
Stablecoin transactions are booming, with custodial stablecoins processing $27.6 trillion in 2024, surpassing Visa and Mastercard combined. But this growth comes with risks like hacks and compliance issues. A Risk Dossier acts as a safety net, ensuring every transaction is secure, compliant, and audit-ready. It combines transaction intent, risk checks, and clear verdicts (PASS, FLAG, or BLOCK) into one actionable package.
Key Steps to Build a Risk Dossier:
Document Transaction Intent: Record payment details, including recipient, purpose, and network.
Verify Funds and Entities: Check balances and validate counterparties against risk standards.
Run Automated Risk Checks: Run sanctions screening for stablecoin payments to identify anomalies and exposure to malicious addresses.
Compile Evidence: Organize findings into a clear, audit-ready dossier.
Approve Transactions: Use multi-party computation (MPC) for secure final approvals and generate detailed receipts.
Risk Dossiers streamline compliance, protect funds, and simplify audits by turning complex data into actionable insights. Tools like Stablerail automate this process, making stablecoin transactions safer and more transparent.
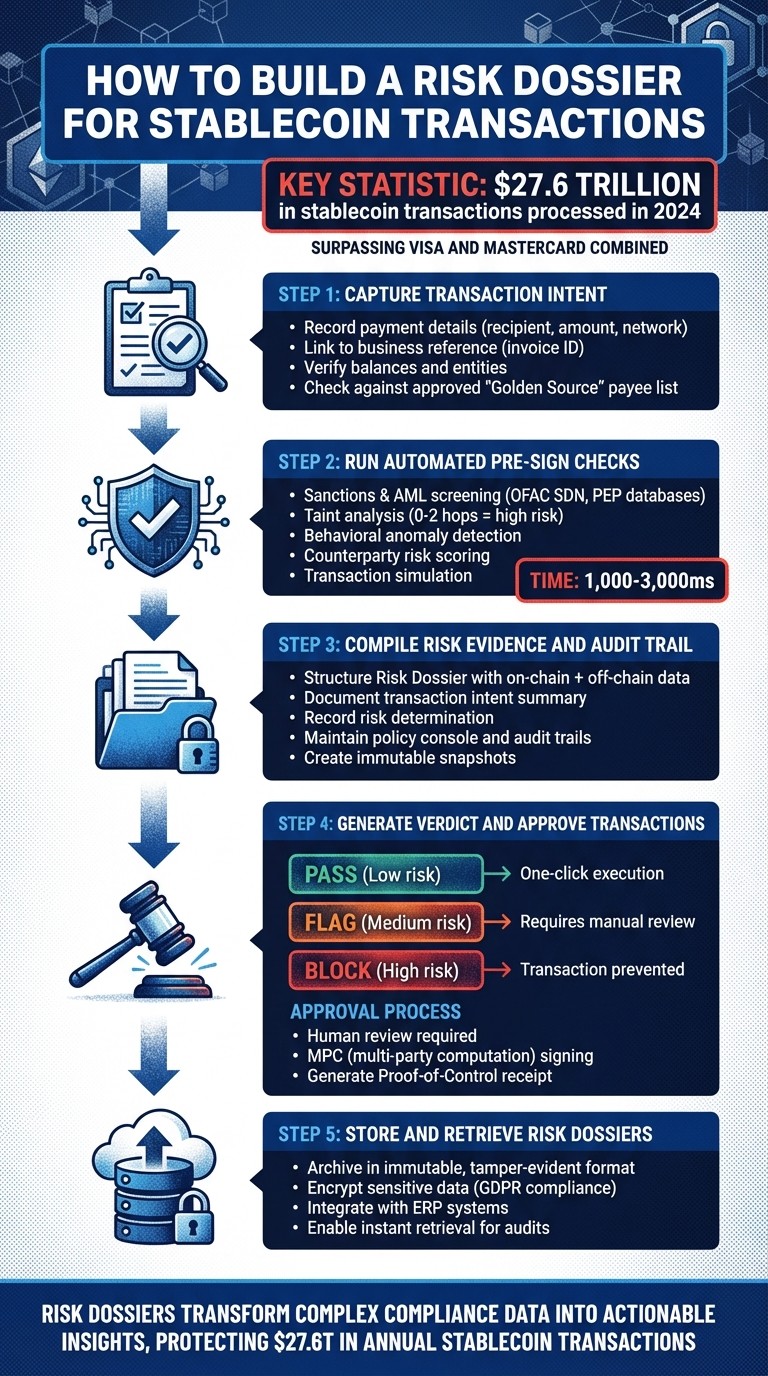
5-Step Process to Build a Risk Dossier for Stablecoin Transactions
Step 1: Capture Transaction Intent
Record Payment Details
Start by documenting the purpose behind each transaction. This includes noting recipient and sender addresses, transaction amounts (both in tokens and USD), the network used (e.g., Ethereum, Base, Solana), and the stablecoin contract involved.
