
Behavioral anomaly logs transform blockchain audits by adding deeper insights into why anomalies occur, not just what happens. These logs combine on-chain and off-chain data, enabling auditors to detect unusual activity patterns, such as transaction spikes, irregular timings, or policy violations, that might signal fraud or compliance risks. They also strengthen audit trails with cryptographic security, making data tamper-resistant and verifiable.
Key Takeaways:
What they track: Transaction irregularities, gas fee anomalies, multi-chain movements, and access patterns.
Data sources: On-chain records (e.g., gas fees, events) + off-chain logs (e.g., KYC, API requests).
Benefits: Faster fraud detection, reduced analysis time, and better regulatory compliance.
Real-world impact: Companies like Coinbase and Bybit have used anomaly logs to mitigate risks and prevent losses.
By integrating behavioral anomaly logs, audits shift from static reviews to real-time monitoring, improving fraud detection and compliance while reducing manual effort.
How BlockSec Phalcon Monitors Oracle Anomalies: Insights from the Rho Markets Incident
What Goes Into Behavioral Anomaly Logs
Behavioral anomaly logs combine on-chain data with off-chain records to provide a complete picture of actions, intent, and authorization. This integration ensures better tracking and understanding of unusual activities.
Data Sources for Anomaly Detection
The backbone of any behavioral anomaly log is on-chain transaction data. Key elements like Gas Price, Gas Limit, and Nonce provide insights into network conditions and transaction sequencing. In Ethereum Virtual Machine (EVM) environments, smart contracts generate events that document granular actions - such as token approvals, liquidations, and governance votes - creating a reliable record for off-chain systems.
But on-chain data alone isn't enough. Off-chain activity logs play a critical role in creating a full audit trail. These include user authentication logs, API request histories, order events (like creation or cancellation), and custody movements. Adding identity and compliance metadata, such as KYC/AML information, links pseudonymous blockchain addresses to real-world entities, making risk detection more precise. This connection enhances audit trails by tying blockchain activity to verified records. Additionally, monitoring oracle updates, price discrepancies, and liquidity pool imbalances can help identify manipulation or instability.
Types of Anomalies to Track
Once you've identified the right data sources, focus on anomalies that signal actual risks. For example, transaction spikes - like sudden large transfers - could indicate suspicious activity. Similarly, unusual timing, such as significant withdrawals late at night or on weekends, might point to compromised accounts or insider threats.
Policy violations are another red flag. These include transactions that bypass approval processes, exceed spending limits, or send funds to non-whitelisted addresses. Multi-chain movements and chain hopping can also obscure fund origins, a tactic highlighted by the U.S. Treasury Department during its investigation of Tornado Cash. This platform allegedly facilitated the laundering of over $7 billion in virtual currency between 2019 and 2022. Monitoring changes to admin keys, such as unauthorized governance contract updates, is equally vital to prevent control shifts that could lead to fund losses.
How Blockchain Ensures Log Integrity
Blockchain technology plays a key role in securing anomaly logs. Each entry is protected by cryptographic hashes, which detect tampering through hash mismatches. Cryptographic sealing ensures that every new block of log data is linked to the previous one, forming a chronological chain. Altering one entry would require rehashing all subsequent blocks, an almost impossible task.
"Once a piece of information is written into the log, it cannot be altered or deleted by anyone - not even a system administrator." - Jason Berwanger, HubiFi
Additionally, decentralized ledger systems distribute logs across multiple nodes instead of relying on a single server, removing any single point of failure. Consensus mechanisms ensure that all participants validate log entries before they are finalized. To handle the large volumes of data generated, many systems use hybrid storage models. For example, the actual log files might be stored on decentralized platforms like IPFS, while only their cryptographic hashes are recorded on the blockchain. This approach creates a lightweight yet verifiable audit trail.
A real-world example of this technology in action comes from the cryptocurrency exchange Bybit. They used blockchain wallet auditing to uncover eight unauthorized transactions made by an employee, Ho Kai Xin, to four unapproved crypto addresses. This immutable evidence led to a successful prosecution in Singapore's High Court. Such measures demonstrate how blockchain-based systems can deliver reliable and actionable anomaly detection for audits.
How to Design Anomaly Logs for Audits
Creating anomaly logs that auditors can rely on requires careful planning to ensure they are complete, secure, and built for long-term use. A well-thought-out log doesn’t just capture events - it anticipates what auditors will need, reinforcing the audit-ready framework discussed earlier. This builds on earlier measures for log integrity by focusing on the data and structure necessary for effective audits.
