
Stablecoins processed over $10 trillion in 2025 but brought heightened risks like irreversible transactions, fraud, and compliance issues. Behavioral anomaly detection systems address these challenges by flagging suspicious activity before transactions are finalized. These systems analyze patterns - such as unusual transaction timings, amounts, or destinations - to prevent errors, fraud, and regulatory violations.
Key Insights:
Irreversible Transactions: Once confirmed, stablecoin payments can't be undone, making pre-signature safeguards critical.
Common Risks: Fraud, operational mistakes, and compliance violations tied to irregular transaction patterns.
How Detection Works: Systems use dynamic baselines to identify anomalies, reducing false positives and catching complex risks.
Benefits: Real-time alerts, pre-sign verification, and audit trails ensure secure, compliant, and efficient treasury operations.
Behavioral anomaly detection bridges the gap between the speed of blockchain payments and the governance needed to manage risks effectively.
Instant Payments Create Massive Fraud Risk
What Are Behavioral Anomalies in Stablecoin Payments?
Behavioral anomalies refer to unusual deviations from an organization's typical transaction patterns. When it comes to stablecoin payments, these deviations can indicate issues like fraud, operational mistakes, or compliance violations. Unlike traditional banking systems, where transactions can often be reversed or accounts frozen, stablecoin transfers are final once confirmed on the blockchain. This makes identifying anomalies before signing off on transactions absolutely crucial.
What counts as "normal" depends on the organization. For example, a $50,000 payment might be routine for a large corporation but highly unusual for a small startup. Similarly, weekend transactions may be standard for global businesses but could raise eyebrows for a company operating strictly Monday through Friday.
Common Signs of Anomalous Activity
Certain red flags can help identify potential issues in stablecoin payments:
Temporal irregularities: Transactions occurring at odd hours, like 3 a.m. on a Sunday, might seem suspicious if your finance team typically operates during standard business hours.
Value deviations: Payments that significantly differ from historical norms are another warning sign. For instance, if your company usually processes payments between $2,000 and $10,000, a sudden $75,000 transfer to an unfamiliar wallet should raise concerns. Similarly, a sudden surge in transaction frequency - such as ten transfers in quick succession when the usual rate is three per day - might signal trouble.
Destination risks: Transfers to unknown or high-risk wallet addresses can be problematic. This includes payments to wallets flagged in sanctions screenings or linked to scams. Another red flag is "chain hopping", where funds are rapidly moved across multiple blockchains to obscure their origin.
These patterns highlight the unique vulnerabilities tied to stablecoin payments.
Why Stablecoin Transactions Carry Greater Risks
Stablecoin transactions present heightened risks because they are irreversible. Unlike traditional bank transfers, which allow for chargebacks, once a stablecoin payment is confirmed, it cannot be undone. This makes it easier for finance teams to fall into the trap of "blind signing" - approving a transaction without fully understanding its context. This could result in funds being sent to the wrong wallet or duplicated payments being authorized.
The issue is often worsened by outdated operational workflows. Many companies still rely on manual processes like using spreadsheets, Slack messages, and wallet approvals, which lack proper approval chains and audit trails. In such setups, a single compromised employee could drain funds before the problem is even detected. Without real-time checks and pre-signature safeguards, these anomalies can easily go unnoticed, leaving organizations exposed to significant risks.