To connect payments with business records, link each transaction to a clear reference, such as an invoice ID. It's essential to include a mandatory reference - like an invoice or purchase order - to ensure on-chain data aligns seamlessly with your accounting system.
As highlighted by Stablecoin Insider:
"Every transaction should tie back to a business purpose, approval evidence, and a ledger entry."
For transactions involving smart contracts, make sure to log technical details like decoded calldata, unique nonces, and timestamps. These steps are key to protecting against replay attacks.
Before moving forward, double-check your available funds and confirm the legitimacy of the counterparty to establish a secure transaction framework.
Verify Balances and Entities
Once the transaction intent is documented, verify that the funds and entity details meet your risk standards. Tools like Stablerail's Treasury Hub can simplify this process by automating verifications, eliminating the need for tedious spreadsheet checks.
Use an approved "Golden Source" payee list to validate legitimate vendors. If a vendor updates their wallet address, the system should automatically flag the payment for review before proceeding. This precaution helps avoid accidental "blind signing" to unverified or potentially harmful destinations.
Additionally, keep an eye out for risk indicators such as wallets with fewer than three transactions or dormant wallets that have been inactive for over 180 days. For regulated transfers, ensure compliance with Travel Rule protocols to mitigate risks.
Step 2: Run Automated Pre-Sign Checks
Execute Required Risk Checks
Once you've captured the transaction intent and verified balances, it's time to run a series of automated checks before signing off on any payment. These checks include sanctions screening, taint analysis, behavioral anomaly detection, counterparty risk scoring, and transaction simulation.
Start with sanctions and AML screening. Your system should cross-check addresses in real time against global sanctions lists like OFAC SDN, PEP databases, and high-risk jurisdictions. Next, conduct taint and exposure analysis using machine learning to identify links to illicit activity. For example, transactions within 0–2 hops of known malicious addresses are typically flagged as "high risk".
Behavioral anomaly detection helps identify unusual activity, such as round-number transfers, unexpected transaction speeds, or payments made outside normal working hours. Imagine your treasury usually processes payments between 9:00 AM and 5:00 PM EST on weekdays. If a $50,000 transfer is initiated at 2:00 AM on a Sunday, it should automatically raise a flag.
Counterparty risk scoring evaluates the recipient's wallet history. Wallets are generally deemed "established" only if they are at least 7 days old and have completed 3 or more transactions. New wallets with no transaction history or dormant wallets inactive for over 180 days should be flagged for further review.
Finally, perform a transaction simulation to test how the payment would execute in real-world conditions. This step can uncover issues like address changes, duplicate payments, or first-time destinations before funds are committed. Risk assessments typically complete within 1,000–3,000ms.
Once the checks are complete, translate the results into clear, actionable insights.
Create Plain-English Explanations
Raw risk scores aren't helpful for finance teams trying to make quick decisions. That's where AI tools come in, converting complex risk data into easy-to-understand narratives. For instance, instead of showing "Risk Score: 7.2", the system might say: "Recipient is a new wallet with no transaction history. This payment requires CFO approval under Policy 3.2."
Trail of Bits highlights the importance of redundancy in risk checks:
"Single points of verification create catastrophic failure modes."
Use smart contract decoding tools to translate technical details into readable terms. For example, hardware wallets often can't interpret DeFi transactions, so software-based simulations become essential for generating accurate, plain-English summaries.