Required Fields for Each Log Entry
Each log entry should provide enough detail to fully reconstruct the context of an anomaly. Start by including identity fields - such as wallet addresses, contract IDs, exchange IDs, and anonymized KYC/AML references - to pinpoint the event's initiator.
Precise timestamps and block numbers are critical for establishing when the event occurred and its sequence. Additionally, action semantics should clearly describe the event. This includes transaction types, method or function selectors, parameters, and amounts in both the native currency (e.g., ETH) and USD. This dual recording helps auditors assess the economic impact, even when token values fluctuate.
Including system and risk context adds another layer of clarity. For example, details like node versions, client types, and specific triggers from risk engines (e.g., spending limit breaches or policy violations) provide insight into the conditions surrounding the event. If a transaction surpasses a $5,000 threshold without CFO approval, the log should reference the violated policy. Cryptographic proofs, such as digital signatures and Merkle proofs, are also essential, linking each log entry to its blockchain record.
Once all essential data is captured, the next step is to organize these entries in a way that simplifies audits.
Organizing Logs for Easy Auditing
The way logs are structured is just as important as the details they capture. Start by categorizing entries based on the actor and target. This helps clarify both responsibility and impact. For example, you can distinguish between actions initiated by a user, an API token, or the system, and identify the affected entities. This structure makes it easier to query specific scenarios, such as finding all API-initiated transactions targeting high-value wallets.
To simplify investigations, use techniques like address clustering and entity linking to group multiple addresses controlled by the same actor. This reduces anonymity and makes patterns clearer. Additionally, ensure that off-chain logs - like API access records or order data - are connected to on-chain transaction hashes. Standardizing smart contract event schemas for key actions (e.g., transfers, approvals, liquidations) further ensures consistency. To prevent tampering, consider write-once storage or anchoring log hashes periodically to a public blockchain, so any unauthorized changes are immediately noticeable.
The final challenge is securing and retaining these structured logs.
Protecting and Retaining Log Data
Maintaining log integrity requires strong cryptographic measures and well-defined retention policies. Use SHA-256 hashing to create unique digital fingerprints for each log entry or batch of entries. Recording these hashes on a blockchain ensures their immutability.
Store critical cryptographic hashes on-chain, while keeping detailed logs in decentralized off-chain storage for efficient verification. Automating the reconciliation of local logs with blockchain-anchored hashes makes it easier to detect tampering.
"Audit logs are only useful if they are regularly monitored and reviewed. Organizations must have a system in place to collect, store, and review audit logs on a regular basis in order to maximize the value and effectiveness of the audit logs." - Kiteworks
Protecting log confidentiality is equally important. Implement Role-Based Access Control (RBAC) to restrict access to authorized personnel, and use smart contracts to automate access control and validation. These measures not only secure sensitive data but also allow auditors to quickly identify and respond to anomalies.
Retention policies should align with industry standards. For example, HIPAA and GDPR often mandate retaining logs for at least one year, though some organizations extend this to five or seven years for long-term forensic investigations.
A real-world example highlights the importance of robust audit logs. In May 2025, Coinbase identified unauthorized data access by overseas contractors months before an extortion attempt. Their security systems flagged unusual access patterns, and audit logs played a key role in terminating the individuals involved and mitigating a $20 million ransom threat.
Step-by-Step: Using Anomaly Logs in Blockchain Audits
Once your anomaly logs are properly designed and secured, the next step is to use them effectively during an audit. This process converts raw anomaly data into actionable insights, helping auditors evaluate compliance and security measures.
Step 1: Define Audit Goals and Risk Scenarios
Start by setting clear objectives for your audit. These goals should align with specific security or compliance requirements, such as detecting unauthorized transactions, verifying the integrity of smart contract executions, or meeting standards like GDPR and HIPAA. Connect these objectives to specific risk scenarios that your anomaly logs are designed to capture.
Focus on four primary risk categories:
Insider threats: Privileged users attempting to delete or manipulate logs.
Unauthorized access: Irregular IAM (Identity and Access Management) patterns or privilege changes.
Transaction irregularities: Unusual activity like large withdrawals or frequent transfers that deviate from established norms.
Initialization risks: Vulnerabilities during the system's "root" user creation phase, where attackers might compromise the first identity.
"The internal audit design itself can be shifted from a retroactive, point-in-time examination to an ongoing, real-time monitoring process that is informed by previous transactions." - Deloitte
Before rolling out the audit fully, pilot the process to ensure your anomaly logs align with business workflows. Categorize risks into three types: inherent risks (those intrinsic to operations), control risks (weaknesses in internal protocols), and detection risks (failures in audit procedures to catch issues). With these goals and scenarios mapped out, move on to establishing baselines and detection rules.