How Anomaly Detection Reduces Stablecoin Risks
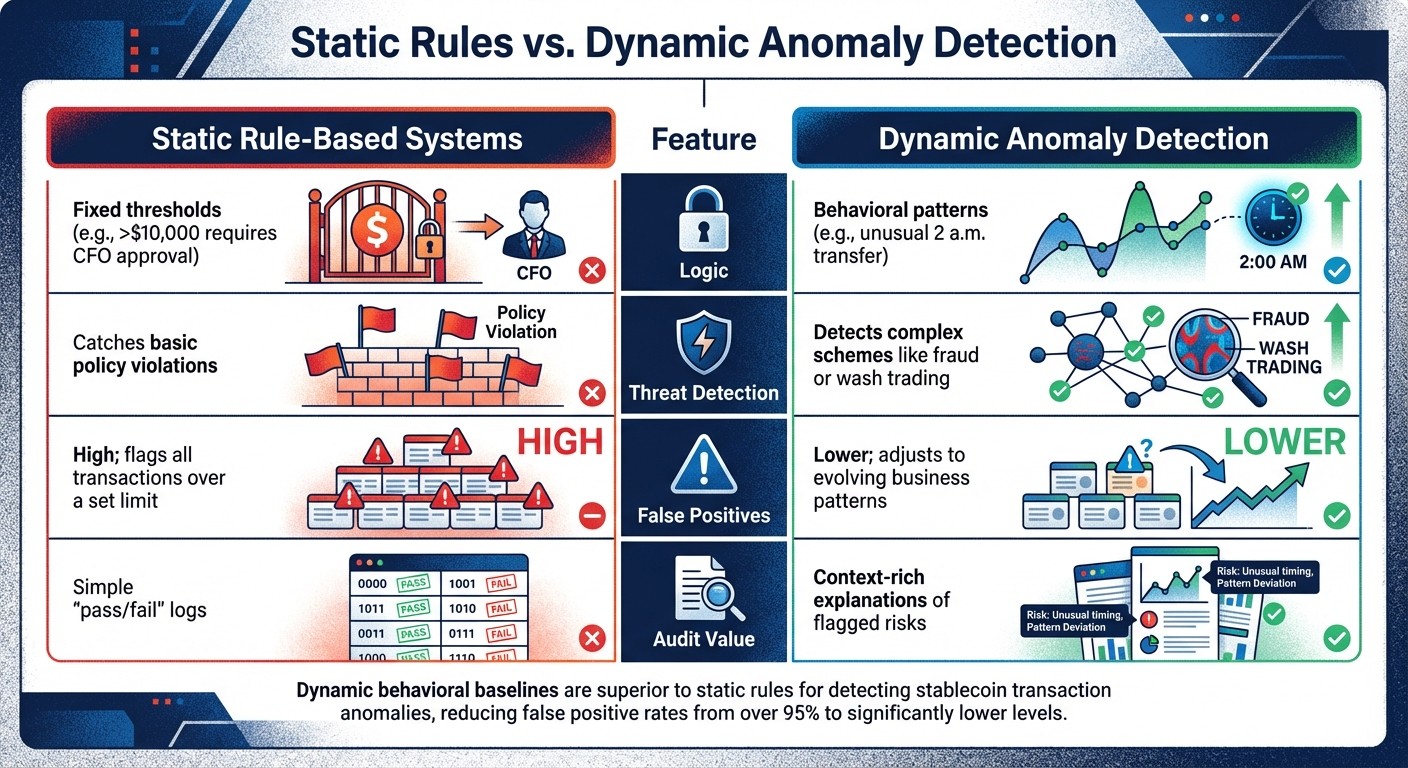
Static Rules vs Dynamic Anomaly Detection in Stablecoin Security
Anomaly detection systems are designed to flag suspicious activity before transactions are signed and broadcast. By catching risky patterns in real time, these systems allow finance teams to manage MPC wallets and step in within minutes, potentially preventing significant losses. This proactive approach shifts stablecoin governance from simply reacting to issues after they occur to actively managing risks ahead of time. Organizations can further quantify these threats using a stablecoin risk calculator to establish baseline safety scores.
For instance, imagine a system identifying a $500,000 transfer happening at 2 a.m. on a Saturday from an account that typically handles $5,000 payments during business hours. It would immediately generate an alert and block the transaction until a human could review it. This pre-sign verification adds a critical layer of protection, allowing teams to prevent losses before they happen.
