
Pre-transaction risk dossiers are essential tools for managing stablecoin payments, ensuring compliance, and mitigating risks before transactions are finalized. They combine automated checks, policy enforcement, and cryptographic evidence to create a reliable audit trail. With stablecoins processing trillions in payments annually and regulations like the GENIUS Act in effect, these dossiers are no longer optional - they're a necessity for financial institutions. Here's a quick overview of what makes them effective:
Policy Mapping: Links payments to clear business rules for automated approvals or blocks.
Transaction Context: Documents details like timestamps, amounts, and business purposes for clarity.
Sanctions Screening: Integrates real-time checks against watchlists and risk indicators.
Behavioral Analysis: Detects anomalies by analyzing transaction patterns and user behavior.
Counterparty Risk: Profiles transaction participants to assess risks based on history and context.
Evidence Binding: Cryptographically ties supporting documents to transactions for audit integrity.
Human Oversight: Captures decisions and justifications for transparency in flagged cases.
Risk Verdicts: Assigns clear outcomes - pass, flag, or block - based on automated evaluations.
Cryptographic Security: Protects dossier integrity with hashing and digital signatures.
Workflow Integration: Embeds dossiers into payment processes for seamless, real-time risk management.
These features transform scattered, error-prone systems into streamlined, automated workflows, ensuring every transaction is secure, compliant, and audit-ready. Platforms like Stablerail exemplify this approach, offering tools that integrate risk assessments, policy enforcement, and cryptographic protections into a single, efficient process.
1. Policy Mapping and Enforcement
Every stablecoin payment should follow a stablecoin compliance checklist tied to a specific business rule that either approves or blocks it. This direct link between your company's policies and the actual transaction forms the backbone of an audit trail. Essentially, it ensures that every decision is grounded in clear, actionable rules, setting the stage for automated evaluations.
Each payment intent undergoes scrutiny through a Policy Evaluation Graph. This system verifies identity (e.g., sanctions and KYC checks), evaluates transaction patterns (like velocity and thresholds), and enforces business rules (such as vendor restrictions and approval tiers). The result is a Policy Trace - a detailed record that includes the Rule ID, the decision outcome, and the reasoning behind it.
This method aligns with the regulatory concept of a Risk-Based Approach (RBA), where controls are customized based on the actual level of risk, rather than relying on rigid, universal thresholds. Tools like Stablerail translate these policies into machine-enforceable rules, which are automatically applied before any transaction gets signed.
The benefits are striking. A 2025 survey of 600 global companies found that 99% of respondents valued the integration of various AML processes into a unified platform. Cutting-edge screening solutions can now process 99% of payments in under half a second, enabling instant settlements while maintaining robust risk controls. This speed advantage ensures compliance checks happen in real time, at the moment decisions are made, rather than relying on after-the-fact reviews.
2. Transaction Context Documentation
An effective risk dossier collects all the critical details of a transaction: unique IDs, exact amounts paired with their currency or token type (e.g., $50,000 USDC), and precise timestamps in ISO format that indicate when the payment intent was initiated. These details elevate a simple transfer into a well-documented, defensible business record.
Counterparty identities are another key component. Modern dossiers incorporate Decentralized Identifiers (DIDs), wallet addresses, organization names, risk classifications, and jurisdictional statuses. By organizing counterparty data in a structured way, these dossiers eliminate fragmented records and make it easier to integrate with existing financial systems. This clarity also lays the groundwork for connecting transactions to their business purposes.
Establishing a clear business purpose for each transaction is a hallmark of a strong dossier. This includes a trace_context field that captures the rationale for the payment, tools used, and any intermediate states to confirm its legitimacy. For B2B payments, detailed line items - such as SKUs, quantities, unit prices, and warranty terms - simplify reconciliation with CRMs and financial reporting systems. The workflows and data leading up to the payment are often the most valuable aspect of B2B payment infrastructure, turning raw transactions into actionable business insights.
