

Threshold cryptography redefines how enterprises manage digital assets by splitting private keys into multiple parts, ensuring the complete key never exists at any point. This approach eliminates single points of failure, making it a safer alternative to traditional single-key or MultiSig wallets. Here's why it matters:
Improved Security: Private keys are divided into "shards", requiring a minimum number of participants (e.g., 3 of 5) to authorize transactions, reducing risks of theft or misuse.
Regulatory Compliance: Meets global standards like the EU’s MiCA by ensuring no single entity controls funds.
Efficiency: Transactions remain small, keeping gas fees low, while off-chain processes maintain privacy.
Governance Integration: Combines cryptographic protection with automated policies (e.g., spending limits, approvals), preventing unauthorized actions.
Threshold cryptography is particularly useful for managing stablecoin treasuries, offering secure, scalable, and efficient solutions for cross-chain operations. Platforms like Stablerail enhance this system with pre-transaction checks and policy enforcement, ensuring every transaction aligns with business rules. This dual-layered security model is quickly becoming the standard for enterprise wallets.
Blockdaemon Builder Vault - Enterprise Key Management
How Threshold Cryptography and MPC Wallets Work
How Threshold Cryptography Works: From Key Splitting to Secure Transaction Signing
Threshold Cryptography and Secret Sharing Basics
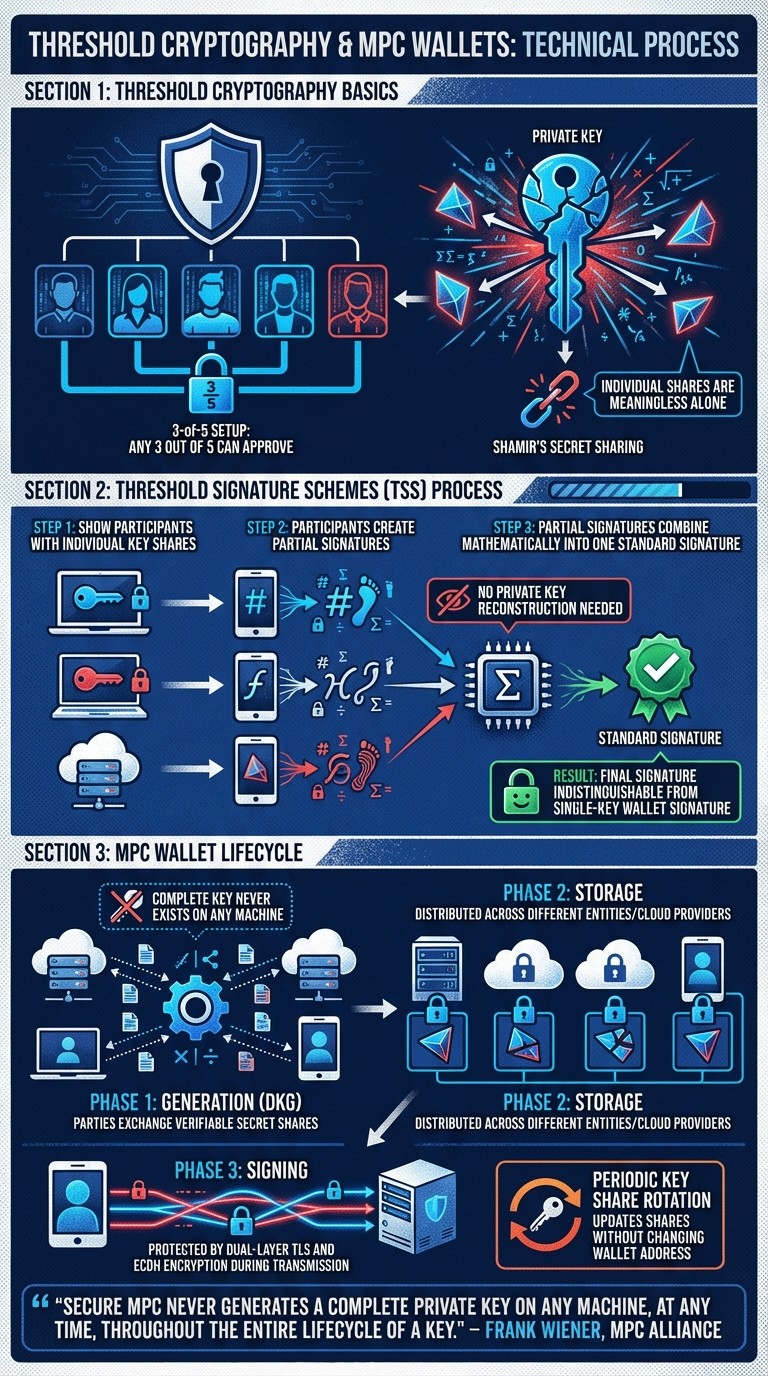
Threshold cryptography operates on a simple yet powerful principle: instead of requiring unanimous approval for a transaction, only a minimum number of participants is needed. This concept, known as t-of-n threshold logic (where t represents the minimum required participants and n is the total number of participants), is a cornerstone for securing enterprise wallets. For example, in a 3-of-5 setup, any three out of five key holders can approve a transaction, providing resilience against both key loss and compromise.