Anomaly detection also creates a detailed compliance trail. Every alert is logged with timestamps and cryptographic hashes, providing auditable documentation for regulators and auditors. This ensures organizations can demonstrate that stringent controls were in place when decisions were made.
Dynamic Baselines vs. Static Rules
One of the key distinctions in anomaly detection is the difference between static rules and dynamic baselines. Static systems rely on fixed thresholds, such as "Any payment over $10,000 requires CFO approval." While simple, this approach often triggers excessive false positives for businesses that routinely handle large transactions. Worse, it might fail to catch sophisticated threats that fall outside these rigid parameters.
Dynamic baselines, on the other hand, adapt to individual behavior patterns. These systems monitor metrics like typical transaction amounts, frequency, counterparties, and time-of-day trends to establish what’s normal for a specific user or wallet. For example, if a user usually makes five weekly transfers of $500, but suddenly initiates 20 transfers of $5,000 in quick succession, the system would flag this as anomalous behavior.
Here’s a quick comparison of static rules and dynamic baselines:
Pre-Sign Verification and Real-Time Alerts
Anomaly detection becomes even more effective when combined with pre-sign verification and real-time alerts. These systems screen transactions before they are signed, checking for compliance with sanctions, policy rules, and behavioral baselines. For example, if a payment intent involves moving $2 million through five wallets in 30 minutes, the system would flag this as a risk and generate a dossier with a verdict: PASS, FLAG, or BLOCK.
This workflow keeps humans in the loop, allowing approvers to review flagged transactions in seconds rather than days. The system provides clear explanations of why a transaction is flagged, making it easier for finance teams to take action - whether that means approving, rejecting, or requesting further verification.
Speed is critical because once a stablecoin transaction is broadcast, it’s final. Systems that screen payments in under a second and generate alerts for anomalies - such as transactions exceeding three standard deviations from the baseline - help ensure reviews are completed in less than 10 minutes. Stablerail exemplifies this approach by using specialized agents to perform mandatory pre-sign checks. These checks include analyzing behavioral anomalies related to timing, amounts, and payout patterns. As Stablerail puts it: agents verify the context, humans approve the transaction, and the system secures the treasury - without ever moving funds.
This layered approach blends the speed of on-chain transactions with the robust controls of traditional banking. It gives finance teams the ability to maintain oversight and streamline workflows, reducing vulnerabilities to fraud, compliance failures, and operational mistakes.
What Makes an Anomaly Detection System Work
For an anomaly detection system to be effective, it needs to rely on dynamic metrics rather than static thresholds. These metrics consider the context around transactions - factors like timing, frequency, counterparties, and interaction methods. For instance, analyzing whether a wallet frequently interacts with decentralized exchanges like Uniswap or centralized platforms can help distinguish routine business activities from suspicious ones, such as potential money laundering schemes.
The system creates dynamic baselines by learning the usual behavior of each wallet. For example, if a treasury wallet typically performs regular transfers during business hours, this pattern becomes its baseline. If the wallet suddenly makes an unusually large transfer at an odd hour, the system flags it - even if the amount would otherwise seem acceptable under static rules. This approach significantly reduces the false positive rate, which is over 95% in traditional rule-based systems. Below, we break down the key metrics used to identify normal behavior.
Metrics Used to Define Normal Behavior
Anomaly detection systems rely on various data categories - temporal, transactional, and counterparty metrics - to recognize normal activity.
Temporal metrics: These include patterns like the time of day or bursts of daily transactions. For example, a wallet that operates between 9 a.m. and 5 p.m. EST on weekdays establishes a temporal baseline. If that wallet suddenly starts processing transactions over the weekend, it could indicate unusual activity.
Transaction characteristics: These cover details such as payment size, frequency, and velocity. The system doesn’t just monitor individual transactions but also tracks patterns, like multiple high-value transfers occurring in quick succession. Techniques like multi-hop tracking, which examines second-degree connections involving transfers over $10,000, are particularly useful for identifying links to illicit networks. This is critical given that in 2024 alone, about $51 billion was laundered through cryptocurrencies, accounting for 0.14% of all on-chain transactions.