Structured context is also essential for audits. Policy evaluation traces document which rules were applied, their outcomes, and any error codes like POLICY_THRESHOLD_EXCEEDED. Tools like Stablerail automatically capture this evidence during pre-sign verification, linking every payment intent to specific policy clauses and timestamps. This creates a tamper-proof record from the initial request to final settlement, meeting the requirements of stablecoin treasury management audits, board reviews, and regulatory compliance.
Without this documentation layer, transaction records often remain scattered across wallets, spreadsheets, and Slack threads. But with it, every transaction becomes a complete, auditable narrative that can withstand scrutiny.
3. Sanctions and Taint Screening Results
Risk dossiers now include real-time screening results to determine if a counterparty appears on government watchlists or is tied to illicit blockchain activities. These checks are critical for adhering to Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations. In 2024, U.S. regulators handed out hefty penalties for AML violations, underscoring the high stakes of non-compliance. Fraud losses also surged, climbing to $12.7 billion - a 25% jump in just one year. This real-time verification works hand-in-hand with the policy mapping discussed earlier.
To go a step further, modern dossiers incorporate Know Your Transaction (KYT) tools that analyze blockchain addresses for risk indicators, such as links to criminal wallets, mixers, or sanctioned entities. Unlike traditional identity checks done during onboarding, KYT operates in real time, examining every single transaction. This event-driven approach allows organizations to automatically block or reject suspicious deposits before they can even reach their treasury.
Building on these screening insights, dossiers also record compliance flags and assign risk tiers. For example, a dossier might include flags like "sanctions: cleared" or "travel rule: fulfilled", alongside live risk scores categorized into tiers such as Low, Medium, High, or Critical. For high-risk alerts, detailed investigator reports from blockchain intelligence tools provide the context needed for informed decisions. Stablerail integrates these checks during pre-sign verification, cryptographically binding the screening evidence to the payment intent. This creates a tamper-proof audit trail that demonstrates due diligence was performed before the transaction was settled.
Without robust screening practices, organizations expose themselves to major regulatory risks and potential reputational harm. By embedding screening results into every payment process, companies can ensure transactions are verified against the latest threat intelligence. Cryptographically linking this evidence to the transaction provides a solid, defensible record for auditors, boards, and regulators alike.
4. Behavioral and Pattern Analysis
Rule-based checks might catch transactions that exceed preset thresholds, but they often fall short when fraudsters operate just below those limits. That’s where behavioral analysis steps in. Instead of relying solely on static rules, it examines deviations from a user’s normal patterns, creating a dynamic profile based on historical data. This profile tracks details like transaction amounts, login times, device fingerprints, and payout behaviors to spot irregularities. When paired with sanctions screening and policy mapping, it provides a more thorough risk assessment.
Here’s the challenge with traditional monitoring systems: they can generate up to 90% false positives. That’s a lot of noise for compliance teams to sift through. By contrast, machine learning significantly improves accuracy, cutting false positives by 30% and boosting detection rates by 50%–90%. This means teams can focus their efforts on real threats instead of chasing down false alarms triggered by rigid thresholds.
Modern systems also flag contextual anomalies - actions that might seem normal in one context but raise red flags in another. For example, a transaction that’s routine during business hours could be suspicious if it happens at 3:00 AM. Similarly, collective anomalies highlight patterns, like a series of small transfers that, when grouped together, cross risk thresholds.
Stablerail takes this a step further with its pre-sign process. Before a transaction is approved, it analyzes factors like time of day, deviations in amounts, and payout patterns. It then provides clear, narrative explanations for any flagged activity. For example, it might highlight: "This $15,000 transfer at 2:47 AM exceeds typical weekend patterns by 340%." This behavioral analysis works seamlessly with other components - sanctions screening, policy enforcement, and audit trails - to present a full risk assessment before the transaction is finalized.