Each explanation should include supporting evidence, such as the policy clause triggered, timestamps, and relevant risk indicators. For example: "Payment flagged at 2:47 PM EST on 2/25/2026. Recipient address (0x742d...8f3a) matches 4-character prefix/suffix poisoning pattern. Treasury Policy 5.1 requires manual verification for suspected address poisoning."
Platforms like Stablerail automatically generate these narratives, tying them to specific evidence like policy clauses and timestamps. These summaries provide the backbone for pre-execution governance.
Organize Results for Review
Once you've generated plain-language summaries, organize the findings into a clear verdict: PASS, FLAG, or BLOCK. This structure ensures reviewers can make quick, informed decisions without needing to interpret raw data.
PASS: The transaction meets all policy requirements and passes every risk check. These payments proceed directly to the approval queue.
FLAG: Indicates concerns that require manual review. If approved, an explicit override reason must be provided.
BLOCK: The transaction violates a hard policy rule or triggers a high-risk alert, preventing execution altogether.
Display each check's outcome alongside the final verdict. For internal reviews, automated "own-account" verification can bypass certain checks while maintaining a full audit trail. These consolidated results form a critical part of the final Risk Dossier, supporting the decision-making process.
As Stablerail explains:
"The copilot can read policies, transaction context, and on-chain data... Its only role is to block, flag, and explain."
For flagged transactions, enforce cooling-off periods. For example, delay high-value transfers over $100,000 or payments to new beneficiaries for a set period, such as 4 hours, to reduce the risk of social engineering attacks.
Step 3: Compile Risk Evidence and Audit Trail
Structure the Risk Dossier
After completing pre-sign checks and organizing the results, the next step is to assemble a comprehensive Risk Dossier for review. This document combines on-chain data - such as transaction hash, timestamp, asset type, amount, fees, and wallet addresses - with off-chain details, like invoice numbers, payment purposes, and supporting documents.
To keep the dossier clear and actionable, divide it into key sections:
Transaction intent summary
Overall risk determination
Detailed breakdown of individual risk factors
Each risk factor should include:
A unique identifier (e.g., "new_wallet_recipient")
A specific risk level (low, medium, or high)
A clear, non-technical explanation of the risk verdict
Following a "maximum risk rule" ensures that if any factor is classified as high risk, the entire dossier is flagged as high risk. This policy highlights critical concerns upfront, saving reviewers from digging into every detail.
Additionally, include a Proof-of-Control record that documents approvals and references to maintain accountability and compliance. This record ensures segregation of duties by showing that no single individual handled the request, approval, and execution of the payment. As Stablerail puts it:
"Every payout generates a defensible receipt: what was paid, why, who approved, and the risk verdict."
Standardizing the data is crucial. Tie each payment to a unique business reference for easier reconciliation and clarity. By organizing this information thoroughly, you safeguard transactions and meet compliance standards.
Once the Risk Dossier is fully structured, log every decision and action in detailed audit records to ensure traceability.
Maintain Policy Console and Audit Trails
Building on the structured dossier, it's essential to maintain a robust, secure audit trail for every approval and override. Use role-based logging to capture key details like the requester, preparer, approver, and signer, along with timestamps and MPC quorum details. This creates a complete, verifiable sign-off trail for auditors, boards, and regulators.
Record the specific policy version and rule set active at the time of each transaction to demonstrate compliance with the governance standards in place at that time. For flagged transactions, document the exact reason for any manual overrides or escalations, ensuring transparency.
Another important step is capturing immutable snapshots of data and risk scores at the time of decision-making. This allows you to justify actions during future reviews, even if your risk policies or models have since changed.
For monthly closes or audits, export Evidence Packs that consolidate transaction data, approval logs, and supporting business documents into a single, defensible record. Stablerail automatically generates these records, linking each payment to its business justification, the specific approvers, and the automated risk verdict.
Your audit trail should clearly establish four key elements:
What happened on-chain (transaction hash and timestamp)
Why it happened (business purpose)
Who approved it (evidence of sign-off)
How it was booked (ledger entry)
This comprehensive framework ensures your Risk Dossier aligns with both internal governance and external compliance requirements.
