

An immutable audit trail ensures every action in your treasury operations is permanently recorded, cryptographically signed, and timestamped. This creates a secure, tamper-proof log that meets regulatory standards and boosts accountability. Here's a quick summary of how to implement one:
Set Goals and Compliance Requirements: Identify regulations like SEC Rule 17a-4 or MiCA, map key events, and assemble a team with technical and regulatory expertise.
Build Secure Logging Systems: Use cryptographic hashing (e.g., SHA-256) and tamper-evident storage like WORM systems. Record comprehensive data for all actions, including timestamps, actors, and event details.
Integrate with Treasury Workflows: Log every step, from automated risk checks to manual approvals. Use policy engines to enforce rules and capture override reasons.
Test and Verify: Run end-to-end tests, ensure tamper resistance with hash checks, and cross-check logs with external systems.
Maintain and Monitor: Schedule regular audits, use retention policies for long-term storage, and implement real-time integrity checks.
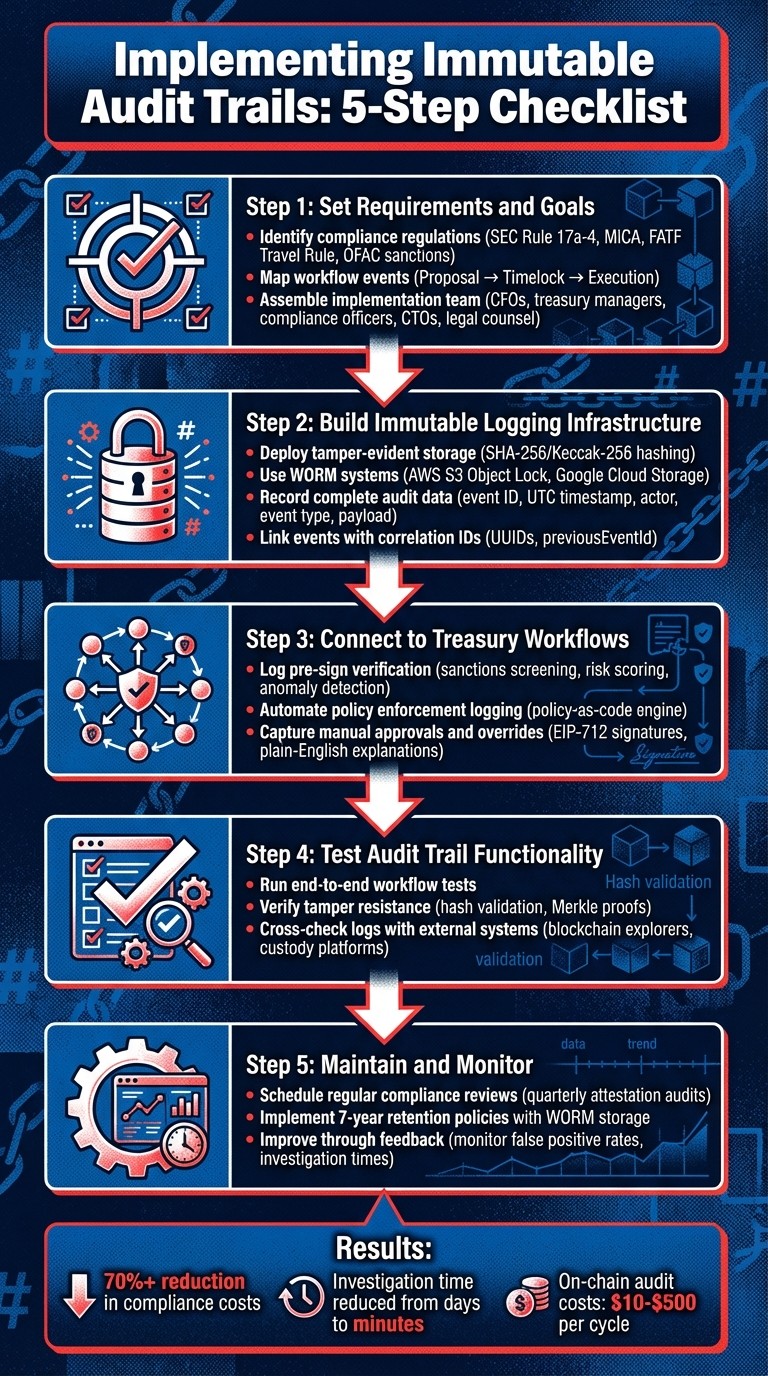
5-Step Process for Implementing Immutable Audit Trails in Treasury Operations
What Does It Mean for Digital Evidence or Logs to Be Immutable?