"Transaction Risk Analysis is where compliance meets competition. The institutions that master real-time fraud modeling don't just meet PSD2 expectations - they deliver faster, safer payments that keep customers loyal." - William Morris, Lead Enterprise Account Executive - UK, Partisia
5. Counterparty Risk Profiles
Understanding who you're dealing with is just as important as knowing why a payment is being made. Counterparty risk profiles fill in the gaps by combining transaction context with behavioral analysis, offering a clearer picture of potential risks. These profiles bring together verified identity, ownership details, transaction history, and behavioral trends, giving decision-makers the information they need before greenlighting payments. Without this layer of insight, payments could be approved without recognizing critical risks.
A well-constructed profile includes a tiered risk rating - Low, Medium, High, or Critical - based on Customer Due Diligence (CDD). This rating guides the level of monitoring and scrutiny required for each counterparty. For instance, low-risk entities might qualify for automatic approval, while high-risk ones could require manual review due to factors like connections to offshore financial hubs or sanctioned entities.
Historical data plays a key role here. Patterns like transaction frequency, amounts, currencies, and payout trends help establish what’s considered "normal" behavior. Deviations from this baseline - such as a sudden $50,000 transfer request when the usual amount is $5,000 - raise red flags. In 2024 alone, fraud losses soared to $12.7 billion, marking a 25% jump in just one year. Many of these losses could have been avoided with stronger counterparty visibility.
But numbers alone aren’t enough. Effective profiles also confirm the legitimacy of the business by checking LinkedIn profiles, verifying website authenticity, reviewing business licenses, and ensuring email domains align with the organization. This extra step ensures that the counterparty is genuinely fit for the transaction. As Stripe explains:
"The more you understand your connected account and their business, the better the risk assessment".
When paired with sanctions screening, policy enforcement, and behavioral analysis, counterparty profiles become a vital tool in pre-transaction risk evaluation.
For example, Stablerail integrates counterparty risk scoring into its Risk Dossier as part of its pre-sign process. The system reviews the recipient’s history, flags elevated risks, and provides clear summaries. A report might state: "Previous transactions averaged $3,200; the current $18,000 request exceeds norms by 463%." This kind of plain-English explanation equips finance teams to make informed decisions, going beyond just ticking compliance boxes.
6. Evidence Binding and Audit Trail
Getting approvals is one thing; proving them later is a whole other challenge. That’s where evidence binding steps in. By directly linking all supporting documents - like invoices, contracts, emails, and approval records - to a transaction, it creates a chronological, date- and time-stamped record that traces every financial decision back to its origin. Without this connection, the integrity of the audit trail can fall apart.
When supporting evidence isn’t captured at the point of decision, finance teams often face the headache of piecing together audit trails from scattered emails and files. It’s a time drain - 56% of accounts payable teams spend over 10 hours weekly manually processing invoices and supplier payments. Worse, 39% of manually processed invoices contain errors that need fixing.
Good evidence binding answers the "who, what, when, where, and why" behind every transaction. Modern audit systems take it further by cross-referencing findings with audit objectives and transaction records, ensuring that every entry checks out. Without cryptographic protection or proper linking, however, the credibility of the audit trail can crumble.
Stablerail tackles these issues head-on by automating evidence binding. It links supporting documents to payment intents using Content Identifiers (CIDs) and cryptographic signatures. For example, when a finance team uploads an invoice for a $15,000 vendor payment, the system ties that document to the transaction record, policy checks, approval process, and final settlement proof. This tamper-proof audit trail builds on the policies and contextual data mentioned earlier, completing the chain of evidence in the risk dossier. For organizations like publicly traded companies under Sarbanes-Oxley or healthcare providers bound by HIPAA, this level of documentation isn’t just helpful - it’s legally required.
7. Human Decision Capture
Automated systems can flag unusual patterns and enforce policies, but they fall short when it comes to explaining the reasoning behind financial decisions. That’s where human judgment steps in. For example, if a CFO overrides a policy to approve an urgent $25,000 vendor payment over the weekend or a treasury manager provides context for a flagged transaction, that reasoning needs to be documented. Without this layer of explanation, the audit trail is incomplete - especially for transactions requiring multiple levels of review.