This system is often built on Shamir's Secret Sharing, a method that splits a private key into multiple shares. Individually, these shares are meaningless, but when the required threshold is met, they can reconstruct the original key. Modern wallets take this further with Threshold Signature Schemes (TSS), which enable secure signing without ever reconstructing the full private key. These principles form the backbone of advanced cryptographic implementations like TSS, which we’ll explore in the next section.
Threshold Signature Schemes (TSS) in Practice
Threshold Signature Schemes take secret sharing to the next level. Instead of reassembling the private key to sign a transaction, TSS allows participants to create partial signatures using their individual shares. These partial signatures are then combined mathematically into a single, standard signature.
The signing process involves coordinated rounds where participants exchange cryptographic commitments, generate partial signatures, and merge them into a final signature. The result is indistinguishable from a signature created by a traditional single-key wallet. This allows TSS wallets to seamlessly interact with any blockchain, eliminating the need for smart contracts or specialized on-chain support. Building on this, Enterprises can set up MPC wallets to enhance security by protecting the entire lifecycle of a key.
Secure Multiparty Computation (MPC) in Wallets
MPC wallets expand the principles of threshold cryptography to cover every stage of a key’s lifecycle - generation, storage, and signing. One of their standout features is that the complete private key never exists on any single machine at any point. This approach has become the backbone of secure governance for stablecoin treasuries, providing the level of protection enterprises demand. During Distributed Key Generation (DKG), parties exchange verifiable secret shares, ensuring no single machine ever holds the full key.
"Secure MPC never generates a complete private key on any machine, at any time, throughout the entire lifecycle of a key." – Frank Wiener, MPC Alliance
Another key advantage of MPC is periodic key share rotation. Enterprises can update the mathematical values of key shares regularly without changing the associated public address or private key. This ensures that even if a share were compromised, it would become useless after the next rotation.
To further enhance security, MPC wallets employ AES-256 encryption to protect key shares at rest, along with dual-layer TLS and ECDH encryption to safeguard key material during transmission.
Building Threshold-Based Wallets for Stablecoin Treasuries
Choosing Threshold Parameters for Security and Availability
When setting up a threshold-based wallet, choosing the right t-of-n configuration is critical for balancing security and accessibility. Here, t represents the number of participants needed to authorize a transaction, while n is the total number of key share holders. For example, a 2-of-2 setup might work for personal use, while a 3-of-5 configuration is better suited for treasury operations.
Raising t increases security but also heightens the risk of operational delays if key holders are unavailable. For instance, a 4-of-5 configuration could stall transactions if two key holders are unreachable. On the other hand, a 2-of-3 setup allows for quicker approvals but sacrifices some security.
To avoid single points of failure, enterprises should spread key shares across different entities and cloud providers. A cautionary tale comes from the May 2023 Multichain incident, where CEO Zhaojun’s detention left all MPC node servers - centralized under his personal cloud account - inaccessible. This mismanagement led to an unauthorized transfer of over $130 million in assets on July 7, 2023.
Another essential practice is regularly rotating key shares. This process updates the shares mathematically without altering the wallet address, ensuring that compromised shares are rendered useless.
Once the threshold parameters are securely in place, the next step is to enforce governance rules through policy-as-code.
Implementing Policy-Driven Threshold Signing
Threshold cryptography becomes much more effective when combined with policy-as-code governance. Instead of relying on manual approvals through emails or messaging apps, businesses can enforce spending limits, role-based access controls, and destination whitelists directly at the infrastructure level - before any signing takes place.
