelligence for Compliance: TRM Labs Cross-Chain Tracing
Core Components of Cross-Chain Audit Trails
Cross-chain audit trails are built on three essential layers: identity, cryptographic timestamping, and transaction context. Each layer addresses specific verification needs, helping auditors, regulators, and finance teams reconstruct transaction histories with precision.
Identity and Attribution
A wallet address like 0x123...abc on Ethereum might belong to your CFO, but when that same individual operates on Base or Polygon, traceability becomes fragmented. Research from 2025 reveals that 33% of cross-chain investigations span three or more blockchains, while 20% stretch across ten or more networks.
To solve this, wallet addresses must be linked to entity identifiers such as KYC references, employee IDs, or API tokens. Implementing EIP-712 structured signing ensures approvals and consent events are human-readable, while domain separators (e.g., Chain ID) help prevent replay attacks across networks. The table below highlights the key identity fields necessary for audit compliance:
Log Field Category | Required Data Points | Purpose for Audit |
|---|---|---|
Identity & Attribution | Wallet address, API Token ID, User ID, Entity Type | Identifies the actor behind the action |
Temporal Anchors | Timestamp, Block Number, Network finality status | Establishes timing and sequence |
Action Semantics | Transaction hash, Method selector, Amount, Asset symbol | Describes the action and its economic impact |
Risk Context | Risk score (0–100), Policy triggers, Risk level | Assesses the threat level |
Integrity Proofs | Cryptographic signatures, Merkle proofs, Receipt roots | Links off-chain data to on-chain records |
By securely linking identities to actions, the next step is to ensure the data is anchored in time and protected from tampering.
Timestamps and Cryptographic Links
Audit records rely on temporal anchors and cryptographic proofs to guarantee accuracy and integrity. Timestamps and block numbers establish the sequence of events, while hash-linking ensures records remain immutable. For high-volume operations, batching logs into a Merkle tree and anchoring only the root hash on-chain significantly reduces costs compared to storing everything directly on-chain.
Cross-chain operations add complexity. Using Chain ID prevents replay attacks, while bridge proofs from protocols like LayerZero or Axelar confirm that actions on a "spoke" chain were authorized by the "hub" chain. To further strengthen proofs, combining blockchain timestamps with RFC 3161 Time-Stamp Authority (TSA) signatures provides a dual layer of verification for off-chain documents.
With timestamps and cryptographic links in place, the final piece of the puzzle is to detail the transaction's context.
Transaction Context and Action Details
The details of the transaction - such as type, asset, amount, and method - form the economic record. For example, a $50,000 USDC transfer on Base at 3:47 PM on March 4, 2026, to vendor wallet 0x789...def becomes a complete narrative when paired with the transaction hash, method selector, and asset symbol. Without standardized schemas, however, cross-chain data risks becoming siloed.
Modern treasury systems address this by combining on-chain transaction data with off-chain context like invoices, policy clauses, and approval justifications. These off-chain details are stored in secure environments such as AWS S3 or IPFS. A SHA-256 hash or Merkle root is then anchored on-chain, acting as a tamper-proof fingerprint. Any change to the off-chain data will cause a hash mismatch, signaling tampering.
To ensure interoperability and machine-readability, tools like JSON Schema or Protocol Buffers are used to structure metadata, including actor IDs, IP addresses, and risk scores. A complete verification package combines the original off-chain log, the Merkle proof path, and the blockchain transaction ID containing the anchored root, delivering a comprehensive and secure audit trail.
Challenges in Cross-Chain Audit Trails
Creating a reliable audit trail across multiple blockchains comes with a unique set of technical and operational challenges. Each blockchain operates under its own set of rules for finality, data storage, and transaction confirmation. These differences can create friction that, if not addressed, may compromise the integrity of audit processes. This is why a unified approach is so important for effective multi-chain governance. Tackling these obstacles is critical for maintaining the audit standards that platforms like Stablerail aim to uphold.
Interoperability and Data Standardization Issues
One of the biggest hurdles is the variety in confirmation protocols across blockchains. For instance, Ethereum's mainnet typically reaches finality in about 15 minutes as of 2025, while Layer 2 networks like Base or Arbitrum achieve this much faster. This inconsistency can lead to serious problems. Imagine an audit system marking a transaction as "confirmed" on one chain, only for that transaction to be undone during a chain reorganization (reorg).