To ensure transparency, risk dossiers should include key details like the identity of the approver, the rationale behind their decision, and any reasons for policy overrides. This means recording internal memos, notes, or labels that justify each decision. For high-value transactions, quorum-based approvals - where multiple stakeholders, such as a CFO and COO, must sign off - help reduce the risk of single-point failures. When automated systems flag a transaction as medium or high risk, these multi-tier approval flows often trigger a "Challenge-Response" process. This mechanism demands additional proof, such as metadata or a clear purpose, before the payment can proceed.
Combining human decisions with automated checks strengthens accountability and streamlines dispute resolution by tying every action to a specific individual. While automated systems provide the raw data, human inputs add the context necessary for refining risk evaluations. In cases where machines can’t resolve disputes, human review becomes the final step, ensuring that decisions are both precise and well-reasoned. This blend of machine efficiency and human oversight is key to creating a resilient governance framework.
At Stablerail, every override of an automated system requires a documented reason. Whether it’s a CFO justifying a flagged vendor payment or a manager appending an internal memo, all actions are logged with timestamps and cryptographic signatures. These records form a unified trail that links decisions to their supporting evidence.
This meticulous approach results in a comprehensive "Policy Trace", detailing the rule applied, the decision made, and the reasoning behind it. Such documentation isn’t just helpful for internal reconciliation - it’s critical for demonstrating accountability to auditors, boards, and regulators. In today’s financial landscape, clear and traceable records are non-negotiable when it comes to justifying every dollar moved.
8. Risk Scoring and Verdicts
After completing all necessary checks, the system must provide a straightforward decision: should the payment go through, require further review, or be stopped altogether? This is where standardized risk scoring steps in. By assigning machine-readable verdicts like PASS, FLAG, or BLOCK, the system eliminates subjective guesswork and ensures consistent decision-making. These clear outcomes streamline the next steps in the process.
Using a multi-tiered logic engine, the system evaluates factors like payment metadata, the reputation of the counterparty, and the overall transaction context to determine a verdict:
PASS: Low-risk transactions are approved automatically and sent for immediate settlement.
FLAG: Medium- or high-risk transactions are flagged, triggering a challenge-response process that requires additional information or justification.
BLOCK: Critical-risk transactions are blocked outright, with funds frozen or rejected to prevent potential issues.
The real strength of standardized scoring lies in its ability to automate workflows. When a transaction is marked as PASS, downstream systems can process it instantly. FLAGGED transactions are routed to the appropriate approval queue, while BLOCKED transactions generate alerts for immediate investigation. This automation replaces the manual polling and scattered API checks often seen in traditional systems, saving time and reducing errors.
Each decision is documented in a Policy Trace, a structured log that details the rules evaluated, thresholds checked, and the reasoning behind the final verdict. This creates a transparent, auditable record that ties every automated decision to specific policy clauses and timestamps.
For example, Stablerail assigns a PASS, FLAG, or BLOCK status to every payment intent before any money moves. The system evaluates transactions based on your policies - like "Weekend transfers exceeding $10,000 require additional approval" - and provides plain-English explanations referencing the relevant policy clauses and supporting evidence. This ensures decisions are consistent, easy to trace, and ready for audits when needed.
9. Cryptographic Integrity Protection
Once a risk dossier is compiled, ensuring it remains tamper-proof is critical. Auditors and regulators require evidence that cannot be altered after its creation. This is where cryptographic methods become indispensable - they transform a dossier into a verifiable record with authenticity that can be instantly proven.
Cryptographic tools play a key role in achieving this. Cryptographic hashing generates a unique digital fingerprint for the dossier's content. Even the smallest change - like altering a single character - results in a completely different hash. Systems employ Self-Addressing Identifiers (SAIDs) to mathematically bind the data to its identifier. Additionally, digital signatures, supported by a Key Event Log (KEL), confirm the origin and timestamp of the dossier, creating a permanent and auditable record. This setup ensures that the issuer cannot deny having produced the evidence.
From 2017 to 2022, the FDA issued over 160 Warning Letters that specifically highlighted Data Integrity deficiencies. In 2018 alone, 49% of GMP Warning Letters cited issues with Data Integrity. Cryptographic protections directly address these concerns by adhering to the ALCOA+ standard - a framework that ensures evidence is Attributable, Legible, Contemporaneous, Original, Accurate, Complete, Consistent, Enduring, and Available, as required by agencies like the FDA and EMA.