Step 1: Set Requirements and Goals
The first step in creating an immutable audit trail is all about laying a solid foundation. This involves defining compliance requirements, mapping key operational events, and assembling the right team to ensure everything runs smoothly. Start by setting clear goals and determining the scope of your audit trail. Identify which regulations apply to your treasury operations, outline the workflows that need logging, and gather the relevant stakeholders to oversee the implementation. With these essentials in place, you’ll be ready to move on to building and integrating a reliable logging system.
Identify Compliance and Regulatory Requirements
The first task is to establish your regulatory perimeter - essentially, the specific data points you need to log to comply with the rules in your operating regions. For example, U.S.-based teams must adhere to SEC Rule 17a-4, which mandates storing electronic records in a tamper-proof format. If your treasury handles cross-border payments, the FATF Travel Rule requires tracking and transmitting originator and beneficiary details for every transaction. In the EU, MiCA (Markets in Crypto-Assets) enforces accessibility of audit data for supervisory authorities to ensure compliance with anti-money laundering (AML) rules and transaction thresholds.
Sanctions compliance is another critical area. For example, OFAC sanctions require screening wallet addresses against restricted lists before processing transactions to avoid dealings with sanctioned entities. Similarly, the EU’s DORA (Digital Operational Resilience Act) emphasizes the need for secure and resilient logging systems. Publicly traded companies must also align their on-chain activities with ASC 350 standards, ensuring corporate stablecoin reserves are accurately reflected in their general ledgers.
One challenge lies in balancing GDPR’s "right-to-erasure" with blockchain’s immutable nature. To comply, only pseudonymous identifiers like wallet addresses or transaction hashes should be stored in the permanent log, while personally identifiable information (PII) is kept in separate, deletable databases. As ChainScore Labs explains:
An audit trail is a chronological, immutable log of key events
However, this doesn’t mean all data remains on-chain indefinitely.
Map Workflow Events to Audit Logging
To create an effective audit trail, log the essential details - like who performed an action, what they did, when it happened, and why. Break your treasury workflows into phases such as Proposal (intent creation), Timelock (review period), and Execution (MPC signing). Each phase should have its own auditable record.
Your audit logs should cover both on-chain events (e.g., FundsTransferred or RoleGranted) and off-chain details (like KYC checks, invoice attachments, or manual overrides). For instance, adding a new vendor address to a whitelist should automatically trigger a logging event that flags payments exceeding a certain threshold for review. Administrative actions - such as role assignments, policy updates, or spending limit changes - should also generate corresponding logs to prevent blind spots.
The blockchain analytics market, valued at over $1 billion annually, plays a crucial role in turning raw blockchain data into actionable insights for compliance. Tools like The Graph, which processes over 1 trillion queries monthly, demonstrate the scale of infrastructure needed for this transformation. A single liquidation event on Compound Finance, for example, can produce more than 15 internal contract events, underscoring the importance of standardized schemas (like TypeScript interfaces or Solidity structs) for consistent logging across treasury operations.
Assemble the Implementation Team
Building an audit trail requires a team that bridges technical expertise, regulatory knowledge, and operational understanding. Key players include:
Executive leadership (CFOs, CEOs): Set control standards and provide accountability to boards and banking partners.
Treasury managers and finance operations leads: Oversee payout runs, manage liquidity, and align the audit trail with everyday workflows.