Step 2: Establish Baselines and Detection Rules
To identify anomalies, you first need to define what "normal" activity looks like. Use historical transaction data to create baselines, such as typical transaction volumes, average amounts, common counterparties, and standard operating hours.
Set specific threshold rules, like daily spending caps or maximum withdrawal limits. Implement logic-based safeguards, such as allow lists for approved addresses and cooldown periods after sensitive actions like key rotations. Add risk-based screening to flag transactions involving sanctioned entities or known illicit addresses.
Real-time risk engines can analyze transaction patterns, counterparty risks, and unusual behaviors with a latency of 60-80 milliseconds.
"Algorithms establish baseline transaction behaviors then flag deviations, such as unusually high or frequent small payments." - Nansen
For effective tracking, use techniques like deriving a window key from ledger timestamps (e.g., day = timestamp / 86,400) to reset totals when the time window changes. When employing allow lists, ensure both root invocations and nested subinvocations are inspected to prevent malicious actors from bypassing restrictions.
Step 3: Log Pre-Transaction Activity
Logging pre-transaction activity creates a clear, audit-ready trail. Record every step of the anomaly checks, including sanctions screening, policy enforcement, and behavioral analysis.
Document all human actions in the approval process: who reviewed the transaction, what risks were flagged, whether policies were overridden, and why. This builds a complete chain of custody from intent to execution. For high-frequency activities, consider using short-lived session keys with limited functionality and amounts to reduce risk.
Tools like Stablerail automate pre-transaction logging by generating a Risk Dossier. This dossier includes a verdict (PASS/FLAG/BLOCK) and plain-English explanations tied to policy clauses and timestamps, ensuring every decision is documented before funds are moved. This pre-transaction layer operates above custody and signing, creating a robust audit trail before any transfer occurs.
Step 4: Organize Evidence for Auditors
Auditors need evidence presented in two ways: high-level summaries and detailed drill-downs. Create unified audit trails that combine on-chain data (blocks, transactions, and smart contract events) with off-chain records (API access logs, exchange actions, custody movements) for a complete timeline.
Structure logs by Actor Type (e.g., User, API Token, or System) and Target Type (the impacted entity) to help auditors quickly identify the source of anomalies. Prepare reconciliation reports comparing calculated balances (from transaction history) with recorded balances from on-chain explorers to pinpoint discrepancies.
"Audit trails are the connective tissue of trust in crypto markets and Web3." - Cube Exchange
Clearly document your methodology, including data sources (e.g., explorers, ledgers), the time period covered, and whether reconciliation was manual or automated. Use visualization tools to map complex transaction paths, making it easier for auditors to understand multi-hop transfers or identify suspicious addresses. Reports should include final reconciled balances, adjustments made, and explanations for unresolved differences.
Step 5: Refine Logs Based on Audit Feedback
Post-audit reviews are an opportunity to improve. Analyze findings to identify gaps in your baselines, detection rules, or log completeness. If auditors flag transaction types that weren’t captured, update your log schema. If anomalies went unnoticed, adjust thresholds or refine behavioral baselines.
Stay ahead of emerging threats by updating risk categorizations. For instance, the NYDFS 2025 Guidance advises all New York Banking Organizations to use blockchain analytics for customer due diligence and transaction monitoring, extending these requirements to traditional banks.
Set up automated alerts for deviations in token supply or collateral ratios. Implement continuous monitoring systems that pause contracts or require extra approvals when high-risk activities are flagged. Shifting from periodic audits to continuous monitoring fosters a cycle of trust, bolstering both security and compliance over time.