"The integrity of the decision depends not only on the validity of the individual pieces of evidence but also on the integrity of the collection itself." - Daniel Hardman, Author, Trust over IP Foundation
A practical example of this approach can be seen in Stablerail's system. Stablerail employs MPC-based wallet architecture to secure cryptographic signatures for payment dossiers. This system creates signed evidence envelopes, which include agent traces and pre-settlement verification data, ensuring the dossier remains unchanged after the risk assessment is finalized. Each transaction is cryptographically linked back to its original intent and policy evaluation, creating an immutable audit trail. This robust cryptographic integrity ensures the dossier meets the rigorous demands of regulatory frameworks.
10. Workflow Integration
A risk dossier’s value lies in how well it integrates into the workflow it supports. When dossiers operate in isolation, they often introduce delays, errors, and governance gaps. Integrated workflows solve these issues by embedding the dossier into every stage of the transaction process, from the initial creation of intent to the final settlement. This ensures that early risk assessments remain connected to the entire payment cycle.
Manual processes are prone to inefficiencies, causing delays and errors. In contrast, event-driven automation streamlines these workflows. Instead of requiring staff to manually track transaction statuses or transfer data between systems, webhooks emit real-time events - like "Transaction Created" or "Confirmed" - that instantly trigger necessary actions downstream. This shift from batch processing to real-time execution eliminates manual handoffs and prevents bottlenecks.
Take Stablerail as an example of this automation in action. Stablerail integrates payment intents, risk dossiers, automated pre-sign verification, human approvals, and MPC-based signing into a smooth, real-time process. It starts when a user creates a PaymentIntent, a structured object that outlines the amount, participants, and terms before any funds are moved. From there, specialized agents generate a Risk Dossier that includes a verdict (PASS, FLAG, or BLOCK) along with plain-English explanations tied to specific policy clauses and timestamps. Approvers can either approve or override the decision, documenting their reasons. Once approved, the transaction is signed using MPC-based wallets, and the system produces a cryptographically bound receipt that ties the final settlement back to the initial intent and risk evaluation. This end-to-end workflow eliminates fragmented manual approvals, replacing them with a unified and fully auditable process.
"Workflow automation with stablecoins represents a fundamental shift from batch processing to event-driven finance." - Bentzi Rabi, CEO, Utila
The result? Consistent governance across every transaction. Traditional siloed systems often lead to fragmented data and delayed responses. Integrated workflows, on the other hand, enable "horizontal governance", where risk intelligence flows seamlessly between compliance, risk management, and finance teams. This approach reduces subjective interpretations and inconsistent outcomes - manual compliance reviews, for instance, can have error rates as high as 10%. With integrated workflows, every decision is traceable, auditable, and aligned with institutional standards, ensuring a reliable and efficient process.