Reorgs - temporary forks where blocks are replaced - can result in duplicate entries or missing events in audit logs. To address this, systems need to implement idempotency by using a composite key (transaction hash + log index) to ensure the same event isn't recorded twice. Beyond finality and reorgs, bridge transactions add another layer of complexity. These require linking the transaction IDs from both the source and destination chains to maintain a seamless record. Additionally, critical security data, such as oracle prices and governance votes, often resides in proprietary databases or off-chain APIs. This makes it almost impossible to cryptographically verify the state of a data feed at a specific block.
Off-Chain Data Risks
Off-chain data introduces its own set of vulnerabilities. Centralized databases that store invoices, approval justifications, or risk assessments can be manipulated or even deleted by users with elevated privileges. For example, a finance team might anchor a transaction hash on-chain, but if the corresponding off-chain invoice is altered or removed, the audit trail becomes incomplete, posing risks during regulatory reviews or internal audits.
A hybrid approach can mitigate this issue. By hashing off-chain documents using SHA-256 and anchoring the resulting hash on a public blockchain, tamper-evidence is ensured. For operations handling large volumes of data, batching thousands of logs into a Merkle tree and anchoring only the root hash on-chain keeps costs manageable while maintaining data integrity.
Scalability Constraints
Storing raw audit data directly on-chain is prohibitively expensive. On Ethereum, on-chain storage costs range from $10 to $50 per MB, compared to just $0.01 to $0.10 for anchoring a hash of off-chain data. For treasury operations processing hundreds or thousands of transactions daily, these costs quickly become unsustainable.
Performance is another key issue. Retrieving historical audit data directly from blockchain nodes is too slow for real-time needs, often taking 12 to 15 seconds per block. To overcome this, modern systems rely on off-chain indexers like The Graph or Covalent, which process blockchain events into easily searchable databases like PostgreSQL, enabling sub-second query speeds. Additionally, deploying on Layer 2 solutions or utilizing data availability layers like Celestia can further reduce logging costs while maintaining cryptographic security. These solutions are paving the way for more effective cross-chain audit trail implementations.
How Stablerail Ensures Consistent Audit Trails

To tackle the challenges of cross-chain transactions, Stablerail introduces a control plane that bridges custody and signing. This integration creates a unified, tamper-evident record for every stablecoin payment, ensuring a seamless and reliable audit trail across blockchains.
Stablerail operates with a "copilot, not autopilot" philosophy. Funds are stored in MPC-based wallets, meaning Stablerail never holds unilateral signing authority. This ensures that every transaction reflects authorized human decisions rather than automated processes.
Complete Action Recording
Stablerail meticulously tracks every stage of a transaction’s lifecycle. From the initial intent - whether uploaded via CSV, invoice PDF, or API - to the final cryptographic signing, every step is documented. This detailed record reveals what occurred, why it happened, and who approved it.
The system logs critical data, including timestamps, user identities, policy checks, risk verdicts, approvals, and override reasons. If a flagged transaction is overridden, the user must provide a recorded reason, which becomes a permanent part of the audit trail. These detailed records generate what Stablerail calls CFO-grade Proof-of-Control receipts, which outline payment purpose, authorization, and associated risk assessments.
"A CFO-grade record for every payment - ready for auditors, boards, and banking partners." - Stablerail
This comprehensive logging framework forms the foundation for Stablerail’s standardized policy enforcement.
Policy-as-Code Enforcement
Instead of relying on manual approvals through spreadsheets or chat tools, Stablerail enforces governance using programmatic policies. These predefined rules cover scenarios like payment limits, time restrictions, and address verifications. For instance, finance teams can set policies such as "New address payments over $5,000 require CFO approval + verification" or "Only allow USDC on Base/Ethereum."
The Policy Engine ensures strict adherence to these rules, preventing manual workarounds. For example, high-value transfers over $100,000 or payments to new beneficiaries can trigger a 4-hour smart cool-off period, allowing additional verification time and reducing risks like social engineering attacks. Similarly, if a vendor’s payment address changes, the system automatically locks the transaction for escalation. Every action and its justification are logged, ensuring a consistent and reliable audit trail.
This programmatic approach simplifies cross-chain verification and delivers standardized, auditor-ready documentation.