Step 4: Generate Verdict and Approve Transactions
Issue a Final Verdict
After completing the detailed pre-sign checks and building a structured audit trail, the system delivers a final verdict that determines whether the transaction moves forward. This decision is based on a maximum risk approach: if any single risk factor is deemed high, the transaction is categorized as high risk overall.
The verdict can fall into one of three categories:
PASS (Low Risk): The transaction appears secure across all factors and is ready for one-click execution via MPC.
FLAG (Medium Risk): There are some concerns - like a reactivated dormant wallet or limited interaction history. These transactions are frozen until a human reviewer provides a recorded override reason.
BLOCK (High Risk): Significant threats are detected, such as ties to malicious addresses (within 0-2 hops) or patterns indicative of address poisoning.
Every decision is backed by evidence from the Risk Dossier. Instead of relying on subjective judgment, the system provides plain-English explanations tied to specific policy clauses, timestamps, and data points. This transparency ensures approvers can understand exactly why a transaction is flagged or blocked, allowing them to make informed decisions rather than relying on instinct. Once the automated verdict is issued, human approvers perform a final review before the transaction proceeds.
Review and Sign via MPC
With the Risk Dossier in hand, the findings are enforced through a final verdict and secure approvals. Human approvers must carefully review the dossier before any transaction is executed. This human-in-the-loop process ensures that while automated systems verify the context, only authorized individuals can provide the final signatures. As Stablerail explains:
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money."
Approvers should confirm that each transaction aligns with mandatory business references, such as invoice IDs, payroll batch IDs, or refund ticket numbers. Supporting evidence, like purchase orders or settlement reports, should also be reviewed. For flagged transactions, the system remains locked until all required approvals and documented override reasons are provided.
To ensure secure signing, MPC (multi-party computation) splits private keys among multiple parties, preventing any single entity from having full control. Configurable signing thresholds - such as 2-of-3 or 3-of-5 - eliminate single points of failure. Even if one signer's environment is compromised, the transaction cannot proceed without meeting the required quorum. High-value transfers or high-risk transactions should enforce stricter thresholds, requiring more approvers and additional scrutiny.
For transactions involving large sums (e.g., over $100,000) or payments to new beneficiaries, a cooling-off period is recommended. This introduces an automatic delay of several hours between the final verdict and MPC signing, giving time to verify unusual requests through secondary channels. Once all approvals are in place and the transaction is signed, the final step is to document the process with a detailed receipt.
Create Transaction Receipts
After the transaction is signed via MPC and broadcast, the system generates a Proof-of-Control receipt that captures the entire decision-making process. These "CFO-grade" receipts detail what was paid, why it was paid, who approved it, and the final risk verdict. They provide essential evidence for auditors and regulators.
Each receipt should include the transaction hash, business purpose, risk verdict, and the identities of all approvers. If a flagged transaction was manually overridden, the receipt must clearly document the specific reason for the override or escalation, ensuring full transparency. This level of detail justifies decisions during future reviews, even if policies evolve.
Stablerail automates the creation of these records, linking each payment to its justification, the approvers involved, and the automated risk verdict. This results in an immutable audit trail that clearly shows what happened on-chain, why it occurred, how it was approved, and how it was recorded - meeting both internal governance needs and external compliance standards.
Step 5: Store and Retrieve Risk Dossiers
Archive Dossiers for Compliance
Once a transaction is settled, the Risk Dossier should be preserved as a permanent compliance record. Properly storing these dossiers ensures that every decision remains defensible during audits or regulatory reviews. To achieve this, use immutable, tamper-evident formats like Merkle-addressable transcripts or databases. These formats provide clear evidence that no alterations were made to the records after the transaction, meeting regulatory requirements.
Each archived dossier must include read-only historical snapshots of all relevant data used during the decision-making process. This includes risk scores, entity tags (e.g., whether an address was flagged as a mixer or exchange), and the sanctions list status as it appeared at the time of the transaction - not as it stands today. For example, if a counterparty was approved in February 2026 but flagged in March, the dossier should document the February status to confirm that the decision was appropriate based on the information available at that time.
To ensure data security and compliance with GDPR, encrypt sensitive dossier details. Additionally, integrate these dossiers with ERP systems through webhooks for automated General Ledger (GL) reconciliation. This integration links on-chain activity directly to GL entries, eliminating the need for manual wallet data extraction and ensuring accurate reconciliation.