Counterparty and interaction features: The system evaluates which addresses receive funds, how frequently these relationships occur, and the protocols involved. Wallets that use decentralized exchanges instead of centralized ones often have different risk profiles, as bad actors tend to avoid platforms with stricter Know Your Customer (KYC) requirements. These metrics also help mitigate freeze-risk scenarios, where stablecoin issuers like Tether or Circle might freeze assets. To date, over $5 billion in USDT and USDC has been frozen in such scenarios.
Clear Explanations and Audit Trails
A system’s value isn’t just in detecting anomalies - it’s also in providing clear, actionable insights. Finance teams need straightforward explanations that link flagged behavior to specific risks. For instance, when a transaction is blocked, the system should outline why the activity deviates from the wallet’s baseline and which policy thresholds it violates. By referencing specific policy clauses and timestamps, the system enables decision-makers to act quickly and confidently.
In stablecoin governance, detailed documentation plays a crucial role in ensuring both compliance and rapid intervention. Key details - like wallet and user IDs, timestamps, transaction hashes, amounts (in both native tokens and USD), risk scores, and cryptographic proofs - are logged. This transforms anomaly detection from a simple alert system into a compliance tool that demonstrates due diligence to regulators and auditors.
Stablerail offers a strong example of this approach. For each payment intent, it generates a comprehensive Risk Dossier that includes a verdict of PASS, FLAG, or BLOCK, along with detailed reasoning. The system keeps an immutable audit trail that records every step, from intent creation to checks, flags, overrides, approvals, and final signing. As Stablerail explains:
Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money.
Combining Anomaly Detection with Policy Enforcement
Behavioral anomaly detection becomes especially effective when paired with policy-as-code systems, creating a governance layer that operates before a transaction is signed. This pre-signature control is critical in blockchain payments, where transactions are irreversible once confirmed. To address this, an "intelligence layer" is placed between treasury custody and the final cryptographic signature, ensuring risks are identified and addressed in advance.
Policy-as-code transforms governance rules into automated commands that execute without manual intervention. Instead of relying on spreadsheets and Slack approvals, governance rules - like requiring enhanced approvals for high-value or weekend transfers - are codified into immutable, automated processes. Within this framework, anomaly detection acts as a dynamic safety net, analyzing real-time factors like deviations in transaction amounts, unusual payout patterns, and time-of-day activity to complement these static rules.
From Detection to Decision
When policy-as-code is in place, anomalies detected by the system are seamlessly integrated into decision-making workflows. The system generates a detailed Risk Dossier with one of three outcomes: PASS, FLAG, or BLOCK. Low-risk transactions that pass all checks proceed directly to signing without delay. Flagged transactions, however, require additional human review, further verification, or documented override reasons before they can move forward.
This shift toward real-time, pre-transaction controls is becoming increasingly important as regulations like the U.S. GENIUS Act push stablecoin issuers to adopt oversight mechanisms similar to those in traditional banking. Unlike post-transaction monitoring, which is ineffective for irreversible blockchain payments, pre-signature controls catch risks before they can materialize. This proactive approach ensures both regulatory compliance and operational efficiency.
Maintaining Speed While Enforcing Governance
One of the biggest challenges is balancing the speed of blockchain settlements with the need for robust governance. Traditional manual approval processes can slow down transactions, but policy-enforced systems take a different approach. Routine, low-risk transactions are processed instantly, while only high-risk or unusual payments are flagged for further review. This approach works hand-in-hand with anomaly detection, ensuring rapid settlements without compromising risk management.