Risk Dossiers and Approval Workflows
Before a payment is finalized, Stablerail generates a Pre-Sign Risk Dossier that delivers a clear verdict: PASS, FLAG, or BLOCK. These dossiers provide detailed explanations in plain language, supported by policy clauses, timestamps, sanctions screening outcomes, and anomaly detection. This eliminates reliance on vague risk scores.
Each payment is simulated before signing to identify potential issues like first-time destinations, address changes, or duplicate transfers. The system also flags activities that might lead to stablecoin issuer freezes, such as transactions involving questionable counterparties. For high-volume operations, Stablerail enables up to 500 transactions to be processed with a single signature, provided agents validate the batch against policy guidelines. These risk dossiers are seamlessly integrated into the audit trail, enhancing compliance and traceability.
"Agents verify the intent. Humans sign the transaction." - Stablerail
Implementation Steps for Cross-Chain Audit Trails
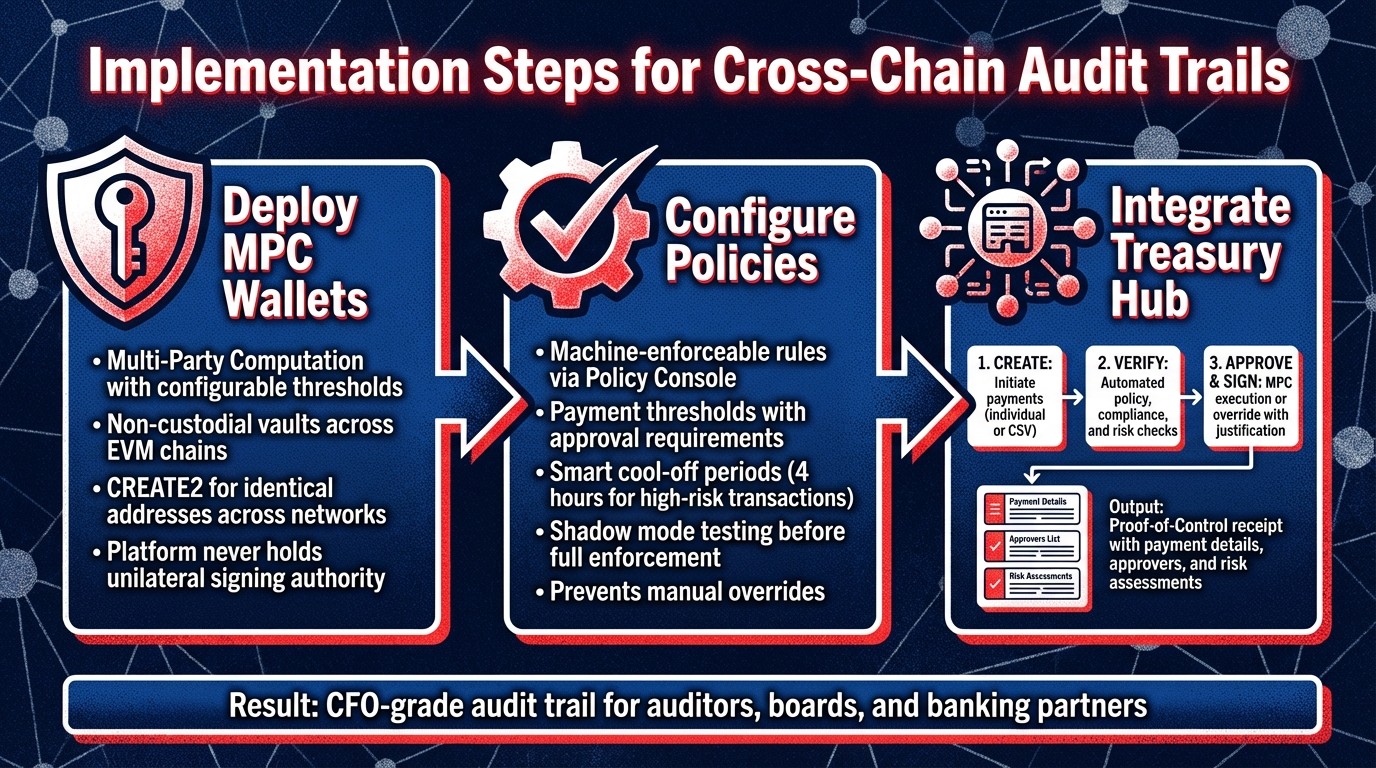
Three-Step Implementation Process for Cross-Chain Audit Trails
Creating consistent audit trails across multiple blockchains requires a carefully planned approach that prioritizes security, governance, and operational efficiency. Stablerail's solution addresses the fragmented workflows many finance teams face, such as juggling wallets, spreadsheets, and Slack approvals.