Compliance and risk officers: Define regulatory boundaries and identify potential risks.
On the technical front, CTOs, architects, and security engineers handle the deployment of tamper-proof storage and secure vaults. Legal counsel ensures compliance with jurisdiction-specific regulations, especially for cross-border operations. External stakeholders like auditors and regulators should also be involved to confirm the system can generate audit-ready reports.
To ensure security and accountability, enforce separation of duties and involve senior stakeholders as a final safeguard. Assign a policy architect to translate treasury policies into "Policy-as-Code" and appoint a verification lead to oversee the indexing layer, ensuring on-chain data is translated into clear, human-readable formats for auditors. As Stablerail puts it:
Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money
Step 2: Build Immutable Logging Infrastructure
After defining your requirements and assembling your team, the next step is to establish a tamper-proof system for your audit trails. This involves creating a storage system that prevents alterations, recording all critical actions, and linking events for seamless traceability. The aim is to design a logging infrastructure that aligns with enterprise compliance standards while remaining functional for daily treasury operations. Here's how to achieve this.
Deploy Tamper-Evident Storage
To ensure your audit trails are immutable, cryptographic hashing is key. By using algorithms like SHA-256 or Keccak-256, each log entry gets a unique fingerprint. Even a minor change - like altering a single character - will completely transform the fingerprint. For systems handling large volumes of data, these hashes can be combined into a Merkle tree, with the Merkle root published to a public blockchain like Ethereum or Polygon. This method creates a tamper-evident seal without the high expense of storing raw data directly on-chain.
To block modifications at the application level, override default database methods like save() and delete() to reject any attempts to alter or remove records. Additionally, use WORM (Write Once, Read Many) storage solutions, such as AWS S3 Object Lock or Google Cloud Storage, to prevent retroactive changes. Implementing a hash chain - where each new record includes the hash of the previous one - provides an extra layer of security. This ensures that any tampering with historical logs breaks the chain, making it immediately apparent.
As CommunityPay succinctly puts it:
"The combination of application-layer enforcement (prevention) and content hashing (detection) provides defense in depth".
Record Complete Audit Data
Every audit entry needs to capture all essential details. At a minimum, include the following:
A unique event ID (e.g., UUID or hash)
A precise UTC timestamp with nanosecond precision
Identification of the actor (e.g., wallet address or system ID)
The type of event (e.g.,
PaymentInitiated,ApprovalGranted)A structured payload showing before-and-after values for any changes
For example, if a spending limit is increased from $10,000 to $25,000, the log should document both values, the user who made the change, and the reason provided for the update.
To enhance traceability, include correlation metadata, such as an on-chain transaction hash, to tie off-chain logs to blockchain events. Adding reason codes or narrative explanations for manual overrides or exceptions further strengthens the audit record. This level of detail transforms raw logs into documentation that’s ready for audits.
The blockchain analytics industry, valued at over $1 billion annually, thrives on converting raw on-chain data into understandable formats. For instance, a single decentralized exchange (DEX) swap might generate over five separate contract events that need to be pieced together to fully grasp the logic behind the transaction. Providing this rich context ensures seamless linkage of events.
Link Events with Correlation IDs
Once you’ve recorded comprehensive data, the next step is to connect each event for continuous traceability. Assign unique identifiers, such as UUIDs, to track a transaction’s entire lifecycle - from the initial intent through policy checks, approvals, and final settlement. For example, a "Payment Intent ID" created at the start of a workflow should be included in every subsequent log entry, covering all steps like sanctions screening, policy decisions, CFO approvals, and MPC signature events.
To further strengthen the integrity of your logs, include a previousEventId and sequence number in each record. This creates a linked chain of events, making it easy to detect deletions, gaps, or replay attempts. For governance-related actions, fields like proposalId or approvalMemo can directly tie financial transactions to the internal documents that authorized them.
For instance, in February 2026, CommunityPay implemented an InstitutionalPacket model that uses a previous_packet_hash to link records. Any alteration invalidates the entire sequence, ensuring tamper-proof logging.