Comparison: Traditional Approvals vs. Structured Risk Dossiers
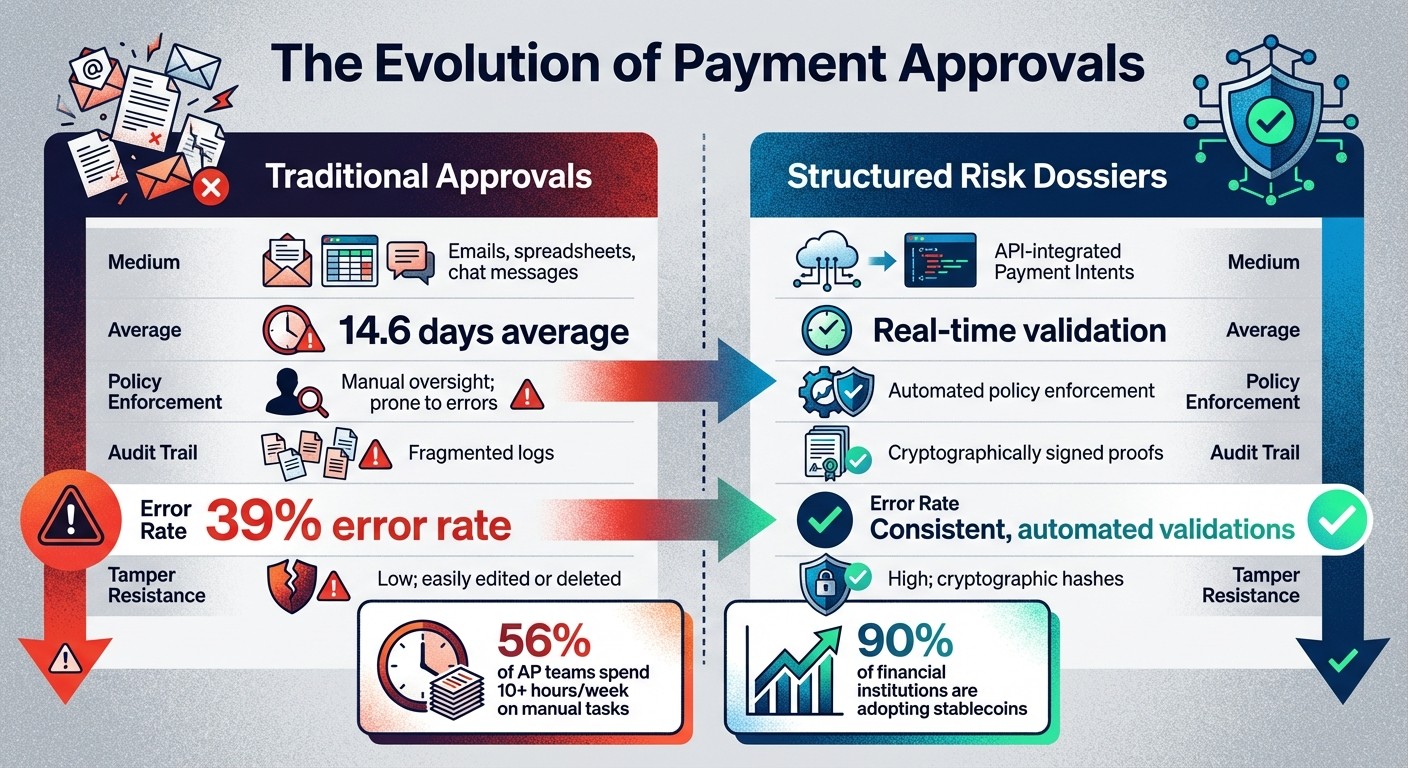
Traditional Payment Approvals vs Structured Risk Dossiers Comparison
Finance teams that depend on emails, spreadsheets, and Slack for approvals often face fragmented records, leading to a 39% error rate and average processing delays of 14.6 days. Payments under this system typically involve scattered communications and records that lack secure, cryptographic links.
Structured risk dossiers present a more systematic approach. Instead of relying on manual checklists, tools like Stablerail implement Policy Evaluation Graphs to enforce rules automatically. These rules cover identity verification, transaction limits, and business logic, ensuring compliance before any payment is processed. Each transaction is tied to a Payment Intent - a structured object that includes the amount, participants, terms, and a detailed audit trail showing which policies were applied and why. This structured approach significantly improves efficiency and accuracy, as shown below.
When comparing the quality of evidence, the difference is clear. Traditional approvals rely on scattered, easily altered records, such as informal email approvals, which are difficult to audit. In contrast, structured dossiers generate cryptographically signed Settlement Proofs that link transactions to specific code paths, policy outcomes, and compliance checks. This tamper-proof evidence is essential for meeting regulatory standards, especially since 90% of financial institutions are already using or planning to adopt stablecoins for payments.
The table below outlines the key differences between these two approaches:
Beyond just improving individual transactions, structured dossiers tackle larger operational inefficiencies. For example, 56% of accounts payable teams spend over 10 hours per week on manual invoice and payment tasks. By automating policy enforcement and generating tamper-resistant evidence, teams can focus on more strategic priorities while maintaining strong audit readiness. These enhancements in accuracy and speed underscore the importance of adopting integrated risk dossiers in today’s financial landscape.