Deploy MPC Wallets Across Chains
The first step in achieving cross-chain audit consistency is deploying secure, non-custodial vaults using MPC (Multi-Party Computation) with configurable signing thresholds. Stablerail employs MPC-based wallets across major EVM chains, ensuring that funds stay under your control while the platform itself never holds unilateral signing authority. By using deterministic deployment via a factory contract (CREATE2), identical wallet addresses are maintained across networks, simplifying management and reconciliation. As Stablerail emphasizes, the platform protects your treasury without ever directly handling your funds.
Once wallets are securely deployed, the focus shifts to enforcing strong governance policies.
Configure Policies and Governance Rules
After deploying wallets, define clear, programmatic rules to ensure consistent audits and prevent manual overrides. Through the Policy Console, you can set machine-enforceable rules that automatically apply to every transaction. For example, you can establish payment thresholds that require additional approvals. This system eliminates manual workarounds, ensuring that even senior executives cannot bypass controls. For high-risk transactions - like transfers exceeding $100,000 or payments to new beneficiaries - smart cool-off periods (e.g., 4 hours) can be triggered to reduce risks like social engineering attacks.
To fine-tune governance, new policies can be tested in "shadow mode", allowing you to monitor their impact and adjust thresholds before fully enforcing them.
With secure wallets and automated governance in place, the final step is streamlining treasury operations.
Integrate Treasury Hub and Establish Workflow
The Treasury Hub provides a centralized interface for real-time visibility across all self-custodial vaults, eliminating the need to rely on multiple blockchain explorers. This unified view boosts efficiency and ensures that every payment is documented, creating a thorough audit trail. Payments are processed in three stages:
Create: Payments are initiated, either individually or through a CSV upload.
Verify: Automated checks are performed to enforce policy limits, compliance requirements, and risk assessments.
Approve & Sign: Transactions are executed via MPC if they meet all criteria; flagged items require explicit override justifications.
Each transaction generates a Proof-of-Control receipt that includes details such as payment information, justification, approvers, and risk assessments. This comprehensive documentation provides CFO-level evidence for auditors, boards, and banking partners. Additionally, the system supports one-time deposit addresses for invoices, keeping main treasury balances confidential.
Best Practices for Audit Trail Integrity
Maintaining secure and reliable audit trails across blockchains is critical. By combining cryptographic safeguards, standardized data recording, and adherence to regulatory frameworks, you can create records that auditors, boards, and regulators can confidently rely on - without introducing unnecessary operational hurdles.
Modular Data Capture and Analysis
A strong starting point for cross-chain auditing is event sourcing, where every state change is recorded immutably rather than overwriting current states. This method preserves the full history, allowing you to reconstruct any event at any point in time. Take Slash Engineering as an example: they managed over $1 billion in stablecoin transactions by breaking operations into three phases - Intent (payment order), Execute (pending), and Reconcile (posted). This modular design ensures that every side effect can be traced back to its original event, creating a comprehensive execution tree for audits.
To further strengthen audit trail integrity, implement a three-layer architecture:
Event Integrity: Hash each record using SHA-256.
Collection Integrity: Use Merkle trees (RFC 6962-compliant) to confirm batch completeness.
External Verifiability: Anchor Merkle roots to a public blockchain or a Time Stamp Authority.
Additionally, adopting deterministic serialization standards like RFC 8785 ensures that identical event data consistently generates the same hash, regardless of the system or blockchain involved.
Automated Auditing with Smart Contracts
Once events are captured immutably, smart contracts can be used to enforce compliance directly on-chain. These contracts automate audit processes by performing real-time checks. For instance, they can ensure reserves always exceed liabilities and trigger circuit breakers if thresholds are breached. This approach transforms compliance from periodic reviews into a system of continuous, automated oversight.