Modern treasury platforms, such as Stablerail, incorporate these practices to deliver CFO-grade audit trails tailored for stablecoin treasury operations.
Step 3: Connect Audit Trails to Treasury Workflows
To ensure a complete and defensible record of all treasury activities, integrate your tamper-proof logs into every stage of your workflows. From automated risk checks to manual approvals, each decision point should be captured to create a seamless record from intent to execution. Building on the secure storage and log data established earlier, here’s how to weave these logs into your treasury processes.
Log Pre-Sign Verification Actions
Before initiating any stablecoin payment, implement automated checks - and make sure to log every step. These checks might include sanctions screening, counterparty risk scoring, anomaly detection, and policy limit enforcement. Each verification should generate a log entry detailing the type of check, the outcome (PASS/FLAG/BLOCK), any risk signals detected, and a timestamp.
For example, if a sanctions screening flags a payment to a new vendor address, the log should include the wallet address, the screening service used, the result, and any associated risk indicators. Similarly, if anomaly detection identifies unusual payment behavior - like an amount that exceeds baseline patterns - the log should specify the breached thresholds. Platforms like Stablerail simplify this process by creating a "Risk Dossier" for each transaction. This consolidated record includes all pre-sign verification results, written in plain language, with references to relevant policy clauses and timestamps.
The complexity of auditing transactions is no small matter. The blockchain analytics market, valued at over $1 billion annually, thrives because even a basic decentralized exchange (DEX) swap may involve parsing multiple contract events across different layers. For treasury workflows, the challenge grows when off-chain policy checks and risk assessments are added. Capturing this full context before signing turns complex transaction data into a clear, defensible business record.
Automate Policy Enforcement Logging
Policy enforcement logs should be automated, bringing your operational decision-making in line with your technical infrastructure. A policy-as-code engine can generate audit logs whenever a rule is applied. For instance, when a payment intent is created, the system might check it against rules like "Payments over $5,000 to new addresses require CFO approval" or "Transfers exceeding $10,000 on weekends need additional verification." Each evaluation should produce a log entry that includes the payment intent ID, the policy version, and the decision (Approve, Deny, Hold, Route, or Step-up).
These logs should provide not just the final decision but also the reasoning behind it. For example, if a transaction is denied for exceeding a spending limit, the log should detail the attempted amount, the specific limit, and the policy rule triggered. By automating these entries, manual compliance reviews can be minimized - potentially by up to 99% - while ensuring that auditors and regulators have access to clear, human-readable explanations for every decision.
Capture Manual Approvals and Overrides
For flagged transactions, enforce a lock until a human provides an approval or override. Each manual action should include a plain-English explanation for bypassing the system’s warning. Following a security incident in 2024, Euler Finance introduced an on-chain attestation registry for treasury transactions. This registry mandates a signed, timestamped attestation from authorized personnel for every treasury action.
You can adopt a similar approach using EIP-712 structured data signatures, which create clear, human-readable sign-offs that detail what was approved, by whom, and when. This prevents ambiguous or replayable signatures. For high-risk overrides, add extra layers of authentication, such as hardware key signatures or multi-factor authentication. As Stablerail’s documentation emphasizes:
Overrides require an explicit, recorded reason.
This approach strengthens the chain of custody, making it clear not only who authorized a payment but also why the decision was made, even in the face of system warnings.
Step 4: Test Audit Trail Functionality
Once your audit logs are integrated into treasury workflows, it's time to thoroughly test their functionality. This step ensures that logs are complete, resistant to tampering, and consistent across all systems. Skipping or rushing this process can lead to unpleasant surprises during audits.
Run End-to-End Workflow Tests
Start by simulating full payment workflows - from creating an intent to final approval and signing. Check that every step generates a log entry with the correct timestamp, user ID, decision outcome, and reasoning. Then, review the audit trail to confirm its accuracy.