"Security policies should exist in code, not spreadsheets." – Dynamic
This approach ensures that every transaction complies with strict, automated rules. Policy engines validate each transaction in real time. If a payment exceeds a spending cap, targets an unauthorized address, or violates velocity limits, the signing process is immediately halted. This system prevents a single compromised device or insider threat from draining the treasury, as transactions require both quorum and policy compliance.
For example, a treasury team might set rules like: "Payments to new vendor addresses over $5,000 require CFO approval and verification", or "Weekend transfers above $10,000 need additional sign-off from another executive." These policies are enforced cryptographically and logged in an immutable audit trail, aligning with regulations like MiCA in the EU and U.S. supervisory standards.
Platforms such as Stablerail (https://stablerail.com) add another layer of protection by conducting pre-transaction checks. These include sanctions screening, policy enforcement, and anomaly detection. Finance teams can define governance rules that are then enforced automatically, ensuring that every transaction is evaluated in the context of the business - not just based on cryptographic authorization.
This combination of cryptography and automated policies creates a solid framework for managing treasury operations securely and efficiently.
Stablecoin Treasury Use Cases
With secure key management and robust governance in place, threshold-based wallets open the door to practical treasury applications like vendor payments, internal transfers, and cross-chain treasury rebalancing. In 2024, stablecoins handled $27.6 trillion in transaction volume - surpassing Visa and Mastercard combined. Today, 90% of financial institutions are either using or planning to use stablecoins for payments and settlements.
For vendor payments, businesses can configure hot wallets with automated policy enforcement for transactions under $10,000, while requiring a 3-of-5 threshold for higher-value transfers. This setup allows for quick processing of routine payments while maintaining strong security for larger transactions.
MPC wallets also generate a single signature compatible with ECDSA or EdDSA blockchains, enabling smooth USDC transfers across Ethereum, Base, and Polygon without needing custom contracts. Companies have reported saving at least 10% on cross-border B2B payments while maintaining strict governance. By layering policy-driven signing onto threshold cryptography, organizations achieve a balance between speed and security for their treasury operations.
Governance, Security, and Risk Management in Threshold Wallets
Security Benefits of Threshold Cryptography
Threshold cryptography offers a powerful safeguard by ensuring that a complete private key never exists on any device or server. Instead, keys are divided into secure shares, which are stored separately - whether in hardware security modules (HSMs), user devices, or cloud environments - throughout their entire lifecycle. This means attackers can’t extract a full key, even if they gain access to a compromised device or server.
This approach also addresses insider threats effectively. Since threshold signing requires a quorum (e.g., 3-of-5 participants), no single individual, even a rogue employee, can drain funds unilaterally. And even if one or two key shares are compromised, they are mathematically useless without meeting the threshold. Regular rotation of key shares further reduces risk by refreshing these shares, limiting their exposure over time.
The Multichain incident in July 2023 serves as a stark reminder of the importance of proper operational architecture. Following CEO Zhaojun's detention, attackers exploited an unauthorized cloud login to steal over $130 million in assets. This incident highlights the critical need to distribute key shares across independent entities and cloud providers to ensure true threshold security.
Integrating Pre-Transaction Controls
Threshold cryptography provides a strong foundation for security, but it becomes even more effective when paired with pre-transaction controls. These controls enforce business rules, ensuring that even a valid quorum cannot bypass established policies. Pre-transaction checks include processes like sanctions screening, spending limits, destination whitelisting, and behavioral anomaly detection, all of which occur before the signing process begins.
Stablerail (https://stablerail.com) operates in this crucial layer, adding an extra level of governance. It performs mandatory pre-sign checks through specialized agents, covering areas like sanctions and taint screening, policy enforcement, and behavioral anomaly detection. For example, it can analyze factors like transaction timing, amounts compared to historical baselines, and payout patterns. It also evaluates counterparty risk. Finance teams can establish governance rules that are automatically enforced, ensuring every transaction is reviewed in its full business context - not just its cryptographic validity. Additionally, Stablerail generates plain-English explanations for each decision, referencing specific policy clauses and timestamps to provide clarity.
This layered approach - combining distributed cryptography with automated policy enforcement - creates a robust defense system. Transactions must meet both quorum requirements and policy compliance, achieving a balance between operational efficiency and security.