Policy-as-code systems take this a step further by generating a Risk Dossier for every transaction. This dossier captures the policy version, decision chain, and full chain of custody, including:
Who proposed the payment
What checks were executed
Any raised flags
Who approved or overrode the transaction
By clearly separating the proposal and execution phases, these systems ensure full traceability. They also simplify alignment with regulatory standards by embedding compliance into the infrastructure itself.
Alignment with Audit Standards
Regulatory compliance often requires mapping controls to specific frameworks. For example:
SOX mandates traceability to individual users and a seven-year log retention period.
PCI-DSS v4.0 requires logs to be safeguarded for one year against modification.
SEC Rule 17a-4 demands WORM (Write Once Read Many) storage to prevent data alteration.
Failing to meet these standards can result in severe penalties. In 2023, a major investment bank was fined $350 million when regulators found that privileged database administrators could alter audit logs, highlighting the inadequacy of traditional access controls.
To meet these requirements, use WORM-compliant storage like S3 Object Lock in compliance mode. Implement non-repudiation through digital signatures (e.g., ECDSA P-256) with keys secured in Hardware Security Modules. For external anchoring, tools like OpenTimestamps (for Bitcoin-backed proof of existence) or RFC 3161 Time Stamp Authorities can provide regulatory-grade verification. As the VeritasChain Standards Organization aptly states:
"Verify, Don't Trust".
Conclusion
Managing operations across multiple blockchains without consistent audit trails creates fragmented logs, making forensic analysis nearly impossible. This leaves finance teams exposed during audits. The risks are real: in 2023, a major investment bank faced a $350 million penalty when regulators found that privileged administrators could alter audit logs. For organizations handling stablecoins at scale, failing to prove who approved what and why can lead to internal governance issues and hefty regulatory penalties.
Addressing these challenges requires a robust control system. Stablerail tackles this by operating above custody and before signing, ensuring that every transaction produces a Proof-of-Control receipt. This receipt documents payment details, risk assessments, approvers, and the matched policy - providing CFO-grade evidence for auditors, boards, and banking partners. It also enforces spending limits, whitelists, and approval workflows programmatically across all chains, preventing unauthorized actions often seen in traditional wallet setups.
The benefits go beyond compliance. Automated on-chain processes can cut regulatory reporting overhead by over 70%, while deterministic reconciliation eliminates the chaos of manual spreadsheets. Additionally, identifying tainted counterparties and monitoring real-time risk patterns protect operations from stablecoin issuer freezes - a critical safeguard when OFAC requires blocked virtual currency to be reported within 10 business days. These advancements not only streamline compliance but also strengthen operational resilience.
As ChainScore Labs aptly puts it:
"On-chain state is the audit trail".
Switching from mutable logs to cryptographically enforced records transforms compliance into a process of continuous, automated oversight. This shift is essential for secure, real-time audit trails in multi-chain operations. For finance teams, it's not just about meeting regulatory demands - it's about creating a resilient system that scales with your business.
Stablerail's approach - integrating MPC-secured self-custody, pre-sign risk assessments, and unified action recording - delivers consistent, defensible audit trails without compromising the speed of on-chain settlements. This framework ensures compliance and operational efficiency across multiple chains.
FAQs
What data should every cross-chain audit log include?
Every cross-chain audit log needs to document critical details such as transaction intent, verification checks, policy enforcement actions, approvals, overrides, signatures, timestamps, and any supporting evidence. These elements help create a complete and compliance-ready record of every decision and action taken.
How can you prove off-chain invoices or approvals weren’t altered later?
To make sure off-chain invoices or approvals stay unchanged, you can rely on cryptographic audit trails. These include tools like tamper-evident cryptographic logging and immutable records, which offer clear, verifiable proof of the original data and any changes made to it. This approach helps maintain both transparency and data integrity.
How are chain reorgs and finality rules managed in audits?
Managing chain reorganizations and understanding finality rules means getting a handle on how each blockchain achieves finality and dealing with temporary forks that might occur. To ensure transactions are stable before they're recorded, audit systems should track confidence levels such as "SAFE" or "FINALIZED."
It's also important to include tools for detecting reorgs and to keep thorough audit trails. These should document everything, from policy checks to approvals, helping maintain accuracy and reliability even when the blockchain environment is unpredictable.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