By building this secure archival system, you create a foundation for easy access and seamless integration into routine financial processes.
Integrate Dossiers into Recurring Workflows
Beyond archiving, embedding Risk Dossiers into daily workflows turns static records into dynamic governance tools. When integrated effectively, these dossiers simplify audits, monthly financial closings, and regulatory reporting, while significantly reducing manual effort.
Begin by requiring mandatory business references for every transaction. For instance, attach an Invoice ID, Payroll Batch ID, or Purchase Order number to each transaction. This ensures that dossiers can be automatically retrieved during audits or reconciliations, creating a direct connection between the transaction and its business purpose. This setup allows for instant retrieval of complete Risk Dossiers whenever needed.
For businesses managing Vendor and B2B payments, tools like Stablerail's module can integrate Risk Dossiers directly into the payment workflow. Each governed transfer automatically generates and archives its dossier, ensuring consistent documentation for all transactions. To handle high transaction volumes, implement message queues such as Apache Kafka or RabbitMQ to guarantee reliable data ingestion, storage, and analysis.
Managing Crypto Threats in 2026 | Compliance, Fraud & Investigation Strategies
Conclusion: Secure Stablecoin Transactions with Risk Dossiers
Establishing a Risk Dossier is a game-changer for securing stablecoin transactions. This approach transforms stablecoin payments into a process that’s both secure and audit-ready. By following a clear five-step framework, you eliminate blind signing and ensure every transaction is backed by thorough documentation. Each payment is verified against sanctions lists, policy limits, and counterparty risk patterns - before the final approval.
The numbers speak for themselves. In 2024, custodial stablecoins hit an astonishing $27.6 trillion in transaction volume, surpassing the combined totals of Visa and Mastercard. This growth has brought intense scrutiny, with global compliance costs reaching over $274 billion in 2023. Risk Dossiers deliver the detailed audit trails and clear explanations that regulators, auditors, and boards expect, while also shielding your treasury from potential freeze risks. For instance, during the Multichain hack, stablecoin issuers managed to freeze $66 million of the $126 million stolen, underscoring the importance of real-time risk management.
Stablerail simplifies this entire process by integrating above custody and before signing. Instead of relying on spreadsheets, Slack approvals, or manual risk assessments, finance teams can implement policy-as-code rules (like "Payments over $5,000 to new addresses require CFO approval and verification"). These rules are enforced automatically. Stablerail’s AI agents create Risk Dossiers with clear PASS/FLAG/BLOCK verdicts and evidence-based justifications, while human controllers maintain full signing authority using MPC-secured vaults. Every transaction generates a Proof-of-Control receipt, detailing the purpose, participants, and risk assessment - making compliance an integral part of the workflow.
"Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money." - Stablerail
FAQs
What should a Risk Dossier include?
A Risk Dossier needs to clearly justify the transaction decision - whether it's PASS, FLAG, or BLOCK. It should outline the intent behind the transaction, reference applicable policy clauses, and include key details like timestamps and compliance check outcomes. These checks might involve sanctions screening, exposure analysis, anomaly detection, counterparty risk scoring, and policy enforcement.
The dossier must also explain the rationale for the decision in plain, straightforward language. This explanation should be backed by evidence and include references to the relevant data, ensuring a transparent audit trail for stakeholders.
How do PASS, FLAG, and BLOCK decisions work?
When evaluating transactions, risk checks and policy enforcement lead to three possible outcomes: PASS, FLAG, and BLOCK.
PASS: The transaction satisfies all compliance and risk requirements, allowing it to move forward without issues.
FLAG: Certain aspects raise potential concerns, requiring additional review or verification before proceeding.
BLOCK: The transaction does not pass risk checks and is stopped to prevent any violations.
Each decision is accompanied by detailed documentation, ensuring transparency for audits and reviews.
How long should we retain Risk Dossiers for audits?
The article doesn’t provide a specific timeframe for keeping Risk Dossiers. However, holding onto them for 3 to 7 years is generally recommended. This timeframe aligns with common practices for financial records and helps ensure you're prepared for regulatory audits, internal reviews, or investigations. Maintaining a solid audit trail is key to showing compliance when needed.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