Auditability and Compliance with Threshold Wallets
Although threshold signatures appear as standard single-key transactions on the blockchain, detailed off-chain logs maintain auditability by recording which participants were involved in each signing session. This creates a transparent audit trail without exposing governance structures publicly, a key advantage over MultiSig wallets.
This design aligns with global regulatory standards. Frameworks like the EU's MiCA, Singapore's Payment Services Act, and Hong Kong's SFC Guidelines increasingly recognize distributed cryptographic solutions, such as key sharding, as secure methods for digital asset custody. A fundamental requirement of these regulations is that no single party can unilaterally move assets - a condition that threshold cryptography enforces mathematically.
Systems like Stablerail enhance compliance by recording every step of the process, from intent creation to checks, flagging, overrides, approvals, and signing. These records provide CFO-level evidence of segregation of duties and adherence to internal controls, even though the resulting blockchain transaction looks like a standard transfer.
Operational resilience is another key strength. Threshold schemes are designed to tolerate up to t-1 node failures or compromises, ensuring treasury operations can continue even if some signers are unavailable. By combining these audit trails with robust threshold protocols, organizations can establish a secure and compliant framework for managing their digital assets effectively.
Conclusion
Threshold cryptography is reshaping digital asset management by ensuring that a complete private key is never fully formed during its generation, storage, or signing process. This approach eliminates the single points of failure that have historically led to major losses when centralized control systems were compromised.
It brings three standout benefits:
Universal compatibility: Standard signatures like ECDSA or EdDSA work seamlessly across all blockchains, even without smart contract support.
Operational efficiency: Transaction sizes remain standard, keeping gas costs low.
Private governance: Off-chain policy updates leave no trace on the blockchain, ensuring privacy.
When combined with pre-transaction controls, these features enable even stricter governance protocols. For instance, platforms like Stablerail (https://stablerail.com) enforce robust policies such as sanctions screening and anomaly detection. This ensures that even if a valid quorum is achieved, transactions still adhere to business rules before execution, creating a dual-layered framework of cryptographic and policy compliance.
Regulators are also taking notice. Frameworks such as the EU's MiCA, Singapore's MAS, and Hong Kong's SFC Guidelines now recognize methods like key sharding and MPC as secure approaches for digital asset custody. By ensuring no single entity can independently move funds, threshold cryptography aligns with the "possession and control" standards that regulators demand today.
FAQs
How does threshold cryptography strengthen security for enterprise wallets?
Threshold cryptography strengthens the security of enterprise wallets by breaking a private key into encrypted parts, known as shares, which are distributed among several independent parties. To generate a valid signature, a specific number of these shares - referred to as the threshold - must work together. This setup ensures that no single party ever has full access to the private key, making it much more difficult for attackers to access funds.
Even if one party is compromised or becomes unavailable, the wallet stays secure and functional, offering both resilience and strong protection for critical digital assets.
How does Secure Multiparty Computation (MPC) enhance private key security?
Secure Multiparty Computation (MPC) strengthens private key protection by breaking the key into multiple encrypted shares and distributing them across different parties. To approve a transaction, a set number of these shares must work together to create a signature - ensuring the complete key is never assembled in one place.
This method drastically lowers the risk of key theft since no single party holds the entire key. It also ensures transactions are authorized only when the required number of parties collaborates, providing an additional layer of security for enterprise wallets.
How do threshold wallets support compliance with global regulations?
Threshold wallets leverage advanced cryptographic techniques, such as threshold signature schemes (TSS) and Distributed Key Generation (DKG), to divide private keys into encrypted shares. These shares never exist as a complete key on any single device, which eliminates single points of failure. This approach not only boosts security but also aligns with regulatory demands for secure custody solutions.
Beyond their cryptographic strength, enterprise-grade wallets come equipped with programmable governance tools. These tools help enforce compliance by performing pre-sign checks before any transaction is approved. Examples include sanctions screening, transaction limits, anomaly detection, and counterparty risk assessments. For added security, high-value or unusual transactions often require multi-level approvals, such as sign-off from the CFO, ensuring they adhere to corporate governance standards.
To meet regulatory requirements, every step of a transaction is recorded in an immutable audit trail. This provides necessary evidence for frameworks like SOX, AML/KYC, and tax reporting. By blending strong cryptographic protections with policy enforcement and detailed auditability, threshold wallets allow for secure and compliant management of digital assets - without sacrificing the speed of on-chain settlements.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