Measuring How Anomaly Logs Improve Audits
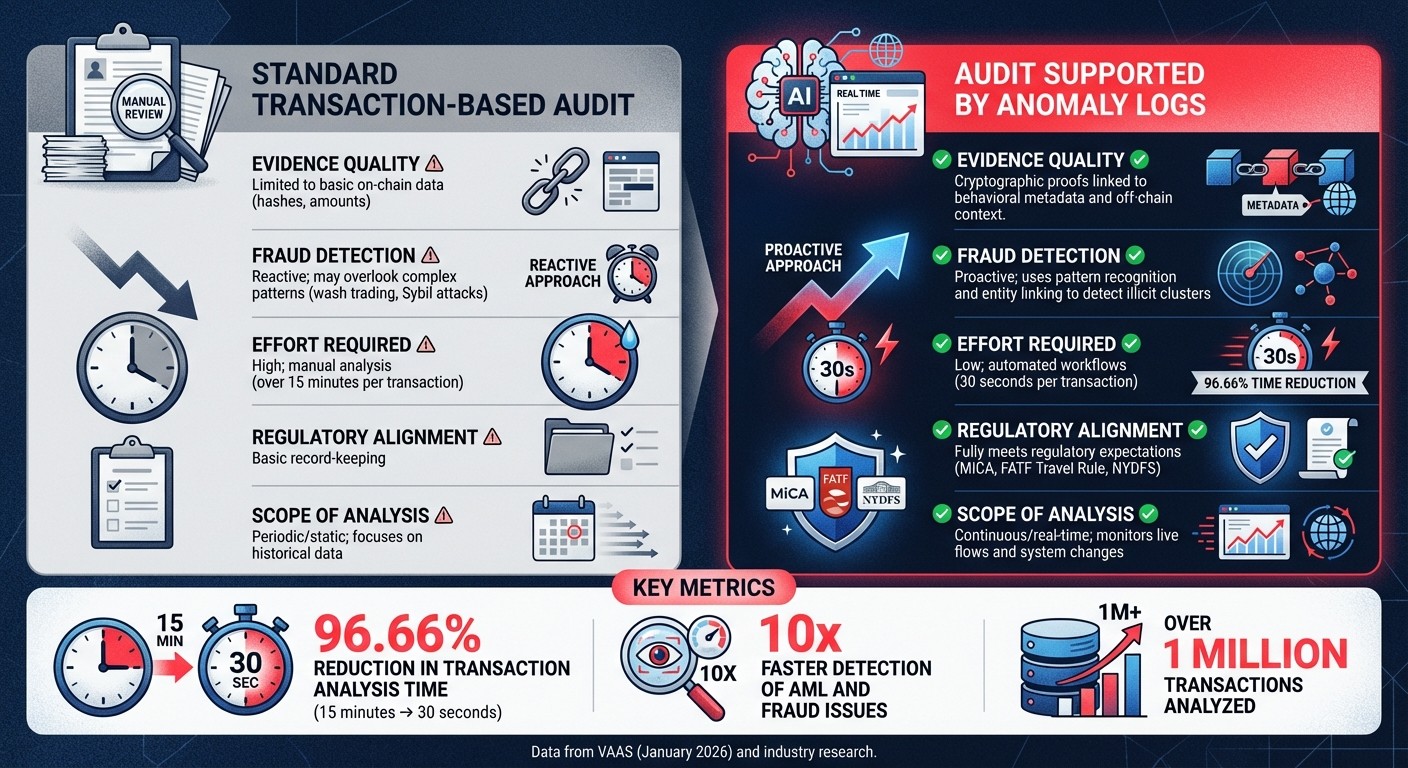
Traditional vs Anomaly Log-Enhanced Blockchain Audits Comparison
Once anomaly logs are in place, it’s important to evaluate their impact. Tracking specific metrics allows you to gauge improvements in areas like efficiency, security, and compliance. This data-driven approach transforms behavioral logging into measurable business value, aligning neatly with the proactive audit strategies discussed earlier.
Metrics to Track Log Performance
One key area to measure is analysis efficiency. For example, in January 2026, VAAS, under CEO Gustavo Tremel, reported a dramatic 96.66% reduction in transaction analysis time after adopting AI-powered anomaly detection. Their system cut the time needed to analyze transactions from 15 minutes to just 30 seconds across over 1 million transactions. These time savings not only reduce costs but also speed up the audit process significantly.
Another important metric is fraud detection velocity, which measures how quickly anomalies are identified. Some organizations have reported up to 10x faster detection of anti-money laundering (AML) and fraud issues with automated anomaly detection systems. Additionally, tracking reconciliation accuracy - by comparing discrepancies between on-chain ledger data and internal records - can uncover critical risks. For instance, in June 2024, Bybit used reconciliation metrics to identify significant internal vulnerabilities.
Other useful metrics include:
Compliance coverage: The percentage of transactions screened against sanctions lists.
False positive rate: Helps minimize unnecessary alerts and reduce alert fatigue.
Recovery value: The total assets recovered as a result of flagged anomalies.
Finance teams using platforms like Stablerail can also monitor the number of flagged transactions requiring CFO overrides, which provides insight into operational efficiency and potential bottlenecks.
Meeting Regulatory Requirements
Beyond performance metrics, anomaly logs play a critical role in meeting regulatory standards. Behavioral anomaly logs create a verifiable record of activities, which is crucial for compliance with regulations like SOX and AML. These logs enable real-time monitoring of suspicious activities, supporting the continuous oversight required by frameworks such as those from the NYDFS and MiCA.