Take a page from CommunityPay's book. In February 2026, their CI pipeline was designed to test the immutability of audit records. They deliberately attempted to modify or delete these records during testing. The system passed only if it returned errors like PermissionDenied or ValueError. This "test via rejection" approach ensures that database constraints are enforced. When testing your system, include edge cases like flagged transactions requiring manual overrides. Make sure the logs capture override reasons and any additional authentication steps.
Once you've verified completeness, move on to tamper resistance.
Verify Tamper Resistance
To test tamper resistance, try modifying logs both through your application and by directly accessing the database. The system should block these attempts and validate log integrity by recalculating SHA-256 hashes. If your system uses Merkle tree batching, generate Merkle proofs for specific log entries and confirm they match the root hash anchored on-chain.
As Trail of Bits highlights:
The critical discipline is comparing transaction hashes character-by-character across all systems before signing. Any discrepancy indicates compromise.
For highly secure environments, consider using independent verification workstations with different technical stacks. This redundancy ensures that even if one library (like ethers.js) has vulnerabilities, your verification process remains unaffected.
Cross-Check Logs with External Systems
After verifying tamper resistance, ensure your logs align with external sources. The audit trail should reconcile perfectly with blockchain explorers, custody platforms, and accounting systems. Automate this process by setting up reconciliation engines that query on-chain data daily using RPC providers like Alchemy or Infura. Then, compare it to your internal database. To avoid unnecessary alerts, set tolerance thresholds for unconfirmed transactions.
For platforms like Stablerail that produce Risk Dossiers and Proof-of-Control receipts, double-check that transaction IDs, amounts, and timestamps match on-chain execution data. If you're using indexing services like The Graph, periodically validate the completeness of indexed data against raw blockchain data to catch any silent failures during abstraction. Offering a verification portal where auditors can input a transaction ID to receive a Merkle proof, along with the corresponding blockchain transaction ID, adds an extra layer of trust.
Step 5: Maintain and Monitor Audit Systems
Creating an audit trail is just the beginning. To ensure it stays reliable, accessible, and compliant, regular maintenance and monitoring are essential.
Schedule Regular Compliance Reviews
Annual audits are becoming a thing of the past. The shift toward continuous assurance means real-time verification of your audit trail against blockchain activity is now the standard. Plan quarterly third-party attestation audits to confirm that your indexing logic accurately interprets blockchain data. Additionally, set up automated integrity checks to sample historical audit entries and verify their cryptographic hashes against blockchain records.
If you're using tools like Stablerail, which provide Risk Dossiers and Proof-of-Control receipts, consider creating a verification portal. This allows auditors to input transaction IDs and quickly confirm that your off-chain records align with on-chain transactions. This level of transparency can significantly cut investigation times from days to minutes.
"The future of audit trails is not more data, but a standardized semantic layer that translates on-chain activity into regulator-ready narratives." - ChainScore Labs
Regulators also require a clear view of how raw blockchain data flows through your indexing system into compliance reports. Documenting this entire data lineage is critical.
These reviews work hand-in-hand with robust retention and backup strategies to ensure data security and compliance.
Implement Retention and Backup Policies
Financial audit data often comes with a seven-year retention requirement. To meet these regulations, use Write Once, Read Many (WORM) storage solutions.
Platform | WORM Primitive | Legal Hold Support | Key Feature |
|---|---|---|---|
AWS S3 | Object Lock | Yes | Compliance mode cannot be overridden by any user |
Google Cloud | Bucket Lock | Yes | Locking a policy is irreversible |
Immutable Storage | Yes | Supports container-level and version-level WORM |
Create a retention matrix that links record types to their required storage durations under regulations like MiCA or DORA. For added security, follow the "three independent proofs" rule: store a signed digest in a primary immutable store, keep an off-account backup in a separate cloud tenant, and anchor a Merkle root hash to a public blockchain such as Ethereum or Polygon.
"Practical compliance is not satisfied by access controls alone - you must show the evidence has an immutable lineage and that lineage can be independently verified outside the system." - Kyra, Beefed.ai
Protect the private keys used for signing audit digests by storing them in a Hardware Security Module (HSM) or a managed service like AWS KMS. Automate periodic recalculation of ledger hashes and compare them to anchored on-chain roots. Any discrepancies should trigger alerts in your SIEM system for immediate resolution.