A practical example of this model in action is Stablerail. Designed for companies managing $1 million to $50 million annually in stablecoin transactions, Stablerail serves as a control layer that operates between custody and signing. It replaces outdated processes - like using spreadsheets and Slack approvals - with a streamlined workflow that includes payment intents, Risk Dossiers, approval chains for flagged transactions, and tamper-evident audit trails. All of this is achieved while maintaining the speed of blockchain settlements. As Stablerail puts it:
Agents verify the context. Humans sign the transaction. The system protects the treasury - it never touches the money.
This "copilot, not autopilot" approach ensures that AI-driven anomaly detection supports human decision-making rather than replacing it. Finance teams maintain full control over their MPC-secured wallets, while the system safeguards against unauthorized actions, social engineering attempts, and regulatory scrutiny, offering CFO-grade audit evidence when needed.
Conclusion
The irreversible nature of stablecoin transactions makes behavioral anomaly detection a game-changer for managing and auditing these payments. By spotting unusual patterns - like sudden spikes in volume or odd transaction timings - such systems can stop fraudulent or illicit activity before it happens. Considering that global illicit fund flows surpass an estimated $3.1 trillion annually, and stablecoins are increasingly used for laundering due to their liquidity, proactive detection is now critical for corporate treasuries.
Incorporating anomaly detection into treasury operations offers three key benefits: reducing risk, ensuring regulatory compliance through audit trails with timestamps and evidence aligned with FATF and OFAC standards, and boosting efficiency by automating verification in just minutes. Unlike traditional post-transaction monitoring, which struggles with the irreversible nature of blockchain payments, pre-signature controls address risks before transactions are finalized.
To maximize these benefits, corporate finance teams need systems that integrate business context with custody infrastructure. Dynamic baselines tailored to individual transaction histories minimize false positives from legitimate high-value activity while exposing actual anomalies that generic rules might overlook. When paired with policy-as-code enforcement, these systems maintain the speed of on-chain settlements while meeting the rigorous governance standards expected of traditional banking.
This shift is transforming treasury governance. Compliance teams can now review flagged transactions in minutes, supported by audit-ready documentation, allowing companies handling anywhere from $1 million to $50 million in stablecoins to operate securely without sacrificing speed.
Platforms like Stablerail, available at https://stablerail.com, demonstrate this approach by combining real-time anomaly detection with pre-signature verification and policy-as-code governance. These tools empower corporate finance teams to handle stablecoin transactions with both speed and confidence.
FAQs
What data does anomaly detection need to learn our “normal” stablecoin behavior?
Behavioral anomaly detection systems use a mix of on-chain and off-chain data to define what constitutes "normal" activity for stablecoins.
On-chain data includes key metrics like transaction patterns, amounts, timing, gas fees, and movements across multiple chains. This provides a detailed view of blockchain activity.
Off-chain data, such as KYC logs and API request histories, brings in additional context that can't be observed directly on the blockchain.
By combining these datasets, these systems can spot unusual behaviors - like sudden transaction spikes or odd timing patterns - helping improve security and ensure compliance in stablecoin transactions.
How can you block or pause a stablecoin payment before it’s irreversible on-chain?
When dealing with stablecoin payments, you can block or pause a transaction before it becomes irreversible by implementing pre-signature governance and risk management. This process starts with creating a payment intent, which is then subjected to various checks, such as sanctions screening, anomaly detection, and policy compliance. If any issues arise, human approvers can step in to review flagged transactions and block them if necessary, all before the transaction is signed using MPC (multi-party computation) wallets. Once a transaction is signed, it cannot be undone, so these pre-signature controls are crucial for avoiding errors or compliance violations.
How do you set dynamic baselines without generating lots of false alarms?
Dynamic baselines work by regularly updating what qualifies as "normal" behavior, using historical data while factoring in natural fluctuations. Behavioral anomaly detection refines thresholds over time to align with recent trends, steering clear of rigid, static rules. By integrating real-time on-chain and off-chain data and learning from past false positives, these systems stay precise - striking a balance between detecting anomalies and allowing room for legitimate changes.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