For stablecoin issuers and DeFi protocols, anomaly logs can track essential parameters like minting and redemption flows, oracle health, and collateral integrity. This aligns with requirements such as the FATF Travel Rule. By combining automated sanctions screening with behavioral pattern detection, anomaly logs strengthen risk management processes. Features like Stablerail's Risk Dossier, which provides plain-English explanations tied to policy clauses and timestamps, further enhance compliance efforts, making it easier to justify decisions to auditors, boards, and regulators.
Comparing Audit Methods: With and Without Anomaly Logs
The contrast between traditional audits and those enhanced by anomaly logs is striking. Conventional audits often rely on manual sampling and static snapshots of ledger data, which can take over 15 minutes per transaction. Anomaly logs, on the other hand, enable continuous monitoring, capturing complex patterns that manual methods might miss.
This comparison highlights how anomaly logs shift auditing from a reactive, time-intensive process to a proactive, streamlined approach. Continuous monitoring not only enhances security but also builds trust with auditors, regulators, and stakeholders. By tracking these metrics and ensuring regulatory alignment, organizations can clearly demonstrate the value of behavioral anomaly logs in modern auditing practices.
Conclusion
Behavioral anomaly logs bring together on-chain and off-chain data - like API access, exchange orders, and KYC checks - to deliver a level of traceability that traditional audits simply can't match. By providing a comprehensive view of asset movement, from its origin to settlement, these logs give auditors and regulators the hard evidence they need to confirm compliance and uncover fraud.
This improved traceability comes with practical advantages. AI-powered anomaly detection boosts efficiency while enabling real-time risk management. As Blockaid puts it:
"Audits aren't enough. Real-time security builds resilience and trust".
With continuous monitoring, teams can identify and address complex threats - such as peel chains, wash trading, or interactions with sanctioned addresses - before they spiral out of control.
For compliance teams, behavioral logs offer the structured proof required by regulatory frameworks like MiCA, the FATF Travel Rule, and NYDFS guidance. The cryptographic chaining and tamper-evident design of these logs ensure that any unauthorized changes are immediately flagged, preserving the integrity that regulators and investors expect. This is becoming increasingly crucial as traditional banks delve into tokenized assets and stablecoin services, where blockchain analytics are quickly becoming a key part of due diligence.
Unlike static, one-time audits, anomaly logs create a dynamic feedback loop. They accelerate forensic investigations, simplify smart contract debugging, and reduce downtime that impacts users.
FAQs
How do anomaly logs help detect fraud during blockchain audits?
Anomaly logs serve as a crucial tool for monitoring deviations from normal transaction patterns, such as unexpected payment amounts, unusual timing, or irregular payout behaviors. These logs provide a detailed, time-stamped record that helps uncover suspicious activities, like rapid, large transfers or dealings with flagged accounts.
By integrating behavioral anomaly detection into pre-sign verification processes, platforms like Stablerail can automatically flag or block transactions deemed high-risk before they go through. This approach minimizes the need for manual reviews, accelerates investigations, and equips auditors with clear, unchangeable evidence of compliance and fraud prevention efforts. These logs ensure that every payment decision is grounded in a strong, data-driven system for detecting fraud.
What data sources are used in behavioral anomaly logs for blockchain audits?
Behavioral anomaly logs gather data from several critical sources to paint a detailed picture of each payment decision. Here's a closer look at these sources:
Transaction metadata: This includes details like the transaction amount, timestamp, source and destination addresses, and the blockchain used. These elements help identify irregular patterns or sudden spikes in activity.
System activity logs: These logs capture low-level events, such as user actions and program executions, making it easier to distinguish between normal operations and potentially suspicious behavior.
Policy enforcement records: By logging pre-sign checks, limit flags, and human approvals, these records ensure governance rules are applied consistently and remain auditable.
External risk feeds: Information such as sanctions lists, counterparty risk scores, and exposure monitoring injects real-world compliance and risk indicators into the analysis.
By integrating these data points, anomaly logs create a searchable record that not only highlights deviations but also supports investigations and ensures alignment with regulatory requirements.
How does blockchain maintain the accuracy and security of anomaly logs?
Blockchain technology strengthens the reliability and security of anomaly logs by storing every entry in an unchangeable, timestamped ledger. Each log is protected using cryptographic hashes and verified through a consensus process, which makes unauthorized alterations nearly impossible to execute without being noticed.
This setup guarantees that any tampering efforts are both visible and traceable, creating a dependable system for audits and regulatory compliance.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