Improve Through Feedback and Audits
Once your audit system is running smoothly, take the opportunity to refine it further by incorporating feedback and conducting regular audits.
Use insights from internal reviews and external audits to fine-tune your logging policies. Monitor key metrics like false positive rates, investigation times, and workflow efficiency to identify bottlenecks in your stablecoin treasury operations by following a stablecoin compliance checklist. If manual reconciliation of logs is taking too long, it's time to automate.
One effective strategy is implementing policy-as-code replayability. This allows you to rerun historical decisions with the same inputs, ensuring your system behaves consistently. After a security incident, Euler Finance adopted an on-chain attestation registry in 2024, requiring every treasury action to include a signed, timestamped attestation. This created a complete on-chain record of governance decisions and execution, offering full transparency for their DAO.
You might also consider launching a bug bounty program focused on your audit and treasury systems. External researchers can help uncover vulnerabilities you may overlook internally. Finally, prepare a standard verification package for auditors. This should include the original log entry, its Merkle proof path, and the corresponding blockchain transaction ID. Providing such a package streamlines external audits and helps build trust with regulators increasingly demanding real-time access to compliance data.
Conclusion
Using immutable audit trails doesn’t just check the compliance box - it transforms how payment decisions are verified and improved. By following the five steps in this checklist - setting clear objectives, building reliable logging systems, integrating with treasury workflows, thorough testing, and ongoing maintenance - you can establish a cryptographically verifiable log. This shifts the proof burden from internal systems to publicly verifiable ledgers, making audits far more transparent and reliable.
The benefits speak for themselves. Organizations that implement automated on-chain compliance have slashed compliance costs by over 70%. Additionally, structured data standards can reduce the time it takes to investigate anomalies from days to mere minutes. On-chain audits also replace expensive quarterly reports with real-time verification processes that cost as little as $10–$500 per cycle.
Beyond cost and time savings, these systems deliver unmatched non-repudiation and cryptographic assurance. Take Euler Finance as an example: when they introduced an on-chain attestation registry in 2024, requiring every treasury transaction to include a signed, timestamped attestation, they achieved a level of transparency for their DAO that traditional audit methods simply can’t match.
"On-chain payments demand an architecture where compliance is not a separate lane. It must become part of the execution path." - Stablecoin Insider
This evolution toward compliance-as-infrastructure changes the game. Audit trails are no longer just static records; they actively participate in the payment approval process. Platforms like Stablerail use these systems to produce Risk Dossiers and Proof-of-Control receipts, which not only satisfy auditors and regulators but also support rapid on-chain settlements. As regulatory standards like MiCA and the FATF Travel Rule continue to evolve, having a tamper-evident, robust audit system ensures your organization is always ready to demonstrate compliance in real-time, rather than scrambling during audits. These advancements make immutable audit trails a cornerstone of secure operations and ongoing compliance in stablecoin treasury management.
FAQs
What data should be immutable vs deletable for GDPR?
Data that should remain unchangeable includes transaction records, user activity logs, and document version histories. These serve as a permanent record, often required for regulatory compliance and accountability. On the other hand, data that can be deleted includes personal identifiers no longer necessary for operational or legal reasons. Removing such data helps protect privacy and aligns with data minimization practices.
How can we ensure logs can’t be altered later?
CommunityPay secures log integrity directly at the application layer by customizing the save() and delete() methods on its models. This setup ensures that once a log is created, it cannot be altered. Any attempt to modify an existing immutable record is automatically blocked, maintaining the original data's accuracy and reliability.
What should we log for approvals and overrides?
To maintain a thorough audit trail, document every approval and override action in detail. This should include the decision-maker's identity, the exact timestamp, the reason for the action, and any relevant evidence or policy rationale. Such meticulous logging not only supports compliance but also strengthens the ability to justify decisions when needed.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