Conclusion
The ten features discussed in this article work together to elevate stablecoin treasury operations from outdated manual processes to streamlined, automated workflows that meet compliance standards. By integrating elements like policy mapping, sanctions screening, behavioral analysis, and cryptographic evidence binding into a cohesive system, finance teams can achieve the governance rigor they need while cutting through the delays of traditional approval methods.
The benefits are clear. Statistics highlight how structured risk dossiers address inefficiencies, satisfying both internal auditors and regulatory requirements under frameworks such as the GENIUS Act (signed July 18, 2025). This measurable progress sets the foundation for platforms like Stablerail to showcase their unified approach.
Stablerail builds on these principles by acting as an intelligent control layer that operates above custody and before transaction signing. It safeguards business decisions by conducting pre-sign checks for sanctions, policy compliance, and behavioral irregularities, while also generating clear, cryptographically bound explanations. Every step - whether it’s an intent, flag, approval, or override - is documented in a comprehensive audit trail. This gives CFOs the confidence and documentation required to justify decisions to boards and regulators.
Transitioning from scattered emails and spreadsheets to structured risk management isn’t just about meeting compliance requirements - it’s also about achieving operational efficiency. Automating policy enforcement and risk scoring allows finance teams to focus on high-value, strategic initiatives. As Matt Higginson and Garry Spanz of McKinsey & Company put it:
"Stablecoin advocates say that the technology can transcend banking hours and global borders, offering substantial improvements on current payment infrastructure, including speed, cost, transparency, availability, and increased inclusion".
These insights underline the dual benefits of automated risk dossiers: strengthening compliance and enhancing agility. For organizations managing corporate stablecoin payments, the real challenge isn’t deciding whether to adopt this technology - it’s implementing it quickly enough to gain a competitive edge.
FAQs
How do pre-transaction risk dossiers improve compliance in stablecoin payments?
Pre-transaction risk dossiers play a crucial role in ensuring compliance by conducting detailed reviews of every stablecoin payment before it’s processed. These reviews cover key areas like sanctions screening, AML/KYC compliance, and policy enforcement, making sure that transactions adhere to both internal policies and regulatory requirements.
Beyond that, they help identify suspicious activity, evaluate counterparty risks, and create a transparent, auditable record of each transaction. This allows finance teams to confidently navigate regulatory demands without sacrificing efficiency in their operations.
How does cryptographic evidence ensure the integrity of an audit trail?
Cryptographic evidence acts as a secure, tamper-resistant safeguard, ensuring that every action in a pre-transaction risk assessment is tied to an unchangeable audit trail. By employing cryptographic hashes to log critical details - like specific function calls and runtime states that lead to a payment intent - any unauthorized modifications to the logic or data can be immediately identified.
To enhance security further, digital signatures are used to seal pre-settlement verification results, agent activity logs, and policy decisions into secure "evidence envelopes." These signatures ensure the evidence remains intact and verifiable, offering non-repudiation and maintaining a clear chain of custody. This method keeps the audit trail dependable, transparent, and resistant to interference throughout the transaction lifecycle.
Why is behavioral analysis important for identifying unusual transactions?
Behavioral analysis plays a key role in spotting unusual transactions by comparing each payment to the normal patterns of an account, user, or entity. It examines details like typical transaction amounts, the time of day transactions occur, frequency, and relationships with counterparties. When something deviates from these norms, it could signal potential fraud, money laundering, or breaches of policy.
Incorporating this kind of analysis before transactions are completed ensures that anomalies are flagged early - before any money changes hands. This allows finance teams to step in, review, and approve transactions in real time. By catching subtle irregularities upfront, this method not only boosts security but also minimizes errors and helps organizations stay compliant.
Related Blog Posts
Ready to modernize your treasury security?
Latest posts
Explore more product news and best practices for using Stablerail.


